Access management PowerPoint Presentation Templates and Google Slides
-

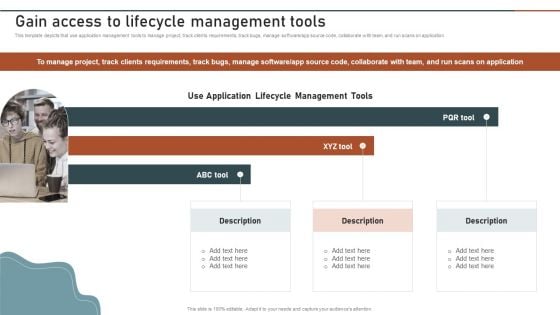
Gain Access To Lifecycle Management Tools Business Application Development Playbook Microsoft PDF
This template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software app source code, collaborate with team, and run scans on application.Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Gain Access To Lifecycle Management Tools Business Application Development Playbook Microsoft PDF template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Gain Access To Lifecycle Management Tools Business Application Development Playbook Microsoft PDF that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers.
-
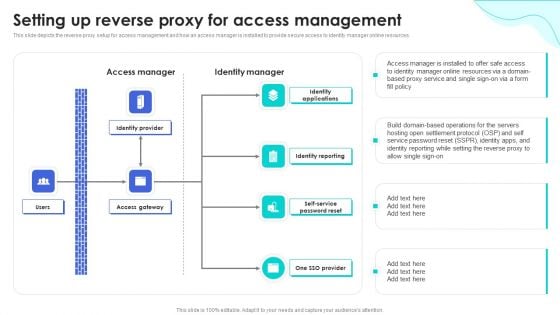
Reverse Proxy Web Server Setting Up Reverse Proxy For Access Management Download PDF
This slide depicts the reverse proxy setup for access management and how an access manager is installed to provide secure access to identity manager online resources. Create an editable Reverse Proxy Web Server Setting Up Reverse Proxy For Access Management Download PDF that communicates your idea and engages your audience. Whether youre presenting a business or an educational presentation, pre-designed presentation templates help save time. Reverse Proxy Web Server Setting Up Reverse Proxy For Access Management Download PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
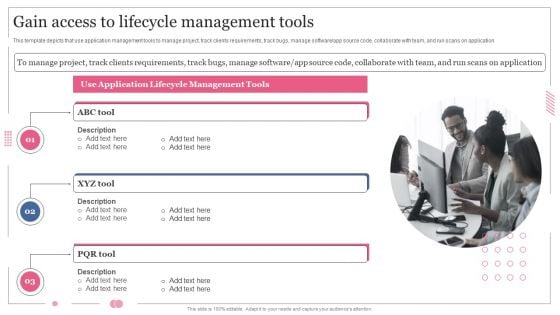
Enterprise Software Application Gain Access To Lifecycle Management Tools Infographics PDF
This template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software or app source code, collaborate with team, and run scans on application. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Enterprise Software Application Gain Access To Lifecycle Management Tools Infographics PDF can be your best option for delivering a presentation. Represent everything in detail using Enterprise Software Application Gain Access To Lifecycle Management Tools Infographics PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.
-
Software Designing And Development Gain Access To Lifecycle Management Tools Pictures PDF
Slidegeeks is here to make your presentations a breeze with Software Designing And Development Gain Access To Lifecycle Management Tools Pictures PDF With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.
