Terrorism PowerPoint Presentation Templates and Google Slides
-
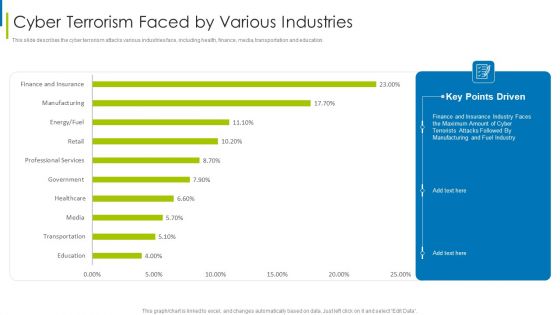
Cyber Terrorism Assault Cyber Terrorism Faced By Various Industries Pictures PDF
This slide describes the cyber terrorism attacks various industries face, including health, finance, media, transportation and education.Deliver an awe inspiring pitch with this creative cyber terrorism assault cyber terrorism faced by various industries pictures pdf bundle. Topics like Cyber Terrorism Faced By Companies In US can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
-
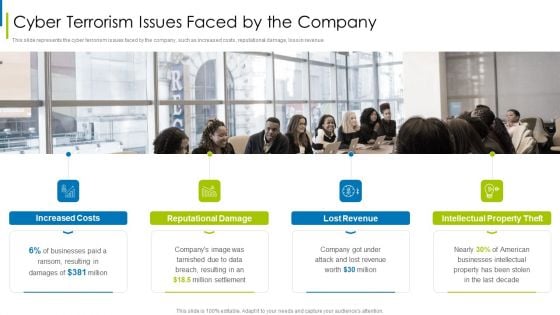
Cyber Terrorism Assault Cyber Terrorism Issues Faced By The Company Microsoft PDF
This slide represents the cyber terrorism issues faced by the company, such as increased costs, reputational damage, loss in revenue.Presenting cyber terrorism assault cyber terrorism issues faced by the company microsoft pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like Professional Services, Government, Finance And Insurance In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-
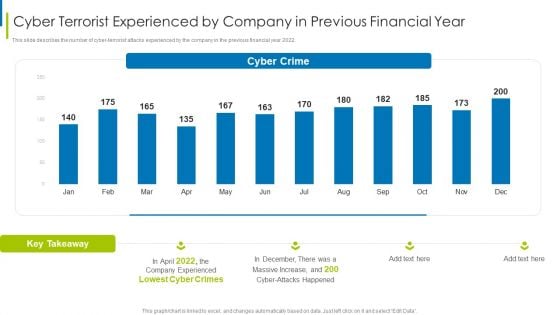
Cyber Terrorism Assault Cyber Terrorist Experienced By Company In Previous Financial Year Sample PDF
This slide describes the number of cyber-terrorist attacks experienced by the company in the previous financial year 2022.Deliver an awe inspiring pitch with this creative cyber terrorism assault cyber terrorist experienced by company in previous financial year sample pdf bundle. Topics like Increased Costs, Reputational Damage, Intellectual Property Theft can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
-
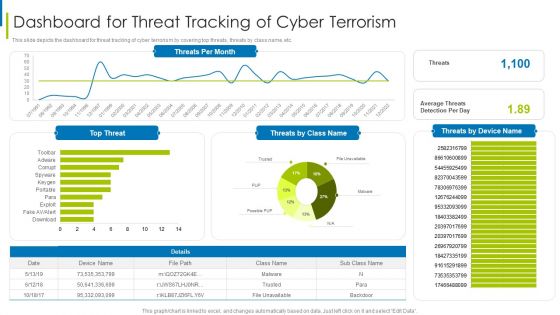
Cyber Terrorism Assault Dashboard For Threat Tracking Of Cyber Terrorism Themes PDF
This slide depicts the dashboard for threat tracking of cyber terrorism by covering top threats, threats by class name, etc.Deliver and pitch your topic in the best possible manner with this cyber terrorism assault dashboard for threat tracking of cyber terrorism themes pdf Use them to share invaluable insights on Massive Increase, Cyber Attacks Happened, Company Experienced and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
-

