Accessibility PowerPoint Presentation Templates and Google Slides
-
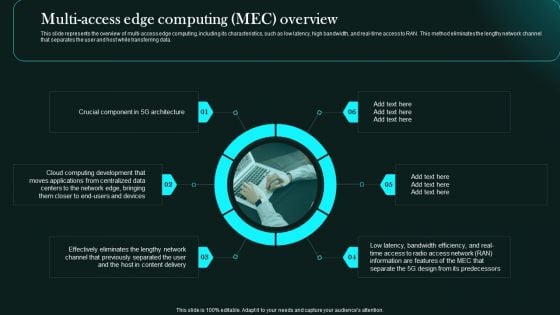
Multi Access Edge Computing Mec Overview 5G Network Functional Architecture Portrait PDF
This slide represents the overview of multi-access edge computing, including its characteristics, such as low latency, high bandwidth, and real-time access to RAN. This method eliminates the lengthy network channel that separates the user and host while transferring data.Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Multi Access Edge Computing Mec Overview 5G Network Functional Architecture Portrait PDF template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Multi Access Edge Computing Mec Overview 5G Network Functional Architecture Portrait PDF that effortlessly grabs the attention of your audience. Begin now and be certain to wow your customers.
-
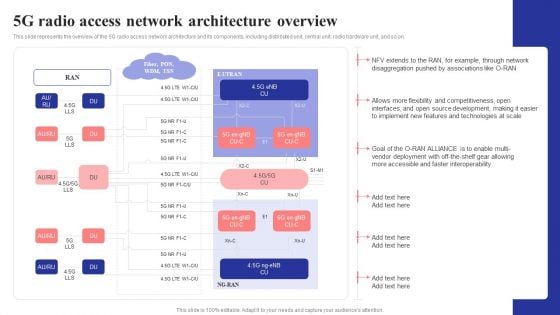
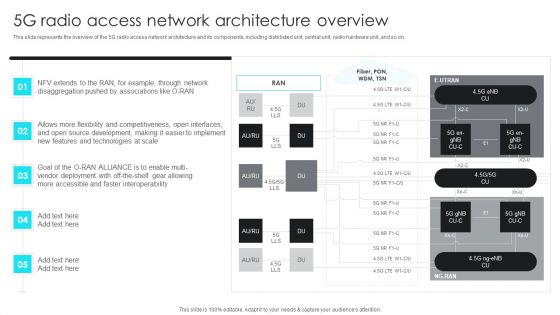
5G Radio Access Network Architecture Overview 5G Network Structure Structure PDF
This slide represents the overview of the 5G radio access network architecture and its components, including distributed unit, central unit, radio hardware unit, and so on.Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give 5G Radio Access Network Architecture Overview 5G Network Structure Structure PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable 5G Radio Access Network Architecture Overview 5G Network Structure Structure PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today
-
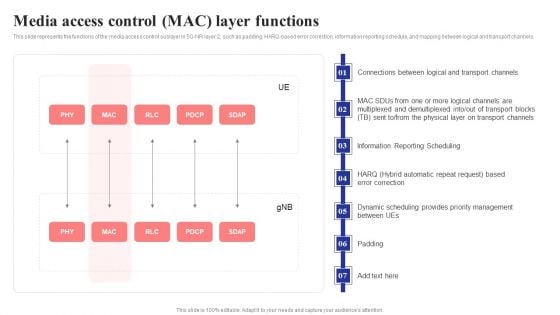
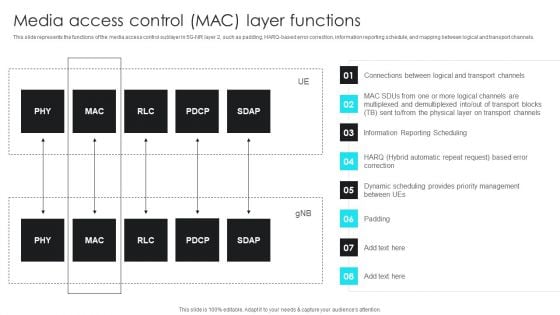
Media Access Control Mac Layer Functions 5G Network Structure Infographics PDF
This slide represents the functions of the media access control sublayer in 5G-NR layer 2, such as padding, HARQ-based error correction, information reporting schedule, and mapping between logical and transport channels.If you are looking for a format to display your unique thoughts, then the professionally designed Media Access Control Mac Layer Functions 5G Network Structure Infographics PDF is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Media Access Control Mac Layer Functions 5G Network Structure Infographics PDF and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.
-
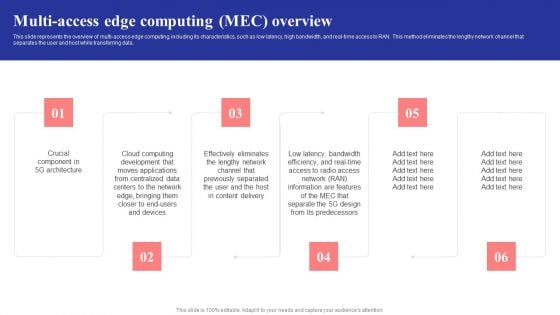
Multi Access Edge Computing Mec Overview 5G Network Structure Demonstration PDF
This slide represents the overview of multi-access edge computing, including its characteristics, such as low latency, high bandwidth, and real-time access to RAN. This method eliminates the lengthy network channel that separates the user and host while transferring data.Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Multi Access Edge Computing Mec Overview 5G Network Structure Demonstration PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.
-
5G Network Operations 5G Radio Access Network Architecture Overview Ideas PDF
This slide represents the 5G protocol layers mapped with Open Systems Interconnection Model. The 5G protocol layers comprise service applications, open transport protocol, upper network layer, lower network layer, and open wireless architecture. Do you have to make sure that everyone on your team knows about any specific topic. I yes, then you should give 5G Network Operations 5G Radio Access Network Architecture Overview Ideas PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable 5G Network Operations 5G Radio Access Network Architecture Overview Ideas PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.
