Collateral Management

Business Logic Diagram 3d Man Tied With Golden Chain PowerPoint Slides
We present our business logic diagram 3d man tied with golden chain PowerPoint Slides.Download and present our Security PowerPoint Templates because Our PowerPoint Templates and Slides will let you Hit the right notes. Watch your audience start singing to your tune. Use our Chains PowerPoint Templates because Our PowerPoint Templates and Slides are effectively colour coded to prioritise your plans They automatically highlight the sequence of events you desire. Download and present our Business PowerPoint Templates because Our PowerPoint Templates and Slides are truly out of this world. Even the MIB duo has been keeping tabs on our team. Present our Process and Flows PowerPoint Templates because you should once Tap the ingenuity of our PowerPoint Templates and Slides. They are programmed to succeed. Use our Shapes PowerPoint Templates because Our PowerPoint Templates and Slides are like the strings of a tennis racquet. Well strung to help you serve aces.Use these PowerPoint slides for presentations relating to 3d, Business, Chain, Connect, Connection, Heavy, Industrial, Industry, Isolated, Link, Linked, Man, Metal, Power, Powerful, Protection, Secure, Steel, Strength, Support, Symbol, Teamwork, Weak, White. The prominent colors used in the PowerPoint template are Red, Yellow, Black. Professionals tell us our business logic diagram 3d man tied with golden chain PowerPoint Slides are effectively colour coded to prioritise your plans They automatically highlight the sequence of events you desire. The feedback we get is that our Industry PowerPoint templates and PPT Slides are designed by a team of presentation professionals. Professionals tell us our business logic diagram 3d man tied with golden chain PowerPoint Slides are effectively colour coded to prioritise your plans They automatically highlight the sequence of events you desire. People tell us our Connect PowerPoint templates and PPT Slides provide you with a vast range of viable options. Select the appropriate ones and just fill in your text. PowerPoint presentation experts tell us our business logic diagram 3d man tied with golden chain PowerPoint Slides are topically designed to provide an attractive backdrop to any subject. You can be sure our Isolated PowerPoint templates and PPT Slides are visually appealing. Arouse the faint hearted with our Business Logic Diagram 3d Man Tied With Golden Chain PowerPoint Slides. Awaken their courage to act.
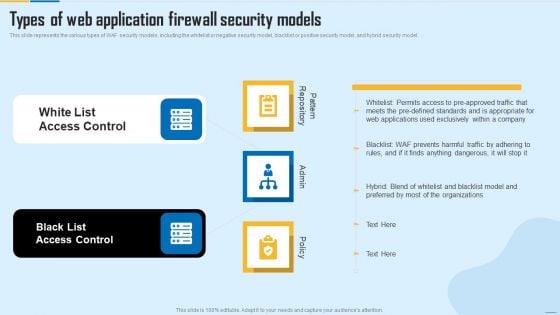
Types Of Web Application Firewall Security Models WAF Platform Themes PDF
This slide represents the various types of WAF security models, including the whitelist or negative security model, blacklist or positive security model, and hybrid security model. Presenting Types Of Web Application Firewall Security Models WAF Platform Themes PDF to provide visual cues and insights. Share and navigate important information on two stages that need your due attention. This template can be used to pitch topics like White List Access Control, Black List Access Control. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Piggy Bank Protect Money Finance PowerPoint Templates Ppt Backgrounds For Slides 0413
We present our Piggy Bank Protect Money Finance PowerPoint Templates PPT Backgrounds For Slides 0413.Download and present our Umbrellas PowerPoint Templates because You can Be the puppeteer with our PowerPoint Templates and Slides as your strings. Lead your team through the steps of your script. Download our Money PowerPoint Templates because You aspire to touch the sky with glory. Let our PowerPoint Templates and Slides provide the fuel for your ascent. Present our Finance PowerPoint Templates because Our PowerPoint Templates and Slides will Embellish your thoughts. They will help you illustrate the brilliance of your ideas. Download and present our Security PowerPoint Templates because It can Bubble and burst with your ideas. Download and present our Future PowerPoint Templates because Watching this your Audience will Grab their eyeballs, they wont even blink.Use these PowerPoint slides for presentations relating to Piggy with umbrella, security, money, finance, future, umbrellas. The prominent colors used in the PowerPoint template are Blue, Yellow, Black. Redesign your organization with our Piggy Bank Protect Money Finance PowerPoint Templates Ppt Backgrounds For Slides 0413. Download without worries with our money back guaranteee.
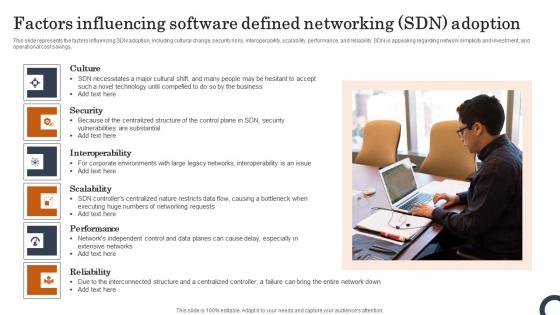
Factors Influencing Software Defined Networking SDN Adoption Evolution Of SDN Controllers Slides Pdf
This slide represents the factors influencing SDN adoption, including cultural change, security risks, interoperability, scalability, performance, and reliability. SDN is appealing regarding network simplicity and investment, and operational cost savings. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Factors Influencing Software Defined Networking SDN Adoption Evolution Of SDN Controllers Slides Pdf and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable. This slide represents the factors influencing SDN adoption, including cultural change, security risks, interoperability, scalability, performance, and reliability. SDN is appealing regarding network simplicity and investment, and operational cost savings.
