Construction Safety Plan
Conditional Database Access Control With Intelligence Download PDF
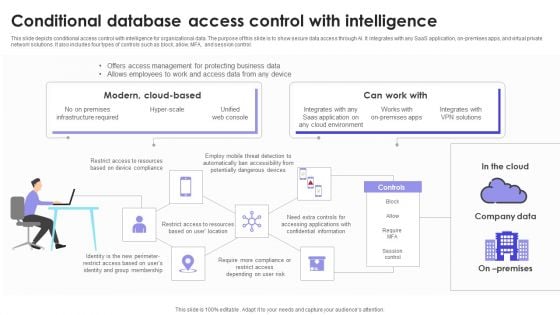
This slide depicts conditional access control with intelligence for organizational data. The purpose of this slide is to show secure data access through AI. It integrates with any SaaS application, on-premises apps, and virtual private network solutions. It also includes four types of controls such as block, allow, MFA, and session control. Pitch your topic with ease and precision using this Conditional Database Access Control With Intelligence Download PDF. This layout presents information on Company Data, Modern, Intelligence. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
Anatomy Process Of Virtual Crypto Coinage For Accounting Themes PDF
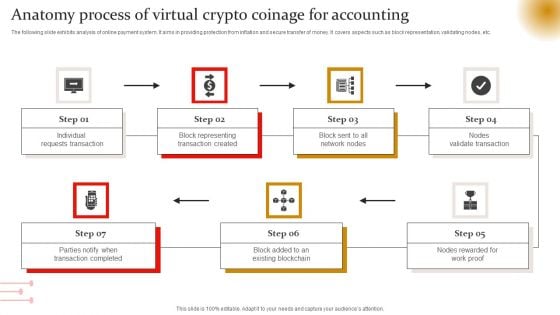
The following slide exhibits analysis of online payment system. It aims in providing protection from inflation and secure transfer of money. It covers aspects such as block representation, validating nodes, etc. Showcasing this set of slides titled Anatomy Process Of Virtual Crypto Coinage For Accounting Themes PDF. The topics addressed in these templates are Individual Requests Transaction, Nodes Validate Transaction, Network Nodes. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
Activities And Functions Of Three Lines Of Defense Border Model Slides PDF
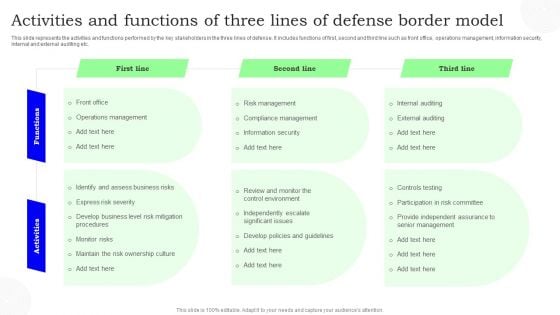
This slide represents the activities and functions performed by the key stakeholders in the three lines of defense. It includes functions of first, second and third line such as front office, operations management, information security, internal and external auditing etc. Showcasing this set of slides titled Activities And Functions Of Three Lines Of Defense Border Model Slides PDF. The topics addressed in these templates are First Line, Second Line, Third Line. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
Cryptocurrencies Available On Kraken Complete Roadmap To Blockchain BCT SS V
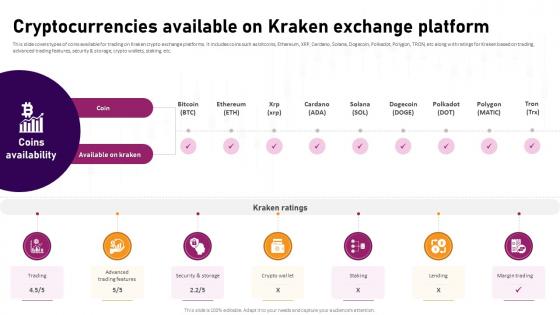
This slide covers types of coins available for trading on Kraken crypto exchange platforms. It includes coins such as bitcoins, Ethereum, XRP, Cardano, Solana, Dogecoin, Polkadot, Polygon, TRON, etc along with ratings for Kraken based on trading, advanced trading features, security and storage, crypto wallets, staking, etc. If you are looking for a format to display your unique thoughts, then the professionally designed Cryptocurrencies Available On Kraken Complete Roadmap To Blockchain BCT SS V is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Cryptocurrencies Available On Kraken Complete Roadmap To Blockchain BCT SS V and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. This slide covers types of coins available for trading on Kraken crypto exchange platforms. It includes coins such as bitcoins, Ethereum, XRP, Cardano, Solana, Dogecoin, Polkadot, Polygon, TRON, etc along with ratings for Kraken based on trading, advanced trading features, security and storage, crypto wallets, staking, etc.
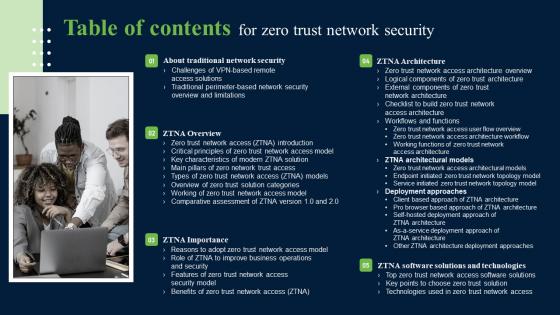
Table Of Contents For Zero Trust Network Security Introduction Pdf
From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Table Of Contents For Zero Trust Network Security Introduction Pdf will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today. Our Table Of Contents For Zero Trust Network Security Introduction Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Overview And Working Of Two Factor Authentication Cryptocurrency Management With Blockchain
This slide represents an overview and working of 2-factor authentication2FA. The purpose of this slide is to outline a 2FA overview, how it works, and why we need 2FA. 2FA is a two-step verification for protection and security it is user-friendly, etc.Get a simple yet stunning designed Overview And Working Of Two Factor Authentication Cryptocurrency Management With Blockchain. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Overview And Working Of Two Factor Authentication Cryptocurrency Management With Blockchain can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today. This slide represents an overview and working of 2-factor authentication2FA. The purpose of this slide is to outline a 2FA overview, how it works, and why we need 2FA. 2FA is a two-step verification for protection and security it is user-friendly, etc.