-
5G Network Operations Media Access Control MAC Layer Functions Professional PDF
This slide represents the functions of the media access control sublayer in 5G-NR layer 2, such as padding, HARQ-based error correction, information reporting schedule, and mapping between logical and transport channels. If you are looking for a format to display your unique thoughts, then the professionally designed 5G Network Operations Media Access Control MAC Layer Functions Professional PDF. is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download 5G Network Operations Media Access Control MAC Layer Functions Professional PDF. and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.
-
5G Network Operations Multi Access Edge Computing MEC Overview Mockup PDF
Are you in need of a template that can accommodate all of your creative concepts. This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download5G Network Operations Multi Access Edge Computing MEC Overview Mockup PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.
-
Components Of Brand Portfolio Strategy For Better Access To New Markets And Consumers Formats PDF
This slide covers the fundamental principles of creating an effective brand communication strategy. It includes guidelines such as building and leveraging strong corporate bonds, defining strategic objectives for brands, employing simple and clear brand architecture, etc. This Components Of Brand Portfolio Strategy For Better Access To New Markets And Consumers Formats PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Components Of Brand Portfolio Strategy For Better Access To New Markets And Consumers Formats PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, dont wait, grab the presentation templates today
-
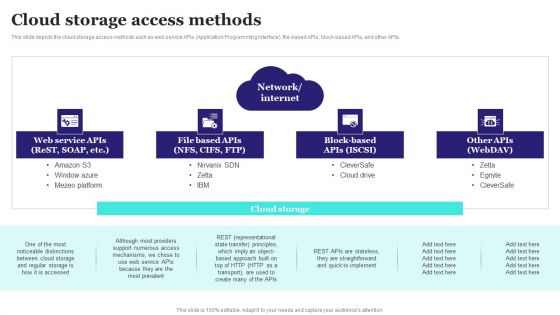
Cloud Storage Access Methods Ppt PowerPoint Presentation File Backgrounds PDF
This slide depicts the cloud storage access methods such as web service APIs Application Programming Interface, file based APIs, block based APIs, and other APIs. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Cloud Storage Access Methods Ppt PowerPoint Presentation File Backgrounds PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.
-
Food Product Package Designing Accessibility Guidelines Elements PDF
This slide showcases packaging design guidelines which should be considered while producing a product to promote consumer accessibility. It provides information regarding various guidelines such as clear visibility, warning instructions, proper sufficient area etc. Showcasing this set of slides titled Food Product Package Designing Accessibility Guidelines Elements PDF. The topics addressed in these templates are Guidelines, Applicable Components, Accessibility Guidelines. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Continuous Software Access Tracking In Devops Guidelines PDF
This slide illustrates application access information monitored with DevOps. It includes name, access level, license source, date added, last Showcasing this set of slides titled Continuous Software Access Tracking In Devops Guidelines PDF. The topics addressed in these templates are Access Level, License Source, Software Access Tracking. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Key Steps To Develop Brand Portfolio Components Of Brand Portfolio Strategy For Better Access Download PDF
This slide covers the fundamental principles of creating an effective brand communication strategy. It includes guidelines such as building and leveraging strong corporate bonds, defining strategic objectives for brands, employing simple and clear brand architecture, etc. This modern and well-arranged Key Steps To Develop Brand Portfolio Components Of Brand Portfolio Strategy For Better Access Download PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint, no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.
-
Role Of IT In Business Communication Models Of Access To Information And Communication Infographics PDF
This slide describes the models of access described by scholar Mark Warschauer as a framework for examining information and communication technology accessibility. The models include devices, conduits, and literacy. This Role Of IT In Business Communication Models Of Access To Information And Communication Infographics PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Role Of IT In Business Communication Models Of Access To Information And Communication Infographics PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, dont wait, grab the presentation templates today.
-
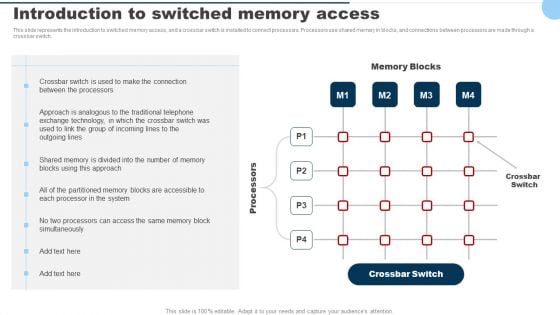
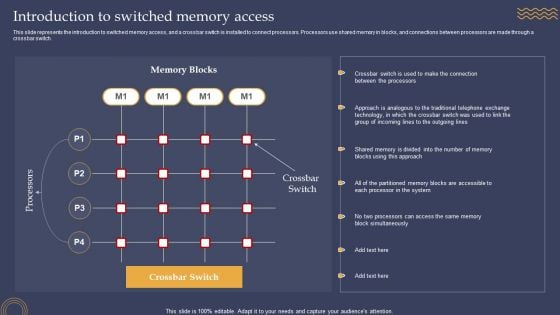
Introduction To Switched Memory Access Ppt PowerPoint Presentation Diagram Graph Charts PDF
This slide represents the introduction to switched memory access, and a crossbar switch is installed to connect processors. Processors use shared memory in blocks, and connections between processors are made through a crossbar switch. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Introduction To Switched Memory Access Ppt PowerPoint Presentation Diagram Graph Charts PDF to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.
-
Introduction To Switched Memory Access Ppt PowerPoint Presentation Diagram Lists PDF
This slide represents the introduction to switched memory access, and a crossbar switch is installed to connect processors. Processors use shared memory in blocks, and connections between processors are made through a crossbar switch. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Introduction To Switched Memory Access Ppt PowerPoint Presentation Diagram Lists PDF to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.