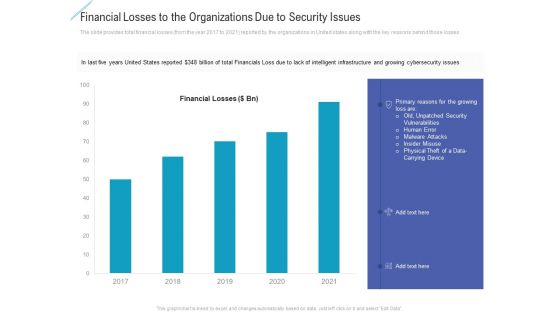
Financial Losses To The Organizations Due To Security Issues Themes PDF
Deliver an awe inspiring pitch with this creative financial losses to the organizations due to security issues themes pdf bundle. Topics like financial losses to the organizations due to security issues can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
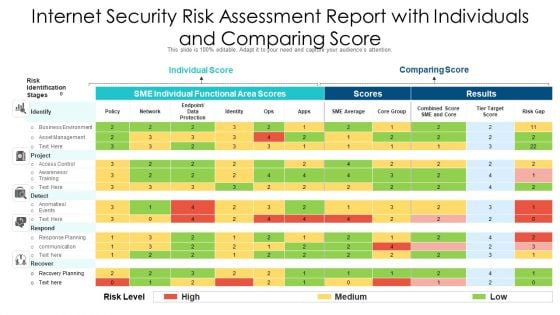
Internet Security Risk Assessment Report With Individuals And Comparing Score Ppt PowerPoint Presentation File Good PDF
Showcasing this set of slides titled internet security risk assessment report with individuals and comparing score ppt powerpoint presentation file good pdf. The topics addressed in these templates are individual score, comparing score, identify. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
Governance Plan Framework For Data Security Ppt PowerPoint Presentation Gallery Model PDF
Presenting governance plan framework for data security ppt powerpoint presentation gallery model pdf to dispense important information. This template comprises six stages. It also presents valuable insights into the topics including data security, data governance, physical data governance. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
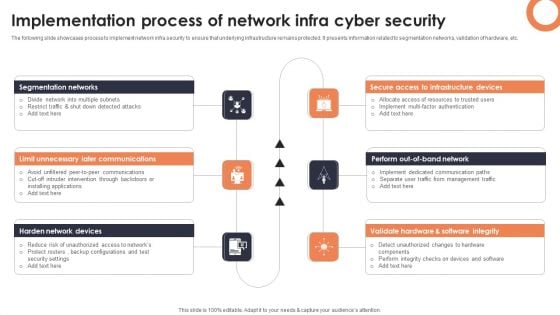
Implementation Process Of Network Infra Cyber Security Introduction PDF
The following slide showcases process to implement network infra security to ensure that underlying infrastructure remains protected. It presents information related to segmentation networks, validation of hardware, etc. Presenting Implementation Process Of Network Infra Cyber Security Introduction PDF to dispense important information. This template comprises six stages. It also presents valuable insights into the topics including Segmentation Networks, Secure Access Infrastructure, Validate Hardware. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
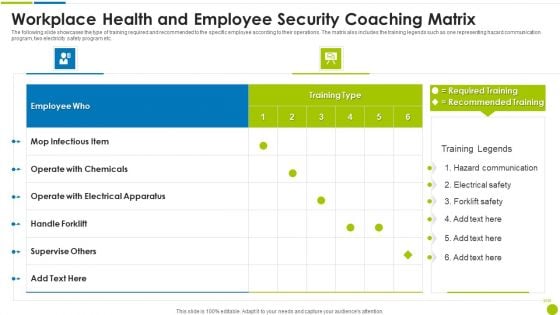
Workplace Health And Employee Security Coaching Matrix Ppt Slides Guide PDF
The following slide showcases the type of training required and recommended to the specific employee according to their operations. The matrix also includes the training legends such as one representing hazard communication program, two electricity safety program etc. Pitch your topic with ease and precision using this workplace health and employee security coaching matrix ppt slides guide pdf. This layout presents information on employee, operate, electrical apparatus, supervise others. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
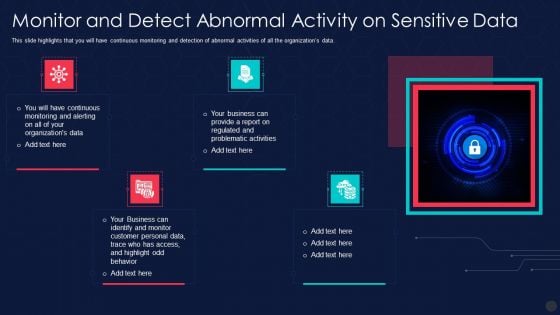
Information Privacy IT Monitor And Detect Abnormal Activity On Sensitive Data Structure PDF
This slide highlights that you will have continuous monitoring and detection of abnormal activities of all the organizations data. Presenting information privacy it monitor and detect abnormal activity on sensitive data structure pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like monitor and detect abnormal activity on sensitive data. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
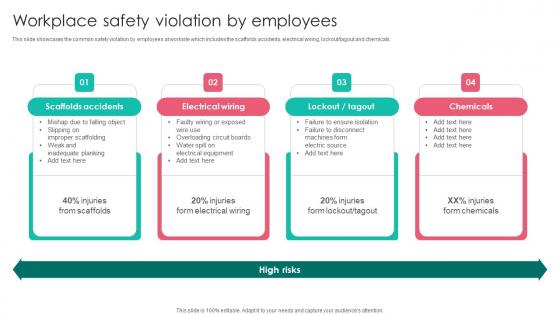
Workplace Safety Violation By Employees Workplace Safety Protocol And Security Practices Demonstration Pdf
This slide showcases the common safety violation by employees at worksite which includes the scaffolds accidents, electrical wiring, lockout tagout and chemicals. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Workplace Safety Violation By Employees Workplace Safety Protocol And Security Practices Demonstration Pdf. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Workplace Safety Violation By Employees Workplace Safety Protocol And Security Practices Demonstration Pdf today and make your presentation stand out from the rest This slide showcases the common safety violation by employees at worksite which includes the scaffolds accidents, electrical wiring, lockout tagout and chemicals.
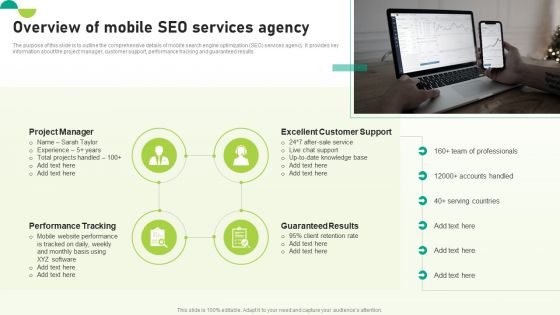
Utilizing SEO To Boost Customer Overview Of Mobile SEO Services Agency Slides PDF
The purpose of this slide is to outline the comprehensive details of mobile search engine optimization SEO services agency. It provides key information about the project manager, customer support, performance tracking and guaranteed results. Are you searching for a Utilizing SEO To Boost Customer Overview Of Mobile SEO Services Agency Slides PDF that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort youve put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Utilizing SEO To Boost Customer Overview Of Mobile SEO Services Agency Slides PDF from Slidegeeks today.