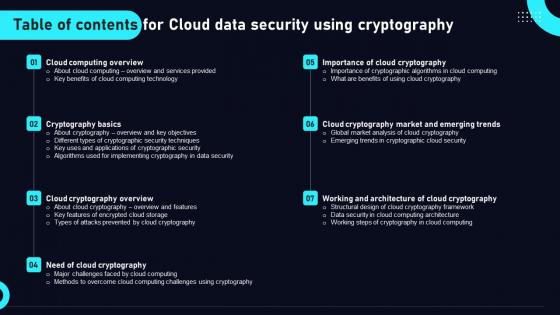
Table Of Contents For Cloud Data Security Using Cryptography Elements Pdf
If you are looking for a format to display your unique thoughts, then the professionally designed Table Of Contents For Cloud Data Security Using Cryptography Elements Pdf is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Table Of Contents For Cloud Data Security Using Cryptography Elements Pdf and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. Our Table Of Contents For Cloud Data Security Using Cryptography Elements Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
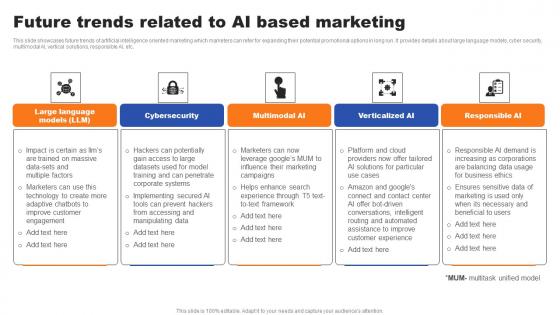
Future Trends Related To AI Based Marketing Ppt File Infographic Template Pdf
This slide showcases future trends of artificial intelligence oriented marketing which marketers can refer for expanding their potential promotional options in long run. It provides details about large language models, cyber security, multimodal AI, vertical solutions, responsible AI, etc. Get a simple yet stunning designed Future Trends Related To AI Based Marketing Ppt File Infographic Template Pdf. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Future Trends Related To AI Based Marketing Ppt File Infographic Template Pdf can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today. This slide showcases future trends of artificial intelligence oriented marketing which marketers can refer for expanding their potential promotional options in long run. It provides details about large language models, cyber security, multimodal AI, vertical solutions, responsible AI, etc.
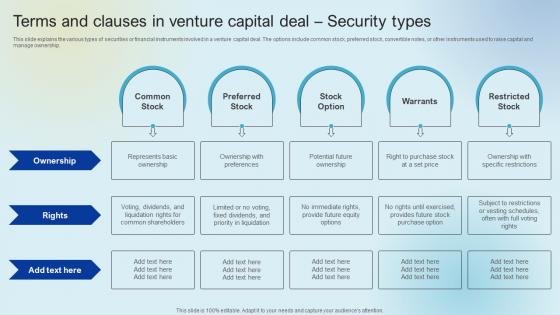
Terms And Clauses In Venture Raising Venture Capital A Holistic Approach Fin SS V
This slide explains the various types of securities or financial instruments involved in a venture capital deal. The options include common stock, preferred stock, convertible notes, or other instruments used to raise capital and manage ownership. This Terms And Clauses In Venture Raising Venture Capital A Holistic Approach Fin SS V is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Terms And Clauses In Venture Raising Venture Capital A Holistic Approach Fin SS V features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today This slide explains the various types of securities or financial instruments involved in a venture capital deal. The options include common stock, preferred stock, convertible notes, or other instruments used to raise capital and manage ownership.
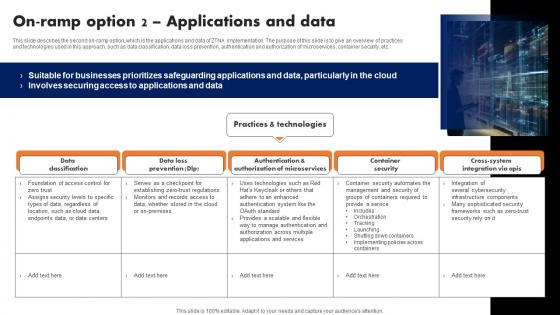
On Ramp Option 2 Applications And Data Software Defined Perimeter SDP
This slide describes the second on-ramp option, which is the applications and data of ZTNA implementation. The purpose of this slide is to give an overview of practices and technologies used in this approach, such as data classification, data loss prevention, authentication and authorization of microservices, container security, etc. The On Ramp Option 2 Applications And Data Software Defined Perimeter SDP is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression. This slide describes the second on-ramp option, which is the applications and data of ZTNA implementation. The purpose of this slide is to give an overview of practices and technologies used in this approach, such as data classification, data loss prevention, authentication and authorization of microservices, container security, etc.
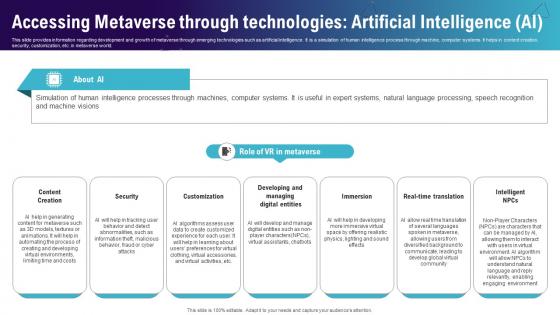
Accessing Metaverse Through Technologies Artificial Continuum Of Technology Revamping Business AI SS V
This slide provides information regarding development and growth of metaverse through emerging technologies such as artificial intelligence. It is a simulation of human intelligence process through machine, computer systems. It helps in content creation, security, customization, etc. in metaverse world. Create an editable Accessing Metaverse Through Technologies Artificial Continuum Of Technology Revamping Business AI SS V that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. Accessing Metaverse Through Technologies Artificial Continuum Of Technology Revamping Business AI SS V is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay. This slide provides information regarding development and growth of metaverse through emerging technologies such as artificial intelligence. It is a simulation of human intelligence process through machine, computer systems. It helps in content creation, security, customization, etc. in metaverse world.

