Threats PowerPoint Presentation Templates and Google Slides
-
Playbook To Remediate False Agile Threat Modeling Overview About Download Pdf
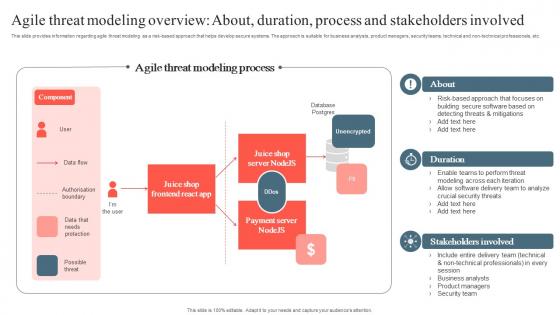
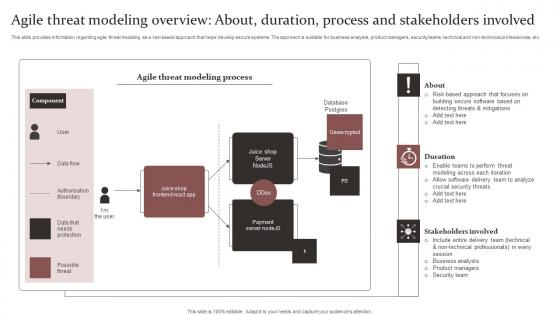
This slide provides information regarding agile threat modeling as a risk based approach that helps develop secure systems. The approach is suitable for business analysts, product managers, security teams, technical and non technical professionals, etc. Want to ace your presentation in front of a live audience Our Playbook To Remediate False Agile Threat Modeling Overview About Download Pdf can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy to edit and downloadable. Use these for both personal and commercial use.
-
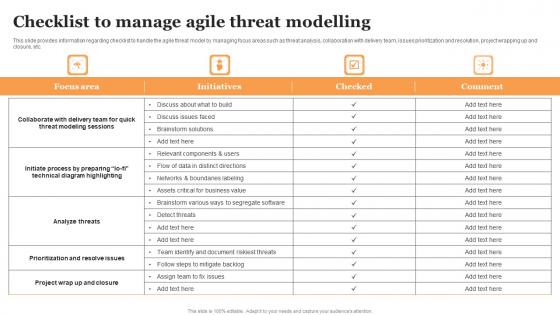
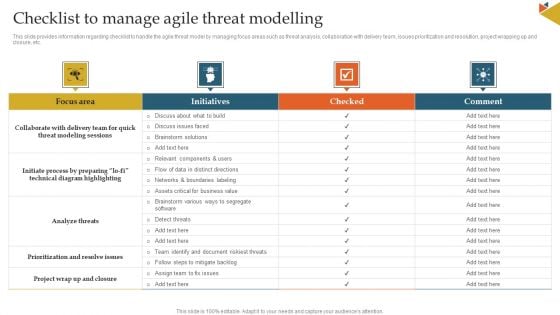
Playbook To Remediate False Checklist To Manage Agile Threat Modelling Download Pdf
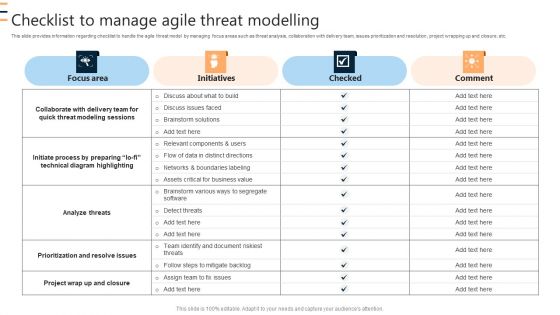
This slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. There are so many reasons you need a Playbook To Remediate False Checklist To Manage Agile Threat Modelling Download Pdf The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
-
Playbook To Remediate False Key Principles Associated With Agile Threat Modelling Professional Pdf
This slide provides information regarding key sustainable, responsible business initiatives in terms of operating responsibly, enhance workplace inclusivity, enable digital inclusivity, promote sustainable innovation, etc. Slidegeeks has constructed Playbook To Remediate False Key Principles Associated With Agile Threat Modelling Professional Pdf after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping off point to explore our content and will give new users an insight into our top notch PowerPoint Templates.
-
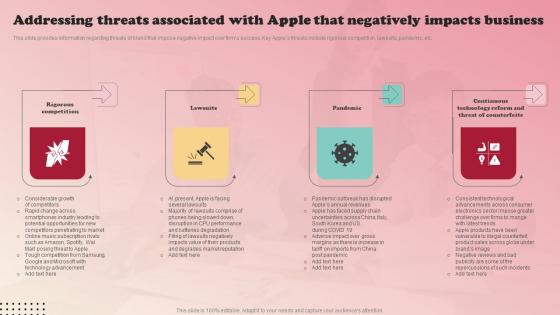
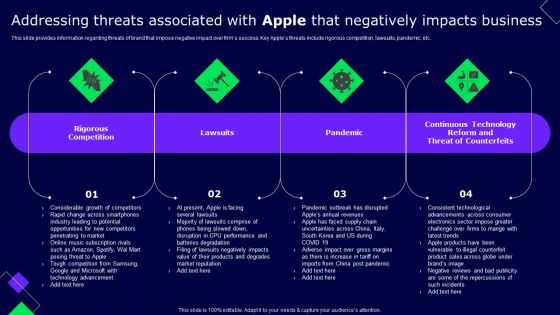
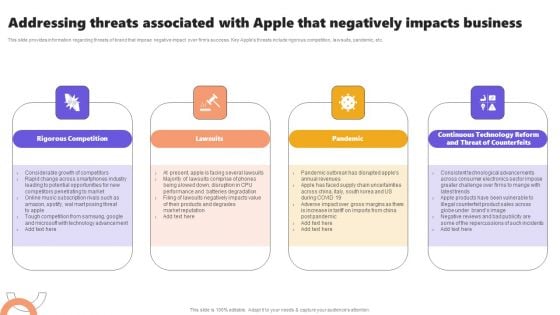
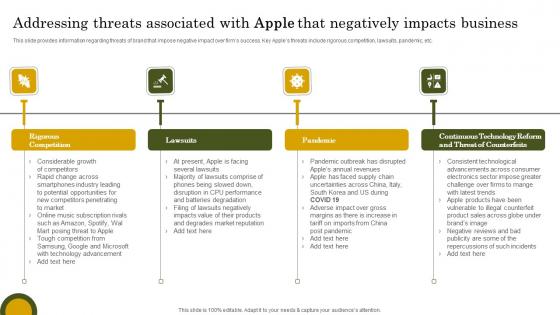
Addressing Threats Associated With Apple Apples Brand Promotional Measures Summary Pdf
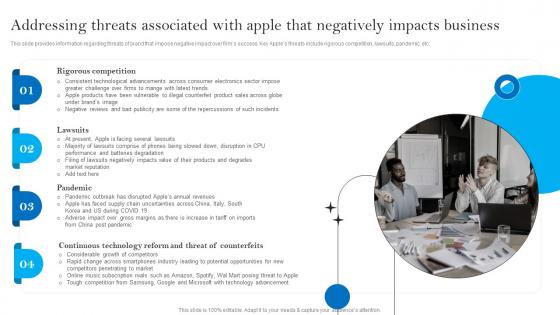
This slide provides information regarding threats of brand that impose negative impact over firm success. Key Apple threats include rigorous competition, lawsuits, pandemic, etc. Find a pre-designed and impeccable Addressing Threats Associated With Apple Apples Brand Promotional Measures Summary Pdf. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
-
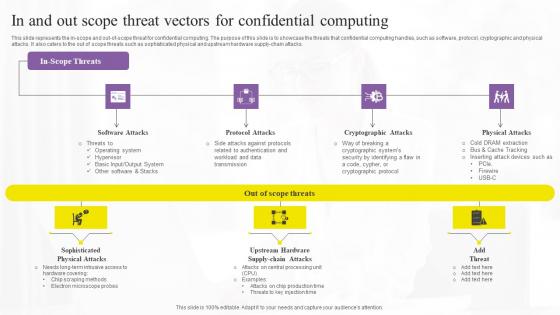
In And Out Scope Threat Vectors For Confidential Computing Secure Multi Party Elements Pdf
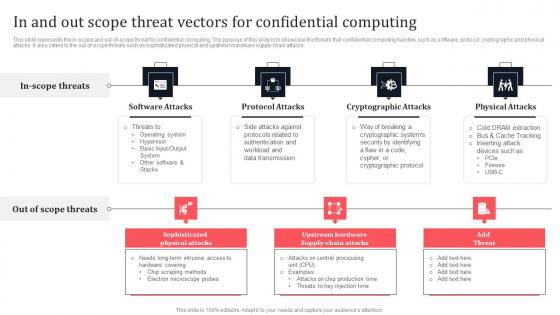
This slide represents the in-scope and out-of-scope threat for confidential computing. The purpose of this slide is to showcase the threats that confidential computing handles, such as software, protocol, cryptographic and physical attacks. It also caters to the out of scope threats such as sophisticated physical and upstream hardware supply-chain attacks. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download In And Out Scope Threat Vectors For Confidential Computing Secure Multi Party Elements Pdf to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the In And Out Scope Threat Vectors For Confidential Computing Secure Multi Party Elements Pdf
-
Product Branding Strategy Of Apple Addressing Threats Associated Download Pdf
This slide provides information regarding threats of brand that impose negative impact over firms success. Key Apples threats include rigorous competition, lawsuits, pandemic, etc. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Product Branding Strategy Of Apple Addressing Threats Associated Download Pdf for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
-
Agile Threat Modeling Overview Responsible Technology Governance Manual Slides Pdf
This slide provides information regarding agile threat modeling as a risk based approach that helps develop secure systems. The approach is suitable for business analysts, product managers, security teams, technical and non technical professionals, etc. Create an editable Agile Threat Modeling Overview Responsible Technology Governance Manual Slides Pdf that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre designed presentation templates help save time. Agile Threat Modeling Overview Responsible Technology Governance Manual Slides Pdf is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
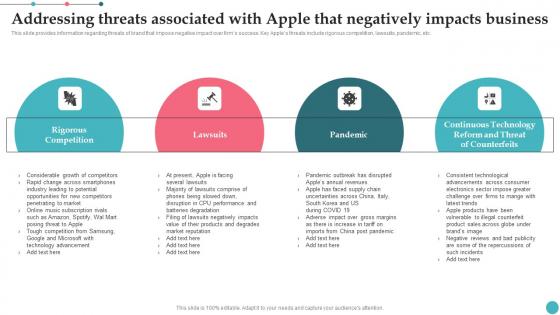
Addressing Threats Associated With Apple That Negatively Impacts Business Rules PDF
Find a pre designed and impeccable Addressing Threats Associated With Apple That Negatively Impacts Business Rules PDF. The templates can ace your presentation without additional effort. You can download these easy to edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
-
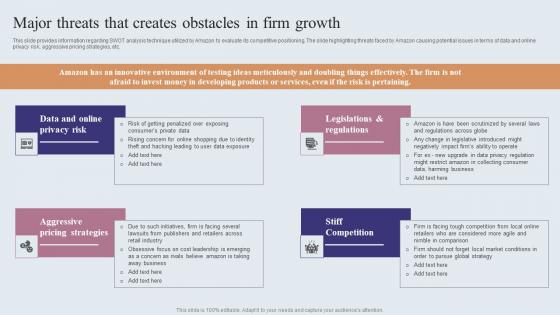
Major Threats That Creates Obstacles In Firm Growth Ppt Icon Portfolio PDF
This slide provides information regarding SWOT analysis technique utilized by Amazon to evaluate its competitive positioning. The slide highlighting threats faced by Amazon causing potential issues in terms of data and online privacy risk, aggressive pricing strategies, etc. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Major Threats That Creates Obstacles In Firm Growth Ppt Icon Portfolio PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.