Cyber Terrorism Assault Disaster Recovery Plan For The Business Template PDF
This slide illustrates the elements that will be taken into account when establishing a recovery plan for company to go back to business swiftly and successfully.This is a cyber terrorism assault disaster recovery plan for the business template pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Dashboard For Threat Tracking Of Cyber Terrorism You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-
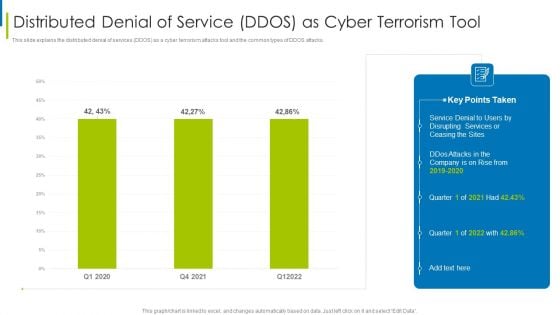
Cyber Terrorism Assault Distributed Denial Of Service DDOS As Cyber Terrorism Tool Slides PDF
This slide explains the distributed denial of services DDOS as a cyber terrorism attacks tool and the common types of DDOS attacks.Deliver and pitch your topic in the best possible manner with this cyber terrorism assault distributed denial of service ddos as cyber terrorism tool slides pdf Use them to share invaluable insights on Make A Risk Assessment, Determine The Importance Of Assets, Make A Complete Inventory and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
-
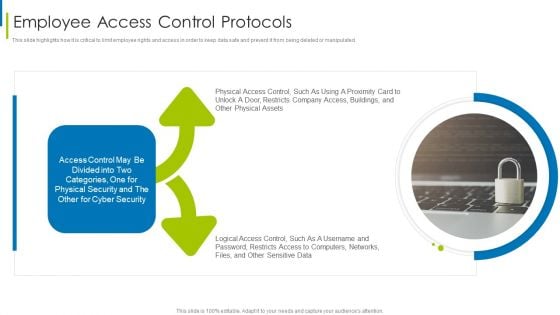
Cyber Terrorism Assault Employee Access Control Protocols Diagrams PDF
This slide highlights how it is critical to limit employee rights and access in order to keep data safe and prevent it from being deleted or manipulated.This is a cyber terrorism assault employee access control protocols diagrams pdf template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Distributed Denial Of Service DDOS As Cyber Terrorism Tool You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-
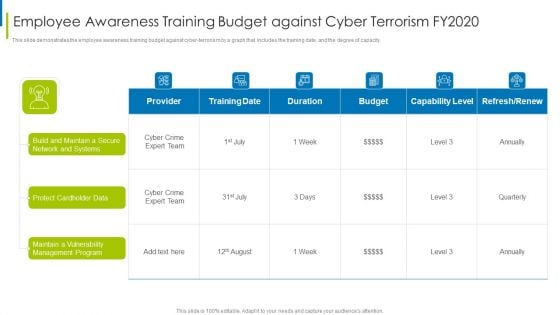
Cyber Terrorism Assault Employee Awareness Training Budget Against Cyber Terrorism FY2020 Inspiration PDF
This slide demonstrates the employee awareness training budget against cyber-terrorism by a graph that includes the training date, and the degree of capacity. Deliver an awe inspiring pitch with this creative cyber terrorism assault employee awareness training budget against cyber terrorism fy2020 inspiration pdf bundle. Topics like Protect Cardholder Data, Maintain A Vulnerability, Management Program can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
-
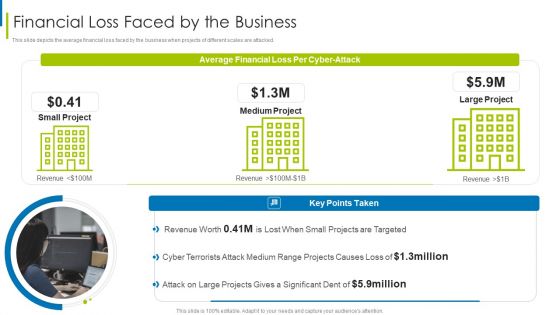
Cyber Terrorism Assault Financial Loss Faced By The Business Summary PDF
This slide depicts the average financial loss faced by the business when projects of different scales are attacked.This is a cyber terrorism assault financial loss faced by the business summary pdf template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like projects are targeted, cyber terrorists, attack on large You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-

Cyber Terrorism Assault How To Prevent Ddos Attacks In The Company Inspiration PDF
This slide represents the ways to prevent DDoS attacks in the company, which include network monitoring, updating security elements, etc.Presenting cyber terrorism assault how to prevent ddos attacks in the company inspiration pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like service providers bandwidth capacity, network monitoring, update security components In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-

Cyber Terrorism Assault How To Protect Company From Trojan Attacks Demonstration PDF
This slide explains how to protect the company from trojan attacks which include procedures such as installing advanced antivirus software. This is a cyber terrorism assault how to protect company from trojan attacks demonstration pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like device conventional, next generation antivirus, prevent trojan infection You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-
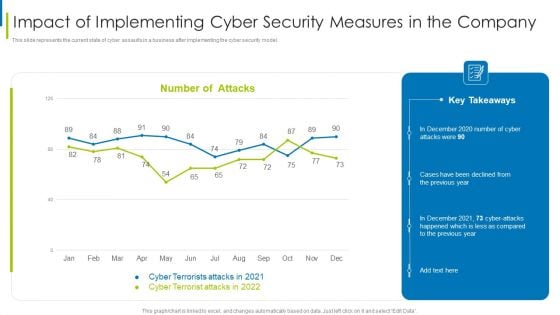
Cyber Terrorism Assault Impact Of Implementing Cyber Security Measures In The Company Professional PDF
This slide represents the current state of cyber assaults in a business after implementing the cyber security model.Deliver an awe inspiring pitch with this creative cyber terrorism assault impact of implementing cyber security measures in the company professional pdf bundle. Topics like impact of implementing cyber security measures in the company can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
-
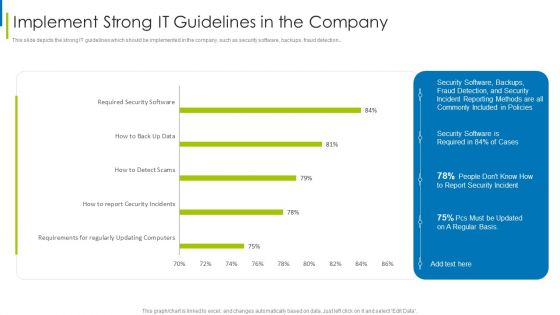
Cyber Terrorism Assault Implement Strong IT Guidelines In The Company Themes PDF
This slide depicts the strong IT guidelines which should be implemented in the company, such as security software, backups, fraud detection.Deliver and pitch your topic in the best possible manner with this cyber terrorism assault implement strong it guidelines in the company themes pdf Use them to share invaluable insights on requirements regularly, updating computers, required security software and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
-

