Computer Virus

Advantages Of Mobile Cloud Computing In Application Areas Of Mobile Cloud Computing
The given slide outlines the potential benefits of using mobile cloud computing in healthcare to streamline concurrent processes. It includes collaboration, security, cost-effectiveness, speed, and scalability. Boost your pitch with our creative Advantages Of Mobile Cloud Computing In Application Areas Of Mobile Cloud Computing. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them. The given slide outlines the potential benefits of using mobile cloud computing in healthcare to streamline concurrent processes. It includes collaboration, security, cost-effectiveness, speed, and scalability
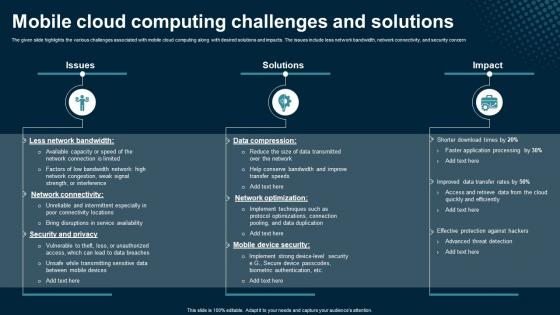
Mobile Cloud Computing Challenges And Solutions Application Areas Of Mobile Cloud Computing
The given slide highlights the various challenges associated with mobile cloud computing along with desired solutions and impacts. The issues include less network bandwidth, network connectivity, and security concern. Retrieve professionally designed Mobile Cloud Computing Challenges And Solutions Application Areas Of Mobile Cloud Computing to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere. The given slide highlights the various challenges associated with mobile cloud computing along with desired solutions and impacts. The issues include less network bandwidth, network connectivity, and security concern
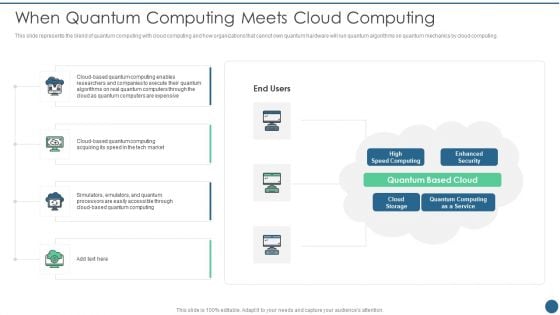
Quantum Key Distribution When Quantum Computing Meets Cloud Computing Summary PDF
This slide represents the blend of quantum computing with cloud computing and how organizations that cannot own quantum hardware will run quantum algorithms on quantum mechanics by cloud computing. Deliver and pitch your topic in the best possible manner with this Quantum Key Distribution When Quantum Computing Meets Cloud Computing Summary PDF Use them to share invaluable insights on Enhanced Security, Quantum Computing, Speed Computing and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
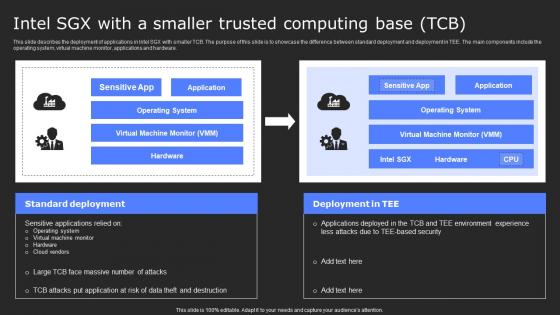
Intel Sgx With A Smaller Trusted Computing Base Tcb Secure Computing Framework Slides Pdf
This slide describes the deployment of applications in Intel SGX with smaller TCB. The purpose of this slide is to showcase the difference between standard deployment and deployment in TEE. The main components include the operating system, virtual machine monitor, applications and hardware. Find a pre-designed and impeccable Intel Sgx With A Smaller Trusted Computing Base Tcb Secure Computing Framework Slides Pdf. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation. This slide describes the deployment of applications in Intel SGX with smaller TCB. The purpose of this slide is to showcase the difference between standard deployment and deployment in TEE. The main components include the operating system, virtual machine monitor, applications and hardware.

Mobile Cloud Computing Overview And Benefits Application Areas Of Mobile Cloud Computing
The given slide showcases an overview of integrating cloud solutions in mobile applications along with the benefits. It includes flexibility, platform support, real-time data availability, and data security. Presenting this PowerPoint presentation, titled Mobile Cloud Computing Overview And Benefits Application Areas Of Mobile Cloud Computing, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Mobile Cloud Computing Overview And Benefits Application Areas Of Mobile Cloud Computing. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Mobile Cloud Computing Overview And Benefits Application Areas Of Mobile Cloud Computing that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs. The given slide showcases an overview of integrating cloud solutions in mobile applications along with the benefits. It includes flexibility, platform support, real-time data availability, and data security
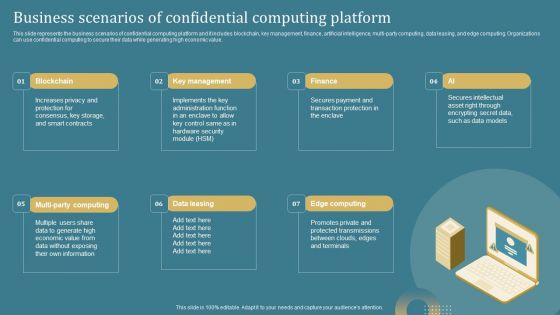
Confidential Computing System Technology Business Scenarios Of Confidential Computing Portrait PDF
This slide represents the business scenarios of confidential computing platform and it includes blockchain, key management, finance, artificial intelligence, multi-party computing, data leasing, and edge computing. Organizations can use confidential computing to secure their data while generating high economic value. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Confidential Computing System Technology Business Scenarios Of Confidential Computing Portrait PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable Confidential Computing System Technology Business Scenarios Of Confidential Computing Portrait PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.