-
Cyber Threat Prevention Ppt PowerPoint Presentation Complete Deck With Slides
If designing a presentation takes a lot of your time and resources and you are looking for a better alternative, then this Cyber Threat Prevention Ppt PowerPoint Presentation Complete Deck With Slides is the right fit for you. This is a prefabricated set that can help you deliver a great presentation on the topic. All the forteen slides included in this sample template can be used to present a birds-eye view of the topic. These slides are also fully editable, giving you enough freedom to add specific details to make this layout more suited to your business setting. Apart from the content, all other elements like color, design, theme are also replaceable and editable. This helps in designing a variety of presentations with a single layout. Not only this, you can use this PPT design in formats like PDF, PNG, and JPG once downloaded. Therefore, without any further ado, download and utilize this sample presentation as per your liking.
-
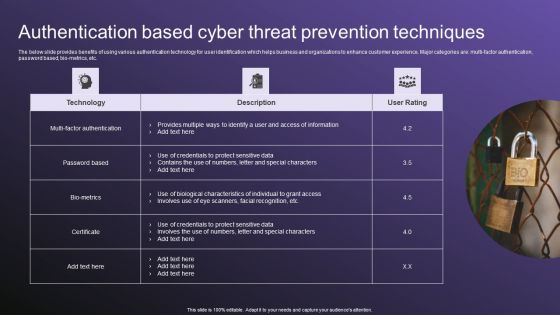
Authentication Based Cyber Threat Prevention Techniques Download PDF
The below slide provides benefits of using various authentication technology for user identification which helps business and organizations to enhance customer experience. Major categories are multi factor authentication, password based, bio-metrics, etc. Showcasing this set of slides titled Authentication Based Cyber Threat Prevention Techniques Download PDF. The topics addressed in these templates are Techniques, Authentication, Threat. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Bio Metrics Technology Icon Promoting Cyber Threat Prevention Designs PDF
Pitch your topic with ease and precision using this Bio Metrics Technology Icon Promoting Cyber Threat Prevention Designs PDF. This layout presents information on Bio Metrics Technology, Promoting Cyber Threat, Prevention. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Blockchain Technology Applications For Cyber Threat Prevention Icons PDF
This slides represents various application of blockchain technology in enhancing cyber safety which helps to speed up data transfer procedures, offer secure transactions, and lower compliance expenses. Key components are IoT security, secure private messaging, etc. Presenting Blockchain Technology Applications For Cyber Threat Prevention Icons PDF to dispense important information. This template comprises six stages. It also presents valuable insights into the topics including Prevention, Infrastructure, System . This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
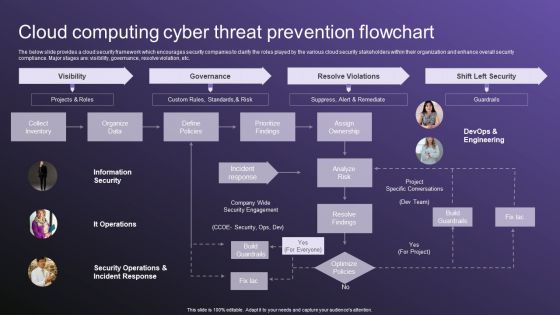
Cloud Computing Cyber Threat Prevention Flowchart Slides PDF
The below slide provides a cloud security framework which encourages security companies to clarify the roles played by the various cloud security stakeholders within their organization and enhance overall security compliance. Major stages are visibility, governance, resolve violation, etc. Showcasing this set of slides titled Cloud Computing Cyber Threat Prevention Flowchart Slides PDF. The topics addressed in these templates are Visibility, Governance, Resolve Violations. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Cyber Security Icon For Cyber Threat Prevention Information PDF
Presenting Cyber Security Icon For Cyber Threat Prevention Information PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Cyber Security, Icon Cyber Threat, Prevention. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
Iot Security Technology For Cyber Threat Prevention Clipart PDF
This slide highlights multiple uses of IoT security technology which helps business to enhance cyber safety of their connected devices. The major elements are device connection, data sensing, communication, data analytics, data value and human value. Persuade your audience using this Iot Security Technology For Cyber Threat Prevention Clipart PDF. This PPT design covers six stages, thus making it a great tool to use. It also caters to a variety of topics including Human Value, Data Value, Data Analytics. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
IT Cyber Threat Prevention Technology Market Topics PDF
This slide provides the statistical data for IT security software user market to help business and organizations enhance process efficiency. Major security technology are authentication, IoT, Zero trust, Cloud, application security, etc. Pitch your topic with ease and precision using this IT Cyber Threat Prevention Technology Market Topics PDF. This layout presents information on Key Insights, Progressive Rate, Technology. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
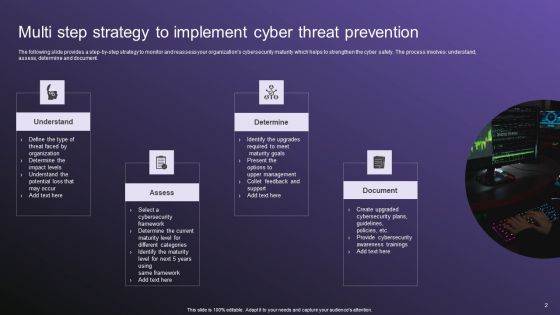
Multi Step Strategy To Implement Cyber Threat Prevention Guidelines PDF
The following slide provides a step by step strategy to monitor and reassess your organizations cybersecurity maturity which helps to strengthen the cyber safety. The process involves understand, assess, determine and document. Persuade your audience using this Multi Step Strategy To Implement Cyber Threat Prevention Guidelines PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Determine, Document, Assess. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
Multiple Challenges Of Business Cyber Threat Prevention Sample PDF
The following slide represent the statistical data of various cyber safety challenges reported by business and organizations which helps to determine the most vulnerable one. Major areas are information security, business agility, automation, integration, etc. Showcasing this set of slides titled Multiple Challenges Of Business Cyber Threat Prevention Sample PDF. The topics addressed in these templates are Key Takeaways, Cyber Safety, Prevention. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Network Security Management For Cyber Threat Prevention Demonstration PDF
This slide exhibits the areas where IT department need to address the network security management in order to reduce errors and promote data security. Major components are deployment, configuration, management, monitor and maintenance. Presenting Network Security Management For Cyber Threat Prevention Demonstration PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Deployment, Management, Configuration. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
SWOT Matrix For Cyber Threat Prevention In Online Gaming Download PDF
This slide provides a matrix to analyse the cyber safety level for online gaming business which helps to address the areas of development. The criteria for evaluation includes strengths, weaknesses, opportunities and threats. Persuade your audience using this SWOT Matrix For Cyber Threat Prevention In Online Gaming Download PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Strengths, Weaknesses, Threats. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
Two Factor Authentication Icon For Cyber Threat Prevention Background PDF
Presenting Two Factor Authentication Icon For Cyber Threat Prevention Background PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Two Factor Authentication, Cyber Threat, Prevention. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
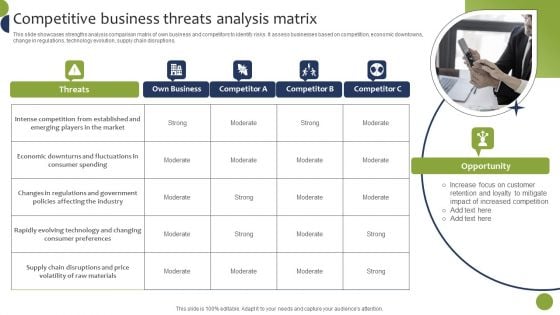
Competitive Business Threats Analysis Matrix Inspiration PDF
This slide showcases strengths analysis comparison matrix of own business and competitors to identify risks. It assess businesses based on competition, economic downtowns, change in regulations, technology evolution, supply chain disruptions. If you are looking for a format to display your unique thoughts, then the professionally designed Competitive Business Threats Analysis Matrix Inspiration PDF is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Competitive Business Threats Analysis Matrix Inspiration PDF and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.
-
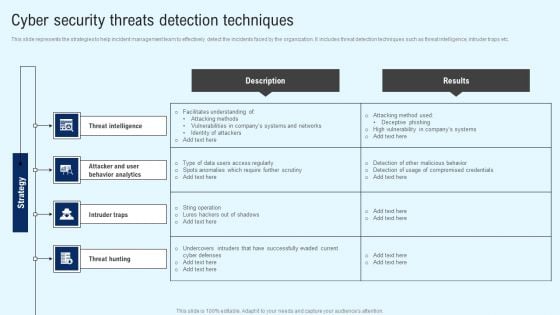
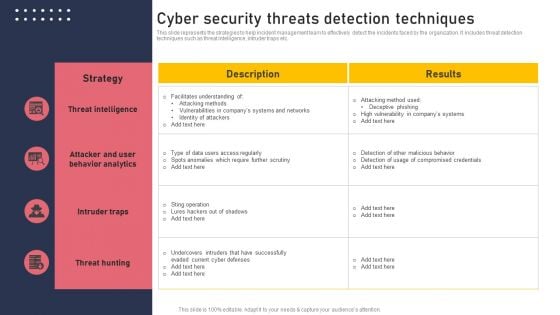
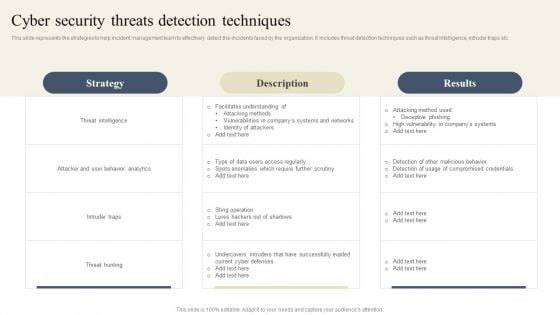
Implementing Cyber Security Incident Cyber Security Threats Detection Techniques Slides PDF
This slide represents the strategies to help incident management team to effectively detect the incidents faced by the organization. It includes threat detection techniques such as threat intelligence, intruder traps etc. Are you searching for a Implementing Cyber Security Incident Cyber Security Threats Detection Techniques Slides PDF that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal. With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Implementing Cyber Security Incident Cyber Security Threats Detection Techniques Slides PDF from Slidegeeks today.
