Application Security

Mastering Blockchain Wallets Best Practices To Enhance Mobile Wallet Security BCT SS V
This slide covers guidelines for users to improve the security of their mobile wallets. The purpose of this template is to provide tips such as adding two factor authentication, using secure Wifi connections, storing passwords in way preventing theft, installing mobile applications from trusted sources, etc. along with security and compliance measures by E-wallets providers. There are so many reasons you need a Mastering Blockchain Wallets Best Practices To Enhance Mobile Wallet Security BCT SS V. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily. This slide covers guidelines for users to improve the security of their mobile wallets. The purpose of this template is to provide tips such as adding two factor authentication, using secure Wifi connections, storing passwords in way preventing theft, installing mobile applications from trusted sources, etc. along with security and compliance measures by E-wallets providers.
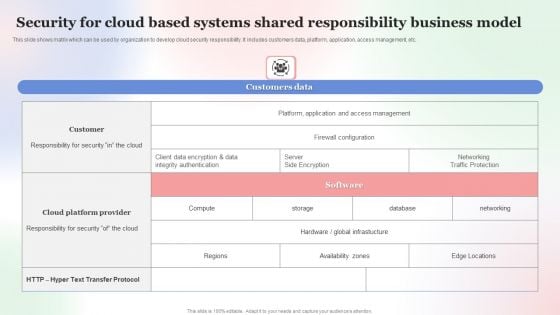
Security For Cloud Based Systems Shared Responsibility Business Model Professional PDF
This slide shows matrix which can be used by organization to develop cloud security responsibility. It includes customers data, platform, application, access management, etc. Showcasing this set of slides titled Security For Cloud Based Systems Shared Responsibility Business Model Professional PDF. The topics addressed in these templates are Security For Cloud Based, Systems Shared Responsibility, Business Model. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Data Safety Initiatives Key Security Controls To Be Addressed In The Program Summary PDF
Purpose of this slide is to provide information about key security controls that are to be addressed in companys information security program. Security controls covered are user application hardening, daily backups and patch applications. Deliver an awe inspiring pitch with this creative data safety initiatives key security controls to be addressed in the program summary pdf bundle. Topics like prevents attacks, limits extent of attacks, data recovery can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
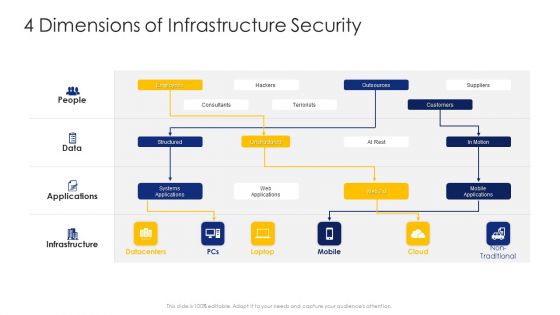
Construction Engineering And Industrial Facility Management 4 Dimensions Of Infrastructure Security Graphics PDF
Deliver an awe inspiring pitch with this creative construction engineering and industrial facility management 4 dimensions of infrastructure security graphics pdf bundle. Topics like structured, unstructured, systems applications can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
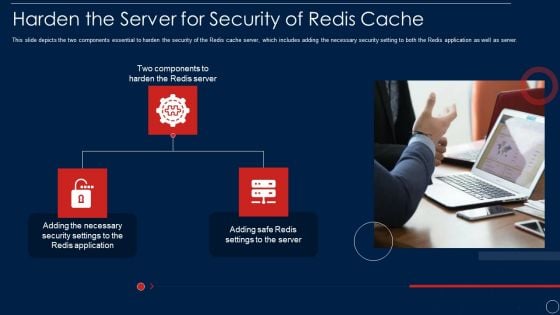
Redis Cache Data Structure IT Harden The Server For Security Of Redis Cache Template PDF
This slide depicts the two components essential to harden the security of the Redis cache server, which includes adding the necessary security setting to both the Redis application as well as server. This is a redis cache data structure it harden the server for security of redis cache template pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like harden the server for security of redis cache. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Landscape Architecture Planning And Management 4 Dimensions Of Infrastructure Security Sample PDF
Deliver an awe inspiring pitch with this creative landscape architecture planning and management 4 dimensions of infrastructure security sample pdf bundle. Topics like people, data, applications, infrastructure can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
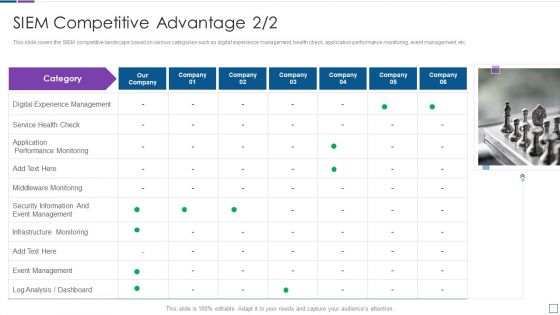
Real Time Assessment Of Security Threats SIEM Competitive Advantage Service Structure PDF
This slide covers the SIEM competitive landscape based on various categories such as digital experience management, health check, application performance monitoring, event management, etc. Presenting real time assessment of security threats siem competitive advantage service structure pdf to provide visual cues and insights. Share and navigate important information on one stages that need your due attention. This template can be used to pitch topics like digital experience management, service health check, application performance monitoring. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
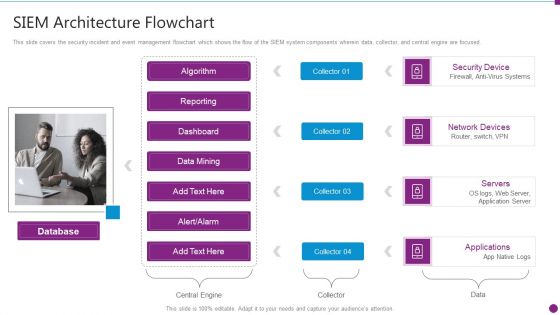
Security Information And Event Management Strategies For Financial Audit And Compliance SIEM Architecture Flowchart Microsoft PDF
This slide covers the security incident and event management flowchart which shows the flow of the SIEM system components wherein data, collector, and central engine are focused. This is a security information and event management strategies for financial audit and compliance siem architecture flowchart microsoft pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like database, security device, network devices, servers, applications. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Cloud Intelligence Framework For Application Consumption Determining The Suitable Software For Organization Icons PDF