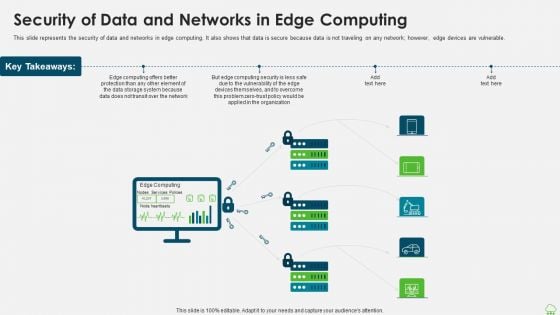
Distributed Computing IT Security Of Data And Networks In Edge Computing Themes PDF
This slide represents the security of data and networks in edge computing. It also shows that data is secure because data is not traveling on any network however, edge devices are vulnerable. Presenting distributed computing it security of data and networks in edge computing themes pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like organization, data storage, computing security. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
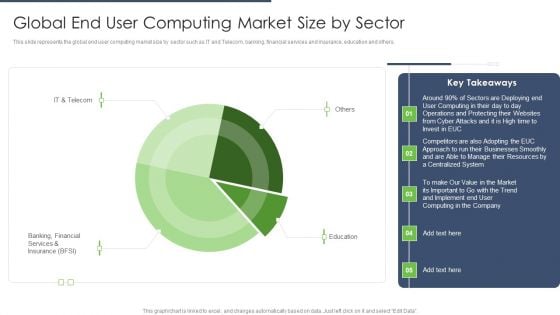
End User Computing Global End User Computing Market Size By Sector Designs PDF
This slide represents the global end user computing market size by sector such as IT and Telecom, banking, financial services and insurance, education and others.Deliver an awe inspiring pitch with this creative End User Computing Global End User Computing Market Size By Sector Designs PDF bundle. Topics like Operations Protecting, Businesses Smoothly, Computing Company can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
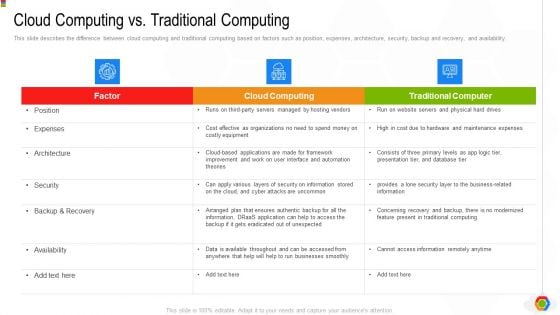
Google Cloud Console IT Cloud Computing Vs Traditional Computing Ppt File Ideas PDF
This slide describes the difference between cloud computing and traditional computing based on factors such as position, expenses, architecture, security, backup and recovery, and availability. Deliver an awe inspiring pitch with this creative google cloud console it cloud computing vs traditional computing ppt file ideas pdf bundle. Topics like security, backup and recovery, architecture, expenses, position can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
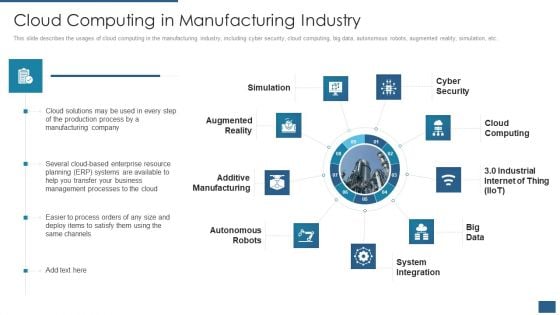
Cloud Computing Service Models IT Cloud Computing In Manufacturing Industry Inspiration PDF
This slide describes the usages of cloud computing in the manufacturing industry, including cyber security, cloud computing, big data, autonomous robots, augmented reality, simulation, etc. This is a cloud computing service models it cloud computing in manufacturing industry inspiration pdf template with various stages. Focus and dispense information on nine stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like simulation, cyber security, cloud computing, system integration, autonomous robots. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Distributed Computing IT Challenges And Solutions Of Edge Computing Deployment Icons PDF
This slide represents the challenges and solutions of edge computing deployment in the organization, and it includes challenges such as scale, performance, control, and security. Deliver and pitch your topic in the best possible manner with this distributed computing it challenges and solutions of edge computing deployment icons pdf. Use them to share invaluable insights on performance, security, performance and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
Confidential Computing System Technology Working Of Confidential Computing Technology Icons PDF
This slide describes the working of confidential computing technology to protect businesses in-memory crucial data while performing computations. It also includes how this approach makes data invisible to the operating system, cloud providers, users and other compute stack assets. This Confidential Computing System Technology Working Of Confidential Computing Technology Icons PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Confidential Computing System Technology Working Of Confidential Computing Technology Icons PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, dont wait, grab the presentation templates today.

Confidential Computing System Technology Confidential Computing Market Driven By Cloud Professional PDF
This slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. This Confidential Computing System Technology Confidential Computing Market Driven By Cloud Professional PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Confidential Computing System Technology Confidential Computing Market Driven By Cloud Professional PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, dont wait, grab the presentation templates today.
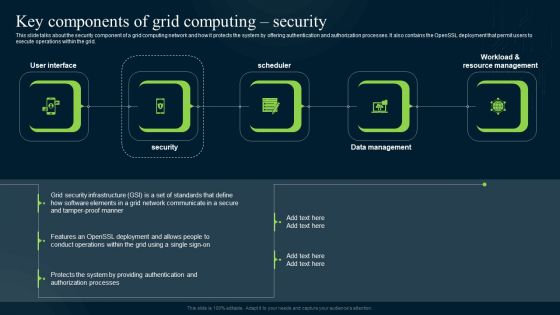
Grid Computing Infrastructure Key Components Of Grid Computing Security Information PDF
This slide talks about the security component of a grid computing network and how it protects the system by offering authentication and authorization processes. It also contains the OpenSSL deployment that permit users to execute operations within the grid. Explore a selection of the finest Grid Computing Infrastructure Key Components Of Grid Computing Security Information PDF here. With a plethora of professionally designed and pre-made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Grid Computing Infrastructure Key Components Of Grid Computing Security Information PDF to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks.