-
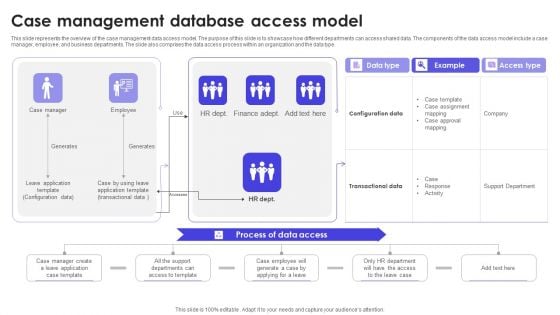
Case Management Database Access Model Download PDF
This slide represents the overview of the case management data access model. The purpose of this slide is to showcase how different departments can access shared data. The components of the data access model include a case manager, employee, and business departments. The slide also comprises the data access process within an organization and the data type. Showcasing this set of slides titled Case Management Database Access Model Download PDF. The topics addressed in these templates are Data Access, Example, Data Type. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
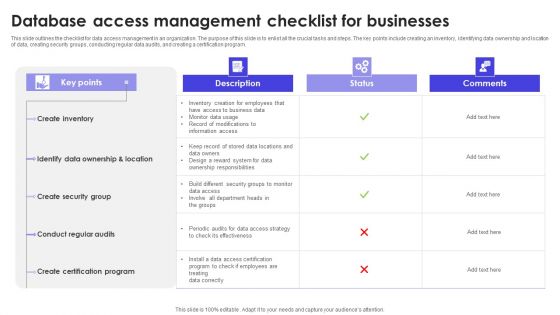
Database Access Management Checklist For Businesses Formats PDF
This slide outlines the checklist for data access management in an organization. The purpose of this slide is to enlist all the crucial tasks and steps. The key points include creating an inventory, identifying data ownership and location of data, creating security groups, conducting regular data audits, and creating a certification program. Showcasing this set of slides titled Database Access Management Checklist For Businesses Formats PDF. The topics addressed in these templates are Description, Status, Comments. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Icon For Server Database Access Management Background PDF
Persuade your audience using this Icon For Server Database Access Management Background PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Server Database, Access, Management. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
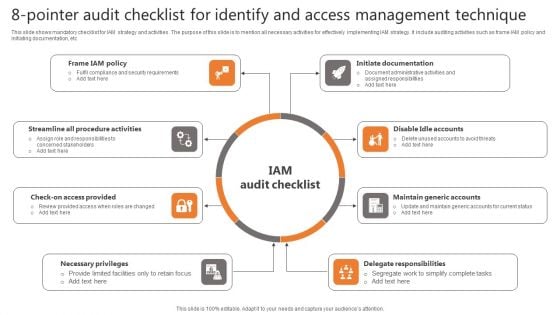
8-Pointer Audit Checklist For Identify And Access Management Technique Background PDF
This slide shows mandatory checklist for IAM strategy and activities. The purpose of this slide is to mention all necessary activities for effectively implementing IAM strategy. It include auditing activities such as frame IAM policy and initiating documentation, etc Presenting 8-Pointer Audit Checklist For Identify And Access Management Technique Background PDF to dispense important information. This template comprises eight stages. It also presents valuable insights into the topics including Procedure Activities, Access Provided, Necessary Privileges. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
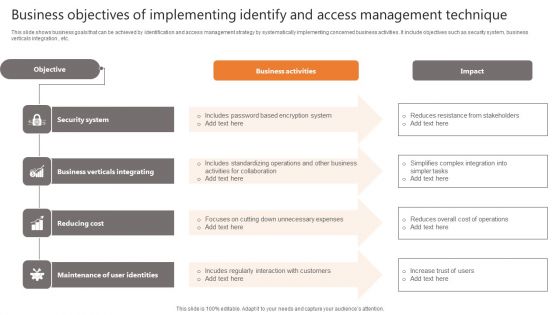
Business Objectives Of Implementing Identify And Access Management Technique Clipart PDF
This slide shows business goals that can be achieved by identification and access management strategy by systematically implementing concerned business activities. It include objectives such as security system, business verticals integration , etc. Showcasing this set of slides titled Business Objectives Of Implementing Identify And Access Management Technique Clipart PDF. The topics addressed in these templates are Business Activities, Impact, Objective. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-

Business Reasons For Executing Identify And Access Management Technique Mockup PDF
This slide shows major reasons to execute IAM strategy in organization to ease complexity of management and reducing IT costs. It include reasons such as improved security system, simplifies information sharing and usability sue , etc. Persuade your audience using this Business Reasons For Executing Identify And Access Management Technique Mockup PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Security System, Information Sharing, Usability Ease. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