-
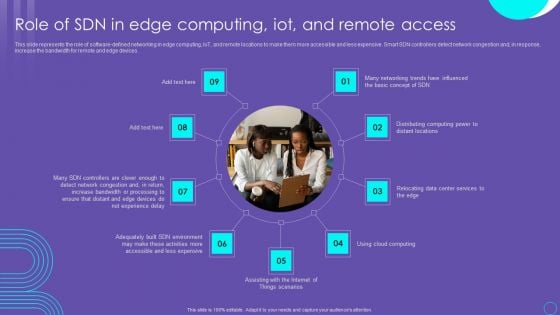
SDN Security Architecture Role Of SDN In Edge Computing Iot And Remote Access Information PDF
This slide represents the role of software defined networking in edge computing, IoT, and remote locations to make them more accessible and less expensive. Smart SDN controllers detect network congestion and, in response, increase the bandwidth for remote and edge devices. Boost your pitch with our creative SDN Security Architecture Role Of SDN In Edge Computing Iot And Remote Access Information PDF. Deliver an awe inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
-
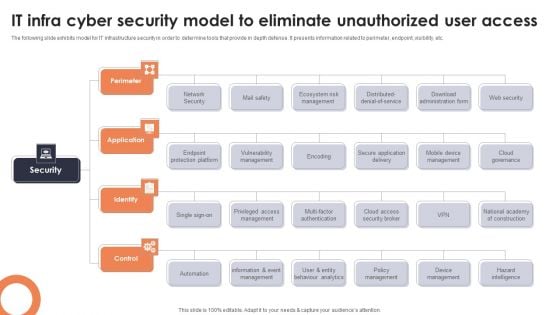
IT Infra Cyber Security Model To Eliminate Unauthorized User Access Topics PDF
The following slide exhibits model for IT infrastructure security in order to determine tools that provide in depth defense. It presents information related to perimeter, endpoint, visibility, etc. Presenting IT Infra Cyber Security Model To Eliminate Unauthorized User Access Topics PDF to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including Perimeter, Application, Identify. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
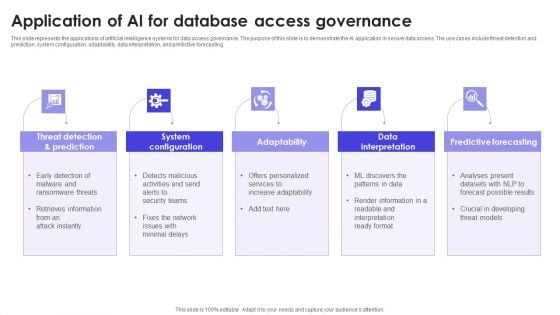
Application Of AI For Database Access Governance Summary PDF
This slide represents the applications of artificial intelligence systems for data access governance. The purpose of this slide is to demonstrate the AI application in secure data access. The use cases include threat detection and prediction, system configuration, adaptability, data interpretation, and predictive forecasting. Presenting Application Of AI For Database Access Governance Summary PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Prediction, System Configuration, Adaptability. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
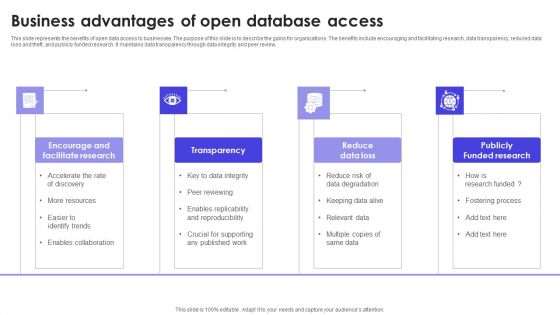
Business Advantages Of Open Database Access Structure PDF
This slide represents the benefits of open data access to businesses. The purpose of this slide is to describe the gains for organizations. The benefits include encouraging and facilitating research, data transparency, reduced data loss and theft, and publicly funded research. It maintains data transparency through data integrity and peer review. Persuade your audience using this Business Advantages Of Open Database Access Structure PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Research, Transparency, Reduce Data Loss . Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
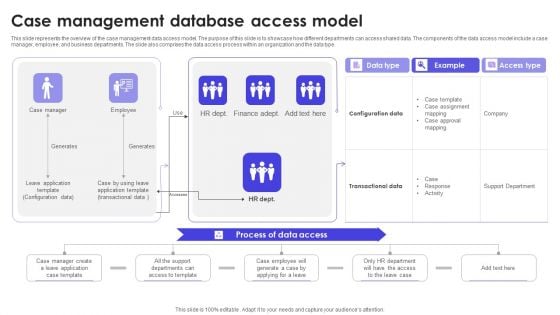
Case Management Database Access Model Download PDF
This slide represents the overview of the case management data access model. The purpose of this slide is to showcase how different departments can access shared data. The components of the data access model include a case manager, employee, and business departments. The slide also comprises the data access process within an organization and the data type. Showcasing this set of slides titled Case Management Database Access Model Download PDF. The topics addressed in these templates are Data Access, Example, Data Type. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
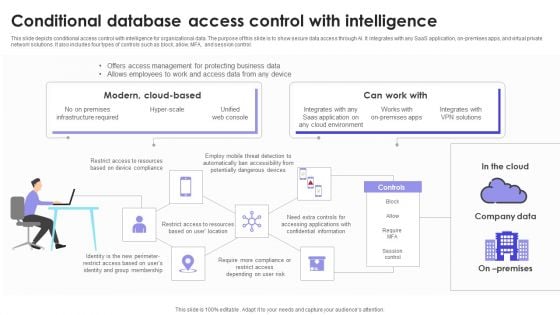
Conditional Database Access Control With Intelligence Download PDF
This slide depicts conditional access control with intelligence for organizational data. The purpose of this slide is to show secure data access through AI. It integrates with any SaaS application, on-premises apps, and virtual private network solutions. It also includes four types of controls such as block, allow, MFA, and session control. Pitch your topic with ease and precision using this Conditional Database Access Control With Intelligence Download PDF. This layout presents information on Company Data, Modern, Intelligence. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
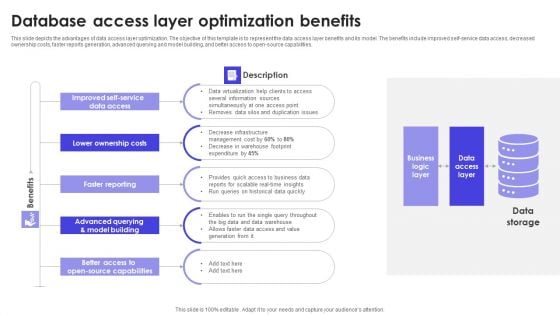
Database Access Layer Optimization Benefits Slides PDF
This slide depicts the advantages of data access layer optimization. The objective of this template is to represent the data access layer benefits and its model. The benefits include improved self-service data access, decreased ownership costs, faster reports generation, advanced querying and model building, and better access to open-source capabilities. Presenting Database Access Layer Optimization Benefits Slides PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Benefits, Lower Ownership Costs, Faster Reporting. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