-
Cybersecurity Operations Cybersecops Secops Software Tools Based On Threats Introduction PDF
This slide talks about categorizing primary SecOps software tools based on threats. The purpose of this slide is to showcase the top software solutions for SecOps, including DNS security, network detection and response, anti-phishing, data discovery, and packet-level visibility. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy to edit and customizable templates. Cybersecurity Operations Cybersecops Secops Software Tools Based On Threats Introduction PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.
-
Cybersecurity Operations Cybersecops Security Operations Threat Management Brochure PDF
This slide depicts the security operations threat management process. The purpose of this slide is to showcase the various stages and operations included in the security operations threat management process. The steps include discovery, preliminary investigation, triage, extended investigation, and contain and respond. The Cybersecurity Operations Cybersecops Security Operations Threat Management Brochure PDF is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression.
-
Major Threats That Creates Obstacles In Firm Growth Ideas PDF
This slide provides information regarding SWOT analysis technique utilized by Amazon to evaluate its competitive positioning. The slide highlighting threats faced by Amazon causing potential issues in terms of data and online privacy risk, aggressive pricing strategies, etc. Are you searching for a Major Threats That Creates Obstacles In Firm Growth Ideas PDF that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Major Threats That Creates Obstacles In Firm Growth Ideas PDF from Slidegeeks today.
-
Major Threats That Creates Obstacles In Firm Growth Guidelines PDF
This slide provides information regarding SWOT analysis technique utilized by Amazon to evaluate its competitive positioning. The slide highlighting threats faced by Amazon causing potential issues in terms of data and online privacy risk, aggressive pricing strategies, etc. Are you searching for a Major Threats That Creates Obstacles In Firm Growth Guidelines PDF that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Major Threats That Creates Obstacles In Firm Growth Guidelines PDF from Slidegeeks today.
-
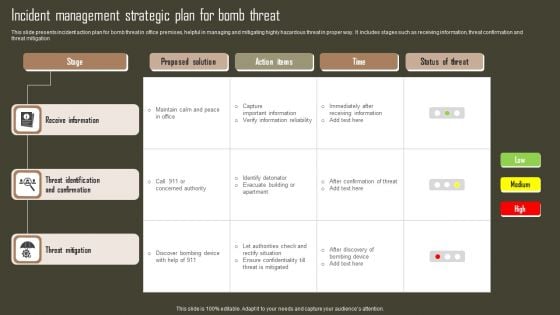
Incident Management Strategic Plan For Bomb Threat Slides PDF
This slide presents incident action plan for bomb threat in office premises, helpful in managing and mitigating highly hazardous threat in proper way. It includes stages such as receiving information, threat confirmation and threat mitigation. Pitch your topic with ease and precision using this Incident Management Strategic Plan For Bomb Threat Slides PDF. This layout presents information on Receive Information, Threat Identification And Confirmation, Threat Mitigation. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
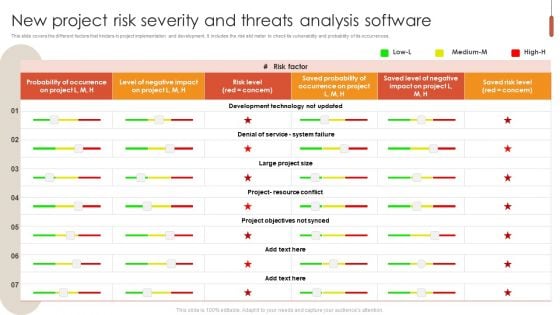
New Project Risk Severity And Threats Analysis Software Information PDF
This slide covers the different factors that hinders in project implementation and development. It includes the risk slid meter to check its vulnerability and probability of its occurrences. Pitch your topic with ease and precision using this New Project Risk Severity And Threats Analysis Software Information PDF. This layout presents information on System Failure, Development Technology, Probability. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Agile Threat Modeling Overview About Duration Process Guide For Ethical Technology Icons Pdf
This slide provides information regarding agile threat modeling as a risk-based approach that helps develop secure systems. The approach is suitable for business analysts, product managers, security teams, technical and non-technical professionals, etc. Create an editable Agile Threat Modeling Overview About Duration Process Guide For Ethical Technology Icons Pdf that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. Agile Threat Modeling Overview About Duration Process Guide For Ethical Technology Icons Pdf is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
Checklist To Manage Agile Threat Modelling Guide For Ethical Technology Brochure Pdf
This slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Checklist To Manage Agile Threat Modelling Guide For Ethical Technology Brochure Pdf for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
-
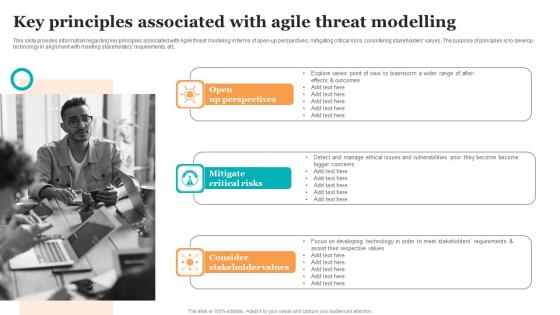
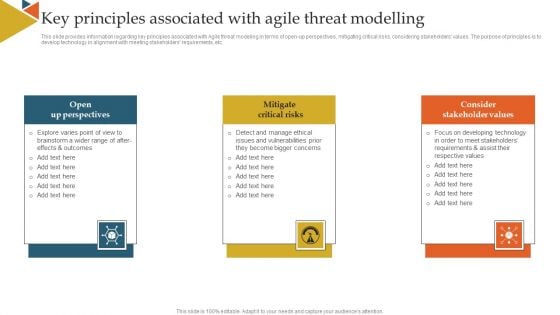
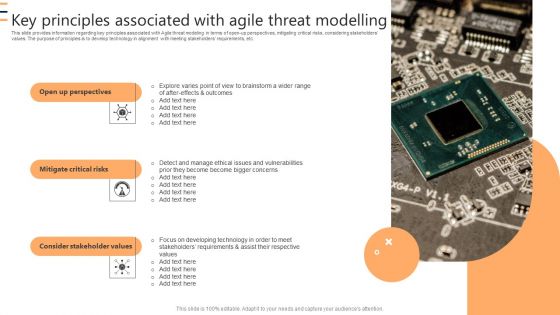
Key Principles Associated With Agile Threat Modelling Guide For Ethical Technology Slides Pdf
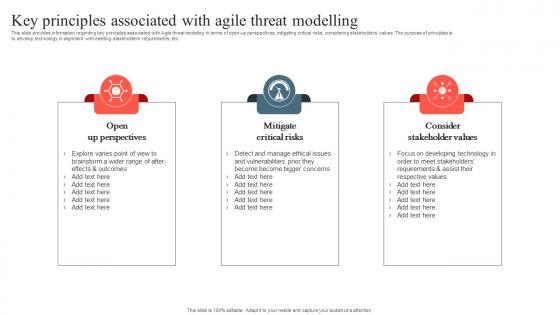
This slide provides information regarding key principles associated with Agile threat modeling in terms of open-up perspectives, mitigating critical risks, considering stakeholders values. The purpose of principles is to develop technology in alignment with meeting stakeholders requirements, etc. Slidegeeks has constructed Key Principles Associated With Agile Threat Modelling Guide For Ethical Technology Slides Pdf after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.
-
Online Risk And Threat Identifying Icon Ideas PDF
Presenting Online Risk And Threat Identifying Icon Ideas PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Online Risk, Threat Identifying Icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
Online Risk Management Dashboard For Tracking Threats And Attacks Icons PDF
The purpose of this slide is to represent dashboard to monitor risks and cyber threats for efficient risk management. It includes various types of key performance indicators such as types of risks, severities, sources and risk meter. Showcasing this set of slides titled Online Risk Management Dashboard For Tracking Threats And Attacks Icons PDF. The topics addressed in these templates are Attack, Indication Severities, Sources. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Addressing Threats Associated With Apple That Negatively Impacts Business Ideas PDF
This slide provides information regarding threats of brand that impose negative impact over firms success. Key Apples threats include rigorous competition, lawsuits, pandemic, etc. Find a pre designed and impeccable Addressing Threats Associated With Apple That Negatively Impacts Business Ideas PDF. The templates can ace your presentation without additional effort. You can download these easy to edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
-
Apples Strategy To Achieve Top Brand Value Position Addressing Threats Associated With Apple That Negatively Clipart PDF
This slide provides information regarding threats of brand that impose negative impact over firms success. Key Apples threats include rigorous competition, lawsuits, pandemic, etc. Boost your pitch with our creative Apples Strategy To Achieve Top Brand Value Position Addressing Threats Associated With Apple That Negatively Clipart PDF. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
-
Cyber Security Threats Detection Techniques Demonstration PDF
This slide represents the strategies to help incident management team to effectively detect the incidents faced by the organization. It includes threat detection techniques such as threat intelligence, intruder traps etc. Create an editable Cyber Security Threats Detection Techniques Demonstration PDF that communicates your idea and engages your audience. Whether youre presenting a business or an educational presentation, pre designed presentation templates help save time. Cyber Security Threats Detection Techniques Demonstration PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
CYBER Security Breache Response Strategy Cyber Security Threats Detection Techniques Diagrams PDF
This slide represents the strategies to help incident management team to effectively detect the incidents faced by the organization. It includes threat detection techniques such as threat intelligence, intruder traps etc. The best PPT templates are a great way to save time, energy, and resources. Slidegeeks have 100 percent editable powerpoint slides making them incredibly versatile. With these quality presentation templates, you can create a captivating and memorable presentation by combining visually appealing slides and effectively communicating your message. Download CYBER Security Breache Response Strategy Cyber Security Threats Detection Techniques Diagrams PDF from Slidegeeks and deliver a wonderful presentation.