The slide provides the key features comparison of various software that will help the company to achieve its objective of process automation and data security. Deliver and pitch your topic in the best possible manner with this cloud intelligence framework for application consumption determining the suitable software for organization icons pdf. Use them to share invaluable insights on process automation, data security, improve productivity, process automation and data security and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
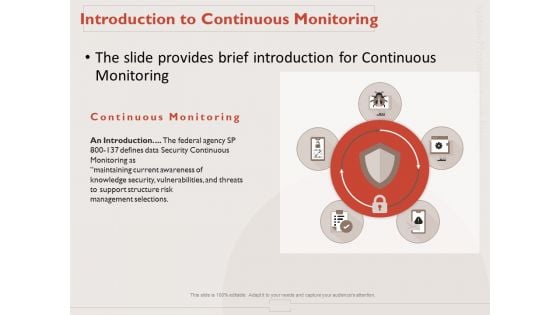
Monitoring Computer Software Application Introduction To Continuous Monitoring Ppt PowerPoint Presentation Model Files PDF
Presenting this set of slides with name monitoring computer software application introduction to continuous monitoring ppt powerpoint presentation model files pdf. This is a five stage process. The stages in this process are introduction, data security continuous monitoring, maintaining current awareness, knowledge security, vulnerabilities, and threats, support structure, risk management selections. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
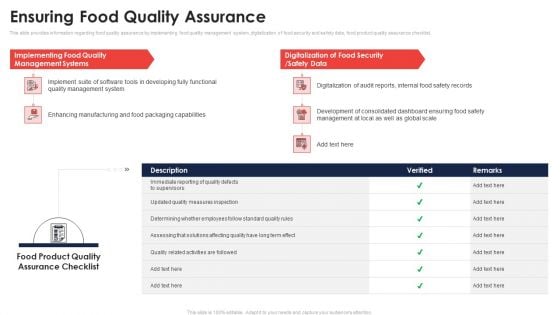
Ensuring Food Quality Assurance Application Of Quality Management For Food Processing Companies Guidelines PDF
This slide provides information regarding food quality assurance by implementing food quality management system, digitalization of food security and safety data, food product quality assurance checklist. Deliver and pitch your topic in the best possible manner with this ensuring food quality assurance application of quality management for food processing companies guidelines pdf. Use them to share invaluable insights on management, implementing, digitalization, security and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
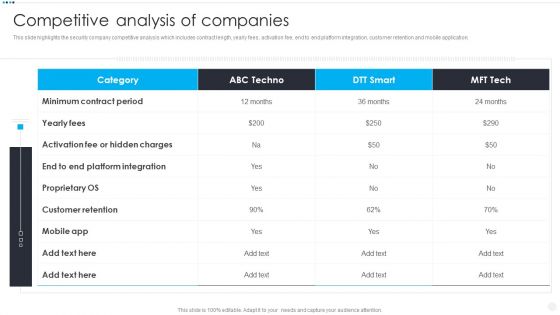
Smart Home Security Solutions Company Profile Competitive Analysis Of Companies Ideas PDF
This slide highlights the security company competitive analysis which includes contract length, yearly fees, activation fee, end to end platform integration, customer retention and mobile application. Deliver an awe inspiring pitch with this creative Smart Home Security Solutions Company Profile Competitive Analysis Of Companies Ideas PDF bundle. Topics like Minimum Contract Period, Activation Fee Hidden, Customer Retention Mobile can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
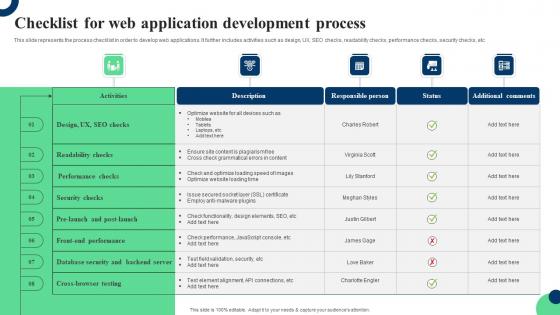
Checklist For Web Application Development Process Ppt Infographic Template Clipart Pdf
This slide represents the process checklist in order to develop web applications. It further includes activities such as design, UX, SEO checks, readability checks, performance checks, security checks, etc. Showcasing this set of slides titled Checklist For Web Application Development Process Ppt Infographic Template Clipart Pdf. The topics addressed in these templates are Readability Checks, Performance Checks, Security Checks. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting. This slide represents the process checklist in order to develop web applications. It further includes activities such as design, UX, SEO checks, readability checks, performance checks, security checks, etc.
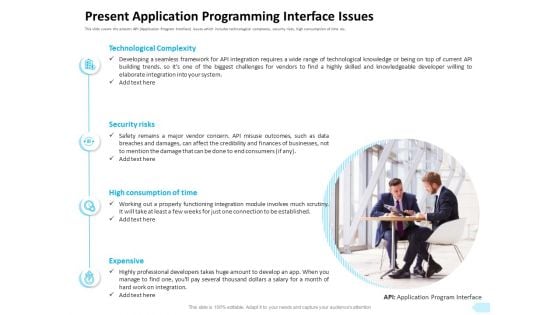
API Integration Software Development Present Application Programming Interface Issues Designs PDF
Presenting this set of slides with name api integration software development present application programming interface issues designs pdf. This is a four stage process. The stages in this process are technological complexity, security risks, high consumption of time, expensive. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Software Application Architecture Roadmap Covering Features And User Experience Topics PDF
Pitch your topic with ease and precision using this software application architecture roadmap covering features and user experience topics pdf. This layout presents information on conversion tracking, security policy, search. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Table Of Contents For IT Security Technology Ppt Infographics Designs PDF
Presenting table of contents for it security technology ppt infographics designs pdf to provide visual cues and insights. Share and navigate important information on six stages that need your due attention. This template can be used to pitch topics like technology, business, security, budget. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
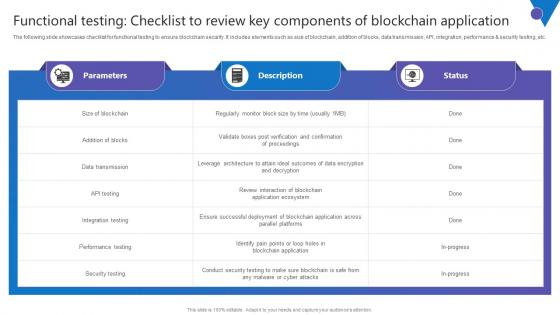
Functional Testing Checklist To Review Key Components Of Blockchain Application Topics Pdf
The following slide showcases checklist for functional testing to ensure blockchain security. It includes elements such as size of blockchain, addition of blocks, data transmission, API, integration, performance and security testing, etc. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Functional Testing Checklist To Review Key Components Of Blockchain Application Topics Pdf a try. Our experts have put a lot of knowledge and effort into creating this impeccable Functional Testing Checklist To Review Key Components Of Blockchain Application Topics Pdf. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today The following slide showcases checklist for functional testing to ensure blockchain security. It includes elements such as size of blockchain, addition of blocks, data transmission, API, integration, performance and security testing, etc.