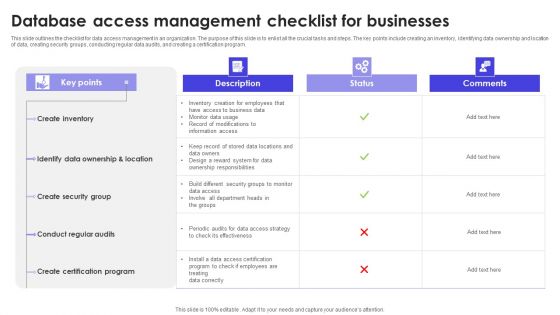
Database Access Management Checklist For Businesses Formats PDF
This slide outlines the checklist for data access management in an organization. The purpose of this slide is to enlist all the crucial tasks and steps. The key points include creating an inventory, identifying data ownership and location of data, creating security groups, conducting regular data audits, and creating a certification program. Showcasing this set of slides titled Database Access Management Checklist For Businesses Formats PDF. The topics addressed in these templates are Description, Status, Comments. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Database Access Security Measures For Businesses Portrait PDF
This slide represents the security measures for data access within an organization. This template aims to demonstrate secure data access techniques and their benefits. The components include workforce training, implementing a data-centric security plan, deploying a multi-factor authentication policy, etc. Pitch your topic with ease and precision using this Database Access Security Measures For Businesses Portrait PDF. This layout presents information on Methods, Benefits, Actions. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
File Directory Database Access Icon Icons PDF
Showcasing this set of slides titled File Directory Database Access Icon Icons PDF. The topics addressed in these templates are File Directory, Database, Access. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Icon For Server Database Access Management Background PDF
Persuade your audience using this Icon For Server Database Access Management Background PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Server Database, Access, Management. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
Secure Computer Database Access Icon Slides PDF
Presenting Secure Computer Database Access Icon Slides PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Secure, Computer, Database Access. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
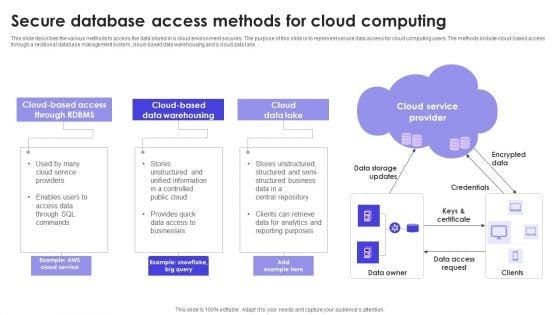
Secure Database Access Methods For Cloud Computing Formats PDF
This slide describes the various methods to access the data stored in a cloud environment securely. The purpose of this slide is to represent secure data access for cloud computing users. The methods include cloud-based access through a relational database management system, cloud-based data warehousing and a cloud data lake. Persuade your audience using this Secure Database Access Methods For Cloud Computing Formats PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Cloud Data Lake, Data Warehousing, Cloud Service Provider. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
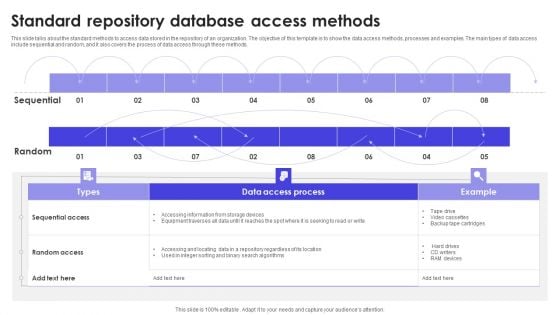
Standard Repository Database Access Methods Formats PDF
This slide talks about the standard methods to access data stored in the repository of an organization. The objective of this template is to show the data access methods, processes and examples. The main types of data access include sequential and random, and it also covers the process of data access through these methods. Pitch your topic with ease and precision using this Standard Repository Database Access Methods Formats PDF. This layout presents information on Sequential, Random, Methods. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
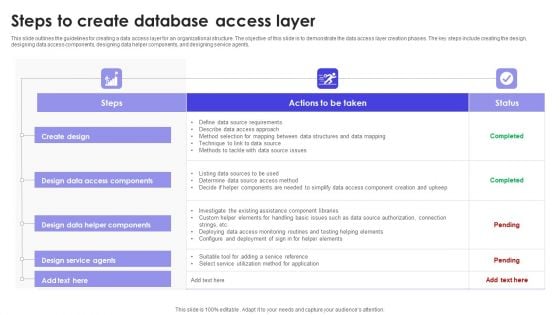
Steps To Create Database Access Layer Slides PDF
This slide outlines the guidelines for creating a data access layer for an organizational structure. The objective of this slide is to demonstrate the data access layer creation phases. The key steps include creating the design, designing data access components, designing data helper components, and designing service agents. Showcasing this set of slides titled Steps To Create Database Access Layer Slides PDF. The topics addressed in these templates are Data Access Components, Create Design, Steps. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
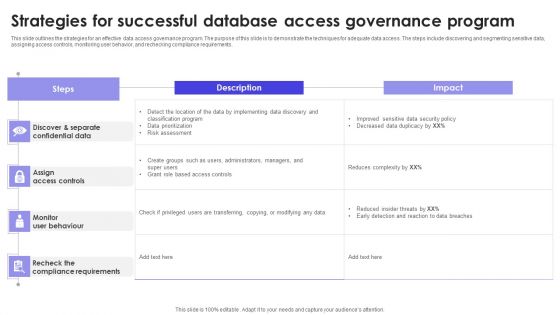
Strategies For Successful Database Access Governance Program Infographics PDF