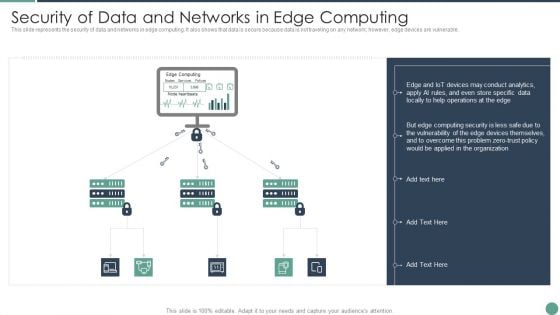
Distributed Computing Security Of Data And Networks In Edge Computing Ideas PDF
This slide represents the security of data and networks in edge computing. It also shows that data is secure because data is not traveling on any network however, edge devices are vulnerable.This is a Distributed Computing Security Of Data And Networks In Edge Computing Ideas PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Conduct Analytics, Devices Themselves, Vulnerability You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
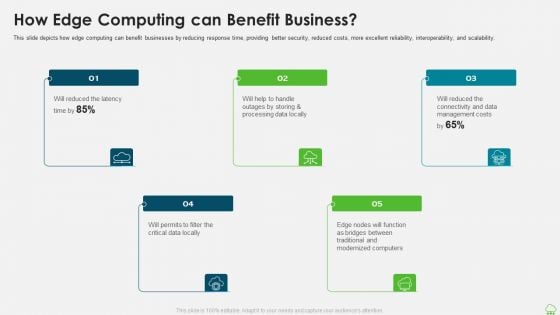
Distributed Computing IT How Edge Computing Can Benefit Business Template PDF
This slide depicts how edge computing can benefit businesses by reducing response time, providing better security, reduced costs, more excellent reliability, interoperability, and scalability. Presenting distributed computing it how edge computing can benefit business template pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like management costs, processing data, computers. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
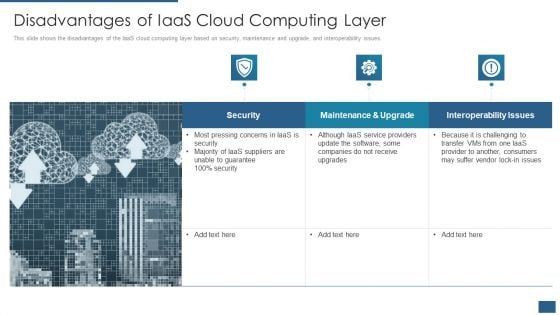
Cloud Computing Service Models IT Disadvantages Of Iaas Cloud Computing Layer Rules PDF
This slide shows the disadvantages of the IaaS cloud computing layer based on security, maintenance and upgrade, and interoperability issues. Deliver an awe inspiring pitch with this creative cloud computing service models it disadvantages of iaas cloud computing layer rules pdf bundle. Topics like security, maintenance and upgrade, interoperability issues can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
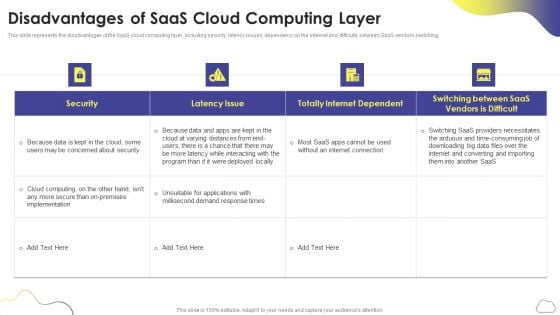
Cloud Computing Services Disadvantages Of Saas Cloud Computing Layer Slides PDF
This slide represents the disadvantages of the SaaS cloud computing layer, including security, latency issues, dependency on the internet and difficulty between SaaS vendors switching. Deliver and pitch your topic in the best possible manner with this Cloud Computing Services Disadvantages Of Saas Cloud Computing Layer Slides PDF. Use them to share invaluable insights on Security, Latency Issue, Totally Internet Dependent and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
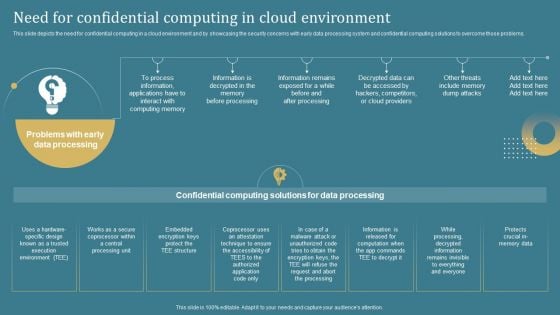
Confidential Computing System Technology Need For Confidential Computing In Cloud Guidelines PDF

Distributed Computing Challenges And Solutions Of Edge Computing Deployment Designs PDF
This slide represents the challenges and solutions of edge computing deployment in the organization, and it includes challenges such as scale, performance, control, and security.This is a Distributed Computing Challenges And Solutions Of Edge Computing Deployment Designs PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Infrastructure Environment, Repository Performance, Monitoring Controlling You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
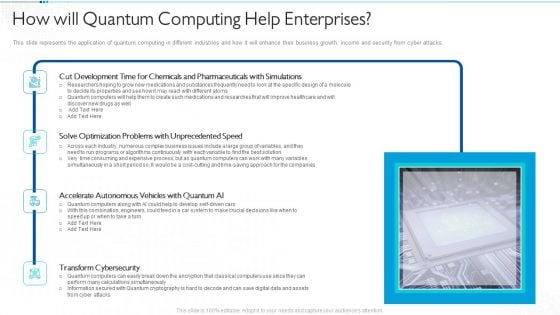
Quantum Computing For Everyone IT How Will Quantum Computing Help Enterprises Download PDF
This slide represents the application of quantum computing in different industries and how it will enhance their business growth, income and security from cyber attacks. Deliver and pitch your topic in the best possible manner with this quantum computing for everyone it how will quantum computing help enterprises download pdf. Use them to share invaluable insights on development, optimization, accelerate autonomous, transform cybersecurity and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
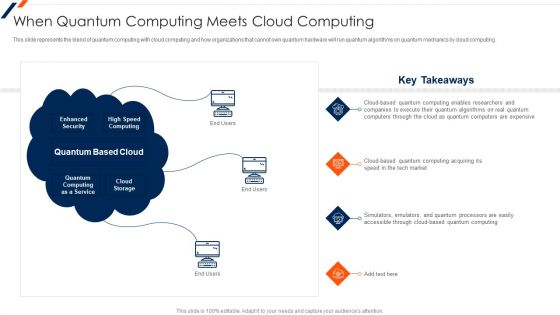
When Quantum Computing Meets Cloud Computing Ppt Model Example File PDF