Cyber Terrorism Assault Implementing Least Privilege Administrative Model Demonstration PDF
This slide depicts that administration and employees should have limited access to the information and confidential data.Presenting cyber terrorism assault implementing least privilege administrative model demonstration pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like prevent cybercriminals, harmful insiders, limited access In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-
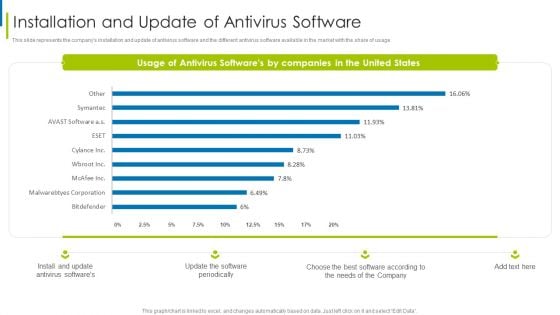
Cyber Terrorism Assault Installation And Update Of Antivirus Software Slides PDF
This slide represents the companys installation and update of antivirus software and the different antivirus software available in the market with the share of usage.Deliver an awe inspiring pitch with this creative cyber terrorism assault installation and update of antivirus software slides pdf bundle. Topics like antivirus softwares, software periodically, softwares by companies can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
-

Cyber Terrorism Assault IT Infrastructure Cyber Security Budget Against Cyber Terrorism FY19 20 Themes PDF
This slide depicts the IT infrastructure budget of incorporating cyber security, as well as the cost of each activity to the company.Deliver and pitch your topic in the best possible manner with this cyber terrorism assault it infrastructure cyber security budget against cyber terrorism fy19 20 themes pdf Use them to share invaluable insights on cloud security, integrated risk management, identify access management and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
-

Cyber Terrorism Assault Malicious Code Malware Misused For Cyber Terrorism Pictures PDF
This slide depicts the malicious code or malware misused for cyber terrorism attacks to hijack or access information from computers.Presenting cyber terrorism assault malicious code malware misused for cyber terrorism pictures pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like broad spectrum, executed by changing, programmer by stopping In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-
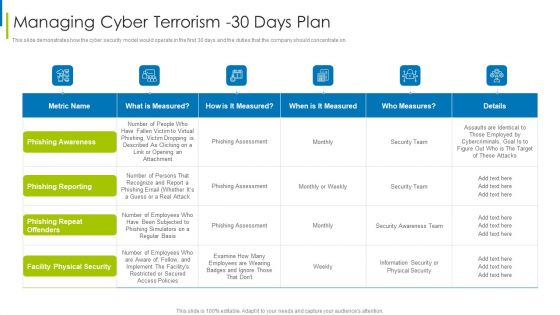
Cyber Terrorism Assault Managing Cyber Terrorism 30 Days Plan Infographics PDF
This slide demonstrates how the cyber security model would operate in the first 30 days and the duties that the company should concentrate on.Deliver an awe inspiring pitch with this creative cyber terrorism assault managing cyber terrorism 30 days plan infographics pdf bundle. Topics like facility physical security, phishing repeat offenders, phishing reporting can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
-
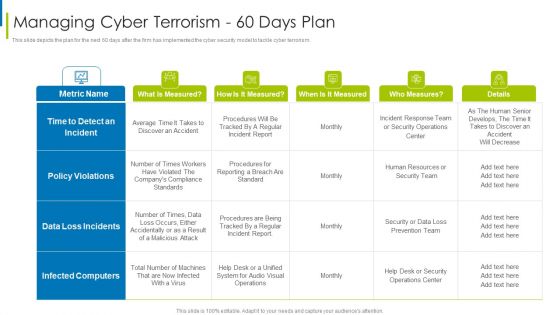
Cyber Terrorism Assault Managing Cyber Terrorism 60 Days Plan Clipart PDF
This slide depicts the plan for the next 60 days after the firm has implemented the cyber security model to tackle cyber terrorism.Deliver and pitch your topic in the best possible manner with this cyber terrorism assault managing cyber terrorism 60 days plan clipart pdf Use them to share invaluable insights on time to detect an incident, data loss incidents, infected computers and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
-
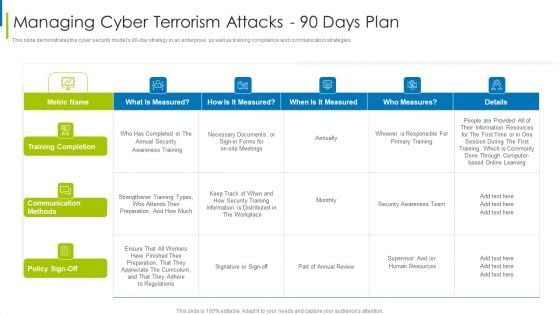
Cyber Terrorism Assault Managing Cyber Terrorism Attacks 90 Days Plan Formats PDF
This slide demonstrates the cyber security models 90 to day strategy in an enterprise, as well as training compliance and communication strategies.Deliver and pitch your topic in the best possible manner with this cyber terrorism assault managing cyber terrorism attacks 90 days plan formats pdf Use them to share invaluable insights on training completion, communication methods, information is distributed and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
-