-
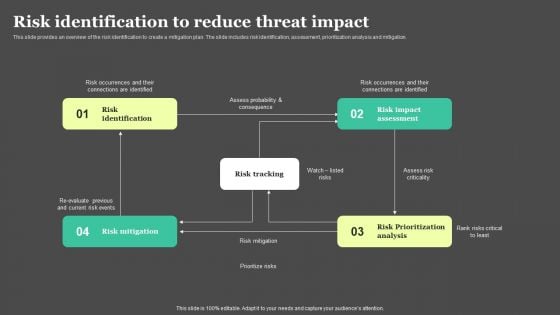
Risk Detection And Management Risk Identification To Reduce Threat Impact Background PDF
This slide provides an overview of the risk identification to create a mitigation plan. The slide includes risk identification, assessment, prioritization analysis and mitigation. Do you know about Slidesgeeks Risk Detection And Management Risk Identification To Reduce Threat Impact Background PDF These are perfect for delivering any kind od presentation. Using it, create PowerPoint presentations that communicate your ideas and engage audiences. Save time and effort by using our pre-designed presentation templates that are perfect for a wide range of topic. Our vast selection of designs covers a range of styles, from creative to business, and are all highly customizable and easy to edit. Download as a PowerPoint template or use them as Google Slides themes.
-
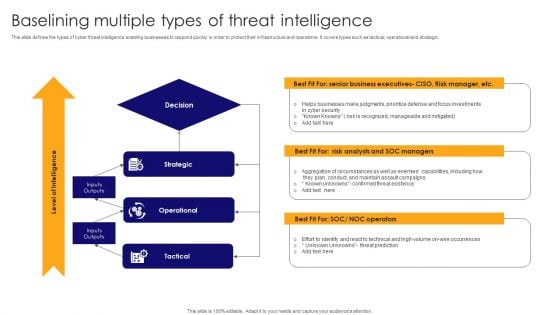
Baselining Multiple Types Of Threat Intelligence Pictures PDF
This slide defines the types of cyber threat intelligence enabling businesses to respond quickly in order to protect their infrastructure and operations. It covers types such as tactical, operational and strategic. Presenting Baselining Multiple Types Of Threat Intelligence Pictures PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Strategic, Operational, Tactical . This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
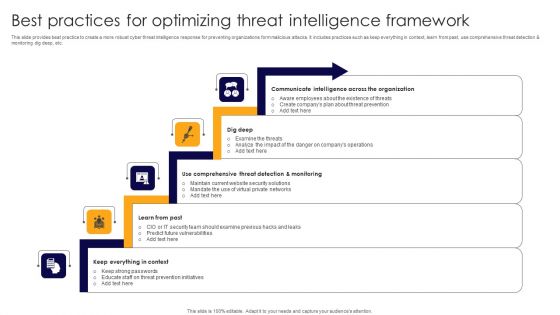
Best Practices For Optimizing Threat Intelligence Framework Formats PDF
This slide provides beat practice to create a more robust cyber threat intelligence response for preventing organizations form malicious attacks. It includes practices such as keep everything in context, learn from past, use comprehensive threat detection and monitoring dig deep, etc. Presenting Best Practices For Optimizing Threat Intelligence Framework Formats PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Communicate Intelligence, Dig Deep, Comprehensive Threat Detection. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
Building An Effective Threat Intelligence Framework Icons PDF
This slide showcases steps to create a framework for effective cyber threat intelligence that will help prevent firms from cyber threats. It includes steps such as scope definition, defines specific goals, cyber threat intelligence tools and continuous refinement. Presenting Building An Effective Threat Intelligence Framework Icons PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Scope Definition, Define Specific Goals, Cyber Threat Intelligence Tools. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
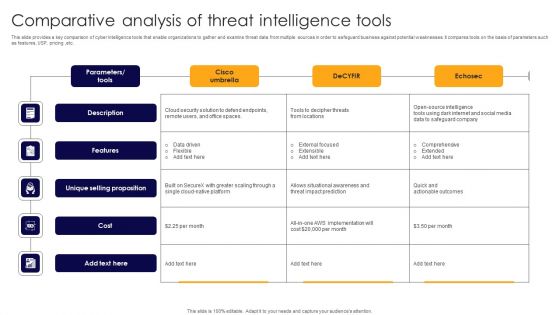
Comparative Analysis Of Threat Intelligence Tools Rules PDF
This slide provides a key comparison of cyber intelligence tools that enable organizations to gather and examine threat data from multiple sources in order to safeguard business against potential weaknesses. It compares tools on the basis of parameters such as features, USP, pricing ,etc. Showcasing this set of slides titled Comparative Analysis Of Threat Intelligence Tools Rules PDF. The topics addressed in these templates are Description, Features, Unique Selling Proposition. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
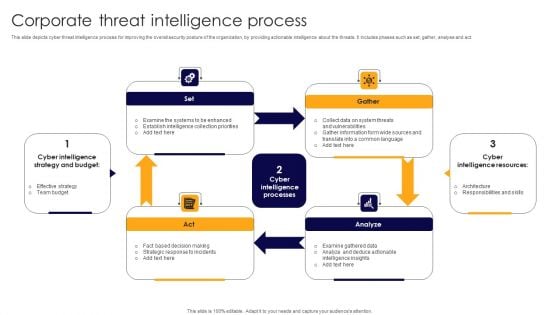
Corporate Threat Intelligence Process Demonstration PDF
This slide depicts cyber threat intelligence process for improving the overall security posture of the organization, by providing actionable intelligence about the threats. It includes phases such as set, gather, analyse and act. Presenting Corporate Threat Intelligence Process Demonstration PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Fact Based Decision Making, Strategic Response Incidents, Collect Data System. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
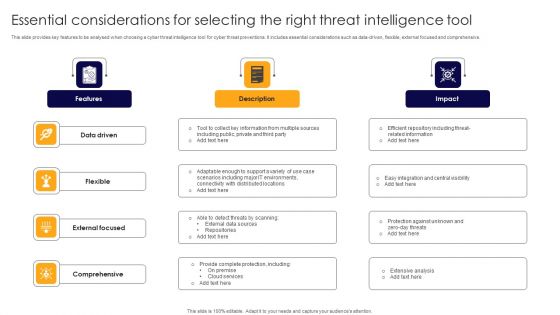
Essential Considerations For Selecting The Right Threat Intelligence Tool Themes PDF
This slide provides key features to be analysed when choosing a cyber threat intelligence tool for cyber threat preventions. It includes essential considerations such as data-driven, flexible, external focused and comprehensive. Presenting Essential Considerations For Selecting The Right Threat Intelligence Tool Themes PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Data Driven, Flexible, External Focused. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
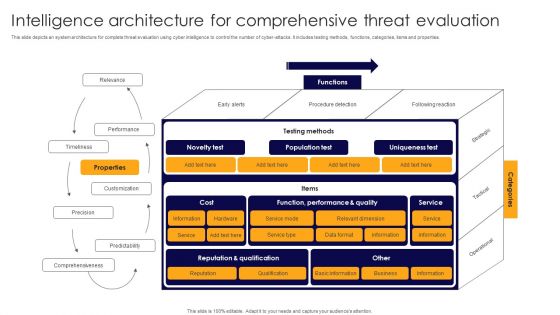
Intelligence Architecture For Comprehensive Threat Evaluation Mockup PDF
This slide depicts an system architecture for complete threat evaluation using cyber intelligence to control the number of cyber-attacks. It includes testing methods, functions, categories, items and properties. Showcasing this set of slides titled Intelligence Architecture For Comprehensive Threat Evaluation Mockup PDF. The topics addressed in these templates are Performance, Timeliness, Customization. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Intelligence Initiatives For Threat Prevention Icon Elements PDF
Presenting Intelligence Initiatives For Threat Prevention Icon Elements PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Intelligence Initiatives, Threat Prevention Icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
Threat Intelligence And AI Technology Icon Sample PDF
Presenting Threat Intelligence And AI Technology Icon Sample PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Threat Intelligence, Ai Technology Icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
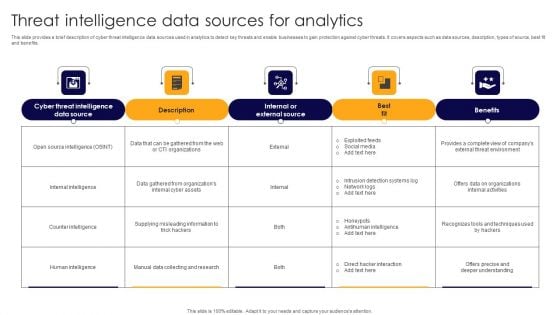
Threat Intelligence Data Sources For Analytics Ideas PDF
This slide provides a brief description of cyber threat intelligence data sources used in analytics to detect key threats and enable businesses to gain protection against cyber threats. It covers aspects such as data sources, description, types of source, best fit and benefits. Showcasing this set of slides titled Threat Intelligence Data Sources For Analytics Ideas PDF. The topics addressed in these templates are Exploited Feeds, Social Media, Intrusion Detection Systems Log. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Threat Intelligence Framework For Banks Icon Designs PDF
Showcasing this set of slides titled Threat Intelligence Framework For Banks Icon Designs PDF. The topics addressed in these templates are Threat Intelligence, Framework Banks Icon. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
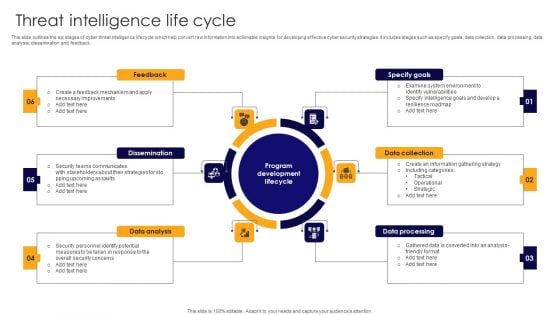
Threat Intelligence Life Cycle Elements PDF
Presenting Threat Intelligence Life Cycle Elements PDF to dispense important information. This template comprises six stages. It also presents valuable insights into the topics including Feedback, Dissemination, Data Collection. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
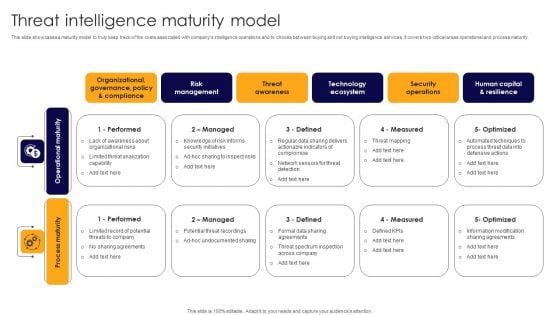
Threat Intelligence Maturity Model Professional PDF
This slide showcases a maturity model to truly keep track of the costs associated with companys intelligence operations and to choose between buying and not buying intelligence services. It covers two critical areas operational and process maturity. Presenting Threat Intelligence Maturity Model Professional PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Performed, Managed, Defined. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
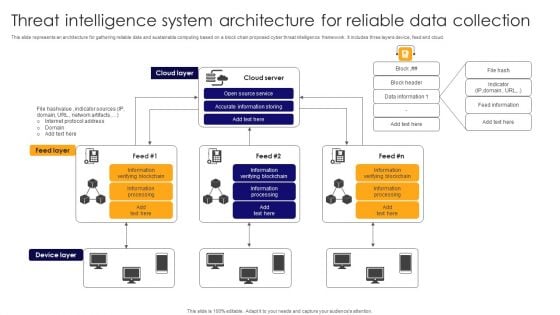
Threat Intelligence System Architecture For Reliable Data Collection Pictures PDF