This is a When Quantum Computing Meets Cloud Computing Ppt Model Example File PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Enhanced Security, High Speed Computing, Quantum Based Cloud. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
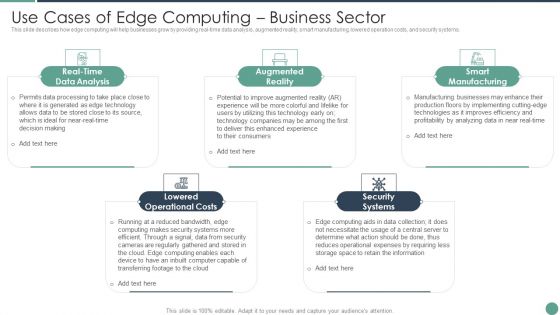
Distributed Computing Use Cases Of Edge Computing Business Sector Themes PDF
This slide describes how edge computing will help businesses grow by providing real-time data analysis, augmented reality, smart manufacturing, lowered operation costs, and security systems.This is a Distributed Computing Use Cases Of Edge Computing Business Sector Themes PDF template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Augmented Reality, Smart Manufacturing, Security Systems You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
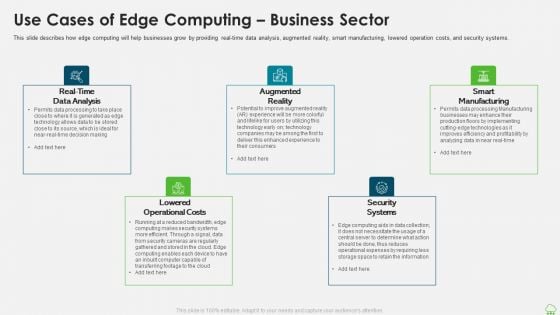
Distributed Computing IT Use Cases Of Edge Computing Business Sector Template PDF
This slide describes how edge computing will help businesses grow by providing real-time data analysis, augmented reality, smart manufacturing, lowered operation costs, and security systems. This is a distributed computing it use cases of edge computing business sector template pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like data analysis, smart manufacturing, lowered operational costs. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
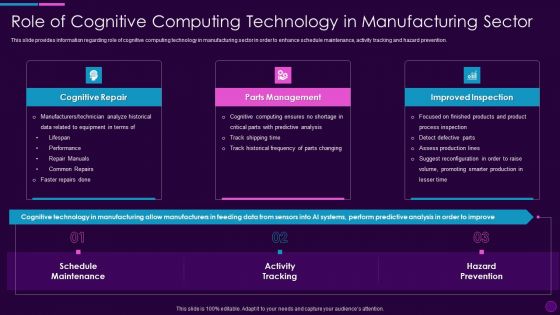
Role Of Cognitive Computing Technology In Cognitive Computing Action Plan Ppt File Aids PDF
This slide provides information regarding role of cognitive computing technology in manufacturing sector in order to enhance schedule maintenance, activity tracking and hazard prevention. Presenting role of cognitive computing technology in cognitive computing action plan ppt file aids pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like cognitive repair, parts management, improved inspection. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
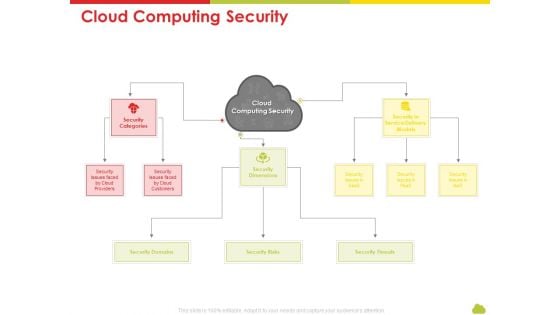
Mesh Computing Technology Hybrid Private Public Iaas Paas Saas Workplan Cloud Computing Security Rules PDF
Presenting mesh computing technology hybrid private public iaas paas saas workplan cloud computing security rules pdf to provide visual cues and insights. Share and navigate important information on one stages that need your due attention. This template can be used to pitch topics like risks, threats, domains, service. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
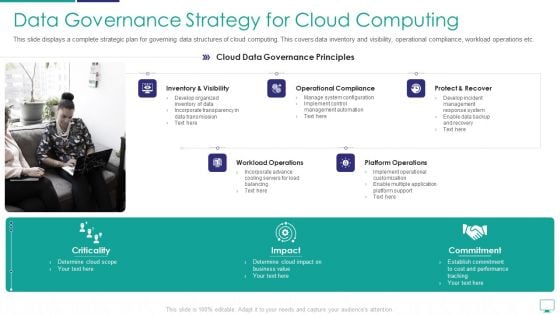
Mesh Computing Infrastructure Adoption Process Data Governance Strategy For Cloud Computing Demonstration PDF
This slide displays a complete strategic plan for governing data structures of cloud computing. This covers data inventory and visibility, operational compliance, workload operations etc. This is a mesh computing infrastructure adoption process data governance strategy for cloud computing demonstration pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like workload operations, platform operations, protect and recover. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
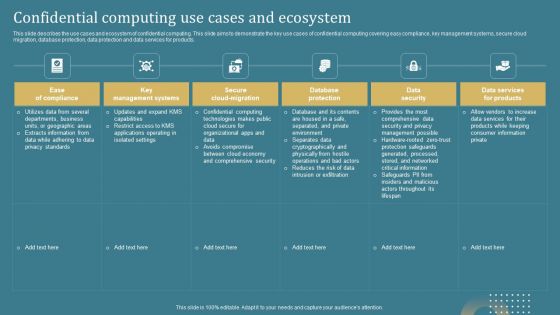
Confidential Computing System Technology Confidential Computing Use Cases And Ecosystem Demonstration PDF
This slide describes the use cases and ecosystem of confidential computing. This slide aims to demonstrate the key use cases of confidential computing covering easy compliance, key management systems, secure cloud migration, database protection, data protection and data services for products. Retrieve professionally designed Confidential Computing System Technology Confidential Computing Use Cases And Ecosystem Demonstration PDF to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You dont have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.
