Technological risks PowerPoint Presentation Templates and Google Slides
-
Icon Risk Evaluation Of Information Technology Systems Summary PDF
Download our innovative and attention grabbing Icon Risk Evaluation Of Information Technology Systems Summary PDF template. The set of slides exhibit completely customizable icons. These icons can be incorporated into any business presentation. So download it immediately to clearly communicate with your clientele.
-
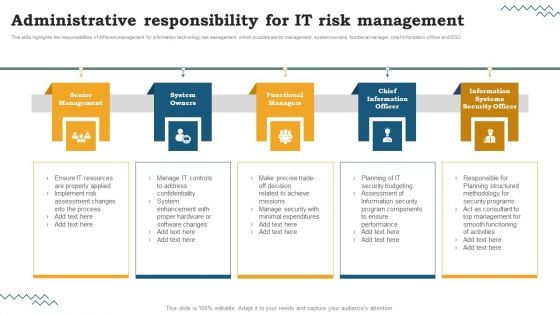
Risk Evaluation Of Information Technology Systems Administrative Responsibility For IT Risk Management Template PDF
This slide highlights the responsibilities of different management for information technology risk management which includes senior management, system owners, functional manager, chief information officer and ISSO. Create an editable Risk Evaluation Of Information Technology Systems Administrative Responsibility For IT Risk Management Template PDF that communicates your idea and engages your audience. Whether youre presenting a business or an educational presentation, pre-designed presentation templates help save time. Risk Evaluation Of Information Technology Systems Administrative Responsibility For IT Risk Management Template PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
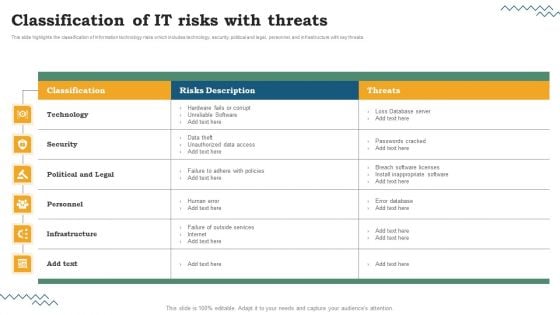
Risk Evaluation Of Information Technology Systems Classification Of IT Risks With Threats Clipart PDF
This slide highlights the classification of information technology risks which includes technology, security, political and legal, personnel, and infrastructure with key threats. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Risk Evaluation Of Information Technology Systems Classification Of IT Risks With Threats Clipart PDF for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
-
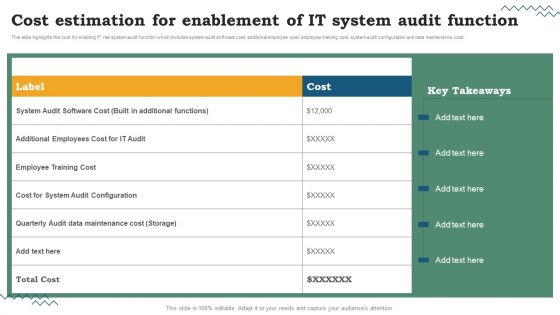
Risk Evaluation Of Information Technology Systems Cost Estimation For Enablement Of IT System Audit Function Clipart PDF
This slide highlights the cost for enabling IT risk system audit function which includes system audit software cost, additional employee cost, employee training cost, system audit configuration and data maintenance cost. Want to ace your presentation in front of a live audience. Our Risk Evaluation Of Information Technology Systems Cost Estimation For Enablement Of IT System Audit Function Clipart PDF can help you do that by engaging all the users towards you.. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy-to-edit and downloadable. Use these for both personal and commercial use.
