Cyber
Types Cyber Security Risks Ppt PowerPoint Presentation Model Backgrounds Cpb
Presenting this set of slides with name types cyber security risks ppt powerpoint presentation model backgrounds cpb. This is an editable Powerpoint four stages graphic that deals with topics like types cyber security risks to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Business Cyber Risk Ppt PowerPoint Presentation Ideas Designs Download Cpb
Presenting this set of slides with name business cyber risk ppt powerpoint presentation ideas designs download cpb. This is an editable Powerpoint three stages graphic that deals with topics like business cyber risk to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Cyber Security Communication Ppt PowerPoint Presentation Model Background Designs Cpb
Presenting this set of slides with name cyber security communication ppt powerpoint presentation model background designs cpb. This is an editable Powerpoint three stages graphic that deals with topics like cyber security communication to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Managing Cyber Security Risks Ppt PowerPoint Presentation Outline Slide Cpb
Presenting this set of slides with name managing cyber security risks ppt powerpoint presentation outline slide cpb. This is an editable Powerpoint four stages graphic that deals with topics like managing cyber security risks to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Cyber Security Process Compliance Ppt PowerPoint Presentation Ideas Inspiration Cpb
Presenting this set of slides with name cyber security process compliance ppt powerpoint presentation ideas inspiration cpb. This is an editable Powerpoint four stages graphic that deals with topics like cyber security process compliance to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Cyber Case Management Ppt PowerPoint Presentation Layouts Design Templates Cpb
Presenting this set of slides with name cyber case management ppt powerpoint presentation layouts design templates cpb. This is an editable Powerpoint six stages graphic that deals with topics like cyber case management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Situational Awareness Cyber Security Ppt PowerPoint Presentation Model Influencers Cpb
Presenting this set of slides with name situational awareness cyber security ppt powerpoint presentation model influencers cpb. This is an editable Powerpoint six stages graphic that deals with topics like situational awareness cyber security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Cyber Incident Response Plan Ppt PowerPoint Presentation Icon Guide Cpb
Presenting this set of slides with name cyber incident response plan ppt powerpoint presentation icon guide cpb. This is an editable Powerpoint four stages graphic that deals with topics like cyber incident response plan to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Cyber Resilience Framework Ppt PowerPoint Presentation Pictures Structure Cpb Pdf
Presenting this set of slides with name cyber resilience framework ppt powerpoint presentation pictures structure cpb pdf. This is an editable Powerpoint six stages graphic that deals with topics like cyber resilience framework to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Cyber Attack Protection Ppt PowerPoint Presentation Model Inspiration Cpb Pdf
Presenting this set of slides with name cyber attack protection ppt powerpoint presentation model inspiration cpb pdf. This is an editable Powerpoint four stages graphic that deals with topics like cyber attack protection to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Cyber Awareness Challenges Ppt PowerPoint Presentation Model Diagrams Cpb Pdf
Presenting this set of slides with name cyber awareness challenges ppt powerpoint presentation model diagrams cpb pdf. This is an editable Powerpoint five stages graphic that deals with topics like cyber awareness challenges to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Applications Cyber Security Ppt PowerPoint Presentation Infographics Brochure Cpb Pdf
Presenting this set of slides with name applications cyber security ppt powerpoint presentation infographics brochure cpb pdf. This is an editable Powerpoint four stages graphic that deals with topics like applications cyber security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Cyber Slacking Ppt PowerPoint Presentation Ideas Graphic Images Cpb Pdf
Presenting this set of slides with name cyber slacking ppt powerpoint presentation ideas graphic images cpb pdf. This is an editable Powerpoint one stages graphic that deals with topics like cyber slacking to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
IOT Cyber Security Ppt PowerPoint Presentation Layouts Clipart Cpb
Presenting this set of slides with name iot cyber security ppt powerpoint presentation layouts clipart cpb. This is an editable Powerpoint four stages graphic that deals with topics like iot cyber security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
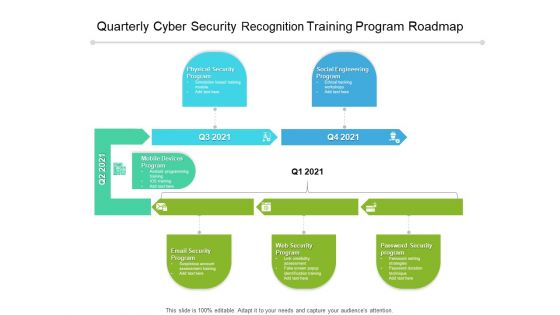
Quarterly Cyber Security Recognition Training Program Roadmap Elements
We present our quarterly cyber security recognition training program roadmap elements. This PowerPoint layout is easy-to-edit so you can change the font size, font type, color, and shape conveniently. In addition to this, the PowerPoint layout is Google Slides compatible, so you can share it with your audience and give them access to edit it. Therefore, download and save this well-researched quarterly cyber security recognition training program roadmap elements in different formats like PDF, PNG, and JPG to smoothly execute your business plan.