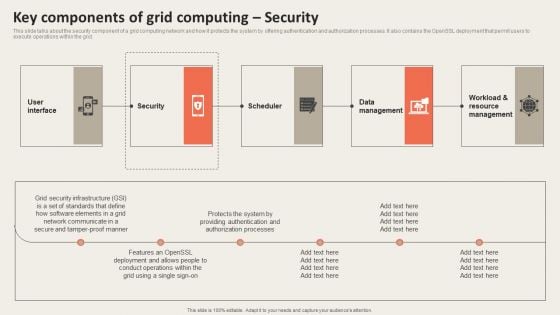
Grid Computing Applications Key Components Of Grid Computing Security Guidelines PDF
This slide talks about the security component of a grid computing network and how it protects the system by offering authentication and authorization processes. It also contains the OpenSSL deployment that permit users to execute operations within the grid. This modern and well arranged Grid Computing Applications Key Components Of Grid Computing Security Guidelines PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.
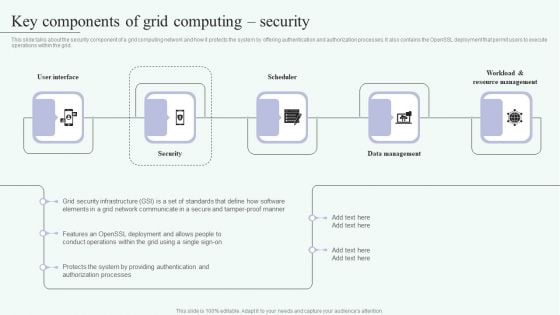
Grid Computing For High Performance Solutions Key Components Of Grid Computing Security Clipart PDF
This slide talks about the security component of a grid computing network and how it protects the system by offering authentication and authorization processes. It also contains the OpenSSL deployment that permit users to execute operations within the grid. Welcome to our selection of the Grid Computing For High Performance Solutions Key Components Of Grid Computing Security Clipart PDF. These are designed to help you showcase your creativity and bring your sphere to life. Planning and Innovation are essential for any business that is just starting out. This collection contains the designs that you need for your everyday presentations. All of our PowerPoints are 100 percent editable, so you can customize them to suit your needs. This multi purpose template can be used in various situations. Grab these presentation templates today.
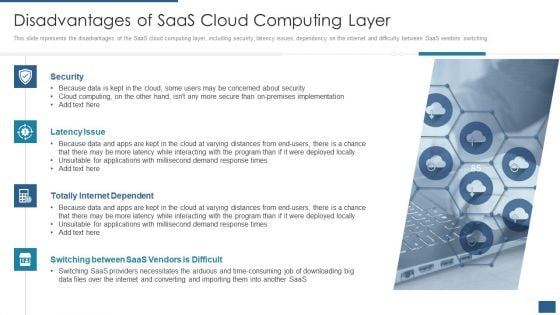
Cloud Computing Service Models IT Disadvantages Of Saas Cloud Computing Layer Elements PDF
This slide represents the disadvantages of the SaaS cloud computing layer, including security, latency issues, dependency on the internet and difficulty between SaaS vendors switching. Presenting cloud computing service models it disadvantages of saas cloud computing layer elements pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like security, latency issue, totally internet dependent, switching between saas vendors is difficult. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
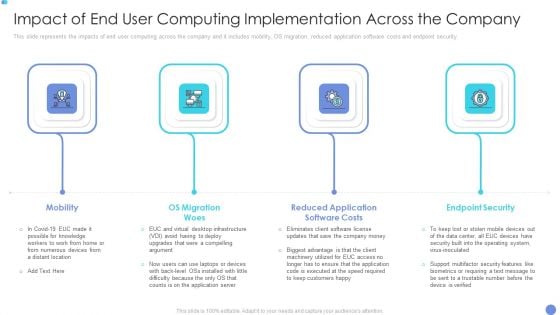
Customer Mesh Computing IT Impact Of End User Computing Implementation Across The Company Pictures PDF
This slide represents the impacts of end user computing across the company and it includes mobility, OS migration, reduced application software costs and endpoint security. Presenting customer mesh computing it impact of end user computing implementation across the company pictures pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like mobility, os migration woes, endpoint security. In addition, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
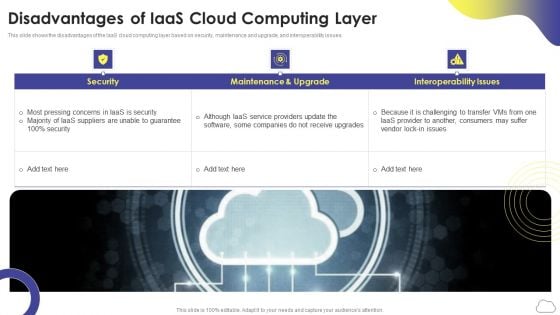
Cloud Computing Services Disadvantages Of Iaas Cloud Computing Layer Introduction PDF
This slide shows the disadvantages of the IaaS cloud computing layer based on security, maintenance and upgrade, and interoperability issues. This is a Cloud Computing Services Disadvantages Of Iaas Cloud Computing Layer Introduction PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Maintenance And Upgrade, Security, Interoperability Issues. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
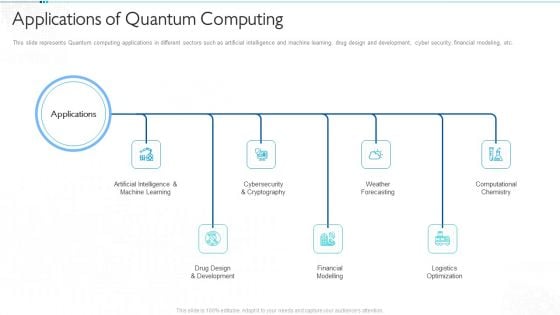
Quantum Computing For Everyone IT Applications Of Quantum Computing Infographics PDF
This slide represents Quantum computing applications in different sectors such as artificial intelligence and machine learning, drug design and development, cyber security, financial modeling, etc. Presenting quantum computing for everyone it applications of quantum computing infographics pdf to provide visual cues and insights. Share and navigate important information on seven stages that need your due attention. This template can be used to pitch topics like artificial intelligence and machine learning, drug design and development, financial modelling, weather forecasting, logistics optimization. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
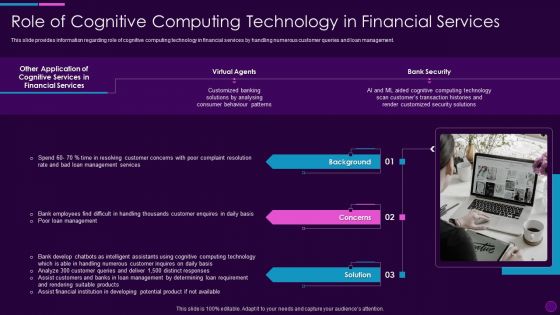
Cognitive Computing Action Plan Role Of Cognitive Computing Technology Ppt Infographics Layouts PDF