This slide represents an architecture for gathering reliable data and sustainable computing based on a block chain proposed cyber threat intelligence framework . It includes three layers device, feed and cloud. Showcasing this set of slides titled Threat Intelligence System Architecture For Reliable Data Collection Pictures PDF. The topics addressed in these templates are Cloud Server, Accurate Information Storing, Open Source Service. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
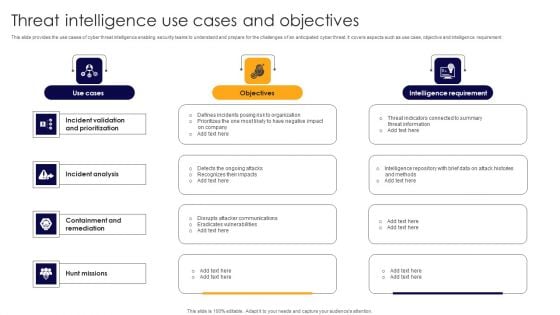
Threat Intelligence Use Cases And Objectives Demonstration PDF
This slide provides the use cases of cyber threat intelligence enabling security teams to understand and prepare for the challenges of an anticipated cyber threat. It covers aspects such as use case, objective and intelligence requirement. Presenting Threat Intelligence Use Cases And Objectives Demonstration PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Incident Analysis, Containment Remediation, Hunt Missions. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
Threat Security Before And After Artificial Intelligence Formats PDF
This slide describes the four main cyber risks that currently threaten our digital world, as well as the difference between traditional methods and newer, AI based methods. It includes cyber threats such as malware, DDoS, IOT and endpoints and social engineering. Showcasing this set of slides titled Threat Security Before And After Artificial Intelligence Formats PDF. The topics addressed in these templates are Malware, Distributed Denial Service, Social Engineering. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Assessment Of Amazon Brand Performance Major Threats That Creates Obstacles Brochure PDF
This slide provides information regarding SWOT analysis technique utilized by Amazon to evaluate its competitive positioning. The slide highlighting threats faced by Amazon causing potential issues in terms of data and online privacy risk, aggressive pricing strategies, etc. Want to ace your presentation in front of a live audience Our Assessment Of Amazon Brand Performance Major Threats That Creates Obstacles Brochure PDF can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy-to-edit and downloadable. Use these for both personal and commercial use.
-
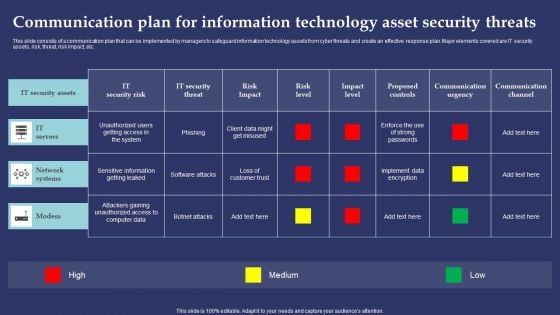
Communication Plan For Information Technology Asset Security Threats Pictures PDF
This slide consists of a communication plan that can be implemented by managers to safeguard information technology assets from cyber threats and create an effective response plan. Major elements covered are IT security assets, risk, threat, risk impact, etc. Showcasing this set of slides titled Communication Plan For Information Technology Asset Security Threats Pictures PDF. The topics addressed in these templates are ZZZZZZZZZZZZZZZZZZZZIT Servers, Network Systems, ModemZZZZZZZZZZZZZ. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Key Principles Associated With Agile Threat Modelling Ppt Infographics Pictures PDF
This slide provides information regarding key principles associated with Agile threat modeling in terms of open-up perspectives, mitigating critical risks, considering stakeholders values. The purpose of principles is to develop technology in alignment with meeting stakeholders requirements, etc. The Key Principles Associated With Agile Threat Modelling Ppt Infographics Pictures PDF is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression.
-
Agile Threat Modeling Overview About Duration Process And Stakeholders Involved Ppt Pictures Graphics Template PDF
This slide provides information regarding agile threat modeling as a risk-based approach that helps develop secure systems. The approach is suitable for business analysts, product managers, security teams, technical and non-technical professionals, etc. Boost your pitch with our creative Agile Threat Modeling Overview About Duration Process And Stakeholders Involved Ppt Pictures Graphics Template PDF. Deliver an awe inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
-
Checklist To Manage Agile Threat Modelling Ppt Show Template PDF
This slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. Create an editable Checklist To Manage Agile Threat Modelling Ppt Show Template PDF that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre designed presentation templates help save time. Checklist To Manage Agile Threat Modelling Ppt Show Template PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
Key Principles Associated With Agile Threat Modelling Ppt Summary Picture PDF
This slide provides information regarding key principles associated with Agile threat modeling in terms of open-up perspectives, mitigating critical risks, considering stakeholders values. The purpose of principles is to develop technology in alignment with meeting stakeholders requirements, etc. The Key Principles Associated With Agile Threat Modelling Ppt Summary Picture PDF is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression.
-
Microsoft Strategic Plan To Become Market Leader Potential Future Threats To Microsoft Corporations Slides PDF
This slide shows four major threats to microsoft in coming years which can effect Microsoft adversely in terms of revenues as well as brand image. It includes competition, changing customer needs, open sources projects and potential lawsuits. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Microsoft Strategic Plan To Become Market Leader Potential Future Threats To Microsoft Corporations Slides PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.
-
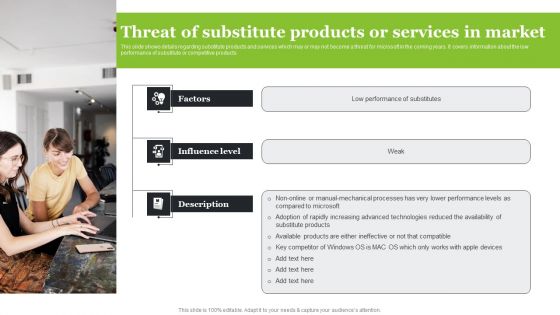
Microsoft Strategic Plan To Become Market Leader Threat Of Substitute Products Or Services In Market Structure PDF
This slide shows details regarding substitute products and services which may or may not become a threat for microsoft in the coming years. It covers information about the low performance of substitute or competitive products. Slidegeeks has constructed Microsoft Strategic Plan To Become Market Leader Threat Of Substitute Products Or Services In Market Structure PDF after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.
-
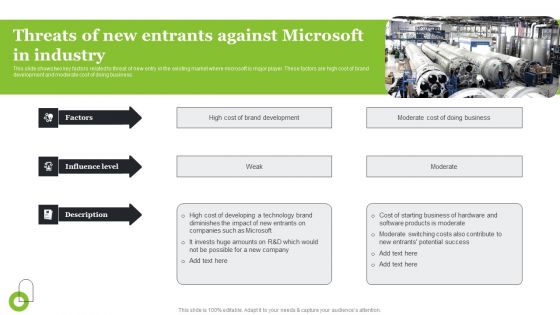
Microsoft Strategic Plan To Become Market Leader Threats Of New Entrants Against Microsoft In Industry Themes PDF
This slide shows two key factors related to threat of new entry in the existing market where microsoft is major player. These factors are high cost of brand development and moderate cost of doing business. Presenting this PowerPoint presentation, titled Microsoft Strategic Plan To Become Market Leader Threats Of New Entrants Against Microsoft In Industry Themes PDF, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Microsoft Strategic Plan To Become Market Leader Threats Of New Entrants Against Microsoft In Industry Themes PDF. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Microsoft Strategic Plan To Become Market Leader Threats Of New Entrants Against Microsoft In Industry Themes PDF that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.
-
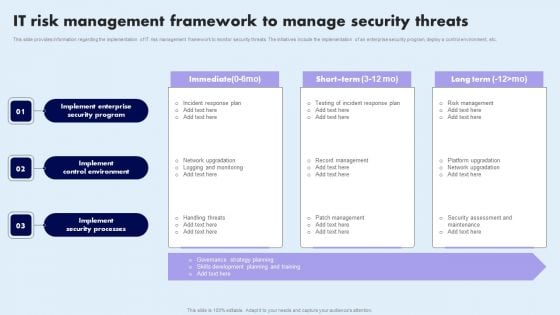
IT Risk Management Framework To Manage Security Threats Summary PDF
This slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Retrieve professionally designed IT Risk Management Framework To Manage Security Threats Summary PDF to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.