Organization Cyber Security Dashboard Ppt Icon Sample PDF
This slide covers the cyber security key performance indicators for the organization including application health, device license consumption, data encryption status and many more Deliver and pitch your topic in the best possible manner with this organization cyber security dashboard ppt icon sample pdf. Use them to share invaluable insights on makes and models, application health, license consumption, operating systems and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
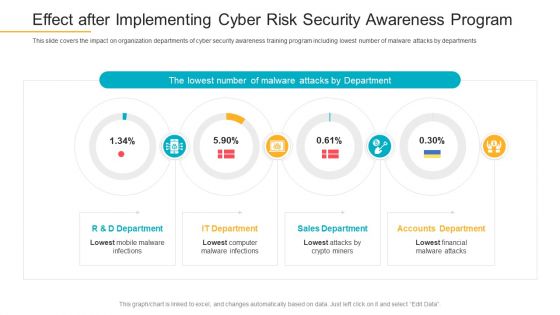
Effect After Implementing Cyber Risk Security Awareness Program Infographics PDF
This slide covers the impact on organization departments of cyber security awareness training program including lowest number of malware attacks by departments. Deliver an awe-inspiring pitch with this creative effect after implementing cyber risk security awareness program infographics pdf bundle. Topics like sales department, accounts department, it department can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Companys Data Safety Recognition Organization Cyber Security Dashboard Pictures PDF
This slide covers the cyber security key performance indicators for the organization including application health, device license consumption, data encryption status and many more. Deliver an awe-inspiring pitch with this creative companys data safety recognition organization cyber security dashboard pictures pdf bundle. Topics like application health, operating systems, encryption status can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Case Study 2 Banks Cyber Security Infrastructure Mockup PDF
Presenting case study 2 banks cyber security infrastructure mockup pdf to provide visual cues and insights. Share and navigate important information on two stages that need your due attention. This template can be used to pitch topics like case study 2 banks cyber security infrastructure. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Organization Cyber Security Dashboard Ppt Show Outfit PDF
This slide covers the cyber security key performance indicators for the organization including application health, device license consumption, data encryption status and many more. Deliver an awe inspiring pitch with this creative organization cyber security dashboard ppt show outfit pdf bundle. Topics like operating systems, license consumption, makes and models, other employees can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
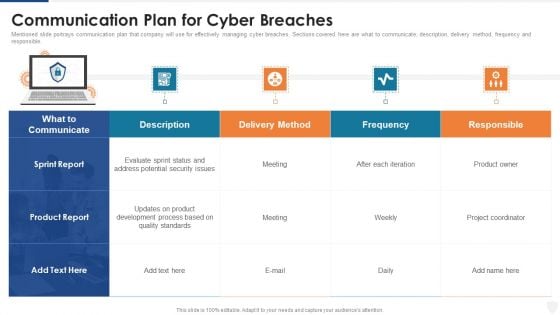
Communication Plan For Cyber Breaches Ppt Layouts Ideas PDF
Mentioned slide portrays communication plan that company will use for effectively managing cyber breaches. Sections covered here are what to communicate, description, delivery method, frequency and responsible. Deliver an awe inspiring pitch with this creative communication plan for cyber breaches ppt layouts ideas pdf bundle. Topics like potential security, development process, method can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