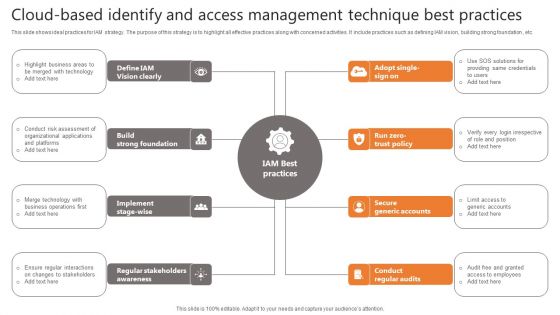
Cloud-Based Identify And Access Management Technique Best Practices Slides PDF
This slide shows ideal practices for IAM strategy. The purpose of this strategy is to highlight all effective practices along with concerned activities. It include practices such as defining IAM vision, building strong foundation , etc. Presenting Cloud-Based Identify And Access Management Technique Best Practices Slides PDF to dispense important information. This template comprises eight stages. It also presents valuable insights into the topics including Vision Clearly, Strong Foundation, Secure Generic Accounts. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
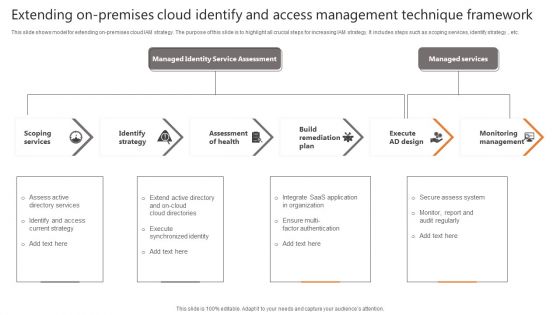
Extending On-Premises Cloud Identify And Access Management Technique Framework Formats PDF
This slide shows model for extending on-premises cloud IAM strategy. The purpose of this slide is to highlight all crucial steps for increasing IAM strategy. It includes steps such as scoping services, identify strategy , etc. Persuade your audience using this Cloud-Based Identify And Access Management Technique Best Practices Slides PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Scoping Services, Identify Strategy, Assessment Of Health. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
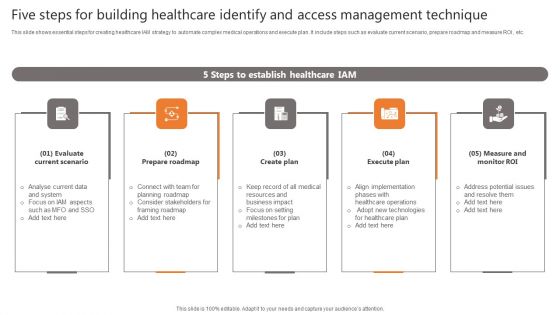
Five Steps For Building Healthcare Identify And Access Management Technique Portrait PDF
This slide shows essential steps for creating healthcare IAM strategy to automate complex medical operations and execute plan. It include steps such as evaluate current scenario, prepare roadmap and measure ROI , etc. Presenting Five Steps For Building Healthcare Identify And Access Management Technique Portrait PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Prepare Roadmap, Create Plan, Execute Plan. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
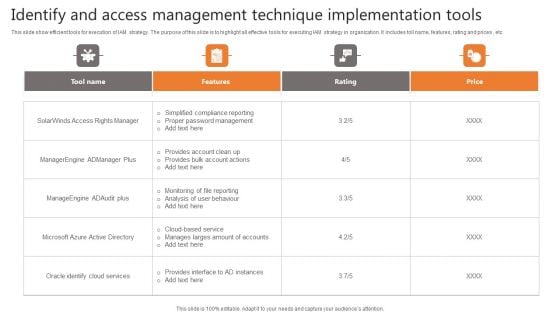
Identify And Access Management Technique Implementation Tools Demonstration PDF
This slide show efficient tools for execution of IAM strategy. The purpose of this slide is to highlight all effective tools for executing IAM strategy in organization. It includes toll name, features, rating and prices , etc. Pitch your topic with ease and precision using this Identify And Access Management Technique Implementation Tools Demonstration PDF. This layout presents information on Tool Name, Features, Rating. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
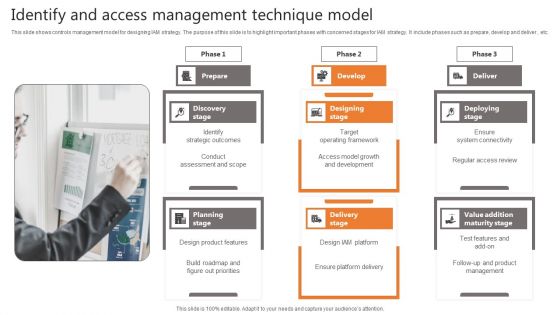
Identify And Access Management Technique Model Icons PDF
This slide shows controls management model for designing IAM strategy. The purpose of this slide is to highlight important phases with concerned stages for IAM strategy. It include phases such as prepare, develop and deliver , etc. Persuade your audience using this Identify And Access Management Technique Model Icons PDF. This PPT design covers six stages, thus making it a great tool to use. It also caters to a variety of topics including Prepare, Develop, Deliver. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