Introduction To Mobile SEM Overview Of Mobile SEO Services Agency Mockup PDF
The purpose of this slide is to outline the comprehensive details of mobile search engine optimization SEO services agency. It provides key information about the project manager, customer support, performance tracking and guaranteed results. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Introduction To Mobile SEM Overview Of Mobile SEO Services Agency Mockup PDF can be your best option for delivering a presentation. Represent everything in detail using Introduction To Mobile SEM Overview Of Mobile SEO Services Agency Mockup PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.

Overview Of Mobile SEO Services Agency Graphics PDF
The purpose of this slide is to outline the comprehensive details of mobile search engine optimization SEO services agency. It provides key information about the project manager, customer support, performance tracking and guaranteed results. Get a simple yet stunning designed Overview Of Mobile SEO Services Agency Graphics PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Overview Of Mobile SEO Services Agency Graphics PDF can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.
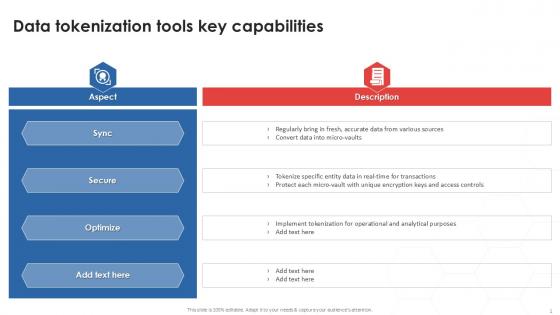
Data Tokenization Tools Tokenization Strategies For Data Security PPT Template
Boost your pitch with our creative Data Tokenization Tools Tokenization Strategies For Data Security PPT Template. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them. Our Data Tokenization Tools Tokenization Strategies For Data Security PPT Template are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
Operational Safety Guidelines Air Workplace Safety Protocol And Security Practices Icons Pdf
This slides highlights the operational safety guidelines to minimize air compressor hazards. It showcases different protective gears with pre operation, operation and post operation. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye catching visual experience. Download Operational Safety Guidelines Air Workplace Safety Protocol And Security Practices Icons Pdf to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high quality content for you. Later on, you can personalize the content by editing the Operational Safety Guidelines Air Workplace Safety Protocol And Security Practices Icons Pdf. This slides highlights the operational safety guidelines to minimize air compressor hazards. It showcases different protective gears with pre operation, operation and post operation.