Cyber Terrorism Assault Peroration Of Cyber Terrorism Attacks Sample PDF
This slide explains the conclusion or peroration of cyber terrorism and how it is different from information warfare as it targets civilians rather than operations. This is a cyber terrorism assault peroration of cyber terrorism attacks sample pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like monitored closely, implemented and every aspect, ideological gain oriented You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-

Cyber Terrorism Assault Phishing Cyber Terrorism Tool Slides PDF
This slide describes phishing in which an attacker tricks a victim to open an email, provide card credentials or any sensitive information.Presenting cyber terrorism assault phishing cyber terrorism tool slides pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like attacker poses, sensitive information, business that are victims In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-
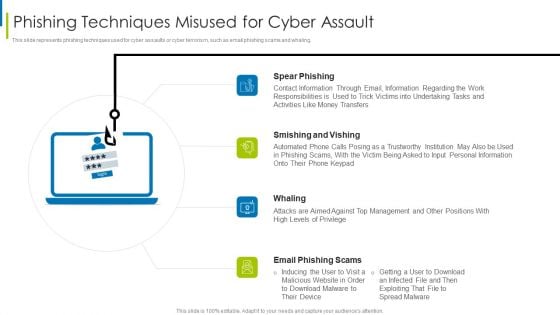
Cyber Terrorism Assault Phishing Techniques Misused For Cyber Assault Slides PDF
This slide represents phishing techniques used for cyber assaults or cyber terrorism, such as email phishing scams and whaling. This is a cyber terrorism assault phishing techniques misused for cyber assault slides pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like smishing and vishing, spear phishing, contact information through You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-

Cyber Terrorism Assault Reputational Loss Faced By The Company Inspiration PDF
This slide demonstrates the reputational loss of the company due to cyber terrorism, which leads to the customers leaving and a decline in sales.This is a cyber terrorism assault reputational loss faced by the company inspiration pdf template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like reputational loss faced by the company You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-

Cyber Terrorism Assault Roadmap To Implement Cyber Security To Mitigate Cyber Terrorism Template PDF
This slide depicts the roadmap to implement strategies to mitigate cyber terrorism such as training employees about cyber terrorism, creating personal accounts.Presenting cyber terrorism assault roadmap to implement cyber security to mitigate cyber terrorism template pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like creating personal accounts, awareness training, keep the hardware In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-
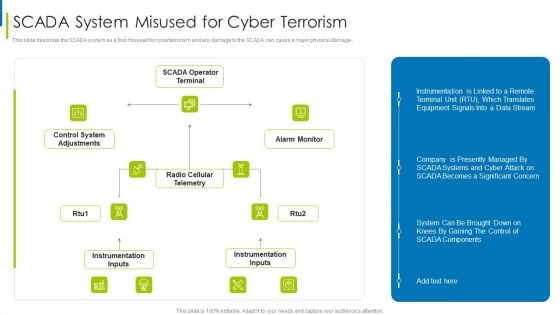
Cyber Terrorism Assault SCADA System Misused For Cyber Terrorism Themes PDF
This slide describes the SCADA system as a tool misused for cyberterrorism and any damage to the SCADA can cause a major physical damage.Deliver an awe inspiring pitch with this creative cyber terrorism assault scada system misused for cyber terrorism themes pdf bundle. Topics like instrumentation inputs, control system adjustments, radio cellular telemetry can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
-
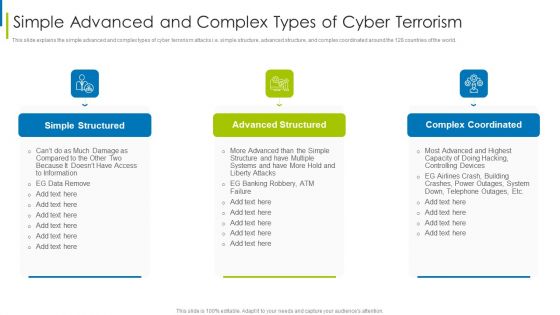
Cyber Terrorism Assault Simple Advanced And Complex Types Of Cyber Terrorism Structure PDF
This slide explains the simple advanced and complex types of cyber terrorism attacks i.e. simple structure, advanced structure, and complex coordinated around the 128 countries of the world.This is a cyber terrorism assault simple advanced and complex types of cyber terrorism structure pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like simple structured, advanced structured, complex coordinated You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-