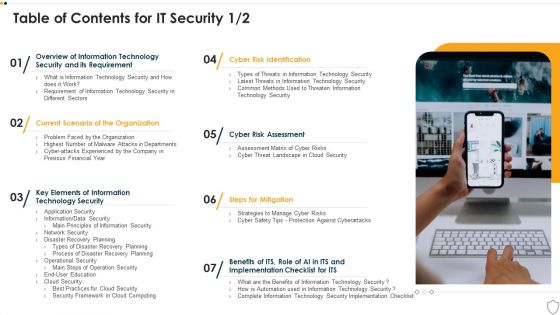
Table Of Contents For IT Security Cyber Ppt Inspiration Introduction PDF
This is a table of contents for it security cyber ppt inspiration introduction pdf template with various stages. Focus and dispense information on seven stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like technology security, implementation, organization, cyber risk assessment. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Computer System Interface Icon Depicting Mobile Security Ppt Show Example PDF
Persuade your audience using this Computer System Interface Icon Depicting Mobile Security Ppt Show Example PDF. This PPT design covers one stages, thus making it a great tool to use. It also caters to a variety of topics including Computer System, Interface Icon, Depicting Mobile Security. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
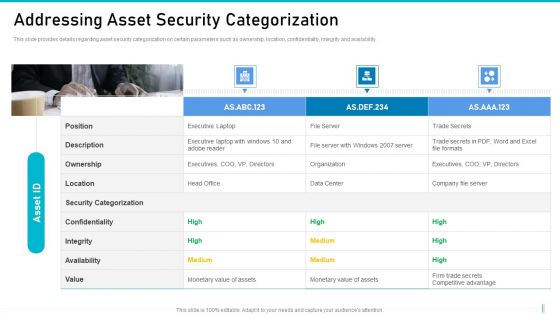
Risk Management For Organization Essential Assets Addressing Asset Security Categorization Diagrams PDF
This slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Presenting risk management for organization essential assets addressing asset security categorization diagrams pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like ownership, location, confidentiality, integrity, availability. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

1G To 5G Cellular What Security Features Does 5G 5Th Generation Technology Include Information PDF
This slide depicts the security features included in 5th generation technology, such as new cryptographic techniques for individual component protection, network slicing, encryption of IMSI to avoid eavesdropping spots, authentication confirmation, and secure network for sensitive data. Welcome to our selection of the 1G To 5G Cellular What Security Features Does 5G 5Th Generation Technology Include Information PDF. These are designed to help you showcase your creativity and bring your sphere to life. Planning and Innovation are essential for any business that is just starting out. This collection contains the designs that you need for your everyday presentations. All of our PowerPoints are 100 percent editable, so you can customize them to suit your needs. This multi-purpose template can be used in various situations. Grab these presentation templates today.
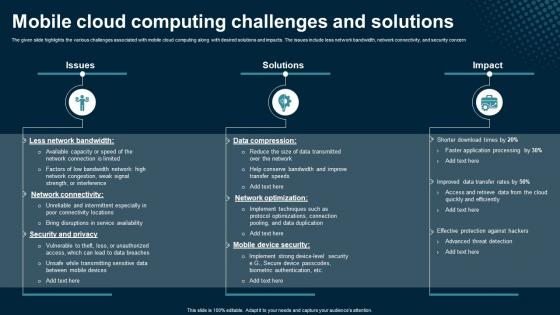
Mobile Cloud Computing Challenges And Solutions Application Areas Of Mobile Cloud Computing
The given slide highlights the various challenges associated with mobile cloud computing along with desired solutions and impacts. The issues include less network bandwidth, network connectivity, and security concern. Retrieve professionally designed Mobile Cloud Computing Challenges And Solutions Application Areas Of Mobile Cloud Computing to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere. The given slide highlights the various challenges associated with mobile cloud computing along with desired solutions and impacts. The issues include less network bandwidth, network connectivity, and security concern
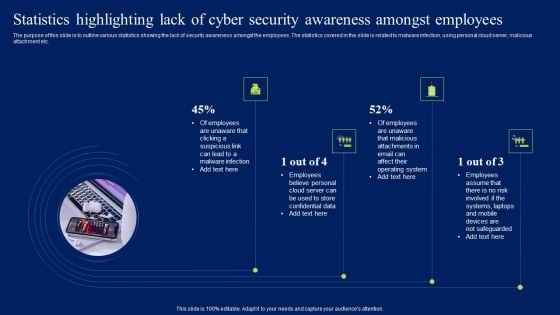
Statistics Highlighting Lack Of Cyber Security Awareness Amongst Employees Diagrams PDF
The purpose of this slide is to outline various statistics showing the lack of security awareness amongst the employees. The statistics covered in the slide is related to malware infection, using personal cloud server, malicious attachment etc. Present like a pro with Statistics Highlighting Lack Of Cyber Security Awareness Amongst Employees Diagrams PDF Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
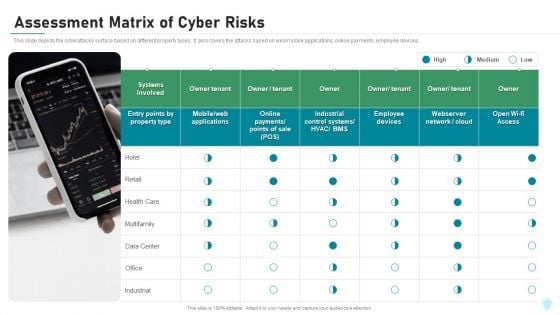
Assessment Matrix Of Cyber Risks IT Security IT Ppt Ideas Display PDF
This slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web or mobile applications, online payments, employee devices. Presenting assessment matrix of cyber risks it security it ppt ideas display pdf to provide visual cues and insights. Share and navigate important information on one stages that need your due attention. This template can be used to pitch topics like industrial, multifamily, data center, retail, health care. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
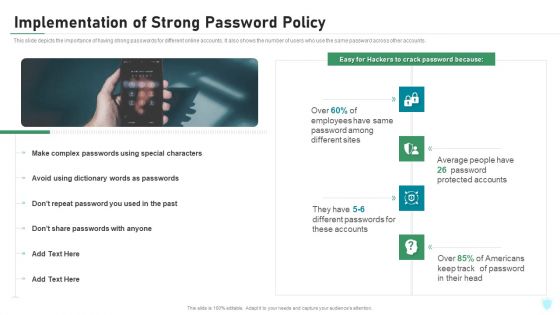
Implementation Of Strong Password Policy IT Security IT Ppt Styles Topics PDF
This slide depicts the importance of having strong passwords for different online accounts. It also shows the number of users who use the same password across other accounts. Presenting implementation of strong password policy it security it ppt styles topics pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like implementation of strong password policy. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