-
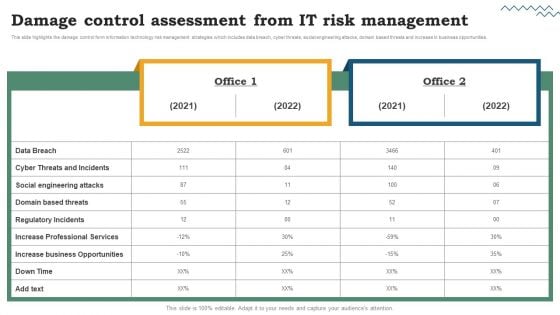
Risk Evaluation Of Information Technology Systems Damage Control Assessment From IT Risk Management Download PDF
This slide highlights the damage control form information technology risk management strategies which includes data breach, cyber threats, social engineering attacks, domain based threats and increase in business opportunities. There are so many reasons you need a Risk Evaluation Of Information Technology Systems Damage Control Assessment From IT Risk Management Download PDF. The first reason is you cant spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
-
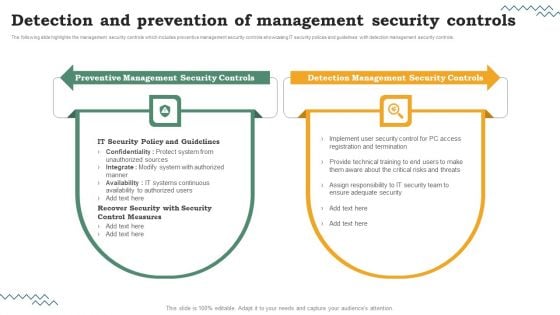
Risk Evaluation Of Information Technology Systems Detection And Prevention Of Management Security Controls Microsoft PDF
Do you have to make sure that everyone on your team knows about any specific topic. I yes, then you should give Risk Evaluation Of Information Technology Systems The following slide highlights the management security controls which includes preventive management security controls showcasing IT security polices and guidelines with detection management security controls. Detection And Prevention Of Management Security Controls Microsoft PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable Risk Evaluation Of Information Technology Systems Detection And Prevention Of Management Security Controls Microsoft PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.
-
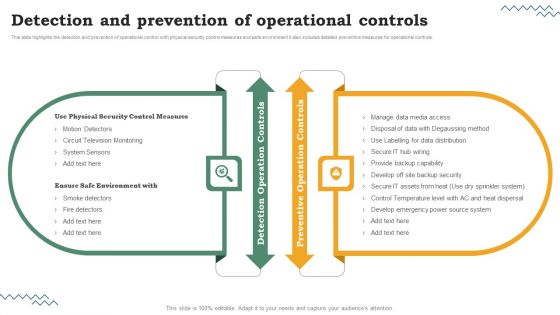
Risk Evaluation Of Information Technology Systems Detection And Prevention Of Operational Controls Portrait PDF
This slide highlights the detection and prevention of operational control with physical security control measures and safe environment it also includes detailed preventive measures for operational controls. Get a simple yet stunning designed Risk Evaluation Of Information Technology Systems Detection And Prevention Of Operational Controls Portrait PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Risk Evaluation Of Information Technology Systems Detection And Prevention Of Operational Controls Portrait PDF can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for. Grab this template today.
-
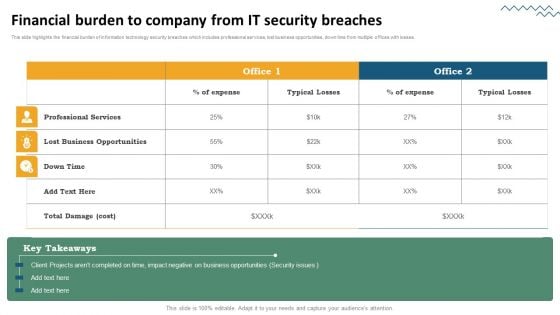
Risk Evaluation Of Information Technology Systems Financial Burden To Company From IT Security Breaches Inspiration PDF
This slide highlights the financial burden of information technology security breaches which includes professional services, lost business opportunities, down time from multiple offices with losses. Present like a pro with Risk Evaluation Of Information Technology Systems Financial Burden To Company From IT Security Breaches Inspiration PDF Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
-
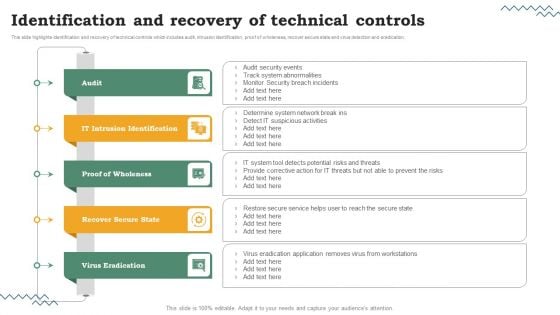
Risk Evaluation Of Information Technology Systems Identification And Recovery Of Technical Controls Designs PDF
This slide highlights identification and recovery of technical controls which includes audit, intrusion identification, proof of wholeness, recover secure state and virus detection and eradication. Slidegeeks is here to make your presentations a breeze with Risk Evaluation Of Information Technology Systems Identification And Recovery Of Technical Controls Designs PDF With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether youre giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.