Cyber Terrorism Assault Strategies To Keep Company Safe From Cyber Terrorists Attacks Pictures PDF
This slide describes the checklist to deal with cyber terrorism threats and counter it such as go after the perpetrators and prosecute them.Presenting cyber terrorism assault strategies to keep company safe from cyber terrorists attacks pictures pdf to provide visual cues and insights. Share and navigate important information on eight stages that need your due attention. This template can be used to pitch topics like inculcate best security, practices by adopting, international security In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-
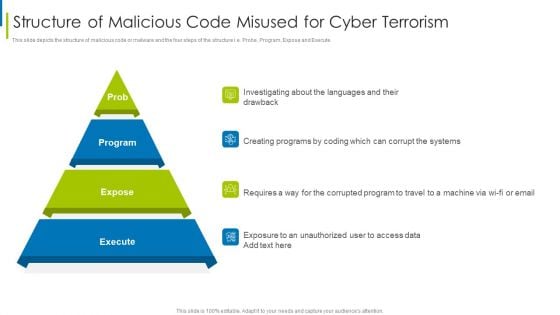
Cyber Terrorism Assault Structure Of Malicious Code Misused For Cyber Terrorism Rules PDF
This slide depicts the structure of malicious code or malware and the four steps of the structure i.e. Probe, Program, Expose and Execute.This is a cyber terrorism assault structure of malicious code misused for cyber terrorism rules pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like investigating about the languages, creating programs by coding, requires a way for the corrupted You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-
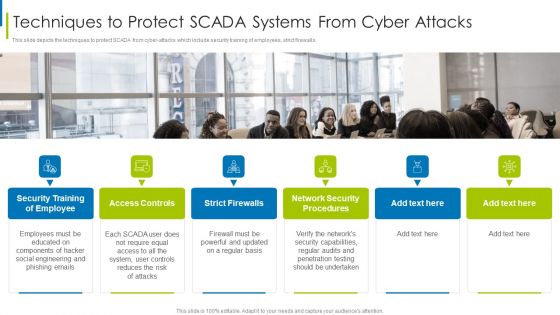
Cyber Terrorism Assault Techniques To Protect SCADA Systems From Cyber Attacks Demonstration PDF
This slide depicts the techniques to protect SCADA from cyber-attacks which include security training of employees, strict firewalls.Presenting cyber terrorism assault techniques to protect scada systems from cyber attacks demonstration pdf to provide visual cues and insights. Share and navigate important information on six stages that need your due attention. This template can be used to pitch topics like access controls, strict firewalls, network security procedures In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-
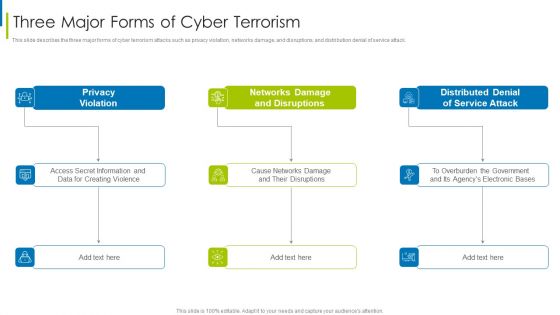
Cyber Terrorism Assault Three Major Forms Of Cyber Terrorism Brochure PDF
This slide describes the three major forms of cyber terrorism attacks such as privacy violation, networks damage, and disruptions, and distribution denial of service attack.This is a cyber terrorism assault three major forms of cyber terrorism brochure pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like privacy violation, networks damage and disruptions, distributed denial You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-
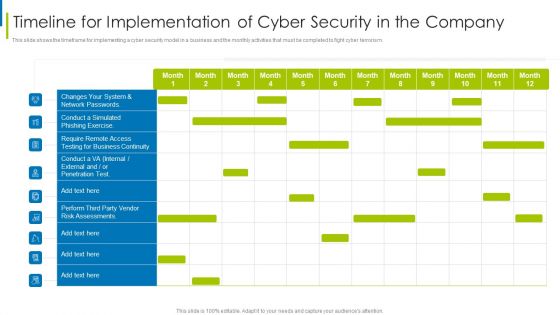
Cyber Terrorism Assault Timeline For Implementation Of Cyber Security In The Company Sample PDF
This slide shows the timeframe for implementing a cyber security model in a business and the monthly activities that must be completed to fight cyber terrorism.Deliver an awe inspiring pitch with this creative cyber terrorism assault timeline for implementation of cyber security in the company sample pdf bundle. Topics like require remote access, testing for business continuity, risk assessments can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
-
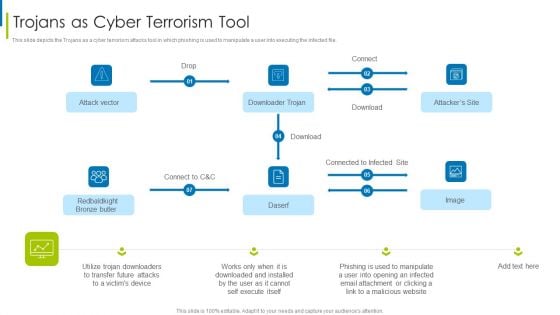
Cyber Terrorism Assault Trojans As Cyber Terrorism Tool Brochure PDF
This slide depicts the Trojans as a cyber terrorism attacks tool in which phishing is used to manipulate a user into executing the infected file.Deliver and pitch your topic in the best possible manner with this cyber terrorism assault trojans as cyber terrorism tool brochure pdf Use them to share invaluable insights on trojans as cyber terrorism tool and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
-

Cyber Terrorism Assault Types Of Ddos Attacks In The Company Sample PDF
This slide demonstrates the types of DDoS attacks happening in the company, which include volume-based attacks, protocol-based attacks, and application layer attacks. This is a cyber terrorism assault types of ddos attacks in the company sample pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like volume based attacks, protocol based attacks, application layer attacks You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-