This slide outlines the strategies for an effective data access governance program. The purpose of this slide is to demonstrate the techniques for adequate data access. The steps include discovering and segmenting sensitive data, assigning access controls, monitoring user behavior, and rechecking compliance requirements. Pitch your topic with ease and precision using this Strategies For Successful Database Access Governance Program Infographics PDF. This layout presents information on Steps, Description, Impact . It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
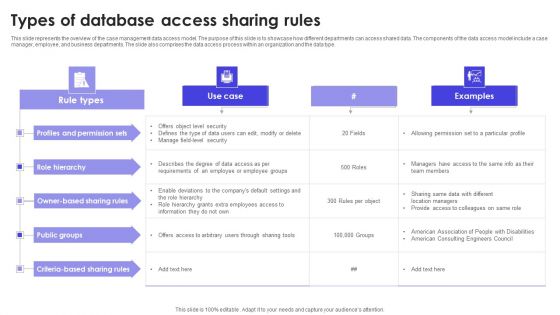
Types Of Database Access Sharing Rules Slides PDF
This slide represents the overview of the case management data access model. The purpose of this slide is to showcase how different departments can access shared data. The components of the data access model include a case manager, employee, and business departments. The slide also comprises the data access process within an organization and the data type. Showcasing this set of slides titled Types Of Database Access Sharing Rules Slides PDF. The topics addressed in these templates are Public Groups, Role Hierarchy, Permission Sets. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
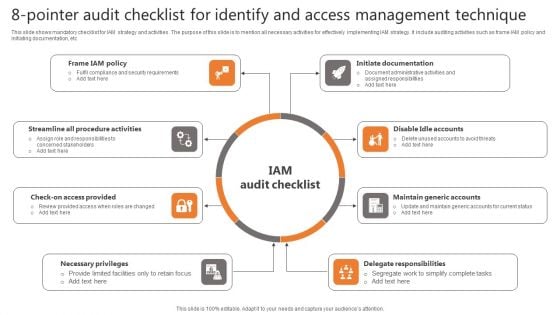
8-Pointer Audit Checklist For Identify And Access Management Technique Background PDF
This slide shows mandatory checklist for IAM strategy and activities. The purpose of this slide is to mention all necessary activities for effectively implementing IAM strategy. It include auditing activities such as frame IAM policy and initiating documentation, etc Presenting 8-Pointer Audit Checklist For Identify And Access Management Technique Background PDF to dispense important information. This template comprises eight stages. It also presents valuable insights into the topics including Procedure Activities, Access Provided, Necessary Privileges. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
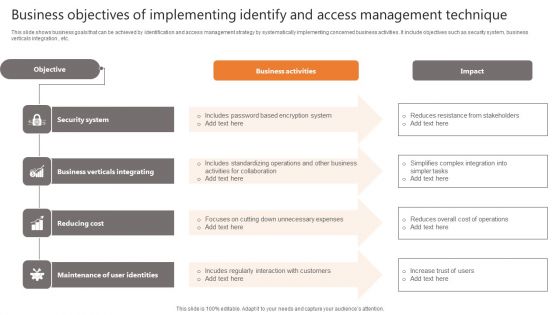
Business Objectives Of Implementing Identify And Access Management Technique Clipart PDF
This slide shows business goals that can be achieved by identification and access management strategy by systematically implementing concerned business activities. It include objectives such as security system, business verticals integration , etc. Showcasing this set of slides titled Business Objectives Of Implementing Identify And Access Management Technique Clipart PDF. The topics addressed in these templates are Business Activities, Impact, Objective. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Business Reasons For Executing Identify And Access Management Technique Mockup PDF
This slide shows major reasons to execute IAM strategy in organization to ease complexity of management and reducing IT costs. It include reasons such as improved security system, simplifies information sharing and usability sue , etc. Persuade your audience using this Business Reasons For Executing Identify And Access Management Technique Mockup PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Security System, Information Sharing, Usability Ease. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
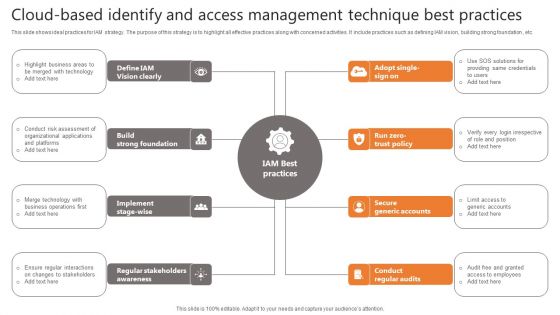
Cloud-Based Identify And Access Management Technique Best Practices Slides PDF
This slide shows ideal practices for IAM strategy. The purpose of this strategy is to highlight all effective practices along with concerned activities. It include practices such as defining IAM vision, building strong foundation , etc. Presenting Cloud-Based Identify And Access Management Technique Best Practices Slides PDF to dispense important information. This template comprises eight stages. It also presents valuable insights into the topics including Vision Clearly, Strong Foundation, Secure Generic Accounts. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
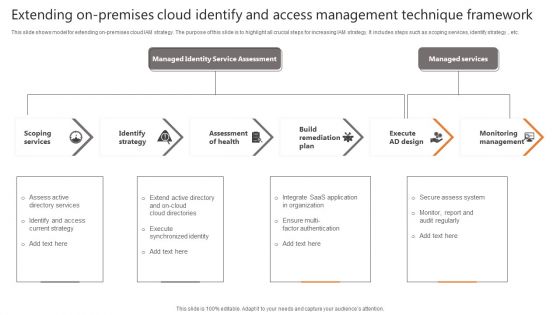
Extending On-Premises Cloud Identify And Access Management Technique Framework Formats PDF
This slide shows model for extending on-premises cloud IAM strategy. The purpose of this slide is to highlight all crucial steps for increasing IAM strategy. It includes steps such as scoping services, identify strategy , etc. Persuade your audience using this Cloud-Based Identify And Access Management Technique Best Practices Slides PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Scoping Services, Identify Strategy, Assessment Of Health. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
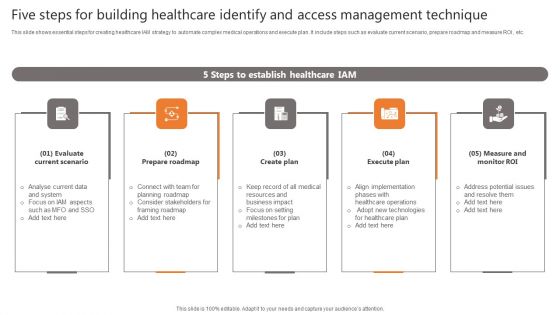