-
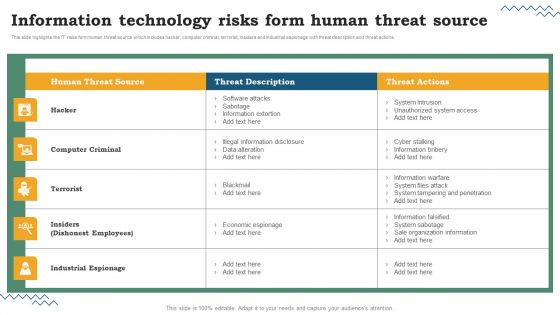
Risk Evaluation Of Information Technology Systems Information Technology Risks Form Human Threat Source Structure PDF
This slide highlights the IT risks form human threat source which includes hacker, computer criminal, terrorist, insiders and industrial espionage with threat description and threat actions. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Risk Evaluation Of Information Technology Systems Information Technology Risks Form Human Threat Source Structure PDF can be your best option for delivering a presentation. Represent everything in detail using Risk Evaluation Of Information Technology Systems Information Technology Risks Form Human Threat Source Structure PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.
-
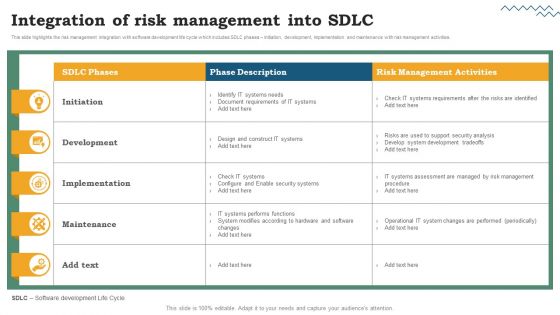
Risk Evaluation Of Information Technology Systems Integration Of Risk Management Into SDLC Demonstration PDF
This slide highlights the risk management integration with software development life cycle which includes SDLC phases Initiation, development, implementation and maintenance with risk management activities. Find highly impressive Risk Evaluation Of Information Technology Systems Integration Of Risk Management Into SDLC Demonstration PDF on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Risk Evaluation Of Information Technology Systems Integration Of Risk Management Into SDLC Demonstration PDF for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now.
-
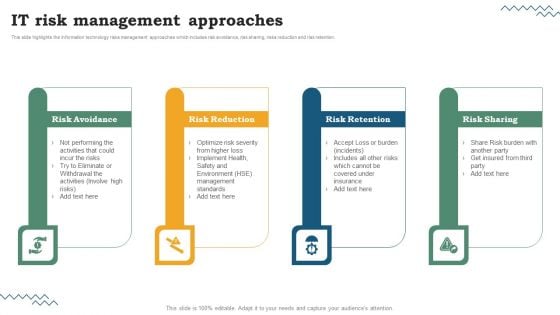
Risk Evaluation Of Information Technology Systems IT Risk Management Approaches Sample PDF
This slide highlights the information technology risks management approaches which includes risk avoidance, risk sharing, risks reduction and risk retention. If your project calls for a presentation, then Slidegeeks is your go-to partner because we have professionally designed, easy-to-edit templates that are perfect for any presentation. After downloading, you can easily edit Risk Evaluation Of Information Technology Systems IT Risk Management Approaches Sample PDF and make the changes accordingly. You can rearrange slides or fill them with different images. Check out all the handy templates
-
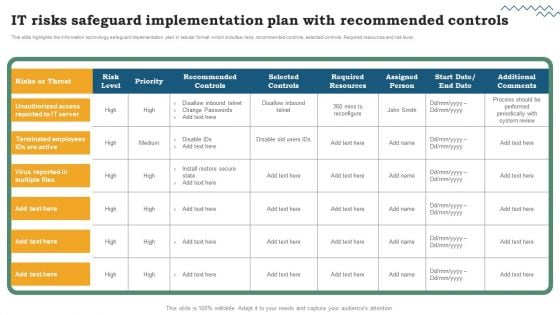
Risk Evaluation Of Information Technology Systems IT Risks Safeguard Implementation Plan With Recommended Controls Introduction PDF
This slide highlights the information technology safeguard implementation plan in tabular format which includes risks, recommended controls, selected controls. Required resources and risk level. Are you in need of a template that can accommodate all of your creative concepts. This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Risk Evaluation Of Information Technology Systems IT Risks Safeguard Implementation Plan With Recommended Controls Introduction PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.