Secure Code Review Process Ppt PowerPoint Presentation Layouts Examples Cpb
Presenting this set of slides with name secure code review process ppt powerpoint presentation layouts examples cpb. This is an editable Powerpoint four stages graphic that deals with topics like secure code review process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
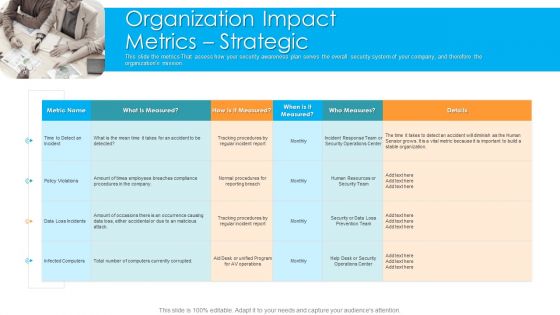
Organization Impact Metrics Strategic Hacking Prevention Awareness Training For IT Security Graphics PDF
This slide the metrics That assess how your security awareness plan serves the overall security system of your company, and therefore the organizations mission. Presenting organization impact metrics strategic hacking prevention awareness training for it security graphics pdf to provide visual cues and insights. Share and navigate important information on one stages that need your due attention. This template can be used to pitch topics like organization, policy violations, data loss incidents, human resources. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
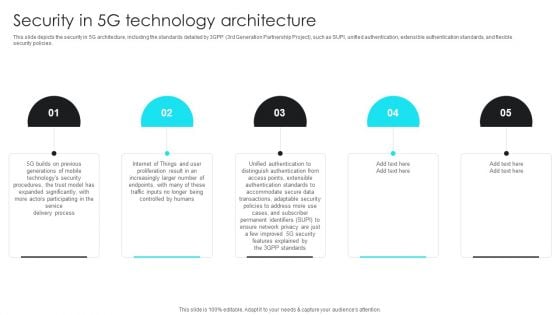
5G Network Operations Security In 5G Technology Architecture Template PDF
This slide depicts the security in 5G architecture, including the standards detailed by 3GPP 3rd Generation Partnership Project, such as SUPI, unified authentication, extensible authentication standards, and flexible security policies. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download 5G Network Operations Security In 5G Technology Architecture Template PDF to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the 5G Network Operations Security In 5G Technology Architecture Template PDF.
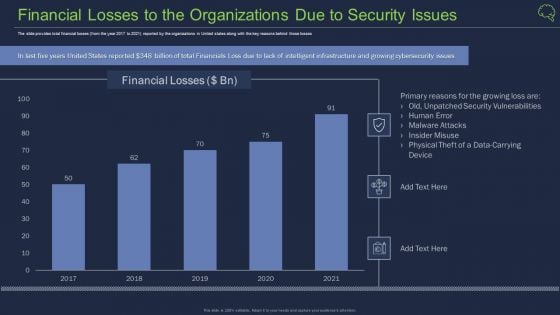
Financial Losses To The Organizations Due To Security Issues Ppt Background PDF
The slide provides total financial losses from the year 2017 to 2021 reported by the organizations in United states along with the key reasons behind those losses Deliver an awe inspiring pitch with this creative financial losses to the organizations due to security issues ppt background pdf bundle. Topics like financial losses to the organizations due to security issues can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Endpoint Initiated Zero Trust Network Topology Zero Trust Network Security Template Pdf
This slide describes the overview of the endpoint-initiated zero trust network topology model of ZTNA deployment. The purpose of this slide is to showcase the conceptual model of the approach along with its benefits and drawbacks. The model components include the end-user device, SDP controller, gateway, and directory. If your project calls for a presentation, then Slidegeeks is your go-to partner because we have professionally designed, easy-to-edit templates that are perfect for any presentation. After downloading, you can easily edit Endpoint Initiated Zero Trust Network Topology Zero Trust Network Security Template Pdf and make the changes accordingly. You can rearrange slides or fill them with different images. Check out all the handy templates This slide describes the overview of the endpoint-initiated zero trust network topology model of ZTNA deployment. The purpose of this slide is to showcase the conceptual model of the approach along with its benefits and drawbacks. The model components include the end-user device, SDP controller, gateway, and directory.
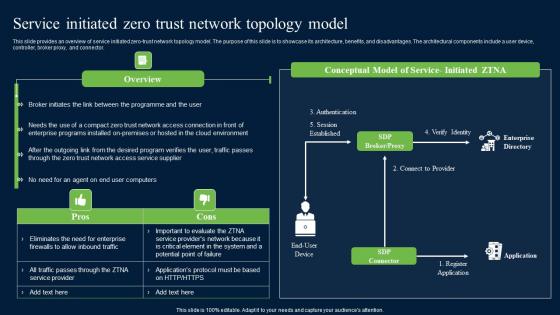
Service Initiated Zero Trust Network Topology Model Zero Trust Network Security Guidelines Pdf
This slide provides an overview of service initiated zero-trust network topology model. The purpose of this slide is to showcase its architecture, benefits, and disadvantages. The architectural components include a user device, controller, broker proxy, and connector. Find a pre-designed and impeccable Service Initiated Zero Trust Network Topology Model Zero Trust Network Security Guidelines Pdf. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation. This slide provides an overview of service initiated zero-trust network topology model. The purpose of this slide is to showcase its architecture, benefits, and disadvantages. The architectural components include a user device, controller, broker proxy, and connector.
Web Application Security Testing Sample Diagram Powerpoint Image
This is a web application security testing sample diagram powerpoint image. This is a four stage process. The stages in this process are information gathering, planning analysis, test execution, view report.
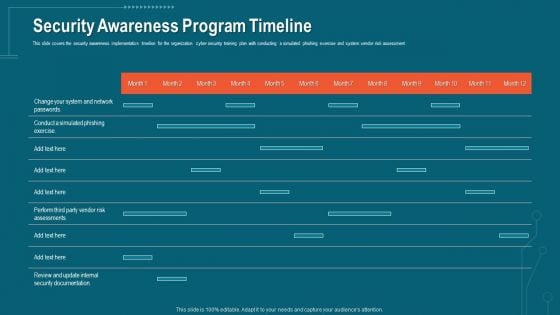
Companys Data Safety Recognition Security Awareness Program Timeline Portrait PDF
This slide covers the security awareness implementation timeline for the organization cyber security training plan with conducting a simulated phishing exercise and system vendor risk assessment. This slide covers the security awareness implementation timeline for the organization cyber security training plan with conducting a simulated phishing exercise and system vendor risk assessment. Deliver an awe-inspiring pitch with this creative companys data safety recognition security awareness program timeline portrait pdf bundle. Topics like security awareness program timeline can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Image Of Key In Dollar Notes PowerPoint Templates Ppt Backgrounds For Slides 0113
We present our Image Of Key In Dollar Notes PowerPoint Templates PPT Backgrounds For Slides 0113.Use our Money PowerPoint Templates because It can Conjure up grand ideas with our magical PowerPoint Templates and Slides. Leave everyone awestruck by the end of your presentation. Download and present our Business PowerPoint Templates because Our PowerPoint Templates and Slides will give good value for money. They also have respect for the value of your time. Present our Security PowerPoint Templates because you can Break through with our PowerPoint Templates and Slides. Bring down the mental barriers of your audience. Download and present our Services PowerPoint Templates because You are an avid believer in ethical practices. Highlight the benefits that accrue with our PowerPoint Templates and Slides. Download our Future PowerPoint Templates because you can Break through with our PowerPoint Templates and Slides. Bring down the mental barriers of your audience.Use these PowerPoint slides for presentations relating to You intend to deliver. Make it happen with our Image Of Key In Dollar Notes PowerPoint Templates Ppt Backgrounds For Slides 0113. Make sure your presentation gets the attention it deserves.