Integrating AI With IoT Overview And Key Benefits Of AIoT In Smart Homes IoT SS V
The purpose of this slide is to showcase brief introduction to Artificial Intelligence of Things AIoT in smart homes. The slide covers information about major advantages and use cases of smart homes such as smart lighting, home security, and health and wellness. Create an editable Integrating AI With IoT Overview And Key Benefits Of AIoT In Smart Homes IoT SS V that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. Integrating AI With IoT Overview And Key Benefits Of AIoT In Smart Homes IoT SS V is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay. The purpose of this slide is to showcase brief introduction to Artificial Intelligence of Things AIoT in smart homes. The slide covers information about major advantages and use cases of smart homes such as smart lighting, home security, and health and wellness.
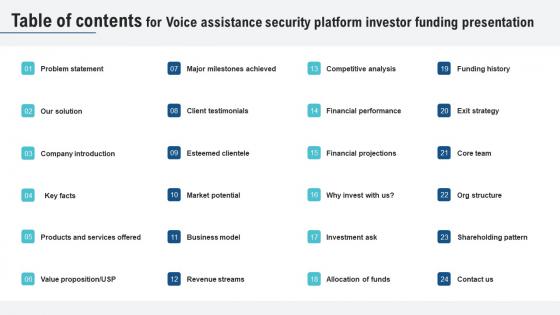
Table Of Contents For Voice Assistance Security Platform Investor Funding Presentation Themes Pdf
Create an editable Table Of Contents For Voice Assistance Security Platform Investor Funding Presentation Themes Pdf that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre designed presentation templates help save time. Table Of Contents For Voice Assistance Security Platform Investor Funding Presentation Themes Pdf is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay. Our Table Of Contents For Voice Assistance Security Platform Investor Funding Presentation Themes Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

What Are The Challenges Of Cloud Data Lake Data Lake Creation With Hadoop Cluster Graphics PDF
This slide depicts the cloud data lake challenges such as data security, data swamp, on-premise data warehouse, and data governance. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our What Are The Challenges Of Cloud Data Lake Data Lake Creation With Hadoop Cluster Graphics PDF was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into What Are The Challenges Of Cloud Data Lake Data Lake Creation With Hadoop Cluster Graphics PDF.
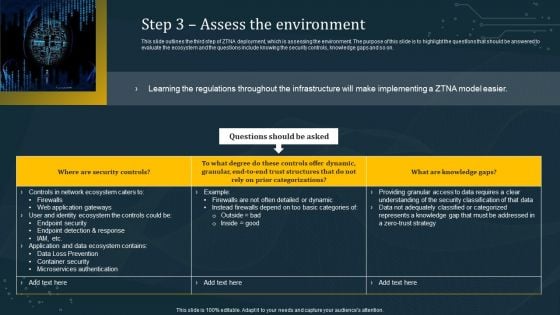
Step 3 Assess The Environment Elements PDF
This slide outlines the third step of ZTNA deployment, which is assessing the environment. The purpose of this slide is to highlight the questions that should be answered to evaluate the ecosystem and the questions include knowing the security controls, knowledge gaps and so on. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Step 3 Assess The Environment Elements PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Step 3 Assess The Environment Elements PDF today and make your presentation stand out from the rest

Regulations Of Security Tokenization Strategies For Data Security PPT Template
This slide discusses the regulations of security tokens for data security. The purpose of this slide is to showcase various security token regulations which include D, A, S regulations, etc. Find a pre-designed and impeccable Regulations Of Security Tokenization Strategies For Data Security PPT Template. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation. This slide discusses the regulations of security tokens for data security. The purpose of this slide is to showcase various security token regulations which include D, A, S regulations, etc.
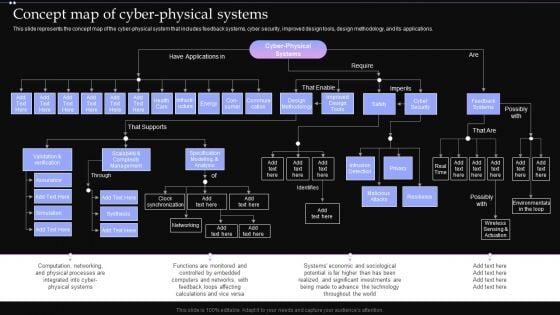
Concept Map Of Cyber Physical Systems Ppt PowerPoint Presentation File Backgrounds PDF
This slide represents the concept map of the cyber physical system that includes feedback systems, cyber security, improved design tools, design methodology, and its applications. Presenting this PowerPoint presentation, titled Concept Map Of Cyber Physical Systems Ppt PowerPoint Presentation File Backgrounds PDF, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Concept Map Of Cyber Physical Systems Ppt PowerPoint Presentation File Backgrounds PDF. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Concept Map Of Cyber Physical Systems Ppt PowerPoint Presentation File Backgrounds PDF that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.