-
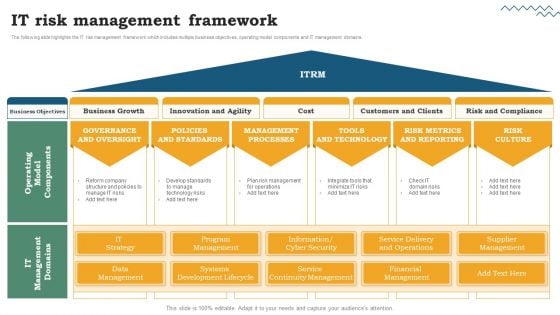
Risk Evaluation Of Information Technology Systems Software Development Life Cycle Planning IT Risk Management Framework Structure PDF
Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Risk Evaluation Of Information The following slide highlights the IT risk management framework which includes multiple business objectives, operating model components and IT management domains.Technology Systems Software Development Life Cycle Planning IT Risk Management Framework Structure PDF template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Risk Evaluation Of Information Technology Systems Software Development Life Cycle Planning IT Risk Management Framework Structure PDF that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers.
-
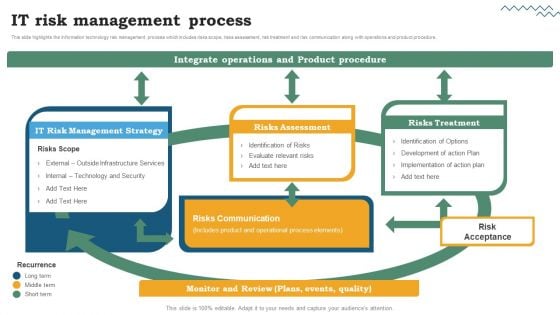
Risk Evaluation Of Information Technology Systems Software Development Life Cycle Planning IT Risk Management Process Inspiration PDF
This slide highlights the information technology risk management process which includes risks scope, risks assessment, risk treatment and risk communication along with operations and product procedure. Make sure to capture your audiences attention in your business displays with our gratis customizable Risk Evaluation Of Information Technology Systems Software Development Life Cycle Planning IT Risk Management Process Inspiration PDF. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.
-
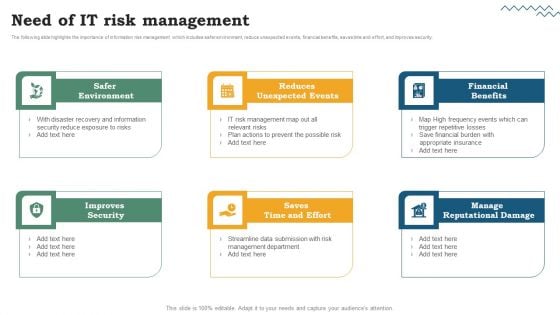
Risk Evaluation Of Information Technology Systems Software Development Life Cycle Planning Need Of IT Risk Management Elements PDF
Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance The following slide highlights the importance of information risk management which includes safer environment, reduce unexpected events, financial benefits, saves time and effort, and improves security.the presenters message, so our Risk Evaluation Of Information Technology Systems Software Development Life Cycle Planning Need Of IT Risk Management Elements PDF was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Risk Evaluation Of Information Technology Systems Software Development Life Cycle Planning Need Of IT Risk Management Elements PDF.
-
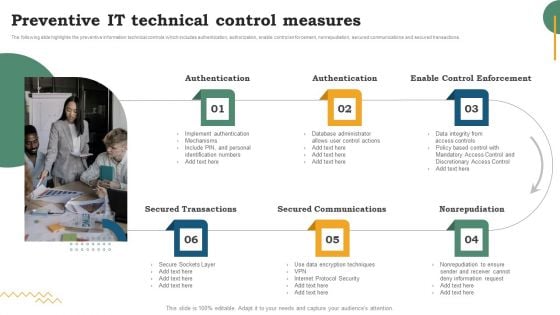
Risk Evaluation Of Information Technology Systems Software Development Life Cycle Planning Preventive IT Technical Control Measures Information PDF
The following slide highlights the preventive information technical controls which includes authentication, authorization, enable control enforcement, nonrepudiation, secured communications and secured transactions. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Risk Evaluation Of Information Technology Systems Software Development Life Cycle Planning Preventive IT Technical Control Measures Information PDF to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.
-
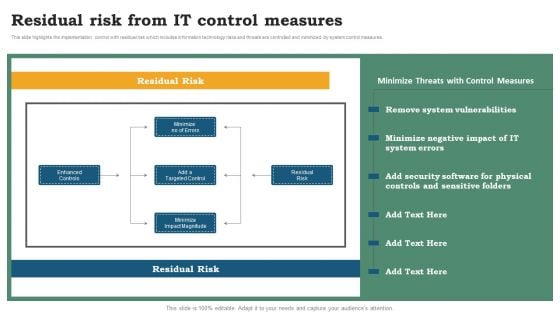
Risk Evaluation Of Information Technology Systems Software Development Life Cycle Planning Residual Risk From IT Control Measures Inspiration PDF
This slide highlights the implementation control with residual risk which includes information technology risks and threats are controlled and minimized by system control measures. This modern and well-arranged Risk Evaluation Of Information Technology Systems Software Development Life Cycle Planning Residual Risk From IT Control Measures Inspiration PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.