Disaster Recovery Planning Element Of Cyber Security Template PDF
This slide depicts the disaster recovery plan in the cyber security model and what strategies an organization needs to adopt to recover from an attack or natural disaster. It also contains the types of disaster recovery plans and planning process. Slidegeeks is here to make your presentations a breeze with Disaster Recovery Planning Element Of Cyber Security Template PDF With our easy to use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.
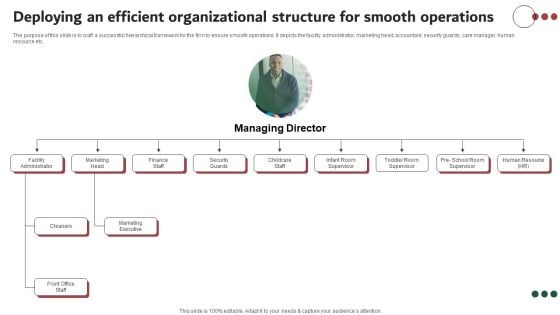
Deploying An Efficient Organizational Structure For Smooth Operations Summary PDF
The purpose of this slide is to craft a successful hierarchical framework for the firm to ensure smooth operations. It depicts the facility administrator, marketing head, accountant, security guards, care manager, human resource etc. Find a pre-designed and impeccable Deploying An Efficient Organizational Structure For Smooth Operations Summary PDF. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
Develop Leaders And Employees Presentation Portfolio
This is a develop leaders and employees presentation portfolio. This is a seven stage process. The stages in this process are zero tolerance for corruption, information security, phase out hazardous, develop leaders and employees, responsible supplier relationships, reduce climate impact, sustainable innovations.
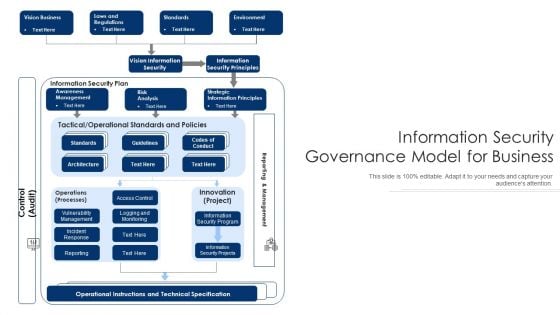
Information Security Governance Model For Business Ppt PowerPoint Presentation Show Graphics PDF
Persuade your audience using this information security governance model for business ppt powerpoint presentation show graphics pdf. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including vision information security, information security principles, operational instructions and technical specification. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
6 Stages Parallel Arrow Control Flow Diagram Startup Business Plan PowerPoint Slides
We present our 6 stages parallel arrow control flow diagram startup business plan PowerPoint Slides.Use our Advertising PowerPoint Templates because You are working at that stage with an air of royalty. Let our PowerPoint Templates and Slides be the jewels in your crown. Use our Arrows PowerPoint Templates because Our PowerPoint Templates and Slides will let you Illuminate the road ahead to Pinpoint the important landmarks along the way. Use our Business PowerPoint Templates because Our PowerPoint Templates and Slides will let you Hit the target. Go the full distance with ease and elan. Present our Shapes PowerPoint Templates because You should Throw the gauntlet with our PowerPoint Templates and Slides. They are created to take up any challenge. Present our Process and Flows PowerPoint Templates because You can Be the puppeteer with our PowerPoint Templates and Slides as your strings. Lead your team through the steps of your script.Use these PowerPoint slides for presentations relating to Arrow, Arrow Button, Arrow Vector, Art, Business, Button, Chart, Clip, communication, Decoration, Diagram, Direction, Drop, Element, Empty, Finance, Flow, Graph, Graphic, Illustration, Isometric, marketing, Presentation, Process, Shape, Sign, success, Step, Symbol, Template, Text, Vector. The prominent colors used in the PowerPoint template are Blue, Gray, Black. Presenters tell us our 6 stages parallel arrow control flow diagram startup business plan PowerPoint Slides effectively help you save your valuable time. Customers tell us our Button PowerPoint templates and PPT Slides will save the presenter time. The feedback we get is that our 6 stages parallel arrow control flow diagram startup business plan PowerPoint Slides will impress their bosses and teams. The feedback we get is that our Business PowerPoint templates and PPT Slides are aesthetically designed to attract attention. We guarantee that they will grab all the eyeballs you need. Presenters tell us our 6 stages parallel arrow control flow diagram startup business plan PowerPoint Slides are specially created by a professional team with vast experience. They diligently strive to come up with the right vehicle for your brilliant Ideas. We assure you our Arrow PowerPoint templates and PPT Slides will get their audience's attention. Consult experts with our 6 Stages Parallel Arrow Control Flow Diagram Startup Business Plan PowerPoint Slides. Download without worries with our money back guaranteee.
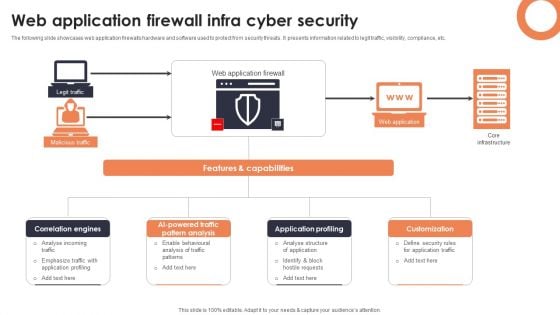
Web Application Firewall Infra Cyber Security Designs PDF
The following slide showcases web application firewalls hardware and software used to protect from security threats. It presents information related to legit traffic, visibility, compliance, etc. Showcasing this set of slides titled Web Application Firewall Infra Cyber Security Designs PDF. The topics addressed in these templates are Correlation Engines, AI Powered Traffic Pattern, Application Profiling. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
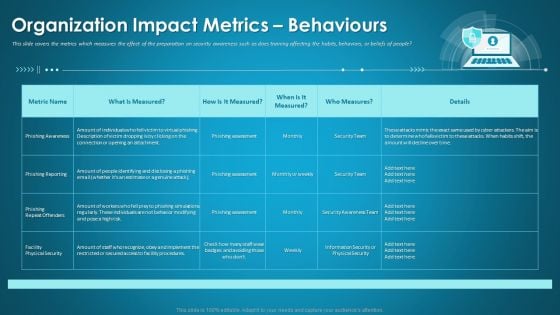
Organizational Network Security Awareness Staff Learning Organization Impact Metrics Behaviours Portrait PDF
This slide covers the metrics which measures the effect of the preparation on security awareness such as does training affecting the habits, behaviors, or beliefs of people. Deliver an awe-inspiring pitch with this creative organizational network security awareness staff learning organization impact metrics behaviours portrait pdf bundle. Topics like organization impact metrics behaviours can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Bring Your Own Device Security Policy Check In Organizations Icon Summary PDF
Persuade your audience using this Bring Your Own Device Security Policy Check In Organizations Icon Summary PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Bring Your Own, Device Security Policy, Check Organizations. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
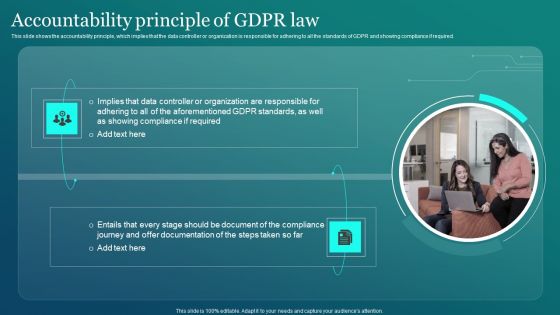
Information Security Accountability Principle Of GDPR Law Ppt PowerPoint Presentation File Backgrounds PDF
This slide shows the accountability principle, which implies that the data controller or organization is responsible for adhering to all the standards of GDPR and showing compliance if required. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Information Security Accountability Principle Of GDPR Law Ppt PowerPoint Presentation File Backgrounds PDF for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
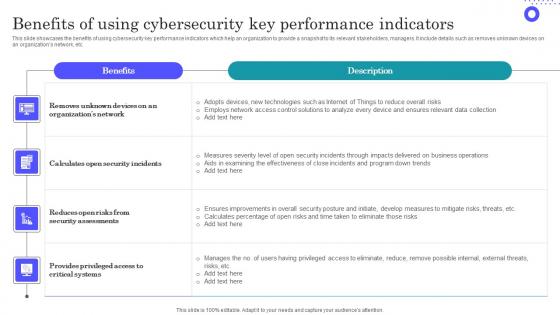
Benefits Of Using Cybersecurity Key Performance Indicators Slides Pdf
Showcasing this set of slides titled Benefits Of Using Cybersecurity Key Performance Indicators Slides Pdf The topics addressed in these templates are Organizations Network, Security Assessments, Provides Privileged All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting. This slide showcases the benefits of using cybersecurity key performance indicators which help an organization to provide a snapshot to its relevant stakeholders, managers. It include details such as removes unknown devices on an organizations network, etc.
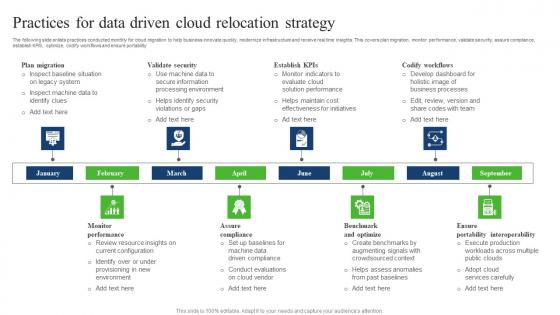
Practices For Data Driven Cloud Relocation Strategy Slides Pdf
The following slide enlists practices conducted monthly for cloud migration to help business innovate quickly, modernize infrastructure and receive real time insights. This covers plan migration, monitor performance, validate security, assure compliance, establish KPIS, optimize, codify workflows and ensure portability. Pitch your topic with ease and precision using this Practices For Data Driven Cloud Relocation Strategy Slides Pdf. This layout presents information on Validate Security, Codify Workflows, Benchmark And Optimize, Assure Compliance. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout. The following slide enlists practices conducted monthly for cloud migration to help business innovate quickly, modernize infrastructure and receive real time insights. This covers plan migration, monitor performance, validate security, assure compliance, establish KPIS, optimize, codify workflows and ensure portability.