Cyber Terrorism Assault Types Of Trojans Misused In Cyber Terrorism Background PDF
This slide describes the types of trojans misused in cyber terrorism attacks such as downloader trojan, spyware, backdoor trojan, and rootkit trojans. Presenting cyber terrorism assault types of trojans misused in cyber terrorism background pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like backdoor trojan, downloader trojan, rootkit trojans In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-
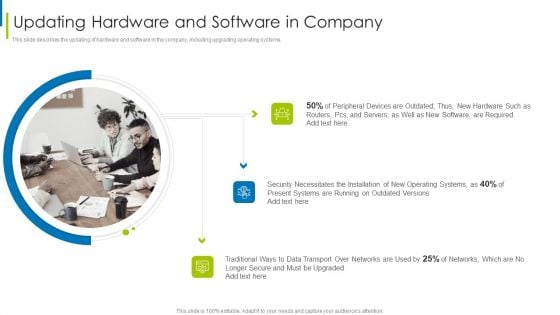
Cyber Terrorism Assault Updating Hardware And Software In Company Infographics PDF
This slide describes the updating of hardware and software in the company, including upgrading operating systems.Deliver an awe inspiring pitch with this creative cyber terrorism assault updating hardware and software in company infographics pdf bundle. Topics like peripheral devices, security necessitates, traditional ways to data transport can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
-
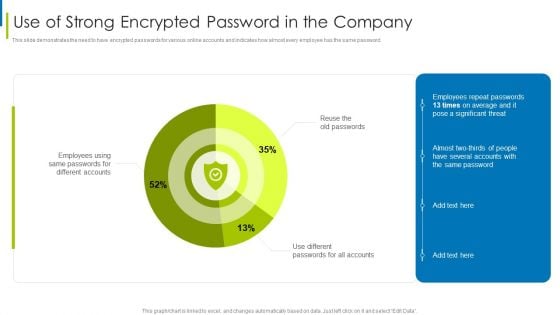
Cyber Terrorism Assault Use Of Strong Encrypted Password In The Company Icons PDF
This slide demonstrates the need to have encrypted passwords for various online accounts and indicates how almost every employee has the same password.Deliver and pitch your topic in the best possible manner with this cyber terrorism assault use of strong encrypted password in the company icons pdf Use them to share invaluable insights on use of strong encrypted password in the company and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
-
Cyber Terrorism Assault What Is Cyber Terrorism Elements PDF
Presenting cyber terrorism assault what is cyber terrorism elements pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like internet in violating, confidential information, political or ideological In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-
Icons Slide For Cyber Terrorism Assault Ideas PDF
Introducing our well designed icons slide for cyber terrorism assault ideas pdf set of slides. The slide displays editable icons to enhance your visual presentation. The icons can be edited easily. So customize according to your business to achieve a creative edge. Download and share it with your audience.
-
Table Of Content Cyber Terrorism Assault Rules Designs PDF
This is a table of content cyber terrorism assault rules designs pdf template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like assessment matrix of cyber terrorism, impact of implementing, dashboard for threat tracking You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
-

Table Of Content Cyber Terrorism Assault Pictures PDF
Presenting table of content cyber terrorism assault pictures pdf to provide visual cues and insights. Share and navigate important information on six stages that need your due attention. This template can be used to pitch topics like elements of cyber terrorism, preventive measures against, tools misused for cyber terrorism . In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
-
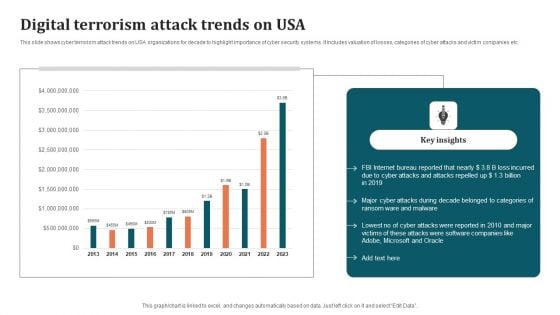
Digital Terrorism Attack Trends On USA Ideas PDF
This slide shows cyber terrorism attack trends on USA organizations for decade to highlight importance of cyber security systems. It includes valuation of losses, categories of cyber attacks and victim companies etc. Showcasing this set of slides titled Digital Terrorism Attack Trends On USA Ideas PDF. The topics addressed in these templates are Key Insights, Internet, Digital Terrorism Attack Trends. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
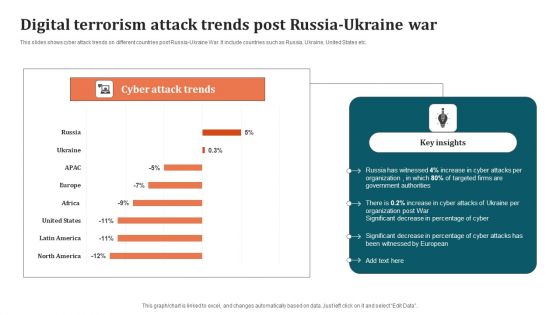
Digital Terrorism Attack Trends Post Russia Ukraine War Graphics PDF
This slides shows cyber attack trends on different countries post Russia-Ukraine War. It include countries such as Russia, Ukraine, United States etc. Pitch your topic with ease and precision using this Digital Terrorism Attack Trends Post Russia Ukraine War Graphics PDF. This layout presents information on Organization, Digital Terrorism Attack Trends. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
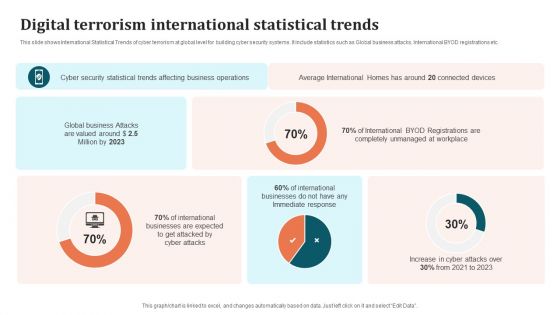
Digital Terrorism International Statistical Trends Brochure PDF
This slide shows International Statistical Trends of cyber terrorism at global level for building cyber security systems. It include statistics such as Global business attacks, International BYOD registrations etc. Showcasing this set of slides titled Digital Terrorism International Statistical Trends Brochure PDF. The topics addressed in these templates are International Businesses, Cyber Security Statistical Trends, Business Operations. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-