Tech Solution Company Elevator Pitch Deck Client Testimonials Summary PDF
This slide caters to the details related to the clients feedback based on their experiences. It consists of information about a company that provides solutions to manufacturers unique problems, creating secure, well designed solutions, and generating data-driven insights. Create an editable Tech Solution Company Elevator Pitch Deck Client Testimonials Summary PDF that communicates your idea and engages your audience. Whether youre presenting a business or an educational presentation, pre designed presentation templates help save time. Tech Solution Company Elevator Pitch Deck Client Testimonials Summary PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
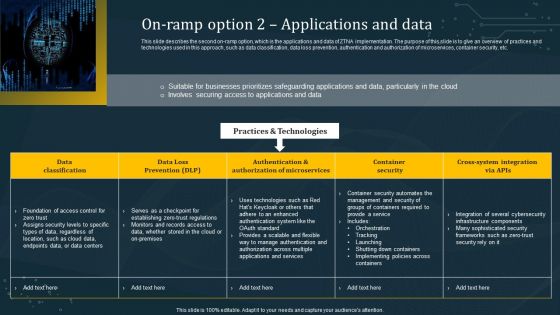
On Ramp Option 2 Applications And Data Template PDF
This slide describes the second on-ramp option, which is the applications and data of ZTNA implementation. The purpose of this slide is to give an overview of practices and technologies used in this approach, such as data classification, data loss prevention, authentication and authorization of microservices, container security, etc. Take your projects to the next level with our ultimate collection of On Ramp Option 2 Applications And Data Template PDF. Slidegeeks has designed a range of layouts that are perfect for representing task or activity duration, keeping track of all your deadlines at a glance. Tailor these designs to your exact needs and give them a truly corporate look with your own brand colors they will make your projects stand out from the rest

Deploying Cloud Technology Deployment Of Cloud Project Management Model Ppt Summary Template PDF
This slide showcases deployment of cloud project management model. It provides information about public, private, hybrid, setup, data security, data control, privacy, scalability, integration, etc. Do you have an important presentation coming up. Are you looking for something that will make your presentation stand out from the rest Look no further than Deploying Cloud Technology Deployment Of Cloud Project Management Model Ppt Summary Template PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Deploying Cloud Technology Deployment Of Cloud Project Management Model Ppt Summary Template PDF today and make your presentation stand out from the rest.
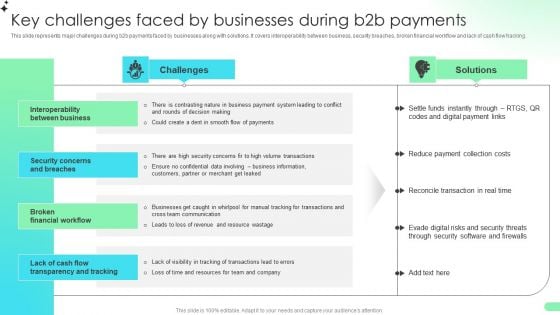
Key Challenges Faced By Businesses During B2b Payments Comprehensive Guide For Developing Rules PDF
This slide represents major challenges during b2b payments faced by businesses along with solutions. It covers interoperability between business, security breaches, broken financial workflow and lack of cash flow tracking.This Key Challenges Faced By Businesses During B2b Payments Comprehensive Guide For Developing Rules PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Key Challenges Faced By Businesses During B2b Payments Comprehensive Guide For Developing Rules PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today
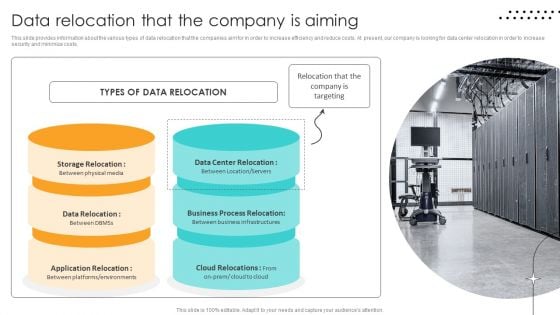
Cost Saving Benefits Of Implementing Data Center Data Relocation That The Company Is Aiming Ideas PDF
This slide provides information about the various types of data relocation that the companies aim for in order to increase efficiency and reduce costs. At present, our company is looking for data center relocation in order to increase security and minimize costs. Get a simple yet stunning designed Cost Saving Benefits Of Implementing Data Center Data Relocation That The Company Is Aiming Ideas PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy to edit Cost Saving Benefits Of Implementing Data Center Data Relocation That The Company Is Aiming Ideas PDF can be your go to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.
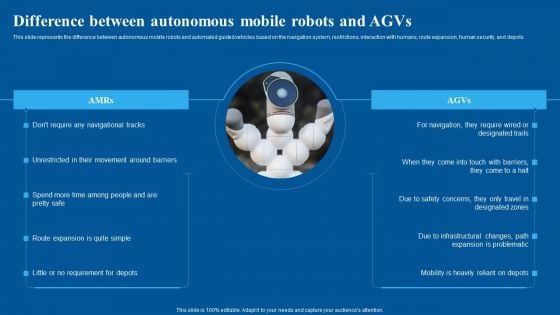
Difference Between Autonomous Mobile Robots And Agvs Brochure PDF
This slide represents the difference between autonomous mobile robots and automated guided vehicles based on the navigation system, restrictions, interaction with humans, route expansion, human security, and depots. Slidegeeks is here to make your presentations a breeze with Difference Between Autonomous Mobile Robots And Agvs Brochure PDF With our easy to use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.