Process For Responding To Internet Security Threats Template PDF
This slide exhibits process for responding to security data breach. It includes multiple steps such as- analyzing the current damage, keeping record how much damage is caused and so on. Pitch your topic with ease and precision using this process for responding to internet security threats template pdf. This layout presents information on process for responding to internet security threats. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Employee Security Coaching Matrix Ppt PowerPoint Presentation Complete Deck With Slides
Boost your confidence and team morale with this well-structured employee security coaching matrix ppt powerpoint presentation complete deck with slides. This prefabricated set gives a voice to your presentation because of its well-researched content and graphics. Our experts have added all the components very carefully, thus helping you deliver great presentations with a single click. Not only that, it contains a set of twelve slides that are designed using the right visuals, graphics, etc. Various topics can be discussed, and effective brainstorming sessions can be conducted using the wide variety of slides added in this complete deck. Apart from this, our PPT design contains clear instructions to help you restructure your presentations and create multiple variations. The color, format, design anything can be modified as deemed fit by the user. Not only this, it is available for immediate download. So, grab it now.

Retirement Nest Future PowerPoint Presentation Slides Cc
Microsoft PowerPoint Templates and Backgrounds with retirement nest eggs make up isolated on black Our Retirement Nest Future PowerPoint Presentation Slides Cc will work in your favour. Acquire the advantage of their ability.
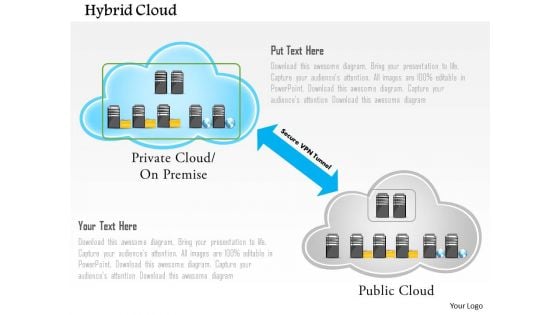
Hybrid Cloud With Public And Privet Cloud Networks And VPN Tunnel Powerpoint Template
This PowerPoint template contains graphic of hybrid cloud with public and privet cloud networks. You may use this PPT slide to exhibit how a VPN tunnel works. Use this technology template design to illustrate your ability.

