Safety Plan
Person Holding Smart Phone With Security Shield Vector Icon Ppt Infographics Format PDF
Presenting person holding smart phone with security shield vector icon ppt infographics format pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including person holding smart phone with security shield vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Person Using Smart Phone With Security Protection Ppt Portfolio Templates PDF
Presenting person using smart phone with security protection ppt portfolio templates pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including person using smart phone with security protection. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Online Security Lock To Prevent Internet Threats Ppt PowerPoint Presentation File Layouts PDF
Presenting online security lock to prevent internet threats ppt powerpoint presentation file layouts pdf to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including online security lock to prevent internet threats. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Managing Cyber Security Incident Management Icon Ppt Infographics Design Templates PDF
Presenting Managing Cyber Security Incident Management Icon Ppt Infographics Design Templates PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Managing Cyber Security, Incident Management, Icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Security For Cloud Based Systems Icon To Reduce Data Breaches Download PDF
Presenting Security For Cloud Based Systems Icon To Reduce Data Breaches Download PDF to dispense important information. This template comprises Three stages. It also presents valuable insights into the topics including Security For Cloud, Based Systems Icon, Reduce Data Breaches . This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Icon Of Digital Transformation To Boost Financial Institution Industry Security Graphics PDF
Presenting Icon Of Digital Transformation To Boost Financial Institution Industry Security Graphics PDF to dispense important information. This template comprises Four stages. It also presents valuable insights into the topics including Digital Transformation, Boost Financial Institution, Industry Security. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Use Of AI In Financial Institution Industry To Improve Security Mockup PDF
Presenting Use Of AI In Financial Institution Industry To Improve Security Mockup PDF to dispense important information. This template comprises Four stages. It also presents valuable insights into the topics including Financial Institution, Industry Improve Security. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
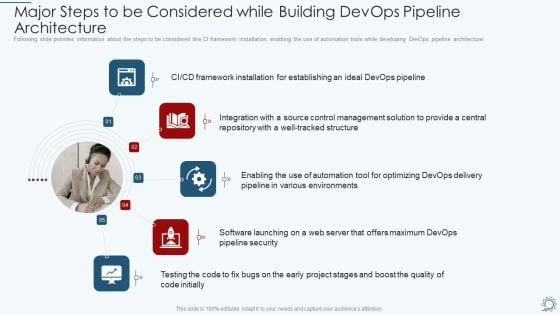
Development And Operations Pipeline IT Major Steps To Be Considered While Building Devops Pipeline Architecture Designs PDF
Following slide provides information about the steps to be considered like CI framework installation, enabling the use of automation tools while developing DevOps pipeline architecture. Presenting development and operations pipeline it major steps to be considered while building devops pipeline architecture designs pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like security, environments, management, integration, framework. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
Executing Security Management Program To Mitigate Threats And Safeguard Confidential Organizational Data Icons Slide Inspiration PDF
Introducing our well designed Executing security management program to mitigate threats and safeguard confidential organizational data icons slide inspiration pdf set of slides. The slide displays editable icons to enhance your visual presentation. The icons can be edited easily. So customize according to your business to achieve a creative edge. Download and share it with your audience.

Secured Money Finance PowerPoint Templates And PowerPoint Themes 1112
We present our Secured Money Finance PowerPoint Templates And PowerPoint Themes 1112.Use our Security PowerPoint Templates because,To strive to give true form to your great dream. Use our Success PowerPoint Templates because, Highlight your ideas broad- based on strong fundamentals and illustrate how they step by step acheive the set growth factor. Use our Signs PowerPoint Templates because, Develop your marketing strategy and communicate your ethusiasm and motivation to raise the bar. Use our Money PowerPoint Templates because, Anticipate the doubts and questions in the minds of your colleagues and enlighten them with your inspired strategy to garner desired success. Use our Business PowerPoint Templates because,Marketing Strategy Business Template:- Maximising sales of your product is the intended destination.Use these PowerPoint slides for presentations relating to Protection of money, security, success, money, signs, business. The prominent colors used in the PowerPoint template are Blue navy, Black, Yellow Make a great career call with our Secured Money Finance PowerPoint Templates And PowerPoint Themes 1112. Put your ideas across emphatically.