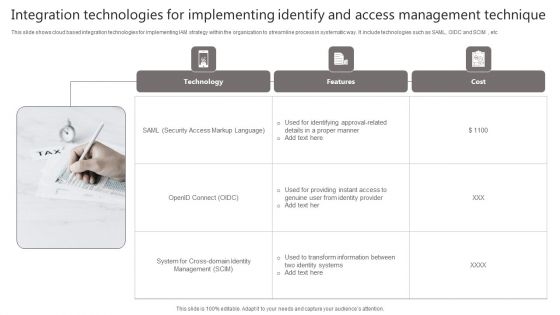
Integration Technologies For Implementing Identify And Access Management Technique Portrait PDF
This slide shows cloud based integration technologies for implementing IAM strategy within the organization to streamline process in systematic way. It include technologies such as SAML, OIDC and SCIM , etc Presenting Integration Technologies For Implementing Identify And Access Management Technique Portrait PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Technology, Features, Cost. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
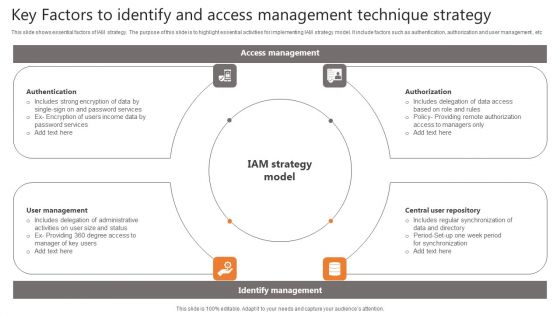
Key Factors To Identify And Access Management Technique Strategy Elements PDF
This slide shows essential factors of IAM strategy. The purpose of this slide is to highlight essential activities for implementing IAM strategy model. It include factors such as authentication, authorization and user management , etc Persuade your audience using this Key Factors To Identify And Access Management Technique Strategy Elements PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Authentication, Management, Repository. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
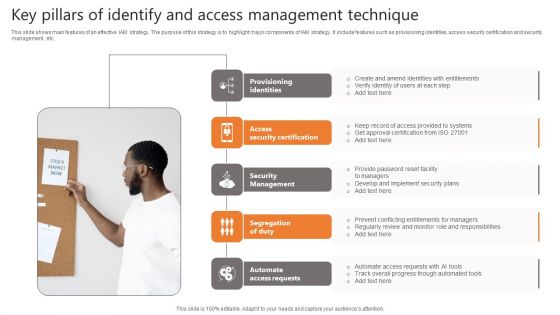
Key Pillars Of Identify And Access Management Technique Topics PDF
This slide shows main features of an effective IAM strategy. The purpose of this strategy is to highlight major components of IAM strategy. It include features such as provisioning identities, access security certification and security management , etc. Presenting Key Pillars Of Identify And Access Management Technique Topics PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Provisioning Identities, Security Certification, Security Management. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
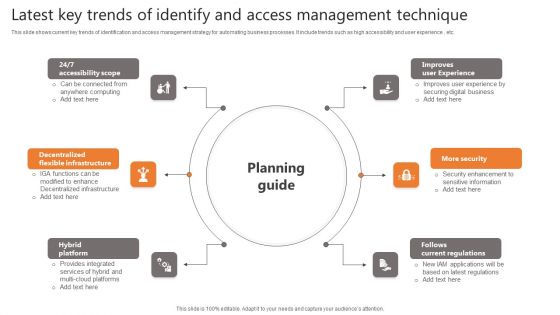
Latest Key Trends Of Identify And Access Management Technique Clipart PDF
This slide shows current key trends of identification and access management strategy for automating business processes. It include trends such as high accessibility and user experience , etc. Persuade your audience using this Latest Key Trends Of Identify And Access Management Technique Clipart PDF. This PPT design covers six stages, thus making it a great tool to use. It also caters to a variety of topics including Accessibility Scope, Flexible Infrastructure, Hybrid Platform. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
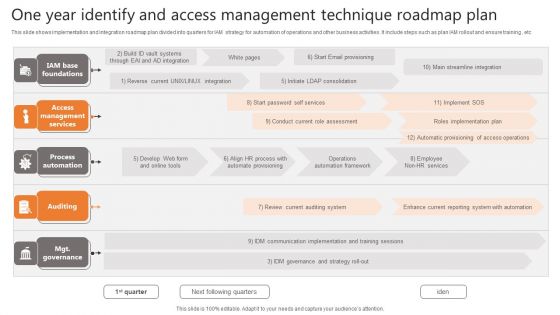
One Year Identify And Access Management Technique Roadmap Plan Icons PDF
This slide shows implementation and integration roadmap plan divided into quarters for IAM strategy for automation of operations and other business activities. It include steps such as plan IAM rollout and ensure training , etc Showcasing this set of slides titled One Year Identify And Access Management Technique Roadmap Plan Icons PDF. The topics addressed in these templates are Management Services, Process Automation, Auditing. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
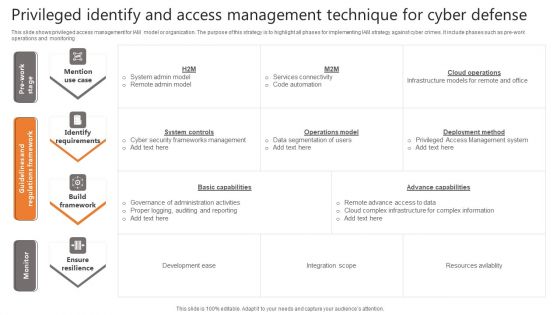
Privileged Identify And Access Management Technique For Cyber Defense Infographics PDF