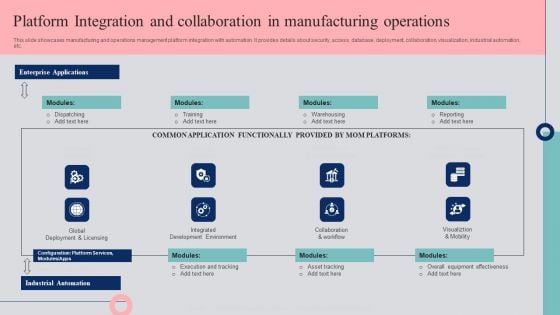
Platform Integration And Collaboration In Manufacturing Operations Template PDF
This slide showcases manufacturing and operations management platform integration with automation. It provides details about security, access, database, deployment, collaboration, visualization, industrial automation, etc. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Platform Integration And Collaboration In Manufacturing Operations Template PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Platform Integration And Collaboration In Manufacturing Operations Template PDF today and make your presentation stand out from the rest
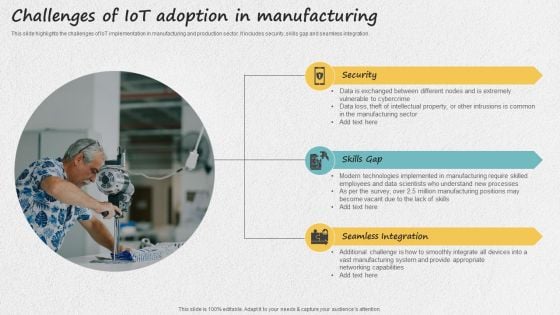
Iot Applications For Manufacturing Industry Challenges Of Iot Adoption In Manufacturing Slides PDF
This slide highlights the challenges of IoT implementation in manufacturing and production sector. It includes security, skills gap and seamless integration. This Iot Applications For Manufacturing Industry Challenges Of Iot Adoption In Manufacturing Slides PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Iot Applications For Manufacturing Industry Challenges Of Iot Adoption In Manufacturing Slides PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today
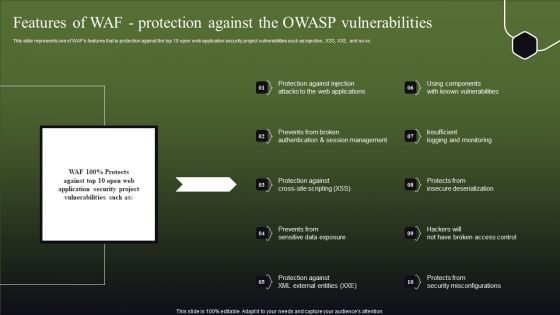
Features Of WAF Protection Against The OWASP Vulnerabilities Slides PDF
This slide represents one of WAFs features that is protection against the top 10 open web application security project vulnerabilities such as injection, XSS, XXE, and so on. This Features Of WAF Protection Against The OWASP Vulnerabilities Slides PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Features Of WAF Protection Against The OWASP Vulnerabilities Slides PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today
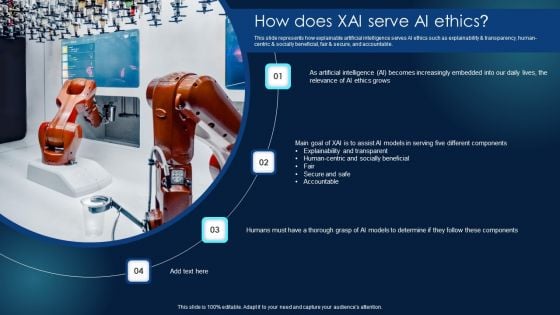
Explainable Machine Learning Explainable ML How Does XAI Serve AI Ethics Infographics PDF
This slide represents how explainable artificial intelligence serves AI ethics such as explainability and transparency, human-centric and socially beneficial, fair and secure, and accountable. Get a simple yet stunning designed Explainable Machine Learning Explainable ML How Does XAI Serve AI Ethics Infographics PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Explainable Machine Learning Explainable ML How Does XAI Serve AI Ethics Infographics PDF can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.
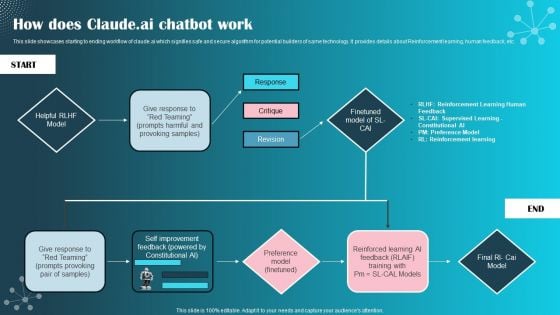
How Does Claude Ai Chatbot Work Ppt PowerPoint Presentation File Model PDF
This slide showcases starting to ending workflow of claude.ai which signifies safe and secure algorithm for potential builders of same technology. It provides details about Reinforcement learning, human feedback, etc. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than How Does Claude Ai Chatbot Work Ppt PowerPoint Presentation File Model PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab How Does Claude Ai Chatbot Work Ppt PowerPoint Presentation File Model PDF today and make your presentation stand out from the rest.
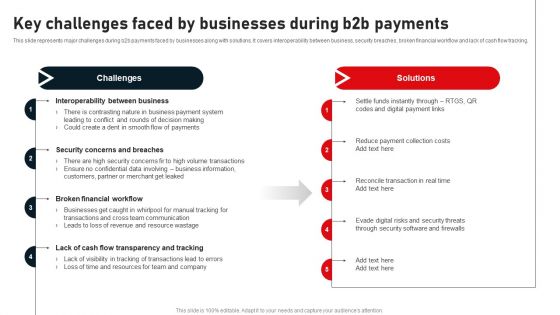
Key Challenges Faced By Businesses During B2B Payments Structure PDF
This slide represents major challenges during b2b payments faced by businesses along with solutions. It covers interoperability between business, security breaches, broken financial workflow and lack of cash flow tracking. Slidegeeks is here to make your presentations a breeze with Key Challenges Faced By Businesses During B2B Payments Structure PDF With our easy to use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.