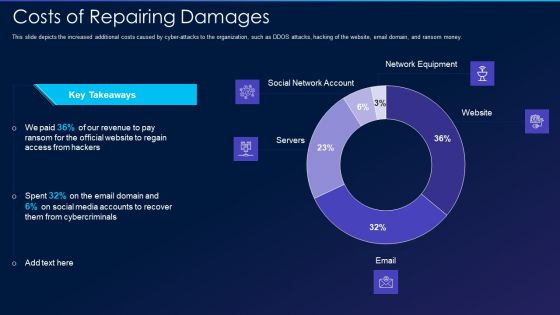
Cyber Exploitation IT Costs Of Repairing Damages Themes PDF
This slide depicts the increased additional costs caused by cyber-attacks to the organization, such as DDOS attacks, hacking of the website, email domain, and ransom money. Deliver an awe inspiring pitch with this creative cyber exploitation it costs of repairing damages themes pdf bundle. Topics like social network account, servers, network equipment, website can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Cyber Exploitation IT Dashboard For Threat Tracking Topics PDF
This slide depicts the dashboard for threat tracking through cyber security measures and ethical hackers by covering monthly threat status, current risk status, threat-based on the role, threats by owners, risk by threats, and threat report. Deliver an awe inspiring pitch with this creative cyber exploitation it dashboard for threat tracking topics pdf bundle. Topics like dashboard for threat tracking can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
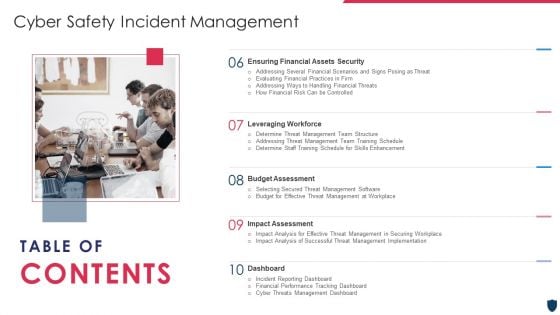
Table Of Contents Cyber Safety Incident Management Security Microsoft PDF
This is a table of contents cyber safety incident management security microsoft pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like current scenario assessment, handling cyber threats to secure digital assets, ensuring physical security, securing firm from natural calamity threats . You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
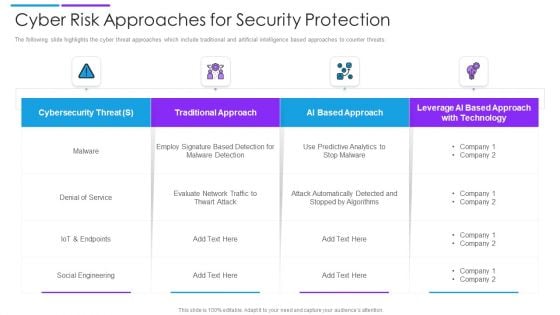
Cyber Risk Approaches For Security Protection Structure PDF
The following slide highlights the cyber threat approaches which include traditional and artificial intelligence based approaches to counter threats. Showcasing this set of slides titled cyber risk approaches for security protection structure pdf. The topics addressed in these templates are traditional approach, ai based approach, cybersecurity threat. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
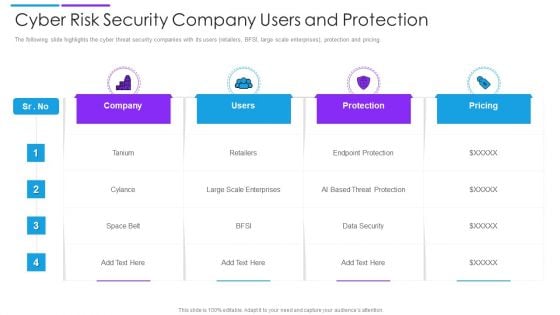
Cyber Risk Security Company Users And Protection Introduction PDF
The following slide highlights the cyber threat security companies with its users retailers, BFSI, large scale enterprises, protection and pricing. Showcasing this set of slides titled cyber risk security company users and protection introduction pdf. The topics addressed in these templates are company, users, protection. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
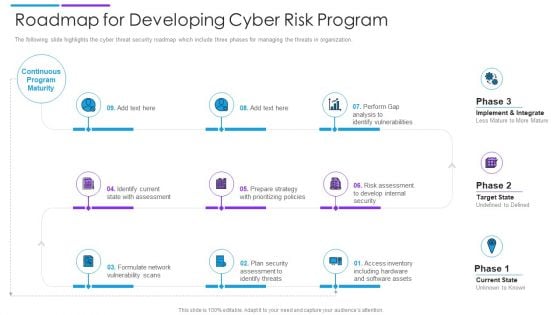
Roadmap For Developing Cyber Risk Program Download PDF
The following slide highlights the cyber threat security roadmap which include three phases for managing the threats in organization. Persuade your audience using this roadmap for developing cyber risk program download pdf. This PPT design covers nine stages, thus making it a great tool to use. It also caters to a variety of topics including internal security, software assets, identify threats. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