This slide provides information regarding role of cognitive computing technology in financial services by handling numerous customer queries and loan management. Presenting cognitive computing action plan role of cognitive computing technology ppt infographics layouts pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like financial services, virtual agents, bank security, background, concerns. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

End User Computing Application Of End User Computing In Insurance Background PDF
This slide represents the end user computing in insurance world and how it can help to generate inventory of all EUCs available in the insurance organizations.Presenting End User Computing Application Of End User Computing In Insurance Background PDF to provide visual cues and insights. Share and navigate important information on six stages that need your due attention. This template can be used to pitch topics like Contain Actuarial, Accuracy Security, Unwelcomed Company. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

End User Computing Benefits Of End User Computing To Business Guidelines PDF
This slide depicts the benefits of the end user computing to business and it includes centralized management, BYOD support, secure end user environment and built-in disaster recovery.Presenting End User Computing Benefits Of End User Computing To Business Guidelines PDF to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like Centralized Management, Disaster Recovery, Alleviates Significant. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
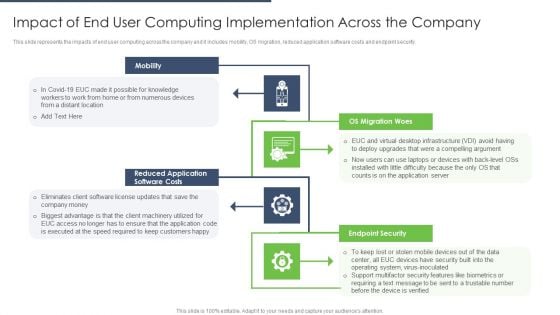
End User Computing Impact Of End User Computing Implementation Across The Company Download PDF
This slide represents the impacts of end user computing across the company and it includes mobility, OS migration, reduced application software costs and endpoint security.This is a End User Computing Impact Of End User Computing Implementation Across The Company Download PDF template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Distant Location, Reduced Application, Eliminates Client. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
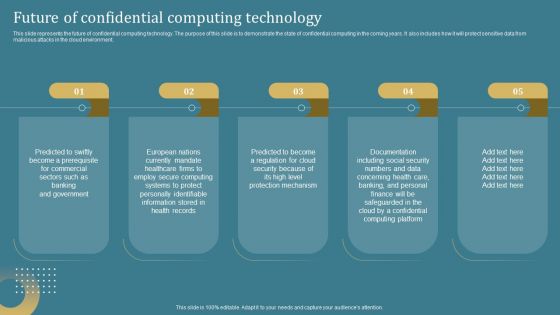
Confidential Computing System Technology Future Of Confidential Computing Technology Summary PDF

Mesh Computing Technology Hybrid Private Public Iaas Paas Saas Workplan Cloud Computing Challenges Download PDF
Presenting mesh computing technology hybrid private public iaas paas saas workplan cloud computing challenges download pdf to provide visual cues and insights. Share and navigate important information on seven stages that need your due attention. This template can be used to pitch topics like portability, costing, resource, security and privacy, availability and reliability. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
Technology Guide For Serverless Computing Business Risk Related To Cloud Computing Vendor Brochure PDF
Presenting technology guide for serverless computing business risk related to cloud computing vendor brochure pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like financial, data security, technology, operational, vendor. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
Technology Guide For Serverless Computing Business Risk Related To Cloud Computing Data Portrait PDF
This is a technology guide for serverless computing business risk related to cloud computing data portrait pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like financial, data security and regulatory, technology, operational, vendor. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Technology Guide For Serverless Computing Why Businesses Should Opt Cloud Computing Icons PDF
Presenting technology guide for serverless computing why businesses should opt cloud computing icons pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like scalability, affordable cost, security and disaster recovery, latest technology, best performance. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
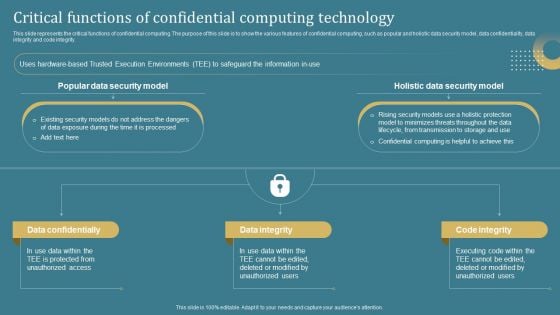
Confidential Computing System Technology Critical Functions Of Confidential Computing Template PDF
This slide represents the critical functions of confidential computing. The purpose of this slide is to show the various features of confidential computing, such as popular and holistic data security model, data confidentiality, data integrity and code integrity. Slidegeeks has constructed Confidential Computing System Technology Critical Functions Of Confidential Computing Template PDF after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.