-
Risk Management Plan To Manage Cyber Threats Summary PDF
This slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. There are so many reasons you need a Risk Management Plan To Manage Cyber Threats Summary PDF. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
-
Agile Threat Modeling Overview About Duration Process And Stakeholders Involved Ppt Pictures Structure PDF
This slide provides information regarding agile threat modeling as a risk-based approach that helps develop secure systems. The approach is suitable for business analysts, product managers, security teams, technical and non-technical professionals, etc. Boost your pitch with our creative Agile Threat Modeling Overview About Duration Process And Stakeholders Involved Ppt Pictures Structure PDF. Deliver an awe inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
-
Checklist To Manage Agile Threat Modelling Ppt File Demonstration PDF
This slide provides information regarding checklist to handle the agile threat model by managing focus areas such as threat analysis, collaboration with delivery team, issues prioritization and resolution, project wrapping up and closure, etc. Create an editable Checklist To Manage Agile Threat Modelling Ppt File Demonstration PDF that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre designed presentation templates help save time. Checklist To Manage Agile Threat Modelling Ppt File Demonstration PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
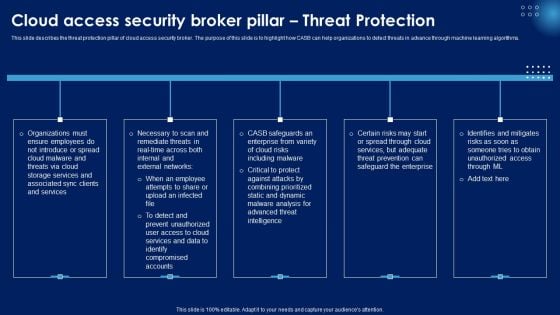
Cloud Access Security Broker Pillar Threat Protection Ppt PowerPoint Presentation File Pictures PDF
This slide describes the threat protection pillar of cloud access security broker. The purpose of this slide is to highlight how CASB can help organizations to detect threats in advance through machine learning algorithms. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Cloud Access Security Broker Pillar Threat Protection Ppt PowerPoint Presentation File Pictures PDF can be your best option for delivering a presentation. Represent everything in detail using Cloud Access Security Broker Pillar Threat Protection Ppt PowerPoint Presentation File Pictures PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.
-
Emerging Cloud Security Risks And Threats Ppt PowerPoint Presentation File Diagrams PDF
This slide represents the emerging cloud security risks, and threats organizations can encounter. The purpose of this slide is to highlight the various threats that CASB deployment can help overcome, including VPNs, system misconfiguration, non-zero security permissions, and so on. Slidegeeks is here to make your presentations a breeze with Emerging Cloud Security Risks And Threats Ppt PowerPoint Presentation File Diagrams PDF With our easy to use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.
-
Business Threat Organizational Prevention Based Strategy Icon Pictures PDF
Introducing Business Threat Organizational Prevention Based Strategy Icon Pictures PDF. to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Business Threat Organizational, Prevention Based Strategy, using this template. Grab it now to reap its full benefits.
-
Cyber Threat Organizational Prevention Based Strategy Icon Graphics PDF
Increase audience engagement and knowledge by dispensing information using Cyber Threat Organizational Prevention Based Strategy Icon Graphics PDF. This template helps you present information on three stages. You can also present information on Cyber Threat Organizational, Prevention Based Strategy Icon using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
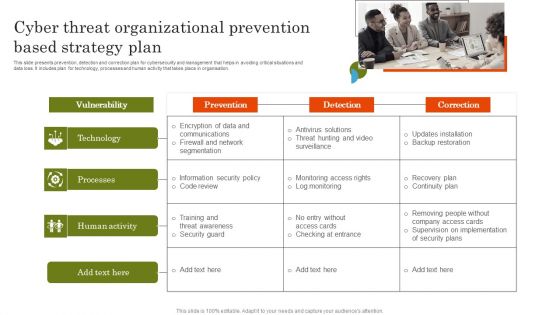
Cyber Threat Organizational Prevention Based Strategy Plan Template PDF
This slide presents prevention, detection and correction plan for cybersecurity and management that helps in avoiding critical situations and data loss. It includes plan for technology, processes and human activity that takes place in organisation. Introducing Cyber Threat Organizational Prevention Based Strategy Plan Template PDF. to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Processes, Human Activity, using this template. Grab it now to reap its full benefits.
-
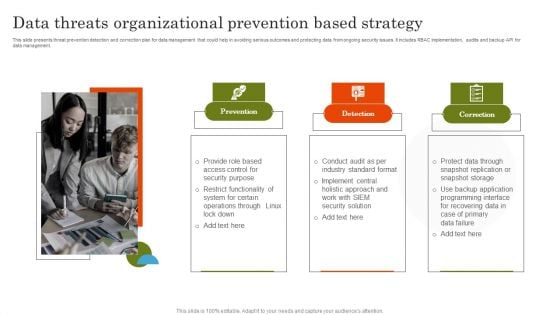
Data Threats Organizational Prevention Based Strategy Infographics PDF
This slide presents threat prevention detection and correction plan for data management that could help in avoiding serious outcomes and protecting data from ongoing security issues. It includes RBAC implementation, audits and backup API for data management. Increase audience engagement and knowledge by dispensing information using Data Threats Organizational Prevention Based Strategy Infographics PDF. This template helps you present information on three stages. You can also present information on Prevention, Detection, Correction using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
Organizational Prevention Based Strategy For Insider Threats Inspiration PDF
This slide presents prevention detection and correction plan for insider threats faced by companies that could help in determining potential vulnerabilities. It includes source, threat, risk, motivation, domain, indicators, protective, detective and corrective controls. Introducing Organizational Prevention Based Strategy For Insider Threats Inspiration PDF. to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Employee Statements, Physical Associations, Background Check, using this template. Grab it now to reap its full benefits.
-
System Threat Organizational Prevention Based Strategy Guidelines PDF
Present the topic in a bit more detail with this System Threat Organizational Prevention Based Strategy Guidelines PDF. Use it as a tool for discussion and navigation on System Threat Organizational, Prevention Based Strategy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
Addressing Threats Associated Apple Brand Story Journey Of Iconic Enterprise Ideas Pdf
This slide provides information regarding threats of brand that impose negative impact over firms success. Key Apples threats include rigorous competition, lawsuits, pandemic, etc. Find a pre designed and impeccable Addressing Threats Associated Apple Brand Story Journey Of Iconic Enterprise Ideas Pdf. The templates can ace your presentation without additional effort. You can download these easy to edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
-
Major Threats That Creates Obstacles In Firm Growth Amazons Journey For Becoming Ideas PDF
This slide provides information regarding SWOT analysis technique utilized by Amazon to evaluate its competitive positioning. The slide highlighting threats faced by Amazon causing potential issues in terms of data and online privacy risk, aggressive pricing strategies, etc. Presenting this PowerPoint presentation, titled Major Threats That Creates Obstacles In Firm Growth Amazons Journey For Becoming Ideas PDF with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Major Threats That Creates Obstacles In Firm Growth Amazons Journey For Becoming Ideas PDF Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Major Threats That Creates Obstacles In Firm Growth Amazons Journey For Becoming Ideas PDF that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.
-
Major Threats That Creates Exploring Amazons Global Business Model Growth Guidelines Pdf
This slide provides information regarding SWOT analysis technique utilized by Amazon to evaluate its competitive positioning. The slide highlighting threats faced by Amazon causing potential issues in terms of data and online privacy risk, aggressive pricing strategies, etc. Presenting this PowerPoint presentation, titled Major Threats That Creates Exploring Amazons Global Business Model Growth Guidelines Pdf, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Major Threats That Creates Exploring Amazons Global Business Model Growth Guidelines Pdf. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Major Threats That Creates Exploring Amazons Global Business Model Growth Guidelines Pdf that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.
-
Addressing Threats Associated Apple Branding Strategy To Become Market Leader Themes Pdf
This slide provides information regarding threats of brand that impose negative impact over firms success. Key Apples threats include rigorous competition, lawsuits, pandemic, etc. Find a pre designed and impeccable Addressing Threats Associated Apple Branding Strategy To Become Market Leader Themes Pdf. The templates can ace your presentation without additional effort. You can download these easy to edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
-
In And Out Scope Threat Vectors For Confidential Computing Technologies Infographics Pdf
This slide represents the in-scope and out-of-scope threat for confidential computing. The purpose of this slide is to showcase the threats that confidential computing handles, such as software, protocol, cryptographic and physical attacks. It also caters to the out of scope threats such as sophisticated physical and upstream hardware supply-chain attacks. Are you searching for a In And Out Scope Threat Vectors For Confidential Computing Technologies Infographics Pdf that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download In And Out Scope Threat Vectors For Confidential Computing Technologies Infographics Pdf from Slidegeeks today.
-
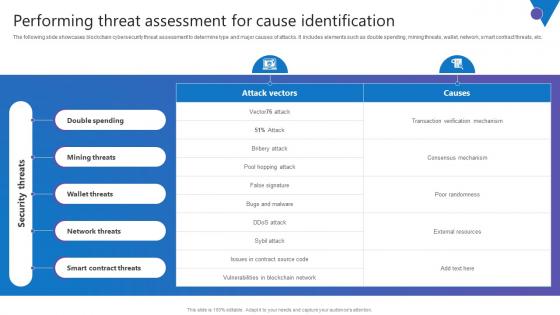
Performing Threat Assessment Comprehensive Guide To Blockchain Digital Security Professional Pdf
The following slide showcases blockchain cybersecurity threat assessment to determine type and major causes of attacks. It includes elements such as double spending, mining threats, wallet, network, smart contract threats, etc. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye catching visual experience. Download Performing Threat Assessment Comprehensive Guide To Blockchain Digital Security Professional Pdf to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high quality content for you. Later on, you can personalize the content by editing the Performing Threat Assessment Comprehensive Guide To Blockchain Digital Security Professional Pdf.
-
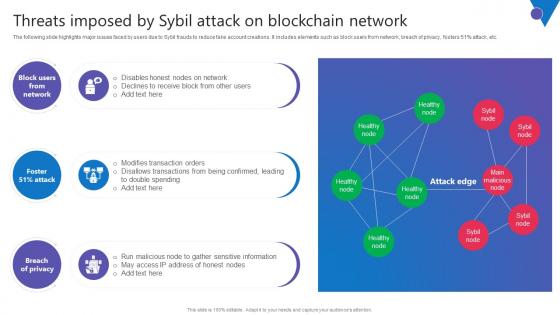
Threats Imposed By Sybil Attack Comprehensive Guide To Blockchain Digital Security Introduction Pdf
The following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Threats Imposed By Sybil Attack Comprehensive Guide To Blockchain Digital Security Introduction Pdf for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
-
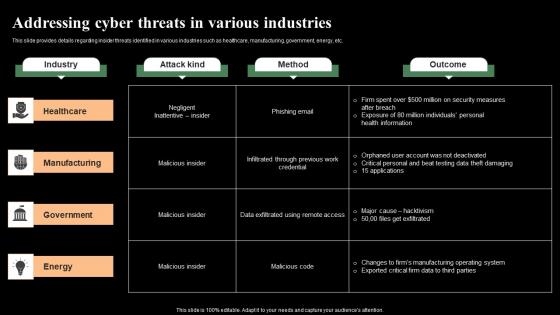
Addressing Cyber Threats In Various Industries Monitoring Digital Assets Designs Pdf
This slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Slidegeeks has constructed Addressing Cyber Threats In Various Industries Monitoring Digital Assets Designs Pdf after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.