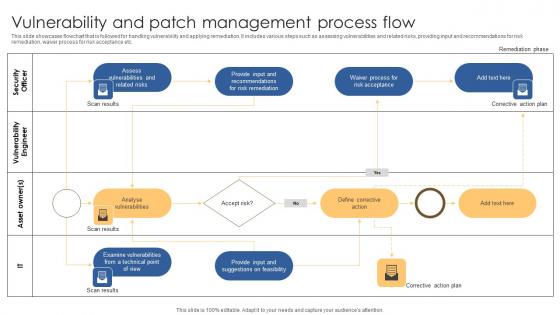
Vulnerability And Patch Management Process Flow Microsoft Pdf
This slide showcases flowchart that is followed for handling vulnerability and applying remediation. It includes various steps such as assessing vulnerabilities and related risks, providing input and recommendations for risk remediation, waiver process for risk acceptance etc. Pitch your topic with ease and precision using this Vulnerability And Patch Management Process Flow Microsoft Pdf. This layout presents information on Security Officer, Vulnerability Engineer, Asset Owner. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout. This slide showcases flowchart that is followed for handling vulnerability and applying remediation. It includes various steps such as assessing vulnerabilities and related risks, providing input and recommendations for risk remediation, waiver process for risk acceptance etc.
Icon Global Security In Powerpoint And Google Slides Cpb
Introducing our well designed Icon Global Security In Powerpoint And Google Slides Cpb. This PowerPoint design presents information on topics like Icon Global Security. As it is predesigned it helps boost your confidence level. It also makes you a better presenter because of its high quality content and graphics. This PPT layout can be downloaded and used in different formats like PDF, PNG, and JPG. Not only this, it is available in both Standard Screen and Widescreen aspect ratios for your convenience. Therefore, click on the download button now to persuade and impress your audience. Our Icon Global Security In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
Icons Slide For Tokenization Strategies For Data Security PPT Presentation
Introducing our well designed Icons Slide For Tokenization Strategies For Data Security PPT Presentation set of slides. The slide displays editable icons to enhance your visual presentation. The icons can be edited easily. So customize according to your business to achieve a creative edge. Download and share it with your audience. Our Icons Slide For Tokenization Strategies For Data Security PPT Presentation are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
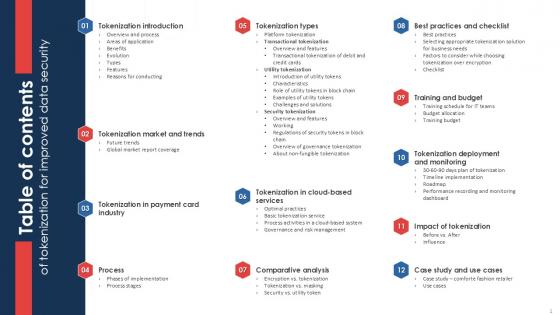
Table Of Contents Of Tokenization For Improved Data Security PPT Sample
Boost your pitch with our creative Table Of Contents Of Tokenization For Improved Data Security PPT Sample. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them. Our Table Of Contents Of Tokenization For Improved Data Security PPT Sample are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Table Of Contents Of Securing Your Data With Tokenization Ppt Sample
Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Table Of Contents Of Securing Your Data With Tokenization Ppt Sample a try. Our experts have put a lot of knowledge and effort into creating this impeccable Table Of Contents Of Securing Your Data With Tokenization Ppt Sample You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today Our Table Of Contents Of Securing Your Data With Tokenization Ppt Sample are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
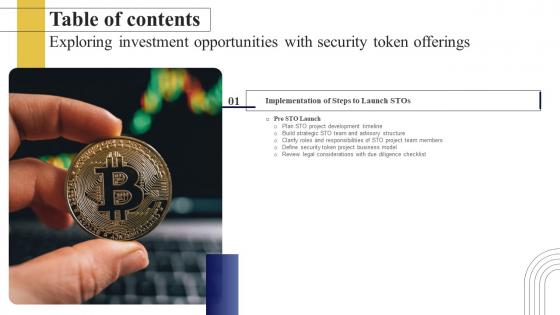
Exploring Investment Opportunities With Security Token Table Of Contents Infographics Pdf
The best PPT templates are a great way to save time, energy, and resources. Slidegeeks have 100 percent editable powerpoint slides making them incredibly versatile. With these quality presentation templates, you can create a captivating and memorable presentation by combining visually appealing slides and effectively communicating your message. Download Exploring Investment Opportunities With Security Token Table Of Contents Infographics Pdf from Slidegeeks and deliver a wonderful presentation. Our Exploring Investment Opportunities With Security Token Table Of Contents Infographics Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Agenda For Securing Your Data With Tokenization Ppt Template
Create an editable Agenda For Securing Your Data With Tokenization Ppt Template that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. Agenda For Securing Your Data With Tokenization Ppt Template is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay. Our Agenda For Securing Your Data With Tokenization Ppt Template are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Agenda For Zero Trust Network Security Pictures Pdf
Find a pre-designed and impeccable Agenda For Zero Trust Network Security Pictures Pdf. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation. Our Agenda For Zero Trust Network Security Pictures Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
Encryption Techniques Icon For Securing Big Data Monitoring Mockup pdf
Showcasing this set of slides titled Encryption Techniques Icon For Securing Big Data Monitoring Mockup pdf. The topics addressed in these templates are Encryption Techniques, IconSecuring, Big Data Monitoring. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting. Our Encryption Techniques Icon For Securing Big Data Monitoring Mockup pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
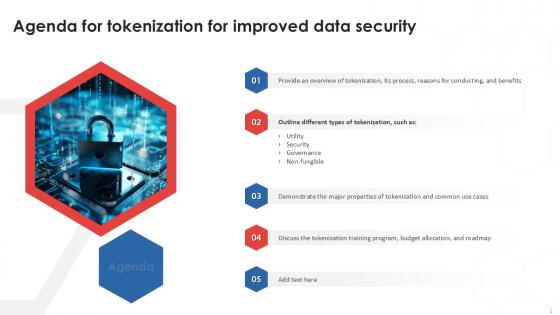
Agenda For Tokenization For Improved Data Security PPT Powerpoint
Find a pre-designed and impeccable Agenda For Tokenization For Improved Data Security PPT Powerpoint. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation. Our Agenda For Tokenization For Improved Data Security PPT Powerpoint are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
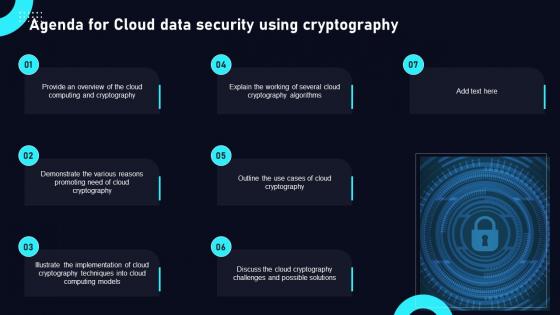
Agenda For Cloud Data Security Using Cryptography Structure Pdf
Find highly impressive Agenda For Cloud Data Security Using Cryptography Structure Pdf on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Agenda For Cloud Data Security Using Cryptography Structure Pdf for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now Our Agenda For Cloud Data Security Using Cryptography Structure Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Teamwork Security In Powerpoint And Google Slides Cpb
Presenting our innovatively designed set of slides titled Teamwork Security In Powerpoint And Google Slides Cpb. This completely editable PowerPoint graphic exhibits Teamwork Security that will help you convey the message impactfully. It can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. Apart from this, you can download this well structured PowerPoint template design in different formats like PDF, JPG, and PNG. So, click the download button now to gain full access to this PPT design. Our Teamwork Security In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