-
Project Risk Management And Reduction Technology And Innovation Risk Mitigation Strategies Topics PDF
This slide depicts the strategies and their description to mitigate strategic risks. The strategies covered are use right tools and suitable techniques and consider experimentation. Create an editable Project Risk Management And Reduction Technology And Innovation Risk Mitigation Strategies Topics PDF that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre designed presentation templates help save time. Lack Technology Innovation, Mitigation Strategies, Risk is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-
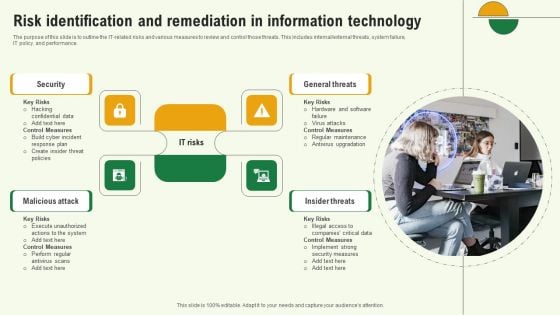
Risk Identification And Remediation In Information Technology Template PDF
The purpose of this slide is to outline the IT related risks and various measures to review and control those threats. This includes internal or external threats, system failure, IT policy, and performance. Persuade your audience using this Risk Identification And Remediation In Information Technology Template PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Insider Threats, General Threats, Security. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
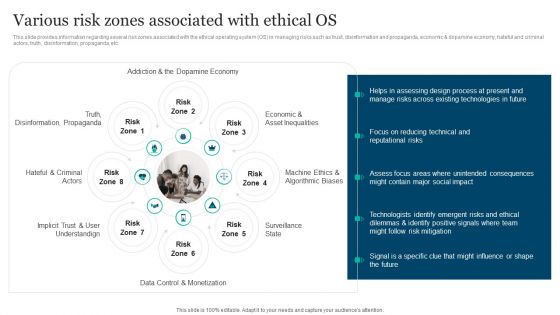
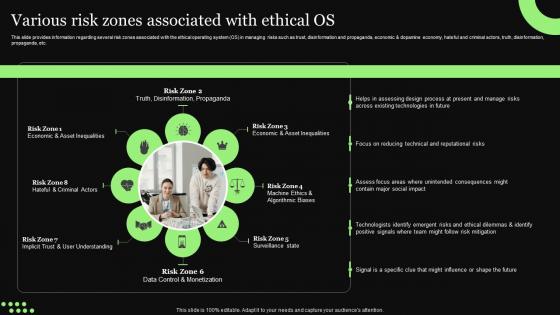
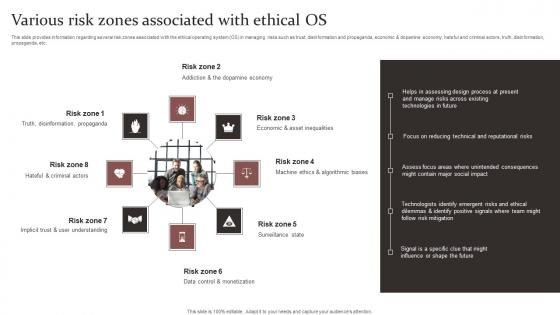
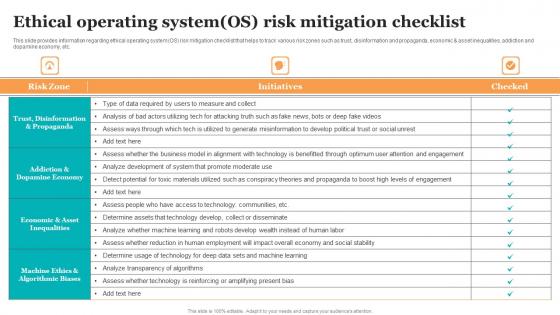
Responsible Technology Playbook Various Risk Zones Associated With Ethical OS Topics PDF
This slide provides information regarding several risk zones associated with the ethical operating system OS in managing risks such as trust, disinformation and propaganda, economic and dopamine economy, hateful and criminal actors, truth, disinformation, propaganda, etc. Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Responsible Technology Playbook Various Risk Zones Associated With Ethical OS Topics PDF template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Responsible Technology Playbook Various Risk Zones Associated With Ethical OS Topics PDF that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers.