Country Wise Security Strategies For Digital Terrorism Professional PDF
This slide shows various strategies adopted by different countries to eliminate threat of cyber attacks. It include various risk area covered such as Hostile cyber attacks, International Cyber Attacks etc. Presenting Country Wise Security Strategies For Digital Terrorism Professional PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including National Strategy, Cyber Security, International Cyber. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-

Digital Terrorism Risk Identification Icon Professional PDF
Presenting Digital Terrorism Risk Identification Icon Professional PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Digital Terrorism Risk, Identification Icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
Digital Terrorism Threat Attacking Network Icon Brochure PDF
Presenting Digital Terrorism Threat Attacking Network Icon Brochure PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Digital Terrorism Threat Attacking, Network Icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
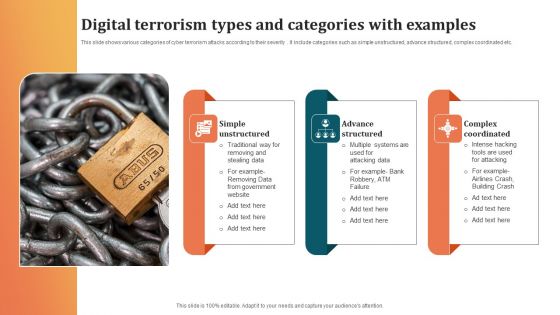
Digital Terrorism Types And Categories With Examples Sample PDF
This slide shows various categories of cyber terrorism attacks according to their severity . It include categories such as simple unstructured, advance structured, complex coordinated etc. Showcasing this set of slides titled Digital Terrorism Types And Categories With Examples Sample PDF. The topics addressed in these templates are Advance Structured, Complex Coordinated, Simple Unstructured. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
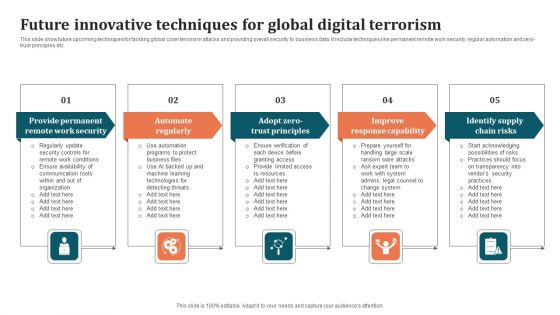
Future Innovative Techniques For Global Digital Terrorism Background PDF
This slide show future upcoming techniques for tackling global cyber terrorism attacks and providing overall security to business data. It include techniques like permanent remote work security, regular automation and zero-trust principles etc. Persuade your audience using this Future Innovative Techniques For Global Digital Terrorism Background PDF. This PPT design covers five stages, thus making it a great tool to use. It also caters to a variety of topics including Improve Response Capability, Identify Supply Chain Risks, Automate Regularly. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-

Global Strategic Objectives For Tackling Digital Terrorism Structure PDF
This slide shows global level objectives to protect and promote digital business activities with transparency. It include objectives such as developing global level cyber crime system, building resilient system etc. Presenting Global Strategic Objectives For Tackling Digital Terrorism Structure PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Develop Cyber Crime System, Global, Economic. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
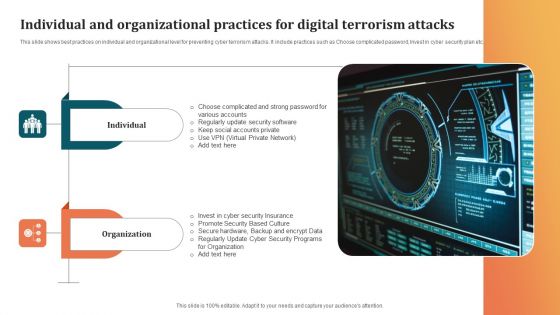
Individual And Organizational Practices For Digital Terrorism Attacks Microsoft PDF
This slide shows best practices on individual and organizational level for preventing cyber terrorism attacks. It include practices such as Choose complicated password, Invest in cyber security plan etc. Pitch your topic with ease and precision using this Individual And Organizational Practices For Digital Terrorism Attacks Microsoft PDF. This layout presents information on Organization, Promote Security, Security Insurance. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
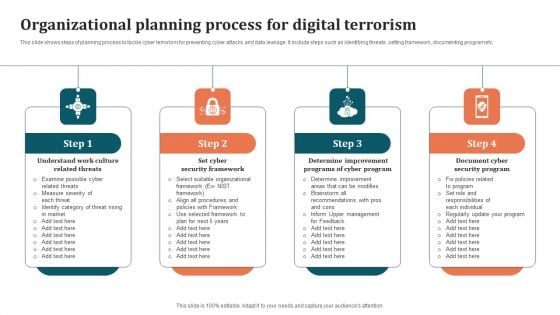
Organizational Planning Process For Digital Terrorism Graphics PDF
This slide shows steps of planning process to tackle cyber terrorism for preventing cyber attacks and data leakage. It include steps such as identifying threats, setting framework, documenting program etc. Presenting Organizational Planning Process For Digital Terrorism Graphics PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Cyber Program, Determine Improvement Programs, Document Cyber Security Program. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-