This slide shows privileged access management for IAM model or organization. The purpose of this strategy is to highlight all phases for implementing IAM strategy against cyber crimes. It include phases such as pre work operations and monitoring Pitch your topic with ease and precision using this Privileged Identify And Access Management Technique For Cyber Defense Infographics PDF. This layout presents information on Identify Requirements, Build Framework, Ensure Resilience. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
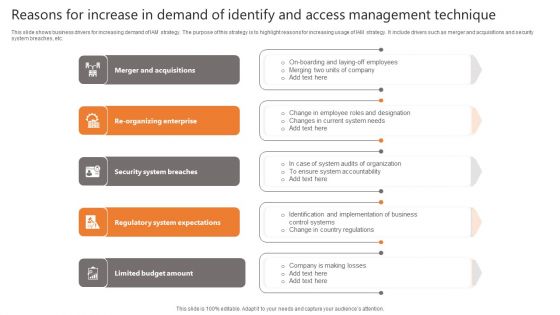
Reasons For Increase In Demand Of Identify And Access Management Technique Sample PDF
This slide shows business drivers for increasing demand of IAM strategy. The purpose of this strategy is to highlight reasons for increasing usage of IAM strategy. It include drivers such as merger and acquisitions and security system breaches, etc. Presenting Reasons For Increase In Demand Of Identify And Access Management Technique Sample PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Security System Breaches, Regulatory System Expectations, Limited Budget Amount. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-

Cloud Based Identify And Access Management Technique Introduction PDF
Presenting Cloud Based Identify And Access Management Technique Introduction PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Cloud Based Identify, Access Management, Technique. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-

Identify And Access Management Technique Icon Information PDF
Showcasing this set of slides titled Identify And Access Management Technique Icon Information PDF. The topics addressed in these templates are Identify, Access Management, Technique. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-

Identify And Access Management Technique Mechanism Icon Information PDF
Persuade your audience using this Identify And Access Management Technique Mechanism Icon Information PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Identify, Access Management, Technique Mechanism. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
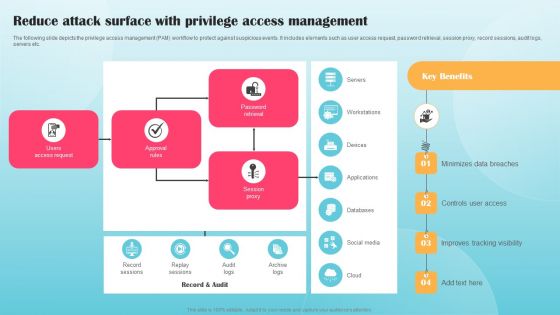
Reduce Attack Surface With Privilege Access Management Ppt PowerPoint Presentation Diagram Graph Charts PDF
The following slide depicts the privilege access management PAM workflow to protect against suspicious events. It includes elements such as user access request, password retrieval, session proxy, record sessions, audit logs, servers etc. Want to ace your presentation in front of a live audience Our Reduce Attack Surface With Privilege Access Management Ppt PowerPoint Presentation Diagram Graph Charts PDF can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy to edit and downloadable. Use these for both personal and commercial use.
-

Organizational Assets Security Management Strategy Determine User Access Controls Levels Diagrams PDF
This slide provides information about information user access controls levels for access critical assets and information associated to firm and levels of access for administrator, maintainer, guest or disabled. Get a simple yet stunning designed Organizational Assets Security Management Strategy Determine User Access Controls Levels Diagrams PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy to edit Organizational Assets Security Management Strategy Determine User Access Controls Levels Diagrams PDF can be your go to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.