Five Steps For Building Healthcare Identify And Access Management Technique Portrait PDF
This slide shows essential steps for creating healthcare IAM strategy to automate complex medical operations and execute plan. It include steps such as evaluate current scenario, prepare roadmap and measure ROI , etc. Presenting Five Steps For Building Healthcare Identify And Access Management Technique Portrait PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Prepare Roadmap, Create Plan, Execute Plan. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
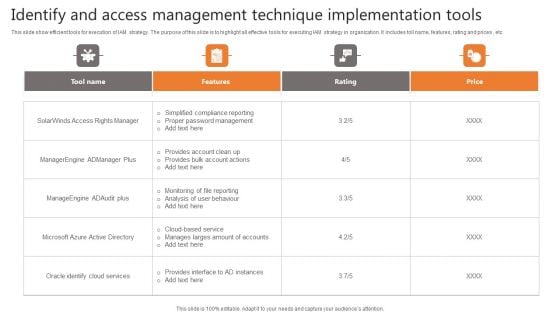
Identify And Access Management Technique Implementation Tools Demonstration PDF
This slide show efficient tools for execution of IAM strategy. The purpose of this slide is to highlight all effective tools for executing IAM strategy in organization. It includes toll name, features, rating and prices , etc. Pitch your topic with ease and precision using this Identify And Access Management Technique Implementation Tools Demonstration PDF. This layout presents information on Tool Name, Features, Rating. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Identify And Access Management Technique Model Icons PDF
This slide shows controls management model for designing IAM strategy. The purpose of this slide is to highlight important phases with concerned stages for IAM strategy. It include phases such as prepare, develop and deliver , etc. Persuade your audience using this Identify And Access Management Technique Model Icons PDF. This PPT design covers six stages, thus making it a great tool to use. It also caters to a variety of topics including Prepare, Develop, Deliver. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
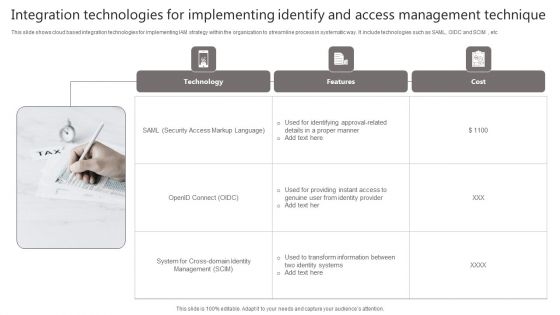
Integration Technologies For Implementing Identify And Access Management Technique Portrait PDF
This slide shows cloud based integration technologies for implementing IAM strategy within the organization to streamline process in systematic way. It include technologies such as SAML, OIDC and SCIM , etc Presenting Integration Technologies For Implementing Identify And Access Management Technique Portrait PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Technology, Features, Cost. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
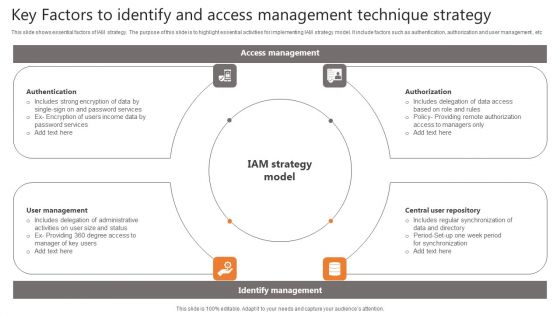
Key Factors To Identify And Access Management Technique Strategy Elements PDF
This slide shows essential factors of IAM strategy. The purpose of this slide is to highlight essential activities for implementing IAM strategy model. It include factors such as authentication, authorization and user management , etc Persuade your audience using this Key Factors To Identify And Access Management Technique Strategy Elements PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Authentication, Management, Repository. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
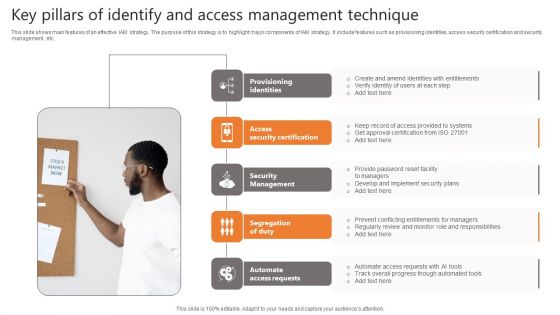
Key Pillars Of Identify And Access Management Technique Topics PDF
This slide shows main features of an effective IAM strategy. The purpose of this strategy is to highlight major components of IAM strategy. It include features such as provisioning identities, access security certification and security management , etc. Presenting Key Pillars Of Identify And Access Management Technique Topics PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Provisioning Identities, Security Certification, Security Management. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
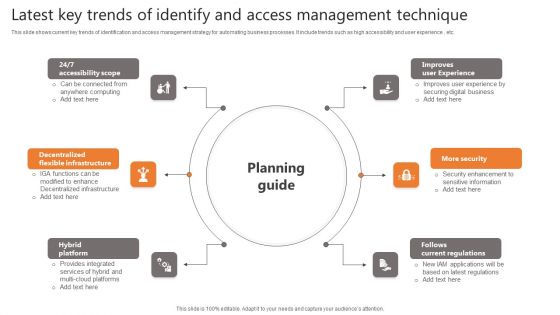
Latest Key Trends Of Identify And Access Management Technique Clipart PDF
This slide shows current key trends of identification and access management strategy for automating business processes. It include trends such as high accessibility and user experience , etc. Persuade your audience using this Latest Key Trends Of Identify And Access Management Technique Clipart PDF. This PPT design covers six stages, thus making it a great tool to use. It also caters to a variety of topics including Accessibility Scope, Flexible Infrastructure, Hybrid Platform. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
One Year Identify And Access Management Technique Roadmap Plan Icons PDF