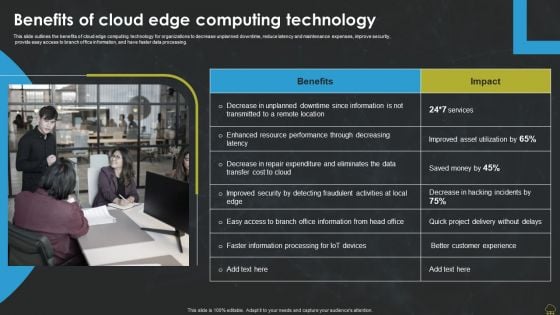
Integrating Edge Computing To Enhance Operational Efficiency Benefits Of Cloud Edge Computing Technology Designs PDF
This slide outlines the benefits of cloud edge computing technology for organizations to decrease unplanned downtime, reduce latency and maintenance expenses, improve security, provide easy access to branch office information, and have faster data processing. Want to ace your presentation in front of a live audience Our Integrating Edge Computing To Enhance Operational Efficiency Benefits Of Cloud Edge Computing Technology Designs PDF can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy to edit and downloadable. Use these for both personal and commercial use.
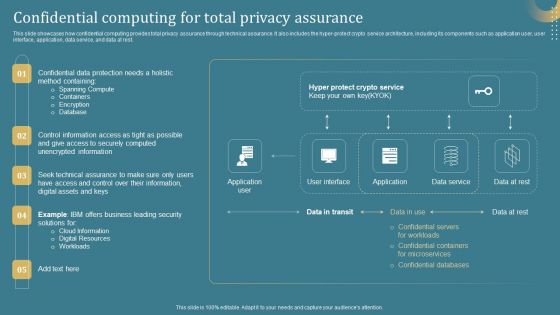
Confidential Computing System Technology Confidential Computing For Total Privacy Assurance Graphics PDF
This slide showcases how confidential computing provides total privacy assurance through technical assurance. It also includes the hyper-protect crypto service architecture, including its components such as application user, user interface, application, data service, and data at rest. This modern and well-arranged Confidential Computing System Technology Confidential Computing For Total Privacy Assurance Graphics PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint, no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.
Mesh Computing Safety Icon Cloud Computing Cloud Security Ppt PowerPoint Presentation Complete Deck
Share a great deal of information on the topic by deploying this mesh computing safety icon cloud computing cloud security ppt powerpoint presentation complete deck. Support your ideas and thought process with this prefabricated set. It includes a set of twelve slides, all fully modifiable and editable. Each slide can be restructured and induced with the information and content of your choice. You can add or remove large content boxes as well, to make this PPT slideshow more personalized. Its high-quality graphics and visuals help in presenting a well-coordinated pitch. This PPT template is also a resourceful tool to take visual cues from and implement the best ideas to help your business grow and expand. The main attraction of this well-formulated deck is that everything is editable, giving you the freedom to adjust it to your liking and choice. Changes can be made in the background and theme as well to deliver an outstanding pitch. Therefore, click on the download button now to gain full access to this multifunctional set.
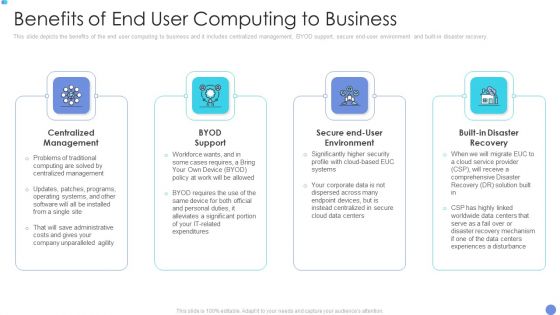
Customer Mesh Computing IT Benefits Of End User Computing To Business Download PDF
This slide depicts the benefits of the end user computing to business and it includes centralized management, BYOD support, secure end user environment and built in disaster recovery. Presenting to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like centralized management, byod support, secure end user environment. In addition, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Computerized Game Pitch Deck What Video Game Experience Challenges Are Faced By Prospect Download PDF
This slide caters details about key business challenges are faced by prospects in terms of security threats, regulatory compliances. Deliver and pitch your topic in the best possible manner with this computerized game pitch deck what video game experience challenges are faced by prospect download pdf. Use them to share invaluable insights on regulatory compliances, security threats and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
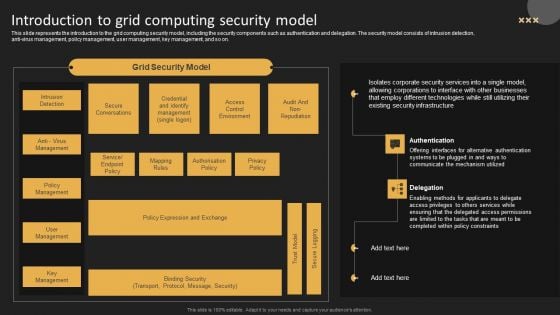
Introduction To Grid Computing Security Model Template PDF
This slide represents the introduction to the grid computing security model, including the security components such as authentication and delegation. The security model consists of intrusion detection, anti virus management, policy management, user management, key management, and so on. Get a simple yet stunning designed Introduction To Grid Computing Security Model Template PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy to edit Introduction To Grid Computing Security Model Template PDF can be your go to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.

Computerized Game Pitch Deck Rendering Unified Solutions To Handle Concerns Faced By Prospect Download PDF
This slide caters details about unified solutions to address concerns faced by clients in terms of game engine, security enhancement, revolutionary gameplay, absolute control. Deliver and pitch your topic in the best possible manner with this computerized game pitch deck rendering unified solutions to handle concerns faced by prospect download pdf. Use them to share invaluable insights on game engine, absolute control, security enhancement, revolutionary gameplay and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
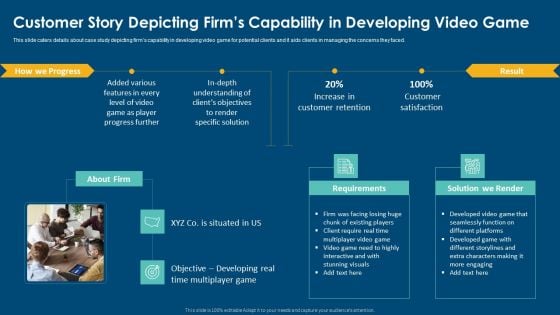
Computerized Game Pitch Deck Customer Story Depicting Firms Capability In Developing Video Game Introduction PDF
This slide caters details about case study depicting firms capability in developing video game for potential clients and it aids clients in managing the concerns they faced. This is a computerized game pitch deck customer story depicting firms capability in developing video game introduction pdf template with various stages. Focus and dispense information on one stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like customer story depicting firms capability in developing video game. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Warning Signs Of Pop Up Phishing Scams Man In The Middle Phishing IT
This slide outlines the various warning signs which helps in identifying pop-up phishing cyber attacks. These include terrible pop-up advertisement, warnings to act fast, immediate scan of computer virus, pop-ups are difficult to close and unpopular company names. Retrieve professionally designed Warning Signs Of Pop Up Phishing Scams Man In The Middle Phishing IT to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere. This slide outlines the various warning signs which helps in identifying pop-up phishing cyber attacks. These include terrible pop-up advertisement, warnings to act fast, immediate scan of computer virus, pop-ups are difficult to close and unpopular company names.