-
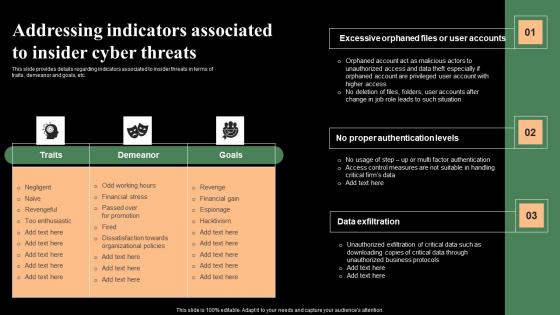
Addressing Indicators Associated To Insider Cyber Threats Monitoring Digital Assets Themes Pdf
This slide provides details regarding indicators associated to insider threats in terms of traits, demeanor and goals, etc. Presenting this PowerPoint presentation, titled Addressing Indicators Associated To Insider Cyber Threats Monitoring Digital Assets Themes Pdf with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Addressing Indicators Associated To Insider Cyber Threats Monitoring Digital Assets Themes Pdf Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Addressing Indicators Associated To Insider Cyber Threats Monitoring Digital Assets Themes Pdf that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.
-
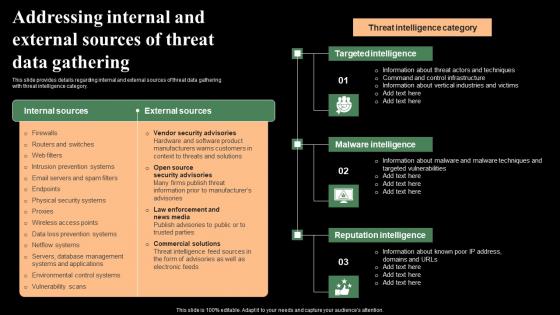
Addressing Internal And External Sources Of Threat Data Monitoring Digital Assets Demonstration Pdf
This slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download Addressing Internal And External Sources Of Threat Data Monitoring Digital Assets Demonstration Pdf to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the Addressing Internal And External Sources Of Threat Data Monitoring Digital Assets Demonstration Pdf
-
Addressing Various Ways To Handle Insider Cyber Threats Monitoring Digital Assets Slides Pdf
This slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. This Addressing Various Ways To Handle Insider Cyber Threats Monitoring Digital Assets Slides Pdf from Slidegeeks makes it easy to present information on your topic with precision. It provides customization options, so you can make changes to the colors, design, graphics, or any other component to create a unique layout. It is also available for immediate download, so you can begin using it right away. Slidegeeks has done good research to ensure that you have everything you need to make your presentation stand out. Make a name out there for a brilliant performance.
-
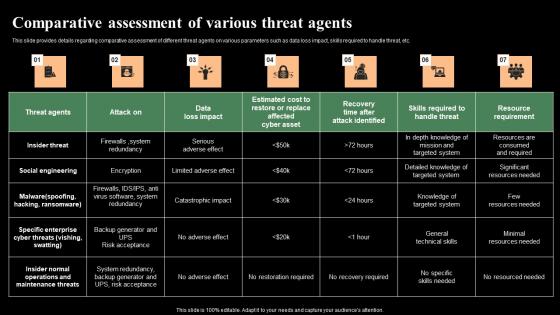
Comparative Assessment Of Various Threat Agents Monitoring Digital Assets Sample Pdf
This slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Find a pre-designed and impeccable Comparative Assessment Of Various Threat Agents Monitoring Digital Assets Sample Pdf The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
-
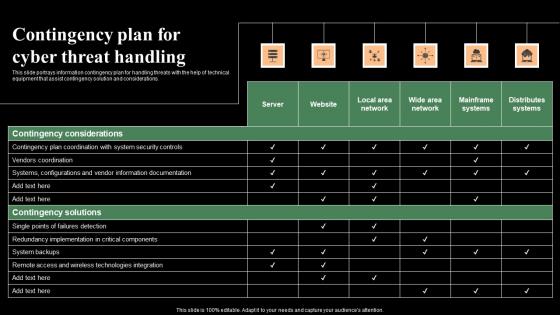
Contingency Plan For Cyber Threat Handling Monitoring Digital Assets Formats Pdf
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Boost your pitch with our creative Contingency Plan For Cyber Threat Handling Monitoring Digital Assets Formats Pdf Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
-
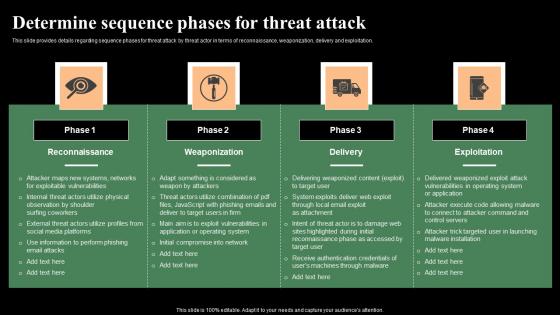
Determine Sequence Phases For Threat Attack Monitoring Digital Assets Infographics Pdf
This slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Create an editable Determine Sequence Phases For Threat Attack Monitoring Digital Assets Infographics Pdf that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. Determine Sequence Phases For Threat Attack Monitoring Digital Assets Infographics Pdf is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
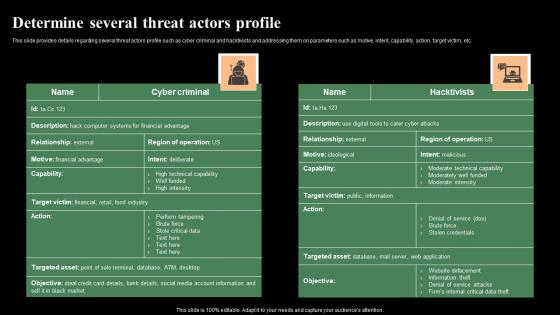
Determine Several Threat Actors Profile Monitoring Digital Assets Topics Pdf
This slide provides details regarding several threat actors profile such as cyber criminal and hacktivists and addressing them on parameters such as motive, intent, capability, action, target victim, etc. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Determine Several Threat Actors Profile Monitoring Digital Assets Topics Pdf for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
-
Determine Threat Scenario Analysis Monitoring Digital Assets Icons Pdf
This slide provides details regarding threat scenario assessment by understanding various phases of threat actor attack on victim. Want to ace your presentation in front of a live audience Our Determine Threat Scenario Analysis Monitoring Digital Assets Icons Pdf can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy-to-edit and downloadable. Use these for both personal and commercial use.
-
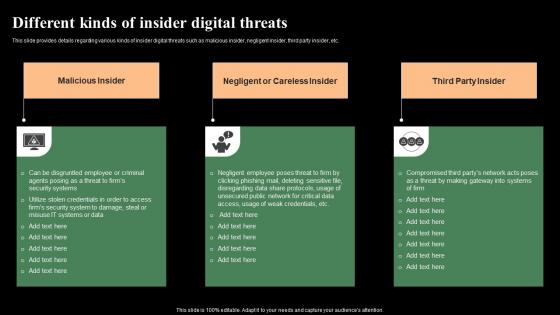
Different Kinds Of Insider Digital Threats Monitoring Digital Assets Graphics Pdf
This slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. There are so many reasons you need a Different Kinds Of Insider Digital Threats Monitoring Digital Assets Graphics Pdf The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
-
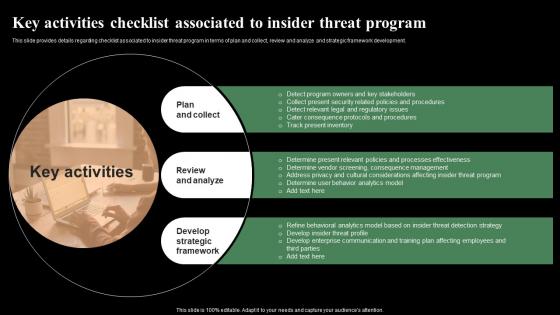
Key Activities Checklist Associated To Insider Threat Monitoring Digital Assets Summary Pdf
This slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Get a simple yet stunning designed Key Activities Checklist Associated To Insider Threat Monitoring Digital Assets Summary Pdf It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Key Activities Checklist Associated To Insider Threat Monitoring Digital Assets Summary Pdf can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.
-
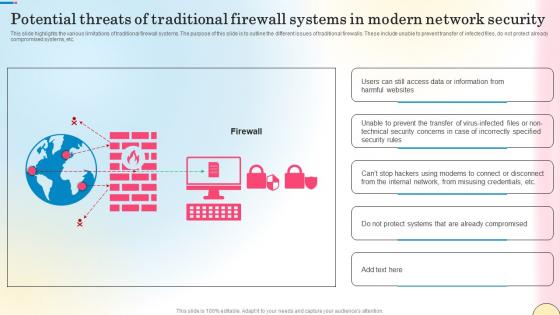
Potential Threats Of Traditional Firewall Systems Security Network Security Portrait Pdf
This slide highlights the various limitations of traditional firewall systems. The purpose of this slide is to outline the different issues of traditional firewalls. These include unable to prevent transfer of infected files, do not protect already compromised systems, etc. Create an editable Potential Threats Of Traditional Firewall Systems Security Network Security Portrait Pdf that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. Potential Threats Of Traditional Firewall Systems Security Network Security Portrait Pdf is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
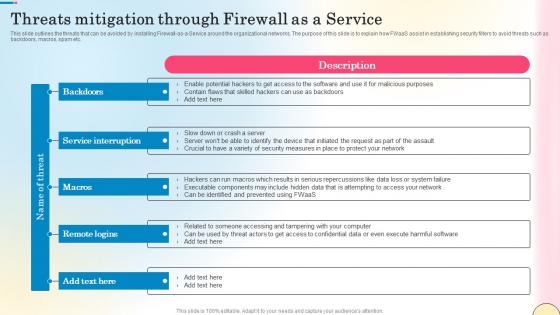
Threats Mitigation Through Firewall As A Service Network Security Guidelines Pdf
This slide outlines the threats that can be avoided by installing Firewall-as-a-Service around the organizational networks. The purpose of this slide is to explain how FWaaS assist in establishing security filters to avoid threats such as backdoors, macros, spam etc. Present like a pro with Threats Mitigation Through Firewall As A Service Network Security Guidelines Pdf Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
-
Addressing Threats Associated With Apple That Negatively Apples Proficiency In Optimizing Elements Pdf
This slide provides information regarding threats of brand that impose negative impact over firms success. Key Apples threats include rigorous competition, lawsuits, pandemic, etc. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Addressing Threats Associated With Apple That Negatively Apples Proficiency In Optimizing Elements Pdf to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.