This slide shows implementation and integration roadmap plan divided into quarters for IAM strategy for automation of operations and other business activities. It include steps such as plan IAM rollout and ensure training , etc Showcasing this set of slides titled One Year Identify And Access Management Technique Roadmap Plan Icons PDF. The topics addressed in these templates are Management Services, Process Automation, Auditing. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
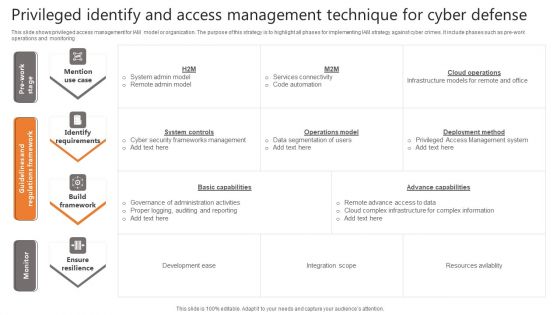
Privileged Identify And Access Management Technique For Cyber Defense Infographics PDF
This slide shows privileged access management for IAM model or organization. The purpose of this strategy is to highlight all phases for implementing IAM strategy against cyber crimes. It include phases such as pre work operations and monitoring Pitch your topic with ease and precision using this Privileged Identify And Access Management Technique For Cyber Defense Infographics PDF. This layout presents information on Identify Requirements, Build Framework, Ensure Resilience. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
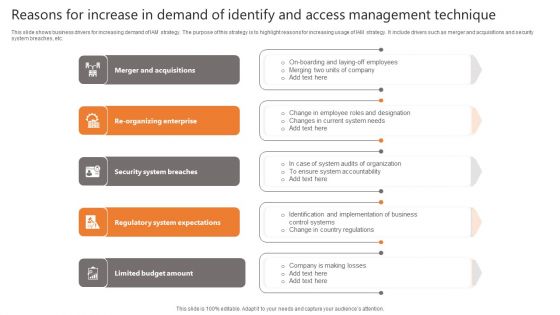
Reasons For Increase In Demand Of Identify And Access Management Technique Sample PDF
This slide shows business drivers for increasing demand of IAM strategy. The purpose of this strategy is to highlight reasons for increasing usage of IAM strategy. It include drivers such as merger and acquisitions and security system breaches, etc. Presenting Reasons For Increase In Demand Of Identify And Access Management Technique Sample PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Security System Breaches, Regulatory System Expectations, Limited Budget Amount. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
Cloud Based Identify And Access Management Technique Introduction PDF
Presenting Cloud Based Identify And Access Management Technique Introduction PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Cloud Based Identify, Access Management, Technique. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
Identify And Access Management Technique Icon Information PDF
Showcasing this set of slides titled Identify And Access Management Technique Icon Information PDF. The topics addressed in these templates are Identify, Access Management, Technique. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Identify And Access Management Technique Mechanism Icon Information PDF
Persuade your audience using this Identify And Access Management Technique Mechanism Icon Information PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Identify, Access Management, Technique Mechanism. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
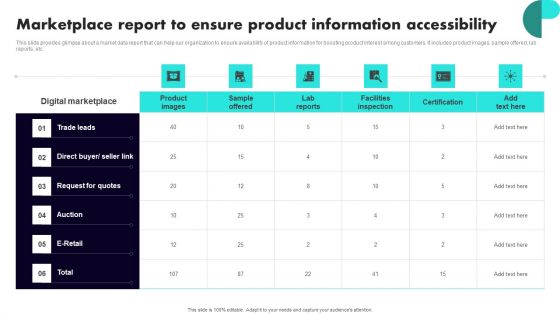
Implementing Client Onboarding Process Marketplace Report To Ensure Product Information Accessibility Microsoft PDF
This slide provides glimpse about a market data report that can help our organization to ensure availability of product information for boosting product interest among customers. It includes product images, sample offered, lab reports, etc. Want to ace your presentation in front of a live audience Our Implementing Client Onboarding Process Marketplace Report To Ensure Product Information Accessibility Microsoft PDF can help you do that by engaging all the users towards you.. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy-to-edit and downloadable. Use these for both personal and commercial use.
-
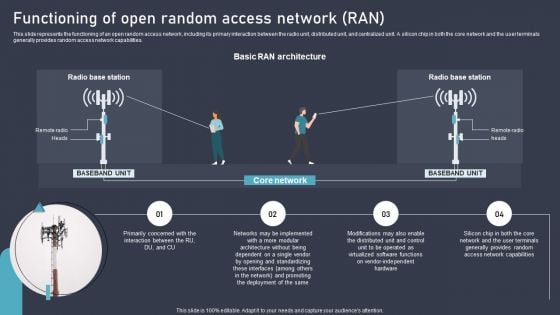
O RAN Architecture Functioning Of Open Random Access Network RAN Clipart PDF
This slide represents the functioning of an open random access network, including its primary interaction between the radio unit, distributed unit, and centralized unit. A silicon chip in both the core network and the user terminals generally provides random access network capabilities. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. O RAN Architecture Functioning Of Open Random Access Network RAN Clipart PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.
-
O RAN Architecture Introduction To Open Random Access Network Ran Icons PDF
This slide represents the introduction to open RAN standards in telecommunication systems, a partnership between device manufacturers and telecommunications to overcome the interoperability challenge. Slidegeeks is here to make your presentations a breeze with O RAN Architecture Introduction To Open Random Access Network Ran Icons PDF With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, youre sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether youre giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.