Security Of Cloud Computing Ppt PowerPoint Presentation Inspiration Microsoft
This is a security of cloud computing ppt powerpoint presentation inspiration microsoft. This is a four stage process. The stages in this process are computer software, operating system, open source.

Checklist To Implement Confidential Secure Computing Framework Rules Pdf
This slide depicts the checklist to implement confidential computing architecture in a cloud environment. The purpose of this slide is to showcase the various steps to be taken to deploy confidential computing, including its status and the responsible person. Get a simple yet stunning designed Checklist To Implement Confidential Secure Computing Framework Rules Pdf. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Checklist To Implement Confidential Secure Computing Framework Rules Pdfcan be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today. This slide depicts the checklist to implement confidential computing architecture in a cloud environment. The purpose of this slide is to showcase the various steps to be taken to deploy confidential computing, including its status and the responsible person.
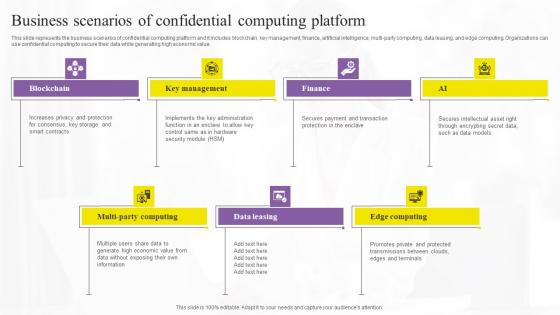
Business Scenarios Of Confidential Confidential Computing Technologies Structure Pdf
This slide represents the business scenarios of confidential computing platform and it includes blockchain, key management, finance, artificial intelligence, multi-party computing, data leasing, and edge computing. Organizations can use confidential computing to secure their data while generating high economic value. There are so many reasons you need a Business Scenarios Of Confidential Confidential Computing Technologies Structure Pdf. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily. This slide represents the business scenarios of confidential computing platform and it includes blockchain, key management, finance, artificial intelligence, multi-party computing, data leasing, and edge computing. Organizations can use confidential computing to secure their data while generating high economic value.
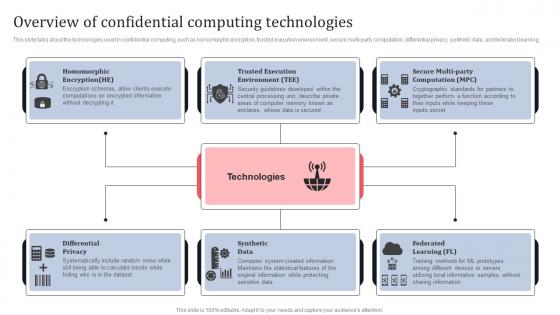
Overview Of Confidential Computing Technologies Secure Multi Party Designs Pdf
This slide talks about the technologies used in confidential computing, such as homomorphic encryption, trusted execution environment, secure multi-party computation, differential privacy, synthetic data, and federated learning. Get a simple yet stunning designed Overview Of Confidential Computing Technologies Secure Multi Party Designs Pdf It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Overview Of Confidential Computing Technologies Secure Multi Party Designs Pdf can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today. This slide talks about the technologies used in confidential computing, such as homomorphic encryption, trusted execution environment, secure multi-party computation, differential privacy, synthetic data, and federated learning.
Cloud Computing Engineering Data Security Service Icon Portrait Pdf
Showcasing this set of slides titled Cloud Computing Engineering Data Security Service Icon Portrait Pdf The topics addressed in these templates are Cloud Computing, Engineering Data Security, Service Icon All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting. Our Cloud Computing Engineering Data Security Service Icon Portrait Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
Icons Slide For Secure Computing Framework Designs Pdf
Download our innovative and attention grabbing Icons Slide For Secure Computing Framework Designs Pdf template. The set of slides exhibit completely customizable icons. These icons can be incorporated into any business presentation. So download it immediately to clearly communicate with your clientele. Our Icons Slide For Secure Computing Framework Designs Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
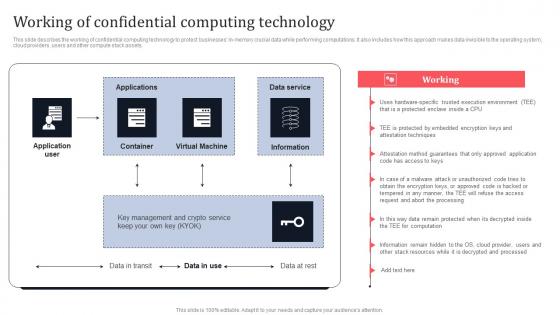
Working Of Confidential Computing Technology Secure Multi Party Information Pdf
This slide describes the working of confidential computing technology to protect businesses in-memory crucial data while performing computations. It also includes how this approach makes data invisible to the operating system, cloud providers, users and other compute stack assets. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Working Of Confidential Computing Technology Secure Multi Party Information Pdf to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation. This slide describes the working of confidential computing technology to protect businesses in-memory crucial data while performing computations. It also includes how this approach makes data invisible to the operating system, cloud providers, users and other compute stack assets.


 Continue with Email
Continue with Email

 Home
Home


