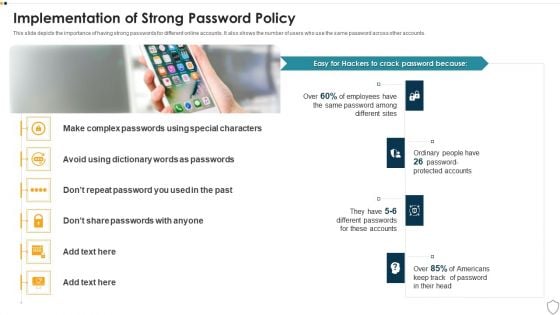
IT Security Implementation Of Strong Password Policy Ppt Summary Gridlines PDF
This slide depicts the importance of having strong passwords for different online accounts. It also shows the number of users who use the same password across other accounts. This is a it security implementation of strong password policy ppt summary gridlines pdf template with various stages. Focus and dispense information on one stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like implementation of strong password policy. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Types Of Disaster Recovery Plan IT Security IT Ppt Portfolio Graphics Pictures PDF
This slide defines the different categories of disaster recovery plans, namely as data center disaster recovery plans, cloud-based disaster recovery plans, etc. This is a types of disaster recovery plan it security it ppt portfolio graphics pictures pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like data center disaster recovery, cloud based disaster recovery, virtualization disaster recovery, disaster recovery as a service. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Financing Catalogue For Security Underwriting Agreement Investment Bank Underwriting Overview Slides PDF
The slide provides the key points related to underwriting agreement between the company and the investment bank. Key points covered in the slide includes type of offering, underwriting fee, number of banks involved in the deal etc. This is a financing catalogue for security underwriting agreement investment bank underwriting overview slides pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like underwriting fee, syndicate or selling group, type of offering. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
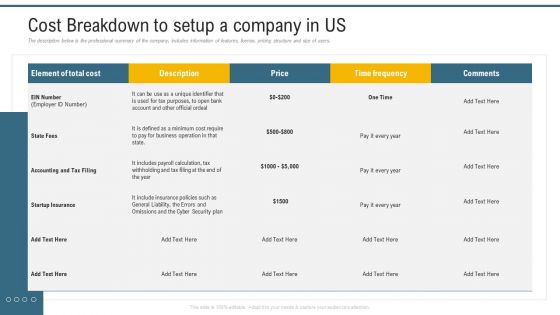
Application Programming Interface Marketplace Cost Breakdown To Setup A Company In US Diagrams PDF
The description below is the professional summary of the company, includes information of features, license, pricing structure and size of users. Deliver and pitch your topic in the best possible manner with this application programming interface marketplace cost breakdown to setup a company in us diagrams pdf. Use them to share invaluable insights on cyber security plan, business operation, time frequency and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
Dollars Note With Loan Application Form For Business Ppt PowerPoint Presentation Icon Template PDF
Persuade your audience using this dollars note with loan application form for business ppt powerpoint presentation icon template pdf. This PPT design covers one stages, thus making it a great tool to use. It also caters to a variety of topics including organization, key objective, amount loan required, repayment term, security offered. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
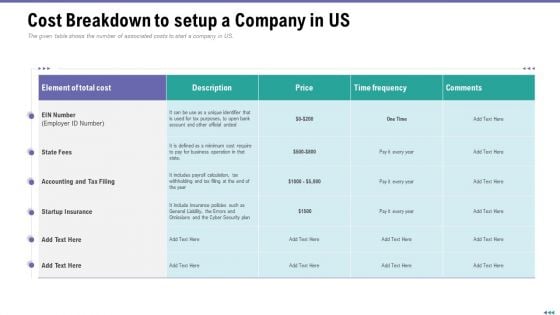
Market Viewpoint Application Programming Interface Governance Cost Breakdown To Setup A Company In Us Template PDF
The given table shows the number of associated costs to start a company in US. Deliver an awe inspiring pitch with this creative market viewpoint application programming interface governance cost breakdown to setup a company in us template pdf bundle. Topics like business, policies, price, cost, cyber security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Handling Cyber Threats Digital Era Key Security Controls To Be Addressed In The Program Ppt Infographics Samples PDF
Purpose of this slide is to provide information about key security controls that are to be addressed in companys information security program. Security controls covered are user application hardening, daily backups and patch applications. Presenting handling cyber threats digital era key security controls to be addressed in the program ppt infographics samples pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like prevents attacks, limits extent of attacks, data recovery. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
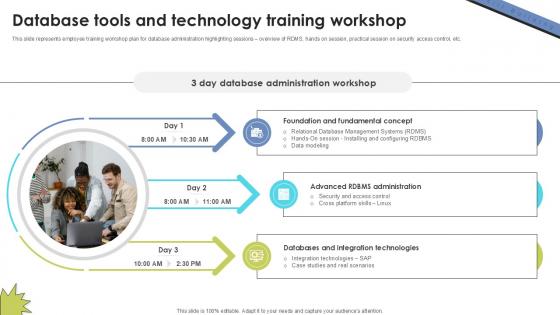
Database Tools And Technology Skill Building Plan For Application PPT Presentation DTE SS V
This slide represents employee training workshop plan for database administration highlighting sessions overview of RDMS, hands on session, practical session on security access control, etc. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Database Tools And Technology Skill Building Plan For Application PPT Presentation DTE SS V will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today. This slide represents employee training workshop plan for database administration highlighting sessions overview of RDMS, hands on session, practical session on security access control, etc.