Risk Based Procedures To IT Security Risk Governance Structure Ppt PowerPoint Presentation Icon Gallery PDF
Mentioned slide illustrates risk governance framework of the company. It include information about different governing committees along with their deliverables. Deliver and pitch your topic in the best possible manner with this Risk Based Procedures To IT Security Risk Governance Structure Ppt PowerPoint Presentation Icon Gallery PDF. Use them to share invaluable insights on Risk Management, Board Directors, Strategy Risk and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
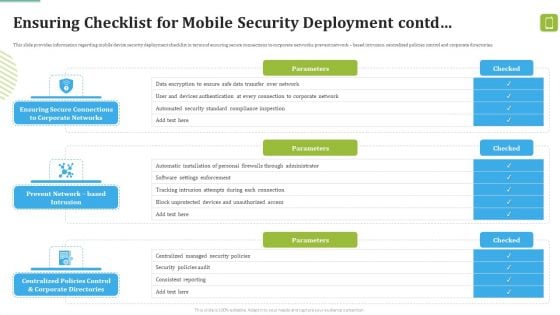
MDM Strategies At Office Ensuring Checklist For Mobile Security Deployment Contd Template PDF
This slide provides information regarding mobile device security deployment checklist in terms of device security, protection against malicious codes. Deliver and pitch your topic in the best possible manner with this MDM Strategies At Office Ensuring Checklist For Mobile Security Deployment Contd Template PDF. Use them to share invaluable insights on Against Malicious, Device Security, Automatic Configuration and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
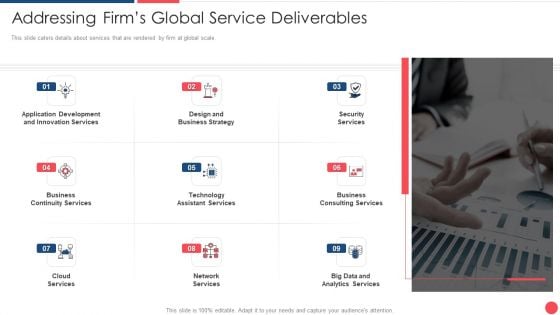
Services Marketing Sales Addressing Firms Global Service Deliverables Ppt Portfolio File Formats PDF
This slide caters details about services that are rendered by firm at global scale. This is a services marketing sales addressing firms global service deliverables ppt portfolio file formats pdf template with various stages. Focus and dispense information on nine stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like application development, innovation services, design and business strategy, security services . You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
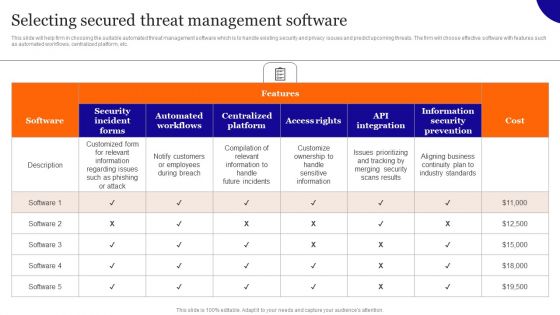
Selecting Secured Threat Management Software Introduction PDF
This slide will help firm in choosing the suitable automated threat management software which is to handle existing security and privacy issues and predict upcoming threats. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Make sure to capture your audiences attention in your business displays with our gratis customizable Selecting Secured Threat Management Software Introduction PDF. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.