-
Strategies For Credit Risk Management Using Technologies To Manage Credit Risk Graphics PDF
This slide covers the methods used by the organizations to minimize the credit risk by increasing the use of new technologies and softwares. This Strategies For Credit Risk Management Using Technologies To Manage Credit Risk Graphics PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Strategies For Credit Risk Management Using Technologies To Manage Credit Risk Graphics PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, dont wait, grab the presentation templates today.
-
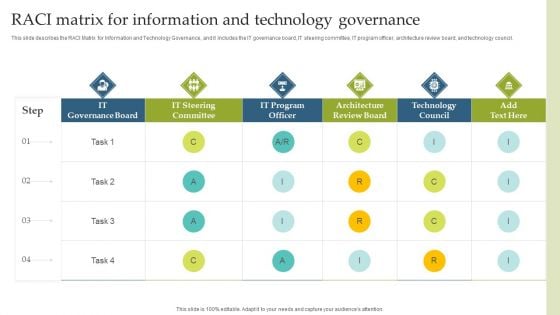
Deploying EGIT To Ensure Optimum Risk Management RACI Matrix For Information And Technology Governance Structure PDF
This slide describes the RACI Matrix for Information and Technology Governance, and it includes the IT governance board, IT steering committee, IT program officer, architecture review board, and technology council. Take your projects to the next level with our ultimate collection of Deploying EGIT To Ensure Optimum Risk Management RACI Matrix For Information And Technology Governance Structure PDF. Slidegeeks has designed a range of layouts that are perfect for representing task or activity duration, keeping track of all your deadlines at a glance. Tailor these designs to your exact needs and give them a truly corporate look with your own brand colors they will make your projects stand out from the rest.
-
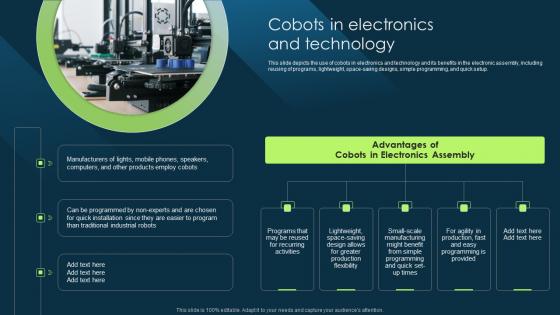
Cobots In Electronics And Technology Cobot Safety Measures And Risk Pictures PDF
This slide depicts the use of cobots in electronics and technology and its benefits in the electronic assembly, including reusing of programs, lightweight, space-saving designs, simple programming, and quick setup. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Cobots In Electronics And Technology Cobot Safety Measures And Risk Pictures PDF With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Cobots In Electronics And Technology Cobot Safety Measures And Risk Pictures PDF today and make your presentation stand out from the rest
-
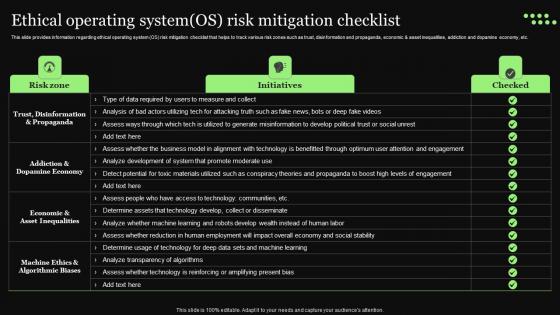
Ethical Technology Utilization Ethical Operating System OS Risk Mitigation Checklist Portrait Pdf
This slide provides information regarding ethical operating system OS risk mitigation checklist that helps to track various risk zones such as trust, disinformation and propaganda, economic and asset inequalities, addiction and dopamine economy, etc. If your project calls for a presentation, then Slidegeeks is your go to partner because we have professionally designed, easy to edit templates that are perfect for any presentation. After downloading, you can easily edit Ethical Technology Utilization Ethical Operating System OS Risk Mitigation Checklist Portrait Pdf and make the changes accordingly. You can rearrange slides or fill them with different images. Check out all the handy templates
-
Ethical Technology Utilization Various Risk Zones Associated With Ethical OS Summary Pdf
This slide provides information regarding several risk zones associated with the ethical operating system OS in managing risks such as trust, disinformation and propaganda, economic and dopamine economy, hateful and criminal actors, truth, disinformation, propaganda, etc. Present like a pro with Ethical Technology Utilization Various Risk Zones Associated With Ethical OS Summary Pdf Create beautiful presentations together with your team, using our easy to use presentation slides. Share your ideas in real time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
-
Various Risk Zones Associated Responsible Technology Governance Manual Information Pdf
This slide provides information regarding several risk zones associated with the ethical operating system OS in managing risks such as trust, disinformation and propaganda, economic and dopamine economy, hateful and criminal actors, truth, disinformation, propaganda, etc. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Various Risk Zones Associated Responsible Technology Governance Manual Information Pdf. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Various Risk Zones Associated Responsible Technology Governance Manual Information Pdf today and make your presentation stand out from the rest.