Mobile Cloud Computing Overview And Benefits Application Areas Of Mobile Cloud Computing
The given slide showcases an overview of integrating cloud solutions in mobile applications along with the benefits. It includes flexibility, platform support, real-time data availability, and data security. Presenting this PowerPoint presentation, titled Mobile Cloud Computing Overview And Benefits Application Areas Of Mobile Cloud Computing, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Mobile Cloud Computing Overview And Benefits Application Areas Of Mobile Cloud Computing. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Mobile Cloud Computing Overview And Benefits Application Areas Of Mobile Cloud Computing that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs. The given slide showcases an overview of integrating cloud solutions in mobile applications along with the benefits. It includes flexibility, platform support, real-time data availability, and data security
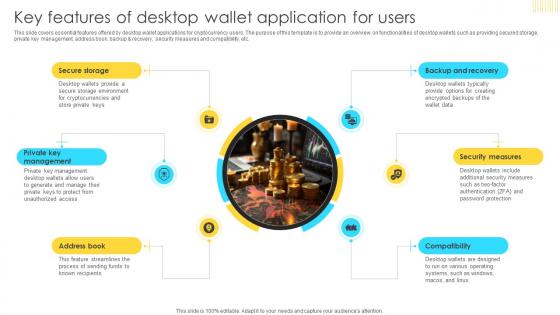
Mastering Blockchain Wallets Key Features Of Desktop Wallet Application BCT SS V
This slide covers essential features offered by desktop wallet applications for cryptocurrency users. The purpose of this template is to provide an overview on functionalities of desktop wallets such as providing secured storage, private key management, address book, backup and recovery, security measures and compatibility, etc. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Mastering Blockchain Wallets Key Features Of Desktop Wallet Application BCT SS V a try. Our experts have put a lot of knowledge and effort into creating this impeccable Mastering Blockchain Wallets Key Features Of Desktop Wallet Application BCT SS V. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today This slide covers essential features offered by desktop wallet applications for cryptocurrency users. The purpose of this template is to provide an overview on functionalities of desktop wallets such as providing secured storage, private key management, address book, backup and recovery, security measures and compatibility, etc.
Various Strategies To Ensure Food Safety Application Of Quality Management For Food Processing Companies Icons PDF
This slide provides information regarding various strategies used by firm in ensuring food safety in terms of streamlining global safety requirements, digitalization of food, food safety network. This is a various strategies to ensure food safety application of quality management for food processing companies icons pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like streamlining global safety requirements, digitalization of food security or safety data, building food safety network. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
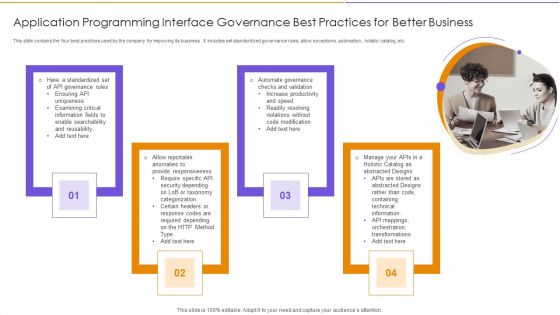
Application Programming Interface Governance Best Practices For Better Business Diagrams PDF
This slide contains the four best practices used by the company for improving its business . It includes set standardized governance rules, allow exceptions, automation , holistic catalog, etc. Presenting Application Programming Interface Governance Best Practices For Better Business Diagrams PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Security Depending, Increase Productivity, Technical Information. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
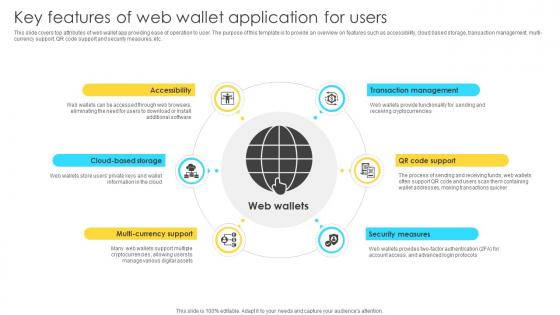
Mastering Blockchain Wallets Key Features Of Web Wallet Application For Users BCT SS V
This slide covers top attributes of web wallet app providing ease of operation to user. The purpose of this template is to provide an overview on features such as accessibility, cloud based storage, transaction management, multi-currency support, QR code support and security measures, etc. Get a simple yet stunning designed Mastering Blockchain Wallets Key Features Of Web Wallet Application For Users BCT SS V. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Mastering Blockchain Wallets Key Features Of Web Wallet Application For Users BCT SS V can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today. This slide covers top attributes of web wallet app providing ease of operation to user. The purpose of this template is to provide an overview on features such as accessibility, cloud based storage, transaction management, multi-currency support, QR code support and security measures, etc.
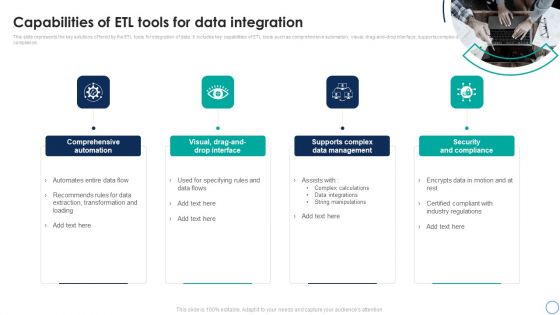
Business Analytics Application Capabilities Of ETL Tools For Data Integration Inspiration PDF
This slide represents the key solutions offered by the ETL tools for integration of data. It includes key capabilities of ETL tools such as comprehensive automation, visual, drag-and-drop interface, supports complex data management and security and compliance. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Business Analytics Application Capabilities Of ETL Tools For Data Integration Inspiration PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Business Analytics Application Capabilities Of ETL Tools For Data Integration Inspiration PDF today and make your presentation stand out from the rest.