4 Phases Funnel Diagram For Security Metrics Strategy Ppt PowerPoint Presentation Gallery Graphics Tutorials PDF
Presenting 4 phases funnel diagram for security metrics strategy ppt powerpoint presentation gallery graphics tutorials pdf to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including 4 phases funnel diagram for security metrics strategy. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Cyber Security Strategy Roadmap Icon With Lock Symbol Ppt PowerPoint Presentation File Gridlines PDF
Presenting Cyber Security Strategy Roadmap Icon With Lock Symbol Ppt PowerPoint Presentation File Gridlines PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Cyber Security Strategy, Roadmap Icon, Lock Symbol. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
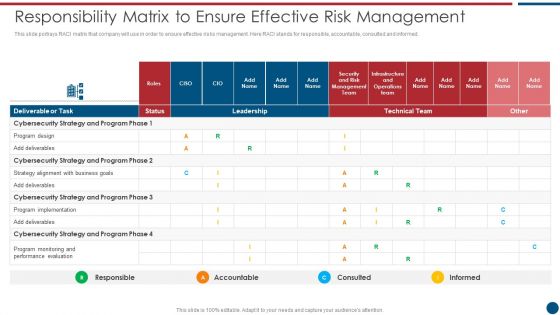
Risk Based Procedures To IT Security Responsibility Matrix To Ensure Effective Risk Management Slides PDF
This slide portrays RACI matrix that company will use in order to ensure effective risks management. Here RACI stands for responsible, accountable, consulted and informed. Deliver an awe inspiring pitch with this creative Risk Based Procedures To IT Security Responsibility Matrix To Ensure Effective Risk Management Slides PDF bundle. Topics like Technical Team, Cybersecurity Strategy, Program Implementation can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
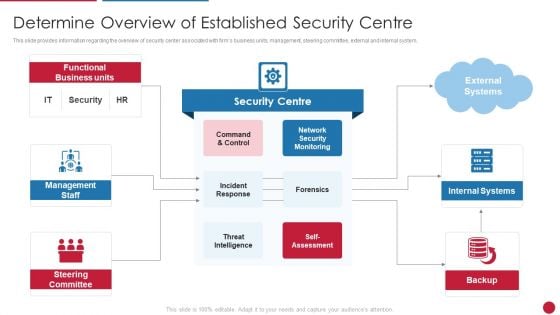
Facilitating IT Intelligence Architecture Determine Overview Of Established Security Centre Introduction PDF
This slide provides information regarding the overview of security center associated with firms business units, management, steering committee, external and internal system. This is a Facilitating IT Intelligence Architecture Determine Overview Of Established Security Centre Introduction PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Network Security Monitoring, Internal Systems, Steering Committee You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
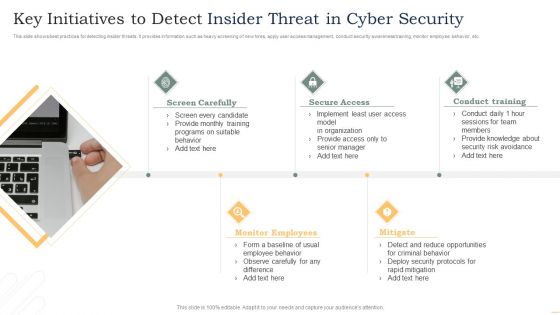
Key Initiatives To Detect Insider Threat In Cyber Security Designs PDF
This slide shows best practices for detecting insider threats. It provides information such as heavy screening of new hires, apply user access management, conduct security awareness training, monitor employee behavior, etc. Presenting Key Initiatives To Detect Insider Threat In Cyber Security Designs PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Screen Carefully, Secure Access, Conduct Training. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
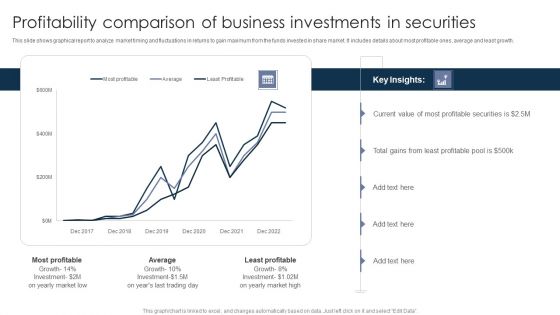
Profitability Comparison Of Business Investments In Securities Ppt PowerPoint Presentation Outline Deck PDF
This slide shows graphical report to analyze market timing and fluctuations in returns to gain maximum from the funds invested in share market. It includes details about most profitable ones, average and least growth. Pitch your topic with ease and precision using this Profitability Comparison Of Business Investments In Securities Ppt PowerPoint Presentation Outline Deck PDF. This layout presents information on Most Profitable, Least Profitable, Least Profitable. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
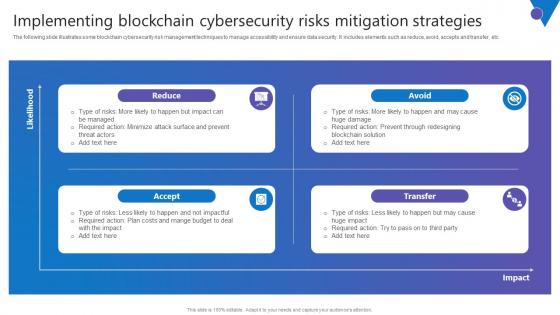
Implementing Blockchain Comprehensive Guide To Blockchain Digital Security Ideas Pdf
The following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Implementing Blockchain Comprehensive Guide To Blockchain Digital Security Ideas Pdf can be your best option for delivering a presentation. Represent everything in detail using Implementing Blockchain Comprehensive Guide To Blockchain Digital Security Ideas Pdf and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results. The following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc.