-
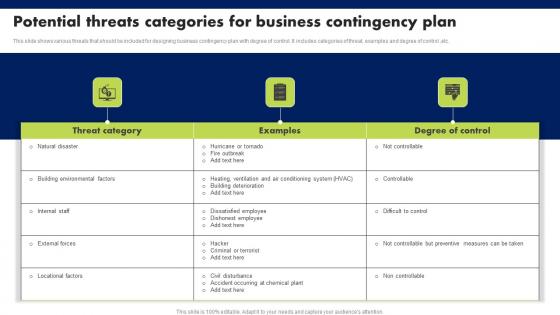
Potential Threats Categories For Business Contingency Plan Designs Pdf
This slide shows various threats that should be included for designing business contingency plan with degree of control. It includes categories of threat, examples and degree of control, etc. Showcasing this set of slides titled Potential Threats Categories For Business Contingency Plan Designs Pdf. The topics addressed in these templates are Threat Category, Examples, Degree Of Control. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Digital Security Metrics Icon Showcasing Threat Protection Topics Pdf
Pitch your topic with ease and precision using this Digital Security Metrics Icon Showcasing Threat Protection Topics Pdf This layout presents information on Digital Security, Metrics Icon, Showcasing Threat Protection It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
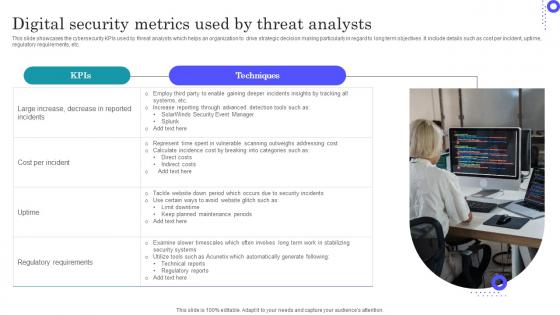
Digital Security Metrics Used By Threat Analysts Graphics Pdf
Showcasing this set of slides titled Digital Security Metrics Used By Threat Analysts Graphics Pdf The topics addressed in these templates are Regulatory Requirements, Large Increase, Scanning Outweighs All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Anti Fraud Threat Evaluation Controls Slides Pdf
This slide showcases the anti fraud risk assessment controls which helps an organization to prevent individuals, groups to commit frauds and mitigate any illogical activity. It include details such as separate functions, audit financial statements, examine internal controls, etc. Showcasing this set of slides titled Anti Fraud Threat Evaluation Controls Slides Pdf The topics addressed in these templates are Separate Functions, Examine Internal Controls, Financial Statements All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Application Of Fraud Detection And Threat Evaluation Professional Pdf
This slide showcases the applications of fraud detection and risk assessment which helps an organization to identify frauds by using patterns of various devices and session indicators. It include details such as banking and financial services, ecommerce and retail, etc. Pitch your topic with ease and precision using this Application Of Fraud Detection And Threat Evaluation Professional Pdf This layout presents information on Financial Services, Ecommerce And Retail, Information Technology It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Best Practices Of Fraud Detection And Threat Evaluation Background Pdf
This slide showcases the best practices of fraud detection and risk assessment which helps an organization to timely detect fraud which reduces future potential losses. It include details such as design potential fraud risk profile, mention fraud indicators, etc. Showcasing this set of slides titled Best Practices Of Fraud Detection And Threat Evaluation Background Pdf The topics addressed in these templates are Design Potential, Mention Fraud Indicators, Artificial Intelligence All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Challenges And Solutions Of Fraud Prevention And Threat Evaluation Microsoft Pdf
This slide showcases the challenges and solutions of fraud prevention and risk assessment which helps an organization to innovate new digital product and services to build customer relationships. It include details such as accelerated digitalization, lack of proper tools, etc. Pitch your topic with ease and precision using this Challenges And Solutions Of Fraud Prevention And Threat Evaluation Microsoft Pdf This layout presents information on Accelerated Digitalization, Impractical Approach, Customer Engagement It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Comparative Analysis Of Fraud Threat Evaluation And Detection Software Ideas Pdf
This slide showcases the comparison between fraud assessment and detection software which helps an organization to quickly track illegitimate and high risk online activities. It include details such as ratings, quick responses, ease of use, payment verification, etc. Showcasing this set of slides titled Comparative Analysis Of Fraud Threat Evaluation And Detection Software Ideas Pdf The topics addressed in these templates are Ratings, Quick Response, Payment Verification, Analytics All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Crucial Principles To Strengthen Fraud Threat Evaluation Download Pdf
This slide showcases the crucial principles required to strength fraud risk assessment which helps an organization to develop a comprehensive program that constantly takes pulse on current and emerging risks. It include details such as identify risk universe, limited research, etc. Pitch your topic with ease and precision using this Crucial Principles To Strengthen Fraud Threat Evaluation Download Pdf This layout presents information on Limited Research, Identify Risk Universe, Focus On Facts It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Elements Of Anti Fraud Threat Evaluation Program Rules Pdf
This slide showcases the elements of anti fraud risk assessment program which helps an organization to check the prevalence and seriousness of the misconduct.it include details such as risk assessment, tone from the top, training, data analytics. Showcasing this set of slides titled Elements Of Anti Fraud Threat Evaluation Program Rules Pdf The topics addressed in these templates are Risk Assessment, Training, Data Analytics All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Fraud Threat Evaluation And Identification Plan Designs Pdf
This slide showcases the fraud risk assessment and identification plan which helps an organization to establish and maintain strong internal control system. It include details such as identified fraud schemes, likelihood, significance, etc. Showcasing this set of slides titled Fraud Threat Evaluation And Identification Plan Designs Pdf The topics addressed in these templates are Financial Reporting, Revenue, Significance All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Fraud Threat Evaluation And Management Icon Mockup Pdf
Pitch your topic with ease and precision using this Fraud Threat Evaluation And Management Icon Mockup Pdf This layout presents information on Fraud Threat Evaluation, Management Icon It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Fraud Threat Evaluation And Prevention Strategies Clipart Pdf
This slide showcases the prevention strategies of fraud risk assessment which helps an organization to gain deeper understanding of particular group of hackers or individual person. It include details such as fraud risk awareness, code of conduct, background check, etc. Showcasing this set of slides titled Fraud Threat Evaluation And Prevention Strategies Clipart Pdf The topics addressed in these templates are Fraud Risk Awareness, Background Check, Code Of Conduct All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Fraud Threat Evaluation Checklist Icon Clipart Pdf
Pitch your topic with ease and precision using this Fraud Threat Evaluation Checklist Icon Clipart Pdf This layout presents information on Fraud Threat Evaluation, Checklist Icon It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Fraud Threat Evaluation Icon Showcasing Hacker Mockup Pdf
Showcasing this set of slides titled Fraud Threat Evaluation Icon Showcasing Hacker Mockup Pdf The topics addressed in these templates are Fraud Threat Evaluation, Icon Showcasing Hacker All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Fraud Threat Management And Evaluation Strategies Portrait Pdf
This slide showcases the strategies of fraud risk management and assessment which helps an organization to provide a structure and protocols which prevent escalations. It include details such as assessment, governance, prevention, detection and tracking. Pitch your topic with ease and precision using this Fraud Threat Management And Evaluation Strategies Portrait Pdf This layout presents information on Assessment, Governance, Prevention, Detection It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Key Components Of Fraud Threat Evaluation Information Pdf
This slide showcases the key elements of fraud risk assessment which helps an organization to understand their vulnerabilities to deploy countermeasures. It include details such as regulatory compliance, financial and non financial reporting, asset misuse, banned activities. Showcasing this set of slides titled Key Components Of Fraud Threat Evaluation Information Pdf The topics addressed in these templates are Regulatory Compliance, Asset Misuse, Banned Activities All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
KPIS Of Fraud Threat Evaluation And Prevention Formats Pdf
This slide showcases the metrics of fraud risk assessment and prevention which helps an organization to maximize legitimate transactions and ensures better business decisions. It include details such as final approval rate, precision, recall, decline rate, etc. Pitch your topic with ease and precision using this KPIS Of Fraud Threat Evaluation And Prevention Formats Pdf This layout presents information on Final Approval Rate, Optimal Performance, Decline Rate It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Methodology Of Fraud Threat Evaluation System Introduction Pdf
This slide showcases the methods of fraud risk assessment system which helps an organization to minimize future losses, builds reputation and improves effectiveness. It include details such as macro risk enterprise wide assessment, micro risk business process assessment, etc. Showcasing this set of slides titled Methodology Of Fraud Threat Evaluation System Introduction Pdf The topics addressed in these templates are Enterprise Wide Assessment, Business Process Assessment All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Steps To Conduct Fraud Threat Evaluation Formats Pdf
This slide showcases the steps to perform risk assessment which helps an organization to proactively address the businesss vulnerabilities to internal and external fraud. It include details such as analyze risks, quantify risks, respond risks, track and reassess risks. Pitch your topic with ease and precision using this Steps To Conduct Fraud Threat Evaluation Formats Pdf This layout presents information on Analyze Risks, Quantify Risks, Respond Risks It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Steps To Prevent Banking Frauds Through Threat Evaluation Microsoft Pdf
This slide showcases the steps to prevent banking frauds through risk assessment which helps an organization to adapt and cope with increasing number of fraudsters. It include details such as device intelligence, behavioral biometrics, behavioral analytics, etc. Showcasing this set of slides titled Steps To Prevent Banking Frauds Through Threat Evaluation Microsoft Pdf The topics addressed in these templates are Steps To Prevent Banking Frauds Through Threat Evaluation Microsoft Pdf All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Threat Evaluation Dashboard Showcasing Quarterly Frauds Slides Pdf
This slide showcases the risk assessment dashboard showcasing quarterly frauds which helps an organization to reduce the risk of theft, corruption. It include details such as minimum amount, other emails, revision spending, etc. Pitch your topic with ease and precision using this Threat Evaluation Dashboard Showcasing Quarterly Frauds Slides Pdf This layout presents information on Threat Evaluation Dashboard Showcasing Quarterly Frauds Slides Pdf It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.