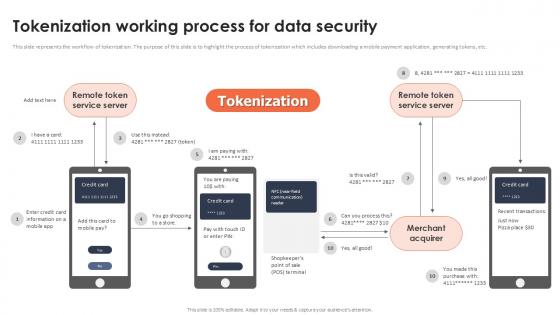
Tokenization Working Process For Data Security Securing Your Data Ppt Presentation
This slide represents the workflow of tokenization. The purpose of this slide is to highlight the process of tokenization which includes downloading a mobile payment application, generating tokens, etc. Find highly impressive Tokenization Working Process For Data Security Securing Your Data Ppt Presentation on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Tokenization Working Process For Data Security Securing Your Data Ppt Presentation for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now This slide represents the workflow of tokenization. The purpose of this slide is to highlight the process of tokenization which includes downloading a mobile payment application, generating tokens, etc.

Content Protection Mechanisms In Mobile Application Areas Of Mobile Cloud Computing
The purpose of the mentioned slide is to showcase the content protection techniques to secure mobile cloud media streaming. It includes encryption, secure authentication and authorization, etc. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Content Protection Mechanisms In Mobile Application Areas Of Mobile Cloud Computing will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today. The purpose of the mentioned slide is to showcase the content protection techniques to secure mobile cloud media streaming. It includes encryption, secure authentication and authorization, etc.
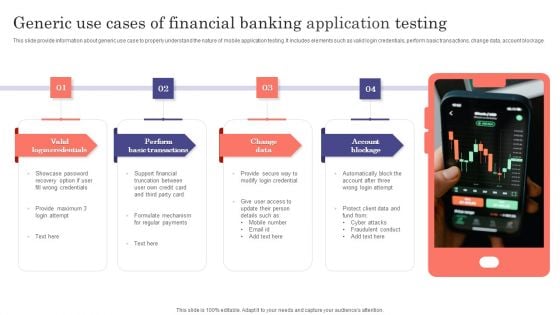
Generic Use Cases Of Financial Banking Application Testing Ppt Summary Show PDF
This slide provide information about generic use case to properly understand the nature of mobile application testing. It includes elements such as valid login credentials, perform basic transactions, change data, account blockage. Presenting Generic Use Cases Of Financial Banking Application Testing Ppt Summary Show PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Valid Login Credentials, Perform Basic Transactions, Change Data, Account Blockage. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
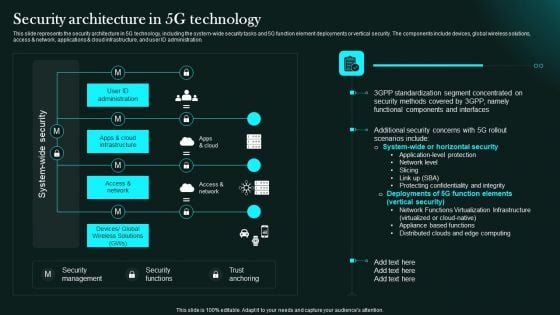
Security Architecture In 5G Technology 5G Network Functional Architecture Clipart PDF
This slide represents the security architecture in 5G technology, including the system-wide security tasks and 5G function element deployments or vertical security. The components include devices, global wireless solutions, access network, applications cloud infrastructure, and user ID administration.Retrieve professionally designed Security Architecture In 5G Technology 5G Network Functional Architecture Clipart PDF to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You Do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.

Comparative Analysis Of Security And Utility Token Securing Your Data Ppt Template
This slide highlights the differences between security and utility tokens. The purpose of this slide is to compare security and utility tokens on various aspects such as purpose, expectations, scam potential, etc. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Comparative Analysis Of Security And Utility Token Securing Your Data Ppt Template can be your best option for delivering a presentation. Represent everything in detail using Comparative Analysis Of Security And Utility Token Securing Your Data Ppt Template and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results. This slide highlights the differences between security and utility tokens. The purpose of this slide is to compare security and utility tokens on various aspects such as purpose, expectations, scam potential, etc.
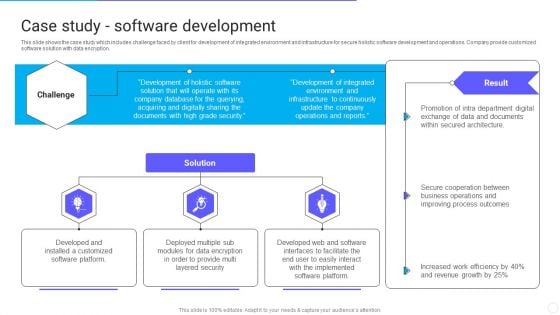
IT Application Services Company Outline Case Study Software Development Infographics PDF
This slide shows the case study which includes challenge faced by client for development of integrated environment and infrastructure for secure holistic software development and operations. Company provide customized software solution with data encryption. Presenting IT Application Services Company Outline Case Study Software Development Infographics PDF to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like Layered Security, Implemented, Developed Web. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
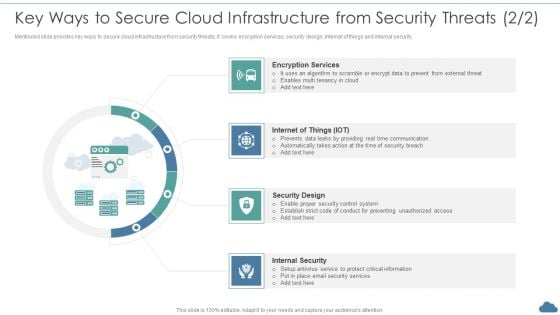
Cloud Optimization Infrastructure Model Key Ways To Secure Cloud Infrastructure From Security Threats Elements PDF
Mentioned slide provides key ways to secure cloud infrastructure from security threats. It covers encryption services, security design, internet of things and internal security.This is a Cloud Optimization Infrastructure Model Key Ways To Secure Cloud Infrastructure From Security Threats Elements PDF template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Encryption Services, Security Design, Internal Security You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Web Access Control Solution Comparison Between Secure Web Gateway And Cloud Security Gateways
This slide demonstrates the concept of cloud security gateways and Secure Web Gateways. The purpose of this slide is to compare cloud security gateways and SWGs on the basis of various factors such as scope, deployment, architecture, features and cost. If you are looking for a format to display your unique thoughts, then the professionally designed Web Access Control Solution Comparison Between Secure Web Gateway And Cloud Security Gateways is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Web Access Control Solution Comparison Between Secure Web Gateway And Cloud Security Gateways and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. This slide demonstrates the concept of cloud security gateways and Secure Web Gateways. The purpose of this slide is to compare cloud security gateways and SWGs on the basis of various factors such as scope, deployment, architecture, features and cost. If you are looking for a format to display your unique thoughts, then the professionally designed Web Access Control Solution Comparison Between Secure Web Gateway And Cloud Security Gateways is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Web Access Control Solution Comparison Between Secure Web Gateway And Cloud Security Gateways and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.