-
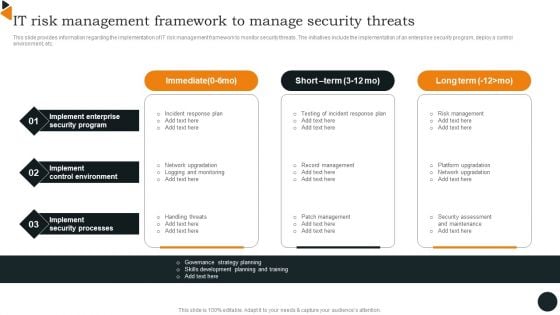
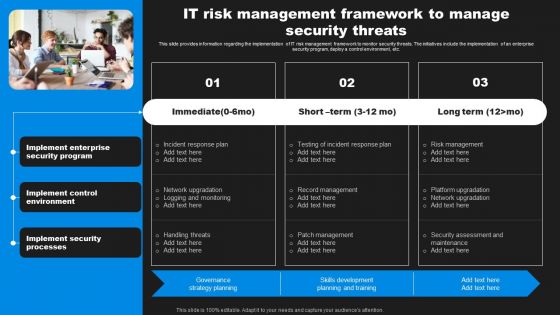
Chief Information Officers Guide On Technology Plan IT Risk Management Framework Infographics PDF
This slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Chief Information Officers Guide On Technology Plan IT Risk Management Framework Infographics PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.
-
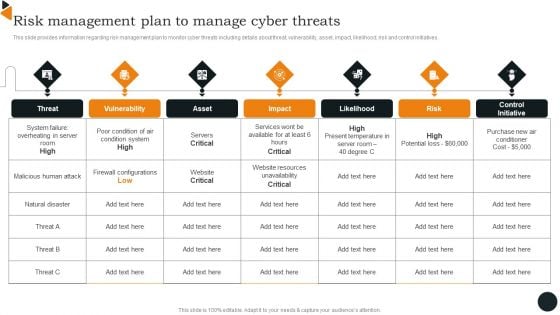
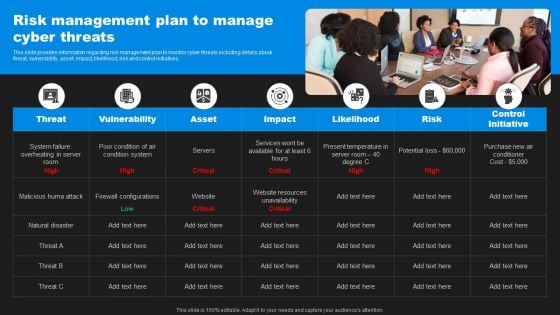
Chief Information Officers Guide On Technology Plan Risk Management Plan Introduction PDF
This slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. This modern and well arranged Chief Information Officers Guide On Technology Plan Risk Management Plan Introduction PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.
-
Ethical Operating System OS Risk Mitigation Checklist Guide For Ethical Technology Inspiration Pdf
This slide provides information regarding ethical operating system OS risk mitigation checklist that helps to track various risk zones such as trust, disinformation and propaganda, economic and asset inequalities, addiction and dopamine economy, etc. If your project calls for a presentation, then Slidegeeks is your go-to partner because we have professionally designed, easy-to-edit templates that are perfect for any presentation. After downloading, you can easily edit Ethical Operating System OS Risk Mitigation Checklist Guide For Ethical Technology Inspiration Pdf and make the changes accordingly. You can rearrange slides or fill them with different images. Check out all the handy templates
-
Various Risk Zones Associated With Ethical OS Guide For Ethical Technology Icons Pdf
This slide provides information regarding several risk zones associated with the ethical operating system OS in managing risks such as trust, disinformation and propaganda, economic and dopamine economy, hateful and criminal actors, truth, disinformation, propaganda, etc. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Various Risk Zones Associated With Ethical OS Guide For Ethical Technology Icons Pdf. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Various Risk Zones Associated With Ethical OS Guide For Ethical Technology Icons Pdf today and make your presentation stand out from the rest.