Implementation Of Digital Advancement Techniques Essential Personnel Required Pictures PDF
The following slide outlines key personnel required to develop digital transformation team for converting insurer traditional to technology based. Team consists of members which are technologists, security and compliance specialists, business technology liaisons, project managers, financial stakeholders, marketers, implementation leads and evangelists. There are so many reasons you need a Implementation Of Digital Advancement Techniques Essential Personnel Required Pictures PDF. The first reason is you cannot spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
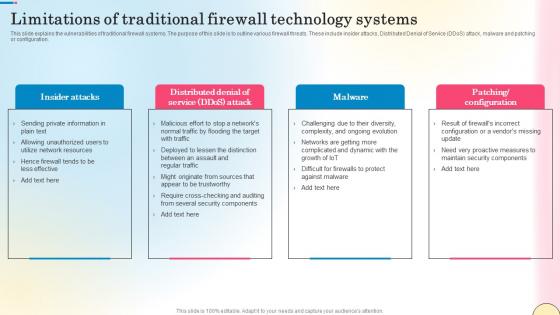
Limitations Of Traditional Firewall Technology Systems Network Security Pictures Pdf
This slide explains the vulnerabilities of traditional firewall systems. The purpose of this slide is to outline various firewall threats. These include insider attacks, Distributed Denial of Service DDoS attack, malware and patching or configuration. Presenting this PowerPoint presentation, titled Limitations Of Traditional Firewall Technology Systems Network Security Pictures Pdf, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Limitations Of Traditional Firewall Technology Systems Network Security Pictures Pdf. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Limitations Of Traditional Firewall Technology Systems Network Security Pictures Pdf that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs. This slide explains the vulnerabilities of traditional firewall systems. The purpose of this slide is to outline various firewall threats. These include insider attacks, Distributed Denial of Service DDoS attack, malware and patching or configuration.
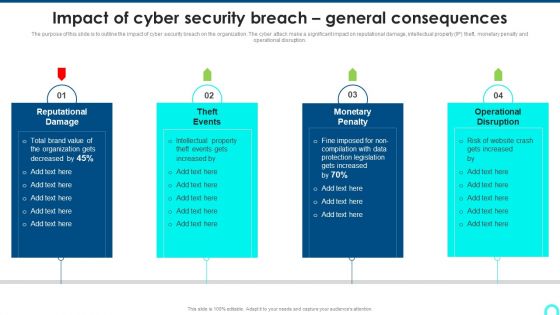
Impact Of Cyber Security Breach General Consequences Ideas PDF
The purpose of this slide is to outline the impact of cyber security breach on the organization. The cyber attack make a significant impact on reputational damage, intellectual property IP theft, monetary penalty and operational disruption. This is a Impact Of Cyber Security Breach General Consequences Ideas PDF template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Reputational Damage, Monetary Penalty, Operational Disruption. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Develop Corporate Cyber Security Risk Mitigation Plan Why Us For Organization Cyber Protection Services Sample PDF
Presenting develop corporate cyber security risk mitigation plan why us for organization cyber protection services sample pdf to provide visual cues and insights. Share and navigate important information on two stages that need your due attention. This template can be used to pitch topics like knowledge, system security, net development, it support services. In addtion, this PPT design contains high-resolution images, graphics, etc, that are easily editable and available for immediate download.

Debit Card With Lock For Safe Transactions Ppt PowerPoint Presentation Infographics Tips PDF
Presenting this set of slides with name data network security with lock showing online safety icon ppt powerpoint presentation infographic template graphics pdf. This is a three stage process. The stages in this process are debit card with lock for safe transactions. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Data Breach Prevention Recognition Security Awareness Program Timeline Inspiration PDF
This slide covers the security awareness implementation timeline for the organization cyber security training plan with conducting a simulated phishing exercise and system vendor risk assessment. Deliver and pitch your topic in the best possible manner with this data breach prevention recognition security awareness program timeline inspiration pdf. Use them to share invaluable insights on security awareness, implementation timeline, organization, cyber security training plan, risk assessment and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
Security Strategic Planning Process For CPS Ppt Slides Icons PDF
This slide represents the security strategic planning process for CPS, including business strategy, technology roadmap, vision statement environment trends, current state assessment, and so on. Deliver and pitch your topic in the best possible manner with this Security Strategic Planning Process For CPS Ppt Slides Icons PDF. Use them to share invaluable insights on Business Strategy, Technology Roadmap, Environmental Trends and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Information Security Risk Evaluation Cyber Attacks Faced By Organization In Previous Financial Year Template PDF
This slide showcases information security attacks faced by organization in past financial year. It can help company to assess different type if cyber attacks and formulate strategies to tackle them.Deliver and pitch your topic in the best possible manner with this Information Security Risk Evaluation Cyber Attacks Faced By Organization In Previous Financial Year Template PDF. Use them to share invaluable insights on Attacks In Organization, Organization Experienced, Attacks Last and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
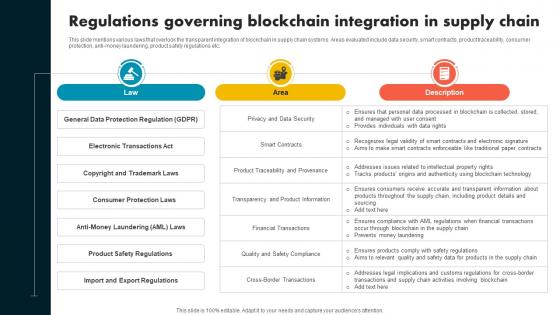
Regulations Governing Blockchain Integration In Supply Chain Evolution Harnessing The Power BCT SS V
This slide mentions various laws that overlook the transparent integration of blockchain in supply chain systems. Areas evaluated include data security, smart contracts, product traceability, consumer protection, anti-money laundering, product safety regulations etc. This modern and well-arranged Regulations Governing Blockchain Integration In Supply Chain Evolution Harnessing The Power BCT SS V provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint, no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included. This slide mentions various laws that overlook the transparent integration of blockchain in supply chain systems. Areas evaluated include data security, smart contracts, product traceability, consumer protection, anti-money laundering, product safety regulations etc.

Implementing Cyber Security Awareness Training Program Professional PDF
The purpose of this slide is to delineate a comprehensive security awareness training program that can assist corporates to mitigate cyber attacks and reduce downtime. Information covered in this slide is related to training goals, major topics to cover, and projected result. Make sure to capture your audiences attention in your business displays with our gratis customizable Implementing Cyber Security Awareness Training Program Professional PDF. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.

Secure Access Service Edge Architecture Characteristics Ppt Summary Portfolio PDF
This slide represents the architectural characteristics of a secure access service edge. The purpose of this slide is to showcase the features of SASE architecture that include identity-driven, cloud-native, support for all edges, and global distribution. Make sure to capture your audiences attention in your business displays with our gratis customizable Secure Access Service Edge Architecture Characteristics Ppt Summary Portfolio PDF. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.