CASB 2 0 IT Cloud Access Security Broker And Secure Web Gateway
This slide represents how CASB 2.0 not just discovers the shadow IT but helps to control it too. The purpose of this slide is to showcase how CASB 2.0 improves the SWG model by empowering it with rich cloud app data, getting dynamic control of shadow IT and simplifying deployment. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our CASB 2 0 IT Cloud Access Security Broker And Secure Web Gateway was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into CASB 2 0 IT Cloud Access Security Broker And Secure Web Gateway. This slide represents how CASB 2.0 not just discovers the shadow IT but helps to control it too. The purpose of this slide is to showcase how CASB 2.0 improves the SWG model by empowering it with rich cloud app data, getting dynamic control of shadow IT and simplifying deployment.
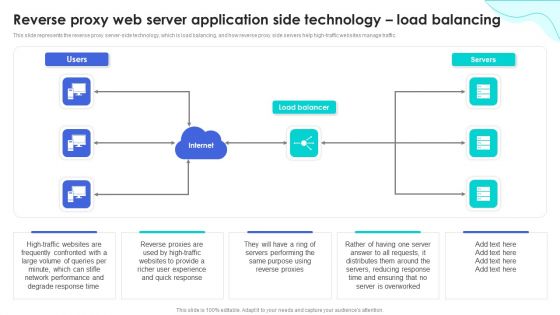
Reverse Proxy Web Server Reverse Proxy Web Server Application Side Technology Ideas PDF
This slide explains the reverse proxy server-side technology, that is security, and how data is transmitted securely in the presence of a proxy server that hides the actual servers identity. Are you searching for a Reverse Proxy Web Server Reverse Proxy Web Server Application Side Technology Ideas PDF that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort youve put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Reverse Proxy Web Server Reverse Proxy Web Server Application Side Technology Ideas PDF from Slidegeeks today.
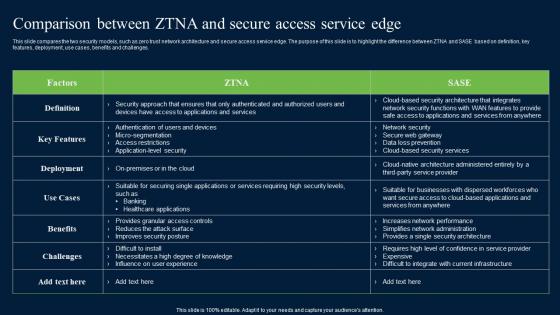
Comparison Between ZTNA And Secure Access Zero Trust Network Security Graphics Pdf
This slide compares the two security models, such as zero trust network architecture and secure access service edge. The purpose of this slide is to highlight the difference between ZTNA and SASE based on definition, key features, deployment, use cases, benefits and challenges. Slidegeeks is here to make your presentations a breeze with Comparison Between ZTNA And Secure Access Zero Trust Network Security Graphics Pdf With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first This slide compares the two security models, such as zero trust network architecture and secure access service edge. The purpose of this slide is to highlight the difference between ZTNA and SASE based on definition, key features, deployment, use cases, benefits and challenges.
Icons Slide For Secure Access Service Edge Cloud Security Model Ppt Gallery Layout PDF
Help your business to create an attention-grabbing presentation using our Icons Slide For Secure Access Service Edge Cloud Security Model Ppt Gallery Layout PDF set of slides. The slide contains innovative icons that can be flexibly edited. Choose this Icons Slide For Secure Access Service Edge Cloud Security Model Ppt Gallery Layout PDF template to create a satisfactory experience for your customers. Go ahead and click the download button.
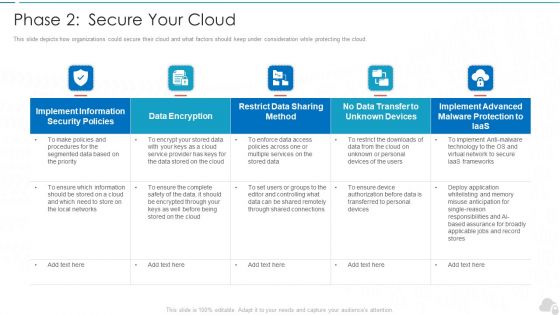
Phase 2 Secure Your Cloud Cloud Computing Security IT Ppt Slides Skills PDF
This slide depicts how organizations could secure their cloud and what factors should keep under consideration while protecting the cloud. Deliver an awe inspiring pitch with this creative phase 2 secure your cloud cloud computing security it ppt slides skills pdf bundle. Topics like implement, security policies, data encryption, services, frameworks can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Reverse Proxy Web Server How Does A Reverse Proxy Web Server Application Icons PDF
This slide explains the working of a reverse proxy server in two ways proxying for load balancing and proxy as a stand-in for a server which is further divided into three parts such as secure client to proxy, secure proxy to content server and secure client to proxy and secure proxy to content server. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Reverse Proxy Web Server How Does A Reverse Proxy Web Server Application Icons PDF was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Reverse Proxy Web Server How Does A Reverse Proxy Web Server Application Icons PDF.