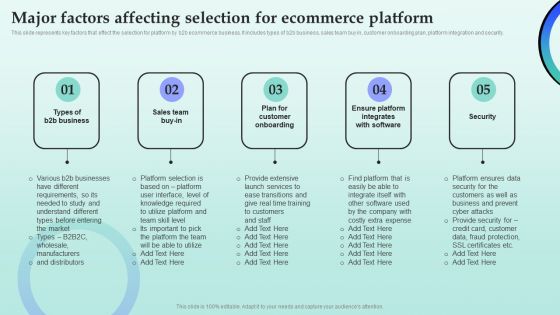
Strategies For Successful Customer Base Development In B2b M Commerce Major Factors Affecting Selection For Ecommerce Microsoft PDF
This slide represents key factors that effect the selection for platform by b2b ecommerce business. It includes types of b2b business, sales team buy in, customer onboarding plan, platform integration and security. Find highly impressive Strategies For Successful Customer Base Development In B2b M Commerce Major Factors Affecting Selection For Ecommerce Microsoft PDF on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Strategies For Successful Customer Base Development In B2b M Commerce Major Factors Affecting Selection For Ecommerce Microsoft PDF for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now.

Security Process Success PowerPoint Templates And PowerPoint Themes 0512
Security Process Success PowerPoint Templates And PowerPoint Themes PPT designs-Microsoft Powerpoint Templates and Background with security process Encourage your community to take action. Get them to back the cause you champion.

Reverse Proxy Web Server Secure Client Connection To Proxy Server Themes PDF
This slide represents the secure client connection to the proxy server and is effective for a little or no risk for data transmission between networks. Presenting this PowerPoint presentation, titled Reverse Proxy Web Server Secure Client Connection To Proxy Server Themes PDF, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Reverse Proxy Web Server Secure Client Connection To Proxy Server Themes PDF. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Reverse Proxy Web Server Secure Client Connection To Proxy Server Themes PDF that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.