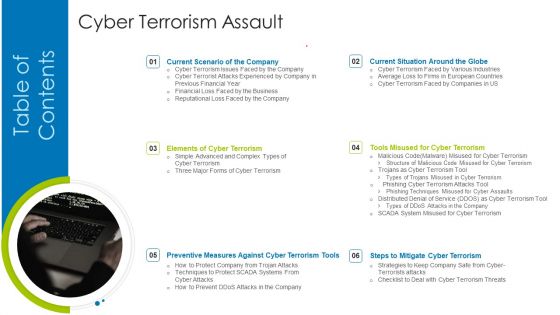
Table Of Content Cyber Terrorism Assault Rules Designs PDF
This is a table of content cyber terrorism assault rules designs pdf template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like assessment matrix of cyber terrorism, impact of implementing, dashboard for threat tracking You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Comparison Checklist For Cyber Cloud And Advanced DR Portrait PDF
The following slide illustrates the cloud disaster recovery solution which also highlights functions like files backup, local recovery and automated VPN connection. Showcasing this set of slides titled comparison checklist for cyber cloud and advanced dr portrait pdf. The topics addressed in these templates are comparison checklist for cyber cloud and advanced dr. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
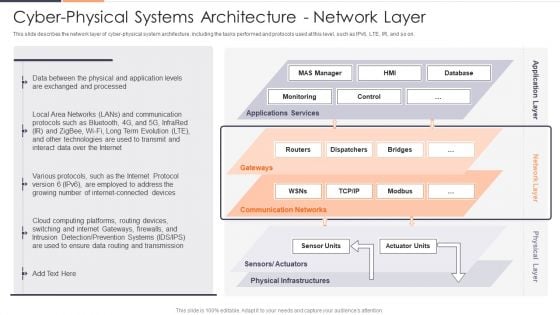
Cyber Physical Systems Architecture Network Layer Ppt Layouts Outline PDF
This slide describes the network layer of cyber physical system architecture, including the tasks performed and protocols used at this level, such as IPv6, LTE, IR, and so on. Deliver an awe inspiring pitch with this creative Cyber Physical Systems Architecture Network Layer Ppt Layouts Outline PDF bundle. Topics like Internet Connected Devices, Internet Protocol, Evolution can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Cyber Physical Systems In Manufacturing Ppt Icon Good PDF
This slide represents the application of CPS in manufacturing, including its five C structure such as connection, conversion, cyber, cognition, and configuration. Deliver an awe inspiring pitch with this creative Cyber Physical Systems In Manufacturing Ppt Icon Good PDF bundle. Topics like Manufacturing Industry, Industrial Processes, Manufacturing Environment can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
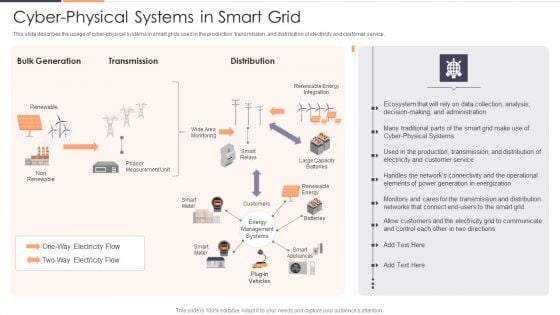
Cyber Physical Systems In Smart Grid Ppt Outline Microsoft PDF
This slide describes the usage of cyber-physical systems in smart grids used in the production, transmission, and distribution of electricity and customer service. Deliver an awe inspiring pitch with this creative Cyber Physical Systems In Smart Grid Ppt Outline Microsoft PDF bundle. Topics like Customer Service, Analysis, Communicate can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Working Of Cyber Physical Systems Ppt Pictures Demonstration PDF
This slide covers the working of cyber physical systems and the type of carried out actions such as planned actions and corrective actions. Deliver an awe inspiring pitch with this creative Working Of Cyber Physical Systems Ppt Pictures Demonstration PDF bundle. Topics like Information, Systems, Planned Actions can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
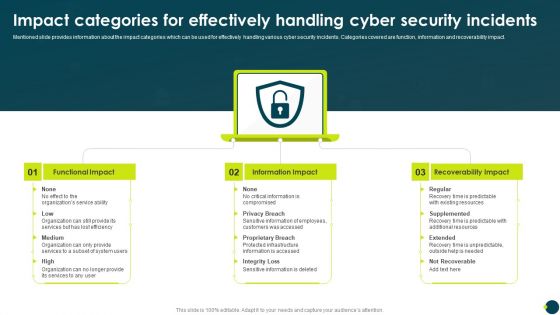
Impact Categories For Effectively Handling Cyber Security Incidents Download PDF
Mentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact.Deliver an awe inspiring pitch with this creative Impact Categories For Effectively Handling Cyber Security Incidents Download PDF bundle. Topics like Functional Impact, Information Impact, Recoverability Impact can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Cyber Safety And Security Reporting Tools For Business Rules PDF
This slide shows comparative analysis of business cyber security reporting software. It includes features, compatibility, price and ratings. Pitch your topic with ease and precision using this Cyber Safety And Security Reporting Tools For Business Rules PDF. This layout presents information on Compatibility, Price, Ratings. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
Icon For Digital Cyber Safety And Security Report Pictures PDF
Persuade your audience using this Icon For Digital Cyber Safety And Security Report Pictures PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Security Report, Icon For Digital, Cyber Safety. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

KPI Metrics For Cyber Safety And Security Report Elements PDF
This slide shows various key performance indicators which can be used to report cyber security. It includes metrics detected intrusion attempts, incident rate, vulnerability patch response times, etc. Showcasing this set of slides titled KPI Metrics For Cyber Safety And Security Report Elements PDF. The topics addressed in these templates are Incident Rate, Application, Metrics. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Cyber Security KPI Dashboard With Metrics Microsoft PDF
This slide showcases dashboard of security support cell based on complaints recorded from ABC company. It includes complaints, non complaints, open and close tickets and security incident by quarter. Showcasing this set of slides titled Cyber Security KPI Dashboard With Metrics Microsoft PDF. The topics addressed in these templates are Cyber Security, Kpi Dashboard With Metrics. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
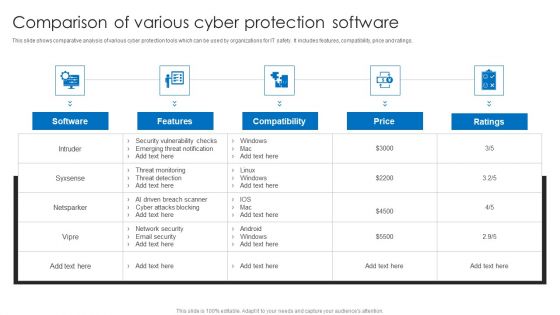
Comparison Of Various Cyber Protection Software Portrait PDF
This slide shows comparative analysis of various cyber protection tools which can be used by organizations for IT safety. It includes features, compatibility, price and ratings. Pitch your topic with ease and precision using this Comparison Of Various Cyber Protection Software Portrait PDF. This layout presents information on Compatibility, Price, Security. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Cyber Security Management Risk Plan Ppt Outline Designs PDF
This slide showcases cyber security issues and action plan to mitigate the risks as per their priority. Risks are prioritized based on their confidentiality, integrity and availability. Pitch your topic with ease and precision using this Cyber Security Management Risk Plan Ppt Outline Designs PDF. This layout presents information on Risk Mitigation Plan, Risk, Confidentiality. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
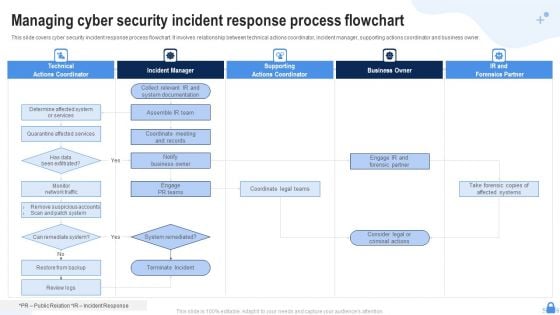
Managing Cyber Security Incident Response Process Flowchart Ppt Templates PDF