-
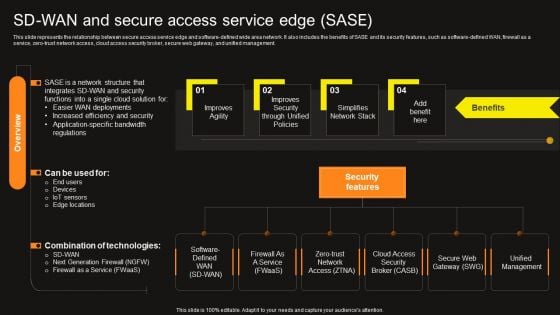
Virtual WAN Architecture Sd Wan And Secure Access Service Edge Sase Formats PDF
This slide represents the relationship between secure access service edge and software-defined wide area network. It also includes the benefits of SASE and its security features, such as software-defined WAN, firewall as a service, zero-trust network access, cloud access security broker, secure web gateway, and unified management. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Virtual WAN Architecture Sd Wan And Secure Access Service Edge Sase Formats PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Virtual WAN Architecture Sd Wan And Secure Access Service Edge Sase Formats PDF today and make your presentation stand out from the rest.
-
Virtual WAN Architecture Secure Access Service Edge Vs SD WAN Ideas PDF
This slide compares secure access service edge and software-defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD-WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. This modern and well-arranged Virtual WAN Architecture Secure Access Service Edge Vs SD WAN Ideas PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint, no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.
-
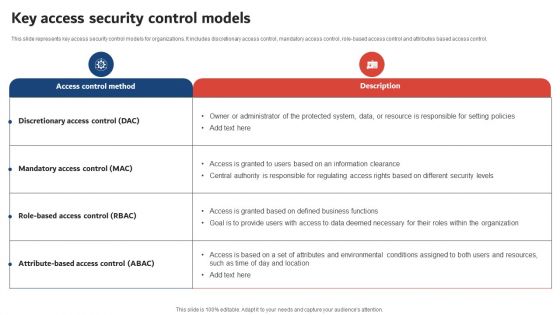
Execution Of ICT Strategic Plan Key Access Security Control Models Topics PDF
This slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role-based access control and attributes based access control, Do you know about Slidesgeeks Execution Of ICT Strategic Plan Key Access Security Control Models Topics PDF These are perfect for delivering any kind od presentation. Using it, create PowerPoint presentations that communicate your ideas and engage audiences. Save time and effort by using our pre designed presentation templates that are perfect for a wide range of topic. Our vast selection of designs covers a range of styles, from creative to business, and are all highly customizable and easy to edit. Download as a PowerPoint template or use them as Google Slides themes.
-
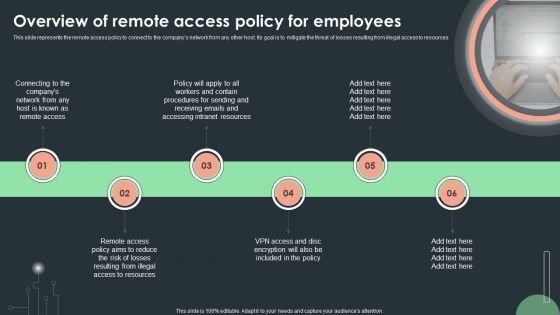
Cybersecurity Guidelines IT Overview Of Remote Access Policy For Employees Structure PDF
This slide represents the remote access policy to connect to the companys network from any other host. Its goal is to mitigate the threat of losses resulting from illegal access to resources. Create an editable Cybersecurity Guidelines IT Overview Of Remote Access Policy For Employees Structure PDF that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. Cybersecurity Guidelines IT Overview Of Remote Access Policy For Employees Structure PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
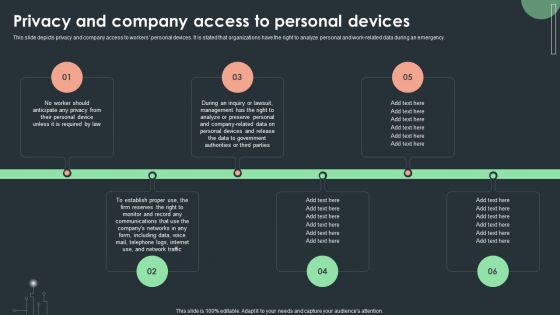
Cybersecurity Guidelines IT Privacy And Company Access To Personal Devices Diagrams PDF
This slide depicts privacy and company access to workers personal devices. It is stated that organizations have the right to analyze personal and work-related data during an emergency. Want to ace your presentation in front of a live audience Our Cybersecurity Guidelines IT Privacy And Company Access To Personal Devices Diagrams PDF can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy-to-edit and downloadable. Use these for both personal and commercial use.
-
Enabling Brand Portfolio Components Of Brand Portfolio Strategy For Better Access To New Clipart PDF
This slide covers the fundamental principles of creating an effective brand communication strategy. It includes guidelines such as building and leveraging strong corporate bonds, defining strategic objectives for brands, employing simple and clear brand architecture, etc. Make sure to capture your audiences attention in your business displays with our gratis customizable Enabling Brand Portfolio Components Of Brand Portfolio Strategy For Better Access To New Clipart PDF. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.
-
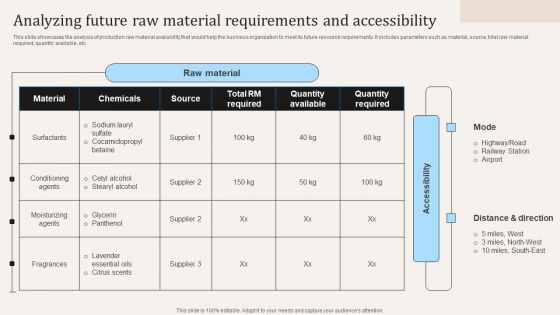
Analyzing Future Raw Material Requirements And Accessibility Ppt PowerPoint Presentation File Example PDF
This slide showcases the analysis of production raw material availability that would help the business organization to meet its future resource requirements. It includes parameters such as material, source, total raw material required, quantity available, etc. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy to edit and customizable templates. Analyzing Future Raw Material Requirements And Accessibility Ppt PowerPoint Presentation File Example PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.