Blockchain Application Areas In Logistics Management Supply Chain Evolution Harnessing The Power BCT SS V
This slide mentions various areas in logistics management that can be improved by introducing blockchain technology. Areas include inventory tracking, better shipments, secure billing, authenticity verification and dispute resolution. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Blockchain Application Areas In Logistics Management Supply Chain Evolution Harnessing The Power BCT SS V a try. Our experts have put a lot of knowledge and effort into creating this impeccable Blockchain Application Areas In Logistics Management Supply Chain Evolution Harnessing The Power BCT SS V. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today This slide mentions various areas in logistics management that can be improved by introducing blockchain technology. Areas include inventory tracking, better shipments, secure billing, authenticity verification and dispute resolution.
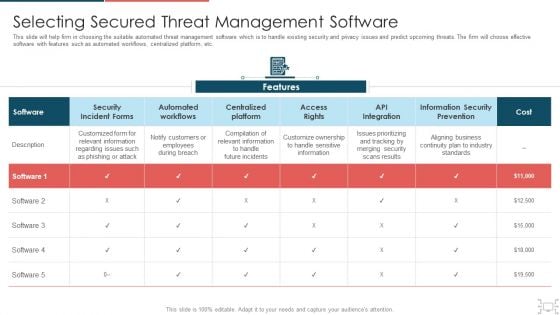
Cyber Security Administration In Organization Selecting Secured Threat Management Software Themes PDF
This slide will help firm in choosing the suitable automated threat management software which is to handle existing security and privacy issues and predict upcoming threats. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Deliver and pitch your topic in the best possible manner with this cyber security administration in organization selecting secured threat management software themes pdf. Use them to share invaluable insights on selecting secured threat management software and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
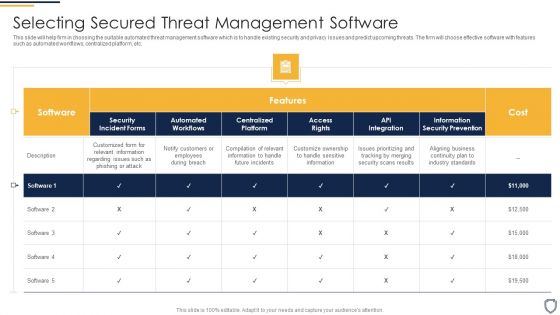
Corporate Security And Risk Management Selecting Secured Threat Management Software Introduction PDF
This slide will help firm in choosing the suitable automated threat management software which is to handle existing security and privacy issues and predict upcoming threats. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Deliver an awe inspiring pitch with this creative corporate security and risk management selecting secured threat management software introduction pdf bundle. Topics like selecting secured threat management software can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
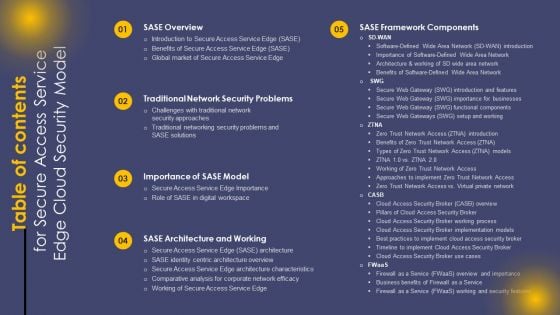
Table Of Contents For Secure Access Service Edge Cloud Security Model Ppt Professional Backgrounds PDF
Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Table Of Contents For Secure Access Service Edge Cloud Security Model Ppt Professional Backgrounds PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Table Of Contents For Secure Access Service Edge Cloud Security Model Ppt Professional Backgrounds PDF today and make your presentation stand out from the rest.

Smart Phone Data Safety Application With Protection Shield Ppt Gallery Outfit PDF
Persuade your audience using this smart phone data safety application with protection shield ppt gallery outfit pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including smart phone data transfer via secured network image. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
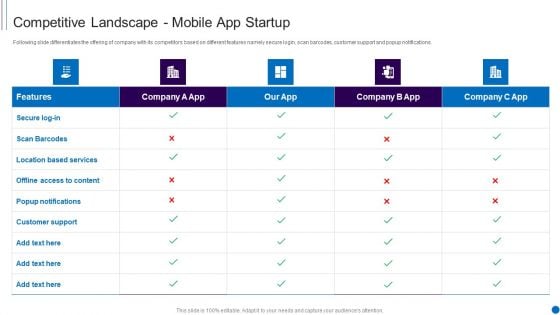
Fundraising Smartphone Application Startup Competitive Landscape Mobile App Startup Themes PDF
Following slide differentiates the offering of company with its competitors based on different features namely secure login, scan barcodes, customer support and popup notifications. Deliver an awe inspiring pitch with this creative Fundraising Smartphone Application Startup Competitive Landscape Mobile App Startup Themes PDF bundle. Topics like Scan Barcodes, Location Based Services, Popup Notifications, Customer Support can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
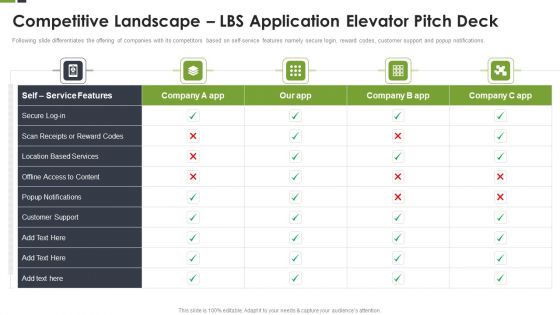
Competitive Landscape LBS Application Elevator Pitch Deck Ppt Inspiration Example Introduction PDF
Following slide differentiates the offering of companies with its competitors based on self-service features namely secure login, reward codes, customer support and popup notifications. Deliver and pitch your topic in the best possible manner with this Competitive Landscape LBS Application Elevator Pitch Deck Ppt Inspiration Example Introduction PDF. Use them to share invaluable insights on Location Based, Customer Support, Popup Notifications and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.


 Continue with Email
Continue with Email

 Home
Home


