This slide covers cyber security incident response process flowchart. It involves relationship between technical actions coordinator, incident manager, supporting actions coordinator and business owner. Presenting Managing Cyber Security Incident Response Process Flowchart Ppt Templates PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Technical Actions Coordinator, Incident Manager, Supporting Actions Coordinator. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
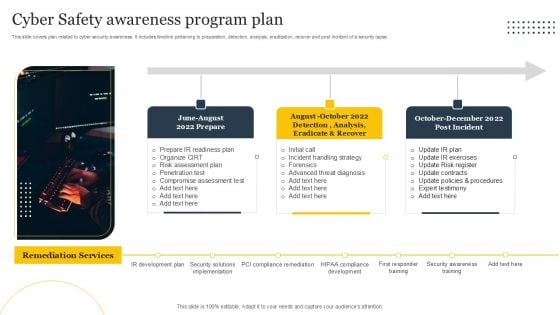
Cyber Safety Awareness Program Plan Ppt Icon Smartart PDF

Business Information Cyber Protection Program For Threat Prevention Background PDF
This slide covers business cyber security program for threat prevention which includes identify, protect, detect, respond and recover.Showcasing this set of slides titled Business Information Cyber Protection Program For Threat Prevention Background PDF. The topics addressed in these templates are Business Environment, Administrative Governance, Evaluating Risk. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
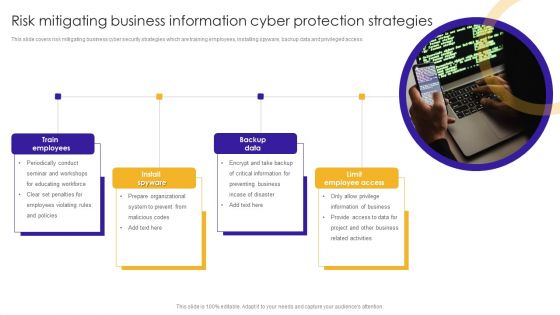
Risk Mitigating Business Information Cyber Protection Strategies Themes PDF
This slide covers risk mitigating business cyber security strategies which are training employees, installing spyware, backup data and privileged access.Presenting Risk Mitigating Business Information Cyber Protection Strategies Themes PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Train Employees, Information Business, Related Activities. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
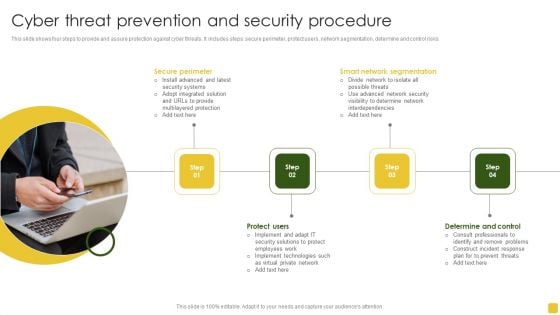
Cyber Threat Prevention And Security Procedure Elements PDF
This slide shows four steps to provide and assure protection against cyber threats. It includes steps secure perimeter, protect users, network segmentation, determine and control risks. Presenting Cyber Threat Prevention And Security Procedure Elements PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Determine Control, Smart Network Segmentation, Secure Perimeter. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Cyber Protection And Precaution Tracking Dashboard Designs PDF
This slide shows the dashboard of cyber safety and security of an organization. It includes risk level, compliance status, tracking and security budget. Showcasing this set of slides titled Cyber Protection And Precaution Tracking Dashboard Designs PDF. The topics addressed in these templates are Risk, Compliance Status, Risk Level. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
IT Divisional Strategy To Improve Cyber Security Measures Icons PDF
This slide signifies information technology department to enhance cyber security measures. It also includes stages like identify, plan, execute and control. Presenting IT Divisional Strategy To Improve Cyber Security Measures Icons PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Identify, Plan, Execute, Control. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