Cyber Security Market Forecast Ppt PowerPoint Presentation Infographics Example File Cpb
Presenting this set of slides with name cyber security market forecast ppt powerpoint presentation infographics example file cpb. This is an editable Powerpoint five stages graphic that deals with topics like cyber security market forecast to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Cyber Security Operations Management Ppt PowerPoint Presentation Show Format Cpb Pdf
Presenting this set of slides with name cyber security operations management ppt powerpoint presentation show format cpb pdf. This is an editable Powerpoint four stages graphic that deals with topics like cyber security operations management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Laptop Protection With Secured Antivirus Vector Icon Ppt PowerPoint Presentation Icon Graphics PDF
Persuade your audience using this laptop protection with secured antivirus vector icon ppt powerpoint presentation icon graphics pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including laptop protection with secured antivirus vector icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Hacker Icon For Online Security Ppt PowerPoint Presentation Styles Example PDF
Persuade your audience using this hacker icon for online security ppt powerpoint presentation styles example pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including hacker icon for online security. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Corporate International Security Guidelines Vector Icon Ppt PowerPoint Presentation Model Example Introduction PDF
Persuade your audience using this corporate international security guidelines vector icon ppt powerpoint presentation model example introduction pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including corporate international security guidelines vector icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Software Professional Working On Website Global Security Icon Ppt PowerPoint Presentation Infographic Template Images PDF
Persuade your audience using this software professional working on website global security icon ppt powerpoint presentation infographic template images pdf. This PPT design covers one stages, thus making it a great tool to use. It also caters to a variety of topics including software professional working on website global security icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Cloud Data Security Management Vector Icon Ppt PowerPoint Presentation Gallery Vector PDF
Persuade your audience using this cloud data security management vector icon ppt powerpoint presentation gallery vector pdf. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including cloud data security management vector icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Vector Showing Security Of Private Cloud Icon Ppt PowerPoint Presentation File Graphics PDF
Persuade your audience using this vector showing security of private cloud icon ppt powerpoint presentation file graphics pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including vector showing security of private cloud icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Smart Phone Device With Security Lock Placed On Table Ppt Professional Inspiration PDF
Persuade your audience using this smart phone device with security lock placed on table ppt professional inspiration pdf. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including smart phone device with security lock placed on table. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Smart Phone With Wireless Network Security Alarm Icon Ppt Pictures Graphics Tutorials PDF
Persuade your audience using this smart phone with wireless network security alarm icon ppt pictures graphics tutorials pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including smart phone with wireless network security alarm icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Online Network Security Against Hackers And Internet Threats Ppt PowerPoint Presentation File Show PDF