Secure Home Network Diagram In Powerpoint And Google Slides Cpb
Presenting our innovatively designed set of slides titled Secure Home Network Diagram In Powerpoint And Google Slides Cpb. This completely editable PowerPoint graphic exhibits Secure Home Network Diagram that will help you convey the message impactfully. It can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. Apart from this, you can download this well structured PowerPoint template design in different formats like PDF, JPG, and PNG. So, click the download button now to gain full access to this PPT design. Our Secure Home Network Diagram In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Computer Flaw Cyber Security In Powerpoint And Google Slides Cpb
Presenting our innovatively designed set of slides titled Computer Flaw Cyber Security In Powerpoint And Google Slides Cpb. This completely editable PowerPoint graphic exhibits Computer Flaw Cyber Security that will help you convey the message impactfully. It can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. Apart from this, you can download this well structured PowerPoint template design in different formats like PDF, JPG, and PNG. So, click the download button now to gain full access to this PPT design. Our Computer Flaw Cyber Security In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Tab Manager Security In Powerpoint And Google Slides Cpb
Presenting our innovatively designed set of slides titled Tab Manager Security In Powerpoint And Google Slides Cpb. This completely editable PowerPoint graphic exhibits Tab Manager Security that will help you convey the message impactfully. It can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. Apart from this, you can download this well structured PowerPoint template design in different formats like PDF, JPG, and PNG. So, click the download button now to gain full access to this PPT design. Our Tab Manager Security In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
Application Security Icon In Powerpoint And Google Slides Cpb
Introducing our well designed Application Security Icon In Powerpoint And Google Slides Cpb. This PowerPoint design presents information on topics like Application Security Icon. As it is predesigned it helps boost your confidence level. It also makes you a better presenter because of its high-quality content and graphics. This PPT layout can be downloaded and used in different formats like PDF, PNG, and JPG. Not only this, it is available in both Standard Screen and Widescreen aspect ratios for your convenience. Therefore, click on the download button now to persuade and impress your audience. Our Application Security Icon In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Security Camera System Business In Powerpoint And Google Slides Cpb
Introducing our well-designed Security Camera System Business In Powerpoint And Google Slides Cpb. This PowerPoint design presents information on topics like Security Camera System Business. As it is predesigned it helps boost your confidence level. It also makes you a better presenter because of its high-quality content and graphics. This PPT layout can be downloaded and used in different formats like PDF, PNG, and JPG. Not only this, it is available in both Standard Screen and Widescreen aspect ratios for your convenience. Therefore, click on the download button now to persuade and impress your audience. Our Security Camera System Business In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
Big Data Monitoring Security Icon Download pdf
Pitch your topic with ease and precision using this Big Data Monitoring Security Icon Download pdf. This layout presents information on Big Data Monitoring, Security Icon. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout. Our Big Data Monitoring Security Icon Download pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Tokenization In Payment Card Industry For Data Security Securing Your Data Ppt Example
This slide outlines the introduction of tokenization in payment card industry. The purpose of this slide is to showcase the process of tokenization in payment card industry to secure non sharable details of client. Slidegeeks is here to make your presentations a breeze with Tokenization In Payment Card Industry For Data Security Securing Your Data Ppt Example With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first This slide outlines the introduction of tokenization in payment card industry. The purpose of this slide is to showcase the process of tokenization in payment card industry to secure non sharable details of client.
Icons Slide For Zero Trust Security Template Pdf
Introducing our well designed Icons Slide For Zero Trust Security Template Pdf set of slides. The slide displays editable icons to enhance your visual presentation. The icons can be edited easily. So customize according to your business to achieve a creative edge. Download and share it with your audience. Our Icons Slide For Zero Trust Security Template Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
Icons Slide For Cloud Data Security Using Cryptography Diagrams Pdf
Introducing our well designed Icons Slide For Cloud Data Security Using Cryptography Diagrams Pdf set of slides. The slide displays editable icons to enhance your visual presentation. The icons can be edited easily. So customize according to your business to achieve a creative edge. Download and share it with your audience. Our Icons Slide For Cloud Data Security Using Cryptography Diagrams Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
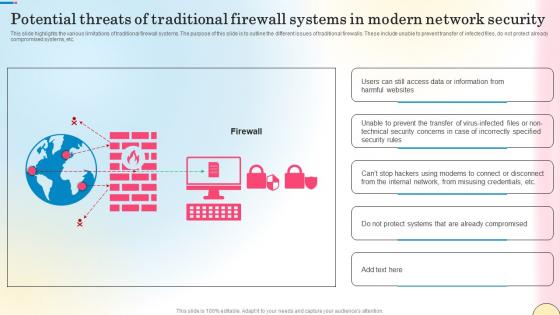
Potential Threats Of Traditional Firewall Systems Security Network Security Portrait Pdf
This slide highlights the various limitations of traditional firewall systems. The purpose of this slide is to outline the different issues of traditional firewalls. These include unable to prevent transfer of infected files, do not protect already compromised systems, etc. Create an editable Potential Threats Of Traditional Firewall Systems Security Network Security Portrait Pdf that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. Potential Threats Of Traditional Firewall Systems Security Network Security Portrait Pdf is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay. This slide highlights the various limitations of traditional firewall systems. The purpose of this slide is to outline the different issues of traditional firewalls. These include unable to prevent transfer of infected files, do not protect already compromised systems, etc.