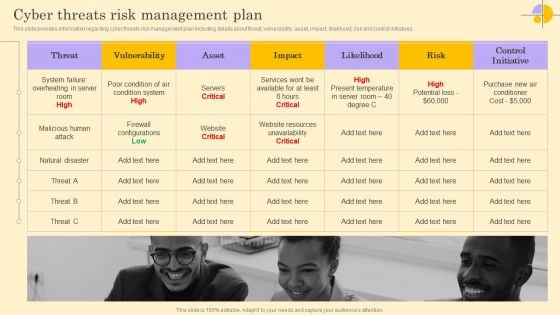
Cyber Threats Risk Management Plan Ppt Portfolio Guide PDF
This slide provides information regarding cyber threats risk management plan including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Find a pre-designed and impeccable Cyber Threats Risk Management Plan Ppt Portfolio Guide PDF. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
Security Operations Cyber Security Icon With Lock Clipart PDF
Persuade your audience using this Security Operations Cyber Security Icon With Lock Clipart PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Security Operations Cyber, Security Icon With Lock. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
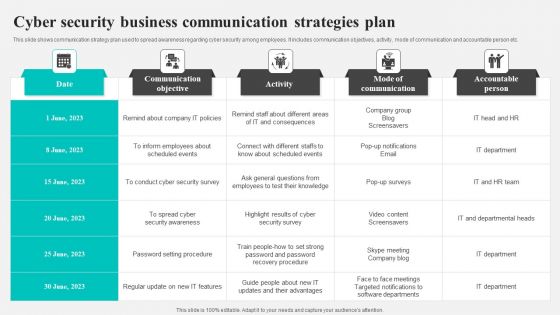
Cyber Security Business Communication Strategies Plan Background PDF
This slide shows communication strategy plan used to spread awareness regarding cyber security among employees. It includes communication objectives, activity, mode of communication and accountable person etc. Showcasing this set of slides titled Cyber Security Business Communication Strategies Plan Background PDF. The topics addressed in these templates are Communication Objective, Activity, Mode Communication. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
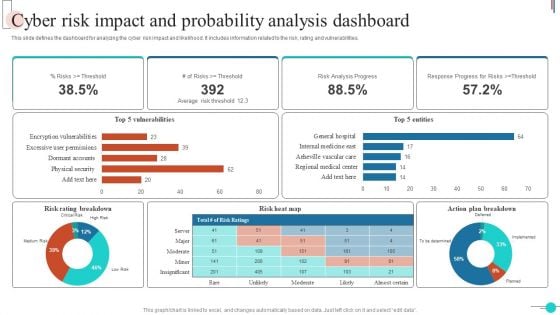
Cyber Risk Impact And Probability Analysis Dashboard Brochure PDF
This slide defines the dashboard for analyzing the cyber risk impact and likelihood. It includes information related to the risk, rating and vulnerabilities. Showcasing this set of slides titled Cyber Risk Impact And Probability Analysis Dashboard Brochure PDF. The topics addressed in these templates are Risk Heat Map, Risk Rating Breakdown, Vulnerabilities. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Risk Management Plan To Manage Cyber Threats Summary PDF
This slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. There are so many reasons you need a Risk Management Plan To Manage Cyber Threats Summary PDF. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
RCA Action Plan For Business Cyber Security Icons PDF
This slide shows root cause analysis action plan to identify and provide strategies for overcoming cyber security threats. It include root cause, action plan and outcomes, etc. Showcasing this set of slides titled RCA Action Plan For Business Cyber Security Icons PDF Elements. The topics addressed in these templates are Root Cause, Action Plan, Outcomes. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
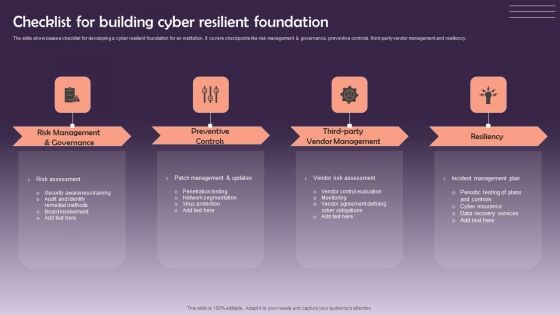
Checklist For Building Cyber Resilient Foundation Sample PDF
The slide showcases a checklist for developing a cyber resilient foundation for an institution. It covers checkpoints like risk management and governance, preventive controls, third-party vendor management and resiliency. Presenting Checklist For Building Cyber Resilient Foundation Sample PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Preventive Controls, Vendor Management, Resiliency. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Cyber Risk Prevention Action Plan Strategy Icon Icons PDF