Program Aligning Phases For Digital Terrorism Infographics PDF
This slide shows three phases for aligning governance with cyber security program to prevent data hacks. It include phases such as understanding basics, planning phase, aligning phase etc. Persuade your audience using this Program Aligning Phases For Digital Terrorism Infographics PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Planning Phase, Aligning Phase, Understand Basics. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
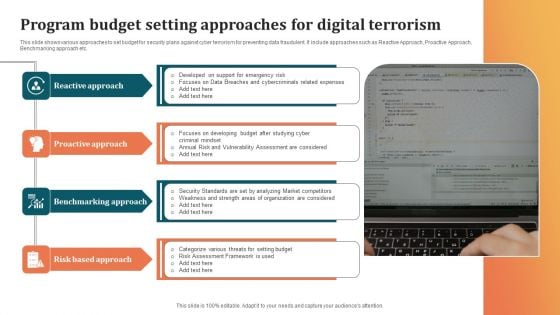
Program Budget Setting Approaches For Digital Terrorism Background PDF
This slide shows various approaches to set budget for security plans against cyber terrorism for preventing data fraudulent. It include approaches such as Reactive Approach, Proactive Approach, Benchmarking approach etc. Presenting Program Budget Setting Approaches For Digital Terrorism Background PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Benchmarking Approach, Risk Based Approach, Proactive Approach. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-

Security Techniques For Digital Terrorism Icon Elements PDF
Persuade your audience using this Security Techniques For Digital Terrorism Icon Elements PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Digital Terrorism Icon, Security Techniques. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
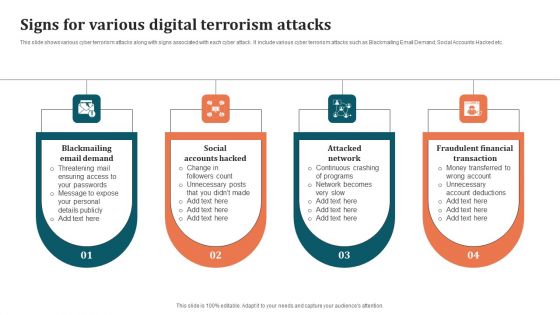
Signs For Various Digital Terrorism Attacks Brochure PDF
This slide shows various cyber terrorism attacks along with signs associated with each cyber attack. It include various cyber terrorism attacks such as Blackmailing Email Demand, Social Accounts Hacked etc. Presenting Signs For Various Digital Terrorism Attacks Brochure PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Attacked Network, Fraudulent Financial Transaction, Social Accounts Hacked. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
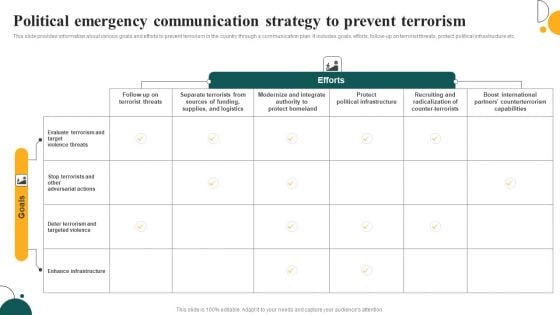
Political Emergency Communication Strategy To Prevent Terrorism Brochure PDF
This slide provides information about various goals and efforts to prevent terrorism in the country through a communication plan. It includes goals, efforts, follow-up on terrorist threats, protect political infrastructure etc. Pitch your topic with ease and precision using this Political Emergency Communication Strategy To Prevent Terrorism Brochure PDF. This layout presents information on Protect Homeland, Protect Political Infrastructure, Targeted Violence. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
Nightmares Night Terrors In Powerpoint And Google Slides Cpb
Presenting our innovatively designed set of slides titled Nightmares Night Terrors In Powerpoint And Google Slides Cpb. This completely editable PowerPoint graphic exhibits Nightmares Night Terrors that will help you convey the message impactfully. It can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. Apart from this, you can download this well structured PowerPoint template design in different formats like PDF, JPG, and PNG. So, click the download button now to gain full access to this PPT design.
-
Terror Management Theory In Powerpoint And Google Slides Cpb
Presenting our innovatively designed set of slides titled Terror Management Theory In Powerpoint And Google Slides Cpb This completely editable PowerPoint graphic exhibits Terror Management Theory that will help you convey the message impactfully. It can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. Apart from this, you can download this well structured PowerPoint template design in different formats like PDF, JPG, and PNG. So, click the download button now to gain full access to this PPT design.