-
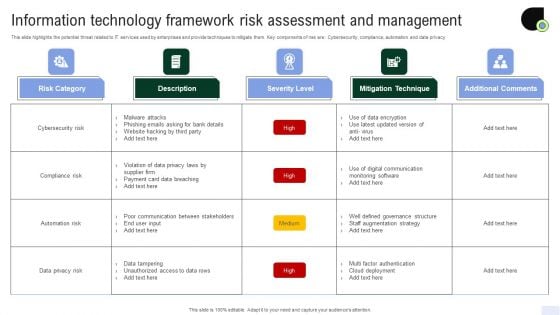
Information Technology Framework Risk Assessment And Management Diagrams PDF
This slide highlights the potential threat related to IT services used by enterprises and provide techniques to mitigate them. Key components of risk are Cybersecurity, compliance, automation and data privacy. Showcasing this set of slides titled Information Technology Framework Risk Assessment And Management Diagrams PDF. The topics addressed in these templates are Malware Attacks, Phishing Emails Asking Bank, Website Hacking Third. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Effective Business Project Risk Mitigation Plan Technology And Innovation Risk Mitigation Strategies Pictures PDF
This slide depicts the strategies and their description to mitigate strategic risks. The strategies covered are use right tools and suitable techniques and consider experimentation. Are you searching for a Effective Business Project Risk Mitigation Plan Technology And Innovation Risk Mitigation Strategies Pictures PDF that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Effective Business Project Risk Mitigation Plan Technology And Innovation Risk Mitigation Strategies Pictures PDF from Slidegeeks today.
-
Comprehensive Resource Guide To Master GPT 3 Risks And Limitations Of Using GPT 3 Technology Slides PDF
This slide showcases restrictions and risks of GPT 3 that hinder its overall performance. It include information about mimicry of human text, decreased accuracy in answers and general bias. Take your projects to the next level with our ultimate collection of Comprehensive Resource Guide To Master GPT 3 Risks And Limitations Of Using GPT 3 Technology Slides PDF. Slidegeeks has designed a range of layouts that are perfect for representing task or activity duration, keeping track of all your deadlines at a glance. Tailor these designs to your exact needs and give them a truly corporate look with your own brand colors they will make your projects stand out from the rest.
-
Enhancing Information Technology With Strategic IT Risk Management Framework Graphics PDF
This slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. Slidegeeks is here to make your presentations a breeze with Enhancing Information Technology With Strategic IT Risk Management Framework Graphics PDF With our easy to use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.
-
Enhancing Information Technology With Strategic Risk Management Plan To Manage Cyber Graphics PDF
This slide provides information regarding risk management plan to monitor cyber threats including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Find highly impressive Enhancing Information Technology With Strategic Risk Management Plan To Manage Cyber Graphics PDF on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Enhancing Information Technology With Strategic Risk Management Plan To Manage Cyber Graphics PDF for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now.
-
Cloud Technology Governance Risk Compliance System Template Pdf
This slide shows governance risk compliance program for cloud based entity to identify and eliminate potential threats. It include compliance initiatives such as threat landscape report, quality standards assurance and contractual audits, etc. Showcasing this set of slides titled Cloud Technology Governance Risk Compliance System Template Pdf. The topics addressed in these templates are Governance Areas, Risks Involved, Compliance Initiatives. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
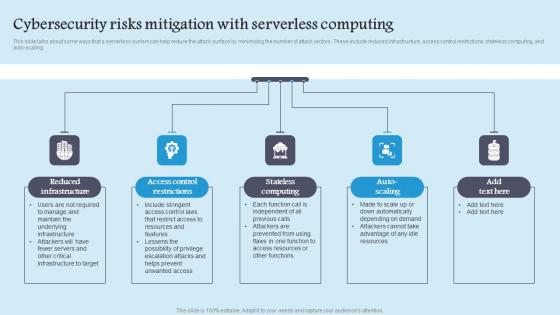
Cybersecurity Risks Mitigation Role Serverless Computing Modern Technology Summary Pdf
This slide talks about some ways that a serverless system can help reduce the attack surface by minimizing the number of attack vectors. These include reduced infrastructure, access control restrictions, stateless computing, and auto scaling. Presenting this PowerPoint presentation, titled Cybersecurity Risks Mitigation Role Serverless Computing Modern Technology Summary Pdf, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Cybersecurity Risks Mitigation Role Serverless Computing Modern Technology Summary Pdf. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Cybersecurity Risks Mitigation Role Serverless Computing Modern Technology Summary Pdf that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.