Persuade your audience using this online network security against hackers and internet threats ppt powerpoint presentation file show pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including online network security against hackers and internet threats. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Security Software Deployed To Countermeasure Internet Threats Ppt PowerPoint Presentation Gallery Icon PDF
Persuade your audience using this security software deployed to countermeasure internet threats ppt powerpoint presentation gallery icon pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including security software deployed to countermeasure internet threats. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
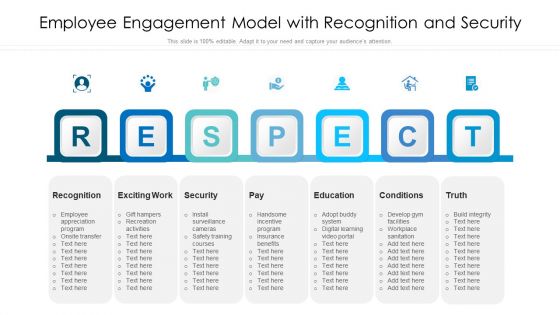
Employee Engagement Model With Recognition And Security Ppt File Templates PDF
Persuade your audience using this employee engagement model with recognition and security ppt file templates pdf. This PPT design covers seven stages, thus making it a great tool to use. It also caters to a variety of topics including recognition, exciting work, security, education, conditions. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Handling Cyber Threats Digital Era Security Lifecycle Ppt Summary Brochure PDF
This is a handling cyber threats digital era security lifecycle ppt summary brochure pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like security lifecycle. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Saas Cloud Security Best Practices Icon Ppt PowerPoint Presentation File Guidelines PDF
Persuade your audience using this Saas Cloud Security Best Practices Icon Ppt PowerPoint Presentation File Guidelines PDF. This PPT design covers one stages, thus making it a great tool to use. It also caters to a variety of topics including Saas Cloud Security, Best Practices, Icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Digitization Of Security Systems Icon With Gear Ppt Portfolio Tips PDF
Persuade your audience using this Digitization Of Security Systems Icon With Gear Ppt Portfolio Tips PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Digitization, Security Systems, Icon With Gear. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Security For Cloud Based Systems Management Icon For IT Project Rules PDF
Persuade your audience using this Security For Cloud Based Systems Management Icon For IT Project Rules PDF. This PPT design covers Three stages, thus making it a great tool to use. It also caters to a variety of topics including Security For Cloud, Based Systems Management, IT Project. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Cyber Security Incident Alert Icon With Desktop Screen Ppt Gallery Layouts PDF
Persuade your audience using this Cyber Security Incident Alert Icon With Desktop Screen Ppt Gallery Layouts PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Cyber Security Incident, Alert Icon, Desktop Screen. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Cyber Security Incident Icon With Man In Black Hood Ppt Inspiration Images PDF
Persuade your audience using this Cyber Security Incident Icon With Man In Black Hood Ppt Inspiration Images PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Cyber Security Incident, Icon With Man, Black Hood. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Overview Of Key Insights On Cyber Security Trends Icon Microsoft PDF
Persuade your audience using this Overview Of Key Insights On Cyber Security Trends Icon Microsoft PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Overview Of Key Insights, Cyber Security Trends Icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
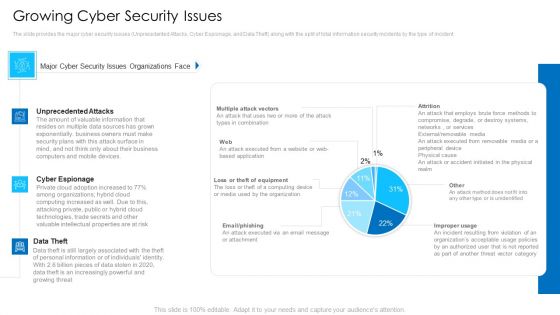
Growing Cyber Security Issues Mockup PDF
Deliver an awe inspiring pitch with this creative growing cyber security issues mockup pdf bundle. Topics like unprecedented attacks, cyber espionage, data theft can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