Information Security System Auditing And Risk Assessment Elements PDF
The following slide highlights the information security system audit and risk assessment illustrating key headings which includes security risk assessment, security auditing, security incident monitoring, security incident response Persuade your audience using this Information Security System Auditing And Risk Assessment Elements PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Security Risk Assessment, Security Auditing, Security Incident Monitoring. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
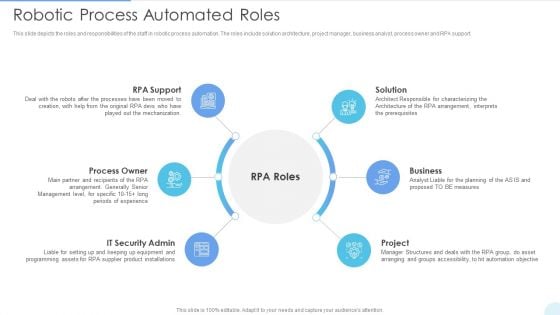
Robotic Process Automated Roles Introduction PDF
This slide depicts the roles and responsibilities of the staff in robotic process automation. The roles include solution architecture, project manager, business analyst, process owner and RPA support. This is a Robotic Process Automated Roles Introduction PDF template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Process Owner, IT Security Admin, Business. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
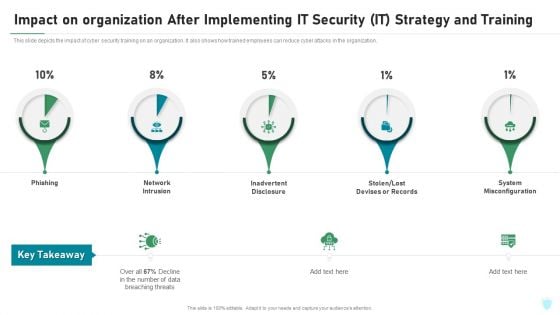
Impact On Organization After Implementing IT Security IT Strategy And Training Ppt File Portrait PDF
This slide depicts the impact of cyber security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Deliver and pitch your topic in the best possible manner with this impact on organization after implementing it security it strategy and training ppt file portrait pdf. Use them to share invaluable insights on phishing, network intrusion, inadvertent disclosure, stolen or lost devises or records, system misconfiguration and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
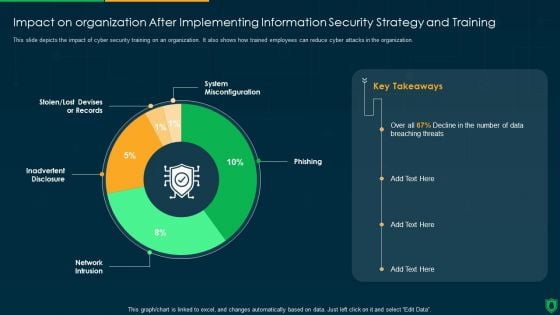
Impact On Organization After Implementing Information Security Strategy Ppt PowerPoint Presentation Gallery Deck PDF
This slide depicts the impact of cyber security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Deliver and pitch your topic in the best possible manner with this impact on organization after implementing information security strategy ppt powerpoint presentation gallery deck pdf. Use them to share invaluable insights on system misconfiguration, phishing, network intrusion, inadvertent disclosure and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
Media Security Ppt PowerPoint Presentation Inspiration File Formats Cpb
This is a media security ppt powerpoint presentation inspiration file formats cpb. This is a three stage process. The stages in this process are media security.
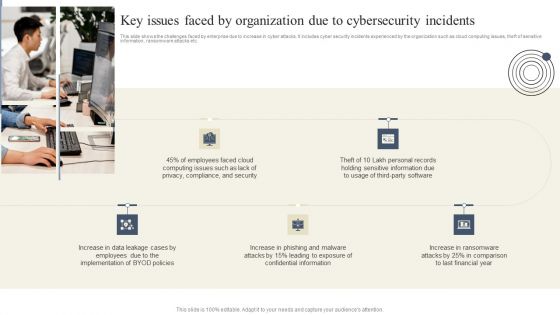
Cyber Security Breache Response Strategy Key Issues Faced By Organization Due To Cybersecurity Incidents Rules PDF
This slide shows the challenges faced by enterprise due to increase in cyber attacks. It includes cyber security incidents experienced by the organization such as cloud computing issues, theft of sensitive information, ransomware attacks etc. Create an editable Cyber Security Breache Response Strategy Key Issues Faced By Organization Due To Cybersecurity Incidents Rules PDF that communicates your idea and engages your audience. Whether youre presenting a business or an educational presentation, pre designed presentation templates help save time. Cyber Security Breache Response Strategy Key Issues Faced By Organization Due To Cybersecurity Incidents Rules PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
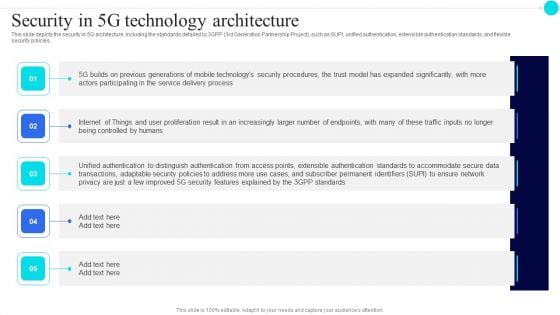
Security In 5G Technology Architecture 5G Functional Architecture Formats PDF
This slide depicts the security in 5G architecture, including the standards detailed by 3GPP 3rd Generation Partnership Project, such as SUPI, unified authentication, extensible authentication standards, and flexible security policies.This is a Security In 5G Technology Architecture 5G Functional Architecture Formats PDF template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Previous Generations, Distinguish Authentication, Transactions Adaptable. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
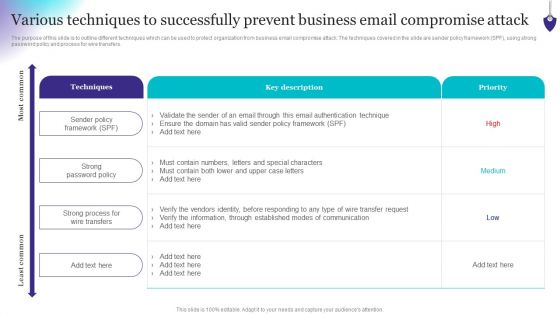
Organizing Security Awareness Various Techniques To Successfully Prevent Business Email Diagrams PDF
The purpose of this slide is to outline different techniques which can be used to protect organization from business email compromise attack. The techniques covered in the slide are sender policy framework SPF, using strong password policy and process for wire transfers. Find a pre-designed and impeccable Organizing Security Awareness Various Techniques To Successfully Prevent Business Email Diagrams PDF. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.

Web Accessibility Validation Diagram Ppt Samples
This is a web accessibility validation diagram ppt samples. This is a four stage process. The stages in this process are strength, weakness, opportunity, threat, business.


 Continue with Email
Continue with Email

 Home
Home


