Multiple Device Based Internet Of Things Security Icon Formats Pdf
Showcasing this set of slides titled Multiple Device Based Internet Of Things Security Icon Formats Pdf The topics addressed in these templates are Multiple Device Based, Internet Of Things, Security Icon All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting. Our Multiple Device Based Internet Of Things Security Icon Formats Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
Cyber Security Breach Icon To Prevent Threat Brochure Pdf
Pitch your topic with ease and precision using this Cyber Security Breach Icon To Prevent Threat Brochure Pdf This layout presents information on Cyber Security Breach, Icon To Prevent Threat It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout. Our Cyber Security Breach Icon To Prevent Threat Brochure Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

CASB 2 0 IT Cloud Access Security Broker And Secure Web Gateway
This slide represents how CASB 2.0 not just discovers the shadow IT but helps to control it too. The purpose of this slide is to showcase how CASB 2.0 improves the SWG model by empowering it with rich cloud app data, getting dynamic control of shadow IT and simplifying deployment. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our CASB 2 0 IT Cloud Access Security Broker And Secure Web Gateway was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into CASB 2 0 IT Cloud Access Security Broker And Secure Web Gateway. This slide represents how CASB 2.0 not just discovers the shadow IT but helps to control it too. The purpose of this slide is to showcase how CASB 2.0 improves the SWG model by empowering it with rich cloud app data, getting dynamic control of shadow IT and simplifying deployment.

Best Security Management In Powerpoint And Google Slides Cpb
Presenting our innovatively designed set of slides titled Best Security Management In Powerpoint And Google Slides Cpb. This completely editable PowerPoint graphic exhibits Best Security Management that will help you convey the message impactfully. It can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. Apart from this, you can download this well structured PowerPoint template design in different formats like PDF, JPG, and PNG. So, click the download button now to gain full access to this PPT design. Our Best Security Management In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
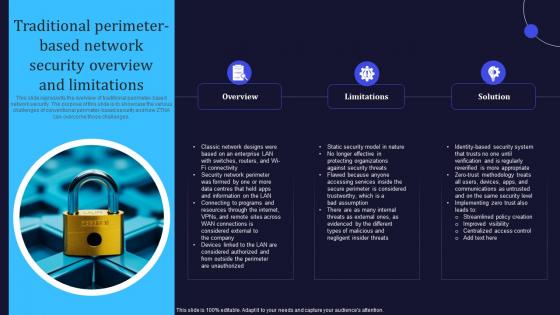
Zero Trust Model Traditional Perimeter Based Network Security Overview
This slide represents the overview of traditional perimeter-based network security. The purpose of this slide is to showcase the various challenges of conventional perimeter-based security and how ZTNA can overcome those challenges. If you are looking for a format to display your unique thoughts, then the professionally designed Zero Trust Model Traditional Perimeter Based Network Security Overview is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Zero Trust Model Traditional Perimeter Based Network Security Overview and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. This slide represents the overview of traditional perimeter-based network security. The purpose of this slide is to showcase the various challenges of conventional perimeter-based security and how ZTNA can overcome those challenges.
Icons Slide For Securing Your Data With Tokenization Ppt Slide
Download our innovative and attention grabbing Icons Slide For Securing Your Data With Tokenization Ppt Slide template. The set of slides exhibit completely customizable icons. These icons can be incorporated into any business presentation. So download it immediately to clearly communicate with your clientele. Our Icons Slide For Securing Your Data With Tokenization Ppt Slide are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Complete Guide To Launch Best Practices For Website Security Management
Following slide showcases best practices that can be used by business to protect website from cyber attacks and threats. It include pointers such as incest in SSL certifications, anti malware programs, regular backups etc. Get a simple yet stunning designed Complete Guide To Launch Best Practices For Website Security Management. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Complete Guide To Launch Best Practices For Website Security Management can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today. Following slide showcases best practices that can be used by business to protect website from cyber attacks and threats. It include pointers such as incest in SSL certifications, anti malware programs, regular backups etc.

Agenda For Building Trust With IoT Security And Privacy Measures IoT SS V
Find a pre-designed and impeccable Agenda For Building Trust With IoT Security And Privacy Measures IoT SS V. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation. Our Agenda For Building Trust With IoT Security And Privacy Measures IoT SS V are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
Icons Slide For Exploring Investment Opportunities With Security Token Offerings Infographics Pdf
Introducing our well designed Icons Slide For Exploring Investment Opportunities With Security Token Offerings Infographics Pdf set of slides. The slide displays editable icons to enhance your visual presentation. The icons can be edited easily. So customize according to your business to achieve a creative edge. Download and share it with your audience. Our Icons Slide For Exploring Investment Opportunities With Security Token Offerings Infographics Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.


 Continue with Email
Continue with Email

 Home
Home


