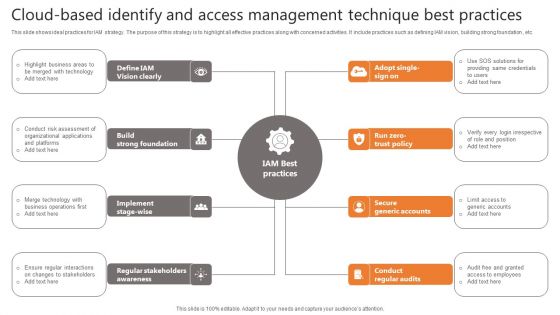
Cloud-Based Identify And Access Management Technique Best Practices Slides PDF
This slide shows ideal practices for IAM strategy. The purpose of this strategy is to highlight all effective practices along with concerned activities. It include practices such as defining IAM vision, building strong foundation , etc. Presenting Cloud-Based Identify And Access Management Technique Best Practices Slides PDF to dispense important information. This template comprises eight stages. It also presents valuable insights into the topics including Vision Clearly, Strong Foundation, Secure Generic Accounts. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Cyber Exploitation IT Roadmap To Implement New Security Strategies Information PDF
This slide represents the roadmap to implement new security strategies, including hiring new professionals, new software or hardware installation, employee awareness sessions, etc. This is a cyber exploitation it roadmap to implement new security strategies information pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like tracking and monitoring, security consultants, cyber security awareness. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
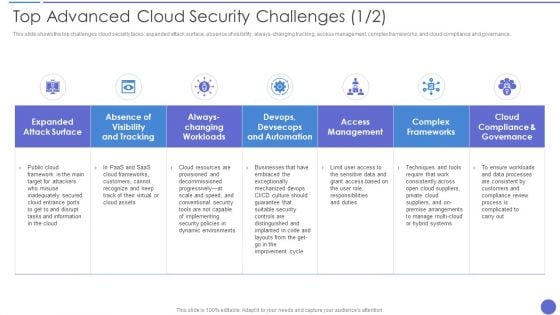
Top Advanced Cloud Security Challenges Brochure PDF
This slide shows the top challenges cloud security faces expanded attack surface, absence of visibility, always changing tracking, access management, complex frameworks, and cloud compliance and governance. Deliver an awe inspiring pitch with this creative Top Advanced Cloud Security Challenges Brochure PDF bundle. Topics like Complex Frameworks, Access Management, Dynamic Environments can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
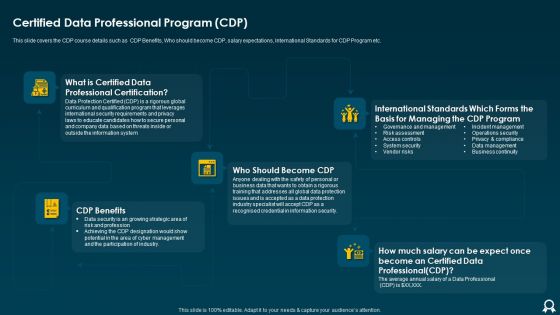
IT Data Services Certification Programs Certified Data Professional Program CDP Structure PDF
This slide covers the CDP course details such as CDP Benefits, Who should become CDP, salary expectations, International Standards for CDP Program etc. This is a IT Data Services Certification Programs Certified Data Professional Program CDP Structure PDF template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like International Standards, Information Security, Data Protection. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Executing Security Management Program To Mitigate Threats And Safeguard Confidential Organizational Data Roadmap Professional PDF
Presenting Executing security management program to mitigate threats and safeguard confidential organizational data roadmap professional pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like roadmap. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
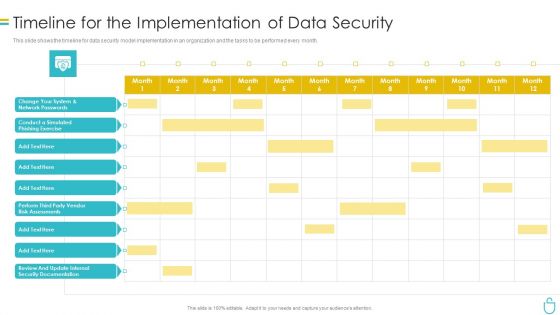
Information Security Timeline For The Implementation Of Data Security Ppt Gallery Topics PDF
This slide shows the timeline for data security model implementation in an organization and the tasks to be performed every month. Deliver and pitch your topic in the best possible manner with this information security timeline for the implementation of data security ppt gallery topics pdf. Use them to share invaluable insights on timeline for the implementation of data security and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
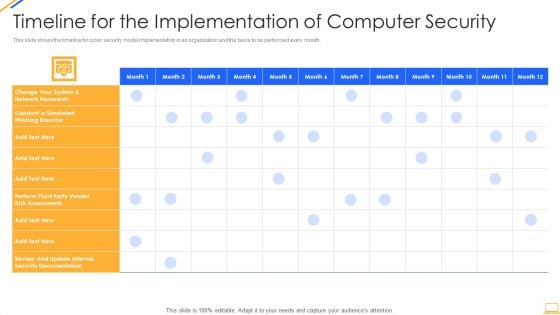
Desktop Security Management Timeline For The Implementation Of Computer Security Sample PDF
This slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Deliver and pitch your topic in the best possible manner with this desktop security management timeline for the implementation of computer security sample pdf. Use them to share invaluable insights on security documentation, system and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

IT Security Timeline For The Implementation Of Information Technology Security Structure PDF
This slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Deliver an awe inspiring pitch with this creative it security timeline for the implementation of information technology security structure pdf bundle. Topics like timeline for the implementation of information technology security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
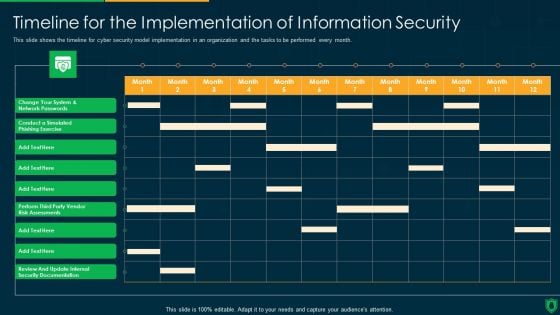
Info Security Timeline For The Implementation Of Information Security Ppt PowerPoint Presentation Diagram Templates PDF
This slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Deliver an awe inspiring pitch with this creative info security timeline for the implementation of information security ppt powerpoint presentation diagram templates pdf bundle. Topics like perform third party, vendor risk assessments, review and update, internal security documentation can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Retail Industry Outlook Retail Price Management Goals Brochure PDF
Deliver and pitch your topic in the best possible manner with this retail industry outlook retail price management goals brochure pdf. Use them to share invaluable insights on enterprise wide price transparency, price monitoring and analysis, system wide security, real time performance metrics and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
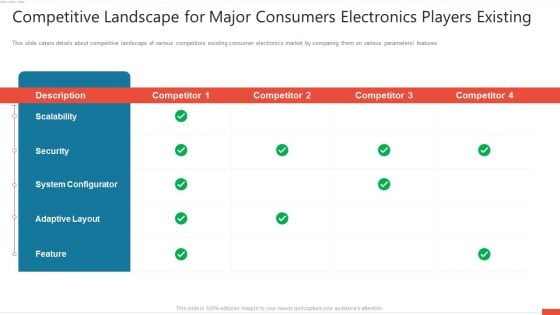
Competitive Landscape For Major Consumers Electronics Players Existing Professional PDF
Deliver an awe-inspiring pitch with this creative competitive landscape for major consumers electronics players existing professional pdf bundle. Topics like scalability, security, system configurator, description, adaptive layout can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Home Appliances Producer Seed Competitive Landscape For Major Consumers Electronics Players Existing Icons PDF
Deliver an awe inspiring pitch with this creative home appliances producer seed competitive landscape for major consumers electronics players existing icons pdf bundle. Topics like scalability, security, system configurator can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
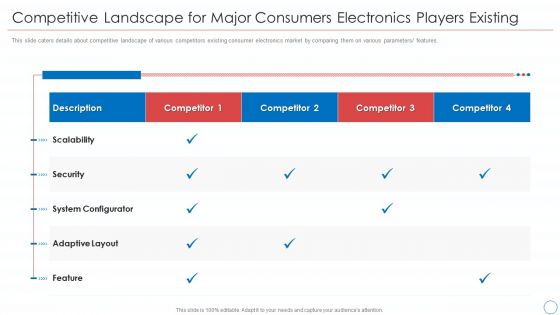
Competitive Landscape For Major Consumers Electronics Players Existing Background PDF
Deliver an awe-inspiring pitch with this creative competitive landscape for major consumers electronics players existing background pdf bundle. Topics like scalability, security, system configurator, adaptive layout, feature can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
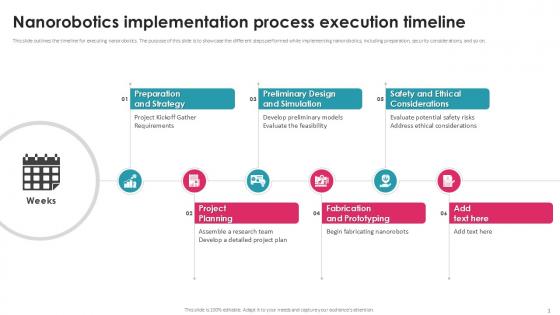
Nanorobotics Implementation Process Execution Timeline PPT Example
This slide outlines the timeline for executing nanorobotics. The purpose of this slide is to showcase the different steps performed while implementing nanorobotics, including preparation, security considerations, and so on. Find a pre-designed and impeccable Nanorobotics Implementation Process Execution Timeline PPT Example. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation. This slide outlines the timeline for executing nanorobotics. The purpose of this slide is to showcase the different steps performed while implementing nanorobotics, including preparation, security considerations, and so on.

Optimizing Digital Marketing Strategy Create Effective And Privacy Safe Marketing Actions Diagrams PDF
This template covers techniques companies can follow to ensure secure and effective marketing efforts. It includes approaches such as making marketing actions memorable, meaningful, and manageable. Slidegeeks is here to make your presentations a breeze with Optimizing Digital Marketing Strategy Create Effective And Privacy Safe Marketing Actions Diagrams PDF With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, youre sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether youre giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.


 Continue with Email
Continue with Email

 Home
Home


