Persuade your audience using this Cyber Risk Prevention Action Plan Strategy Icon Icons PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Cyber Risk Prevention, Action Plan Strategy. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Cyber Risk Prevention Strategy For Manufacturing Sector Icon Slides PDF
Persuade your audience using this Cyber Risk Prevention Strategy For Manufacturing Sector Icon Slides PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Cyber Risk Prevention Strategy, Manufacturing Sector. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
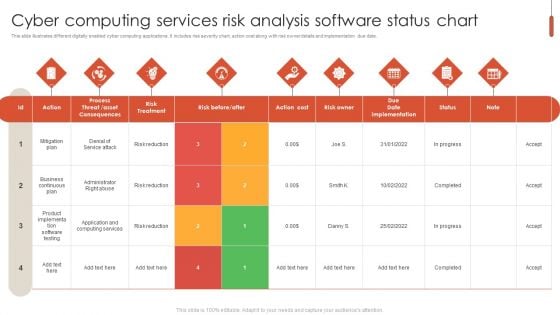
Cyber Computing Services Risk Analysis Software Status Chart Portrait PDF
This slide illustrates different digitally enabled cyber computing applications. It includes risk severity chart, action cost along with risk owner details and implementation due date. Showcasing this set of slides titled Cyber Computing Services Risk Analysis Software Status Chart Portrait PDF. The topics addressed in these templates are Risk Treatment, Risk Owner, Implementation. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
Cyber Security Risk Analysis Shield Software Icon Themes PDF
Persuade your audience using this Cyber Security Risk Analysis Shield Software Icon Themes PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Cyber Security Risk Analysis, Shield Software Icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
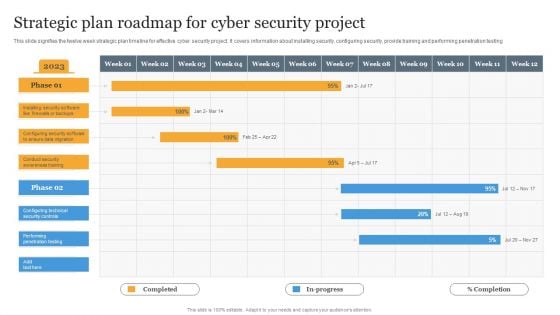
Strategic Plan Roadmap For Cyber Security Project Information PDF
This slide signifies the twelve week strategic plan timeline for effective cyber security project. It covers information about installing security, configuring security, provide training and performing penetration testing Pitch your topic with ease and precision using this Strategic Plan Roadmap For Cyber Security Project Information PDF. This layout presents information on Strategic, Plan, Project. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
Ppt Cyber PowerPoint On Add Success Step Templates
PPT cyber PowerPoint on add success step Templates-Visually support your Microsoft office PPT Presentation with our above Diagram illustrating seventh stage using pink puzzle piece. This way, you can use the idea of a jigsaw quickly and easily in your presentation. Use this Diagram to illustrate your method, piece by piece, and interlock the whole process in the minds of your audience.-PPT cyber PowerPoint on add success step Templates-achievement, activity, adversity, bridge, built, business, cartoon, challenge, character, computer, concept, construction, creativity, decisions, figure, games, goal, graphic, icon, idea, intelligence, organization, people, planning, problems, puzzle, solution, stick, strategy, success Let our Ppt Cyber PowerPoint On Add Success Step Templates be your chauffeur. Be prepared for a grand joyride.


 Continue with Email
Continue with Email

 Home
Home


































