Vulnerability PowerPoint Presentation Templates and Google Slides
-

Secops Dashboard To Track Vulnerabilities Clipart PDF
This slide provides information regarding the SecOps dashboard which is used to track and monitor various vulnerabilities identified. Deliver an awe inspiring pitch with this creative secops dashboard to track vulnerabilities clipart pdf bundle. Topics like assets, vulnerabilities, unmapped, vulnerabilities by severity, minimal can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
-
Corporate Vulnerability Analysis Ppt PowerPoint Presentation Complete Deck With Slides
If designing a presentation takes a lot of your time and resources and you are looking for a better alternative, then this Corporate Vulnerability Analysis Ppt PowerPoint Presentation Complete Deck With Slides is the right fit for you. This is a prefabricated set that can help you deliver a great presentation on the topic. All the thirteen slides included in this sample template can be used to present a birds-eye view of the topic. These slides are also fully editable, giving you enough freedom to add specific details to make this layout more suited to your business setting. Apart from the content, all other elements like color, design, theme are also replaceable and editable. This helps in designing a variety of presentations with a single layout. Not only this, you can use this PPT design in formats like PDF, PNG, and JPG once downloaded. Therefore, without any further ado, download and utilize this sample presentation as per your liking.
-
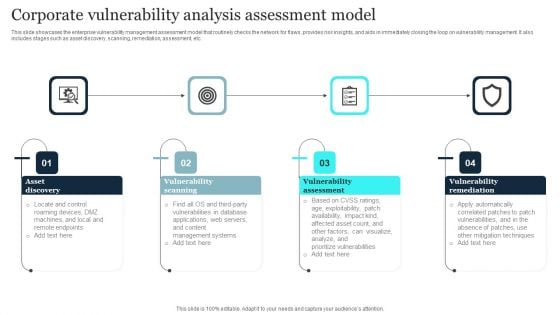
Corporate Vulnerability Analysis Assessment Model Elements PDF
This slide showcases the enterprise vulnerability management assessment model that routinely checks the network for flaws, provides risk insights, and aids in immediately closing the loop on vulnerability management. It also includes stages such as asset discovery, scanning, remediation, assessment, etc. Presenting Corporate Vulnerability Analysis Assessment Model Elements PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Vulnerability Assessment, Vulnerability Scanning, Asset Discovery. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-

Corporate Vulnerability Analysis In Business Icon Designs PDF
Showcasing this set of slides titled Corporate Vulnerability Analysis In Business Icon Designs PDF. The topics addressed in these templates are Corporate Vulnerability Analysis, Business Icon. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
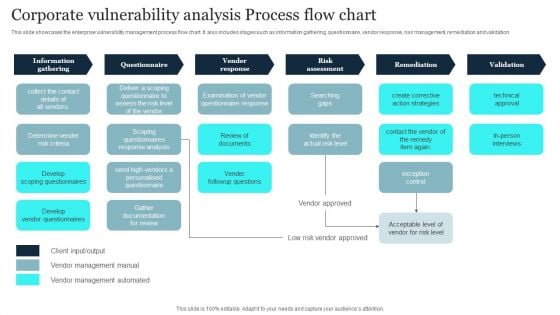
Corporate Vulnerability Analysis Process Flow Chart Summary PDF
This slide showcases the enterprise vulnerability management process flow chart. It also includes stages such as information gathering, questionnaire, vendor response, risk management, remediation and validation. Pitch your topic with ease and precision using this Corporate Vulnerability Analysis Process Flow Chart Summary PDF. This layout presents information on Vender Response, Risk Assessment, Information Gathering. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-

Corporate Vulnerability Analysis Team Icon Clipart PDF
Showcasing this set of slides titled Corporate Vulnerability Analysis Team Icon Clipart PDF. The topics addressed in these templates are Corporate Vulnerability, Analysis Team Icon. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
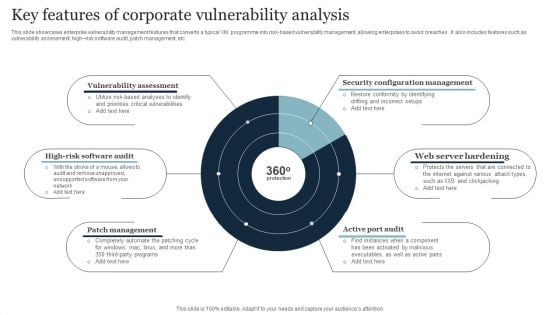
Key Features Of Corporate Vulnerability Analysis Inspiration PDF
This slide showcases enterprise vulnerability management features that converts a typical VM programme into risk-based vulnerability management, allowing enterprises to avoid breaches . It also includes features such as vulnerability assessment, high risk software audit, patch management, etc. Presenting Key Features Of Corporate Vulnerability Analysis Inspiration PDF to dispense important information. This template comprises six stages. It also presents valuable insights into the topics including Security Configuration Management, Web Server Hardening, Active Port Audit. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-

Open Source Corporate Vulnerability Analysis Software Tools Demonstration PDF
This slide showcases open source enterprise vulnerability management software tools that aids companies in securing their networks by locating and repairing flaws. It also includes descriptions regarding tools such as triviy, metasploit, openscap, etc. Persuade your audience using this Open Source Corporate Vulnerability Analysis Software Tools Demonstration PDF. This PPT design covers one stages, thus making it a great tool to use. It also caters to a variety of topics including Environment, Secure Web Applications, Industrial. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
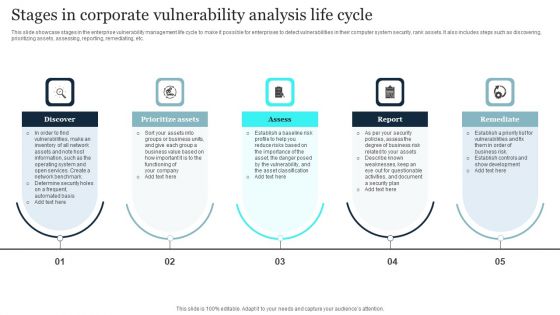
Stages In Corporate Vulnerability Analysis Life Cycle Slides PDF
This slide showcase stages in the enterprise vulnerability management life cycle to make it possible for enterprises to detect vulnerabilities in their computer system security, rank assets. It also includes steps such as discovering, prioritizing assets, assessing, reporting, remediating, etc. Presenting Stages In Corporate Vulnerability Analysis Life Cycle Slides PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Prioritize Assets, Report, Remediate, Assess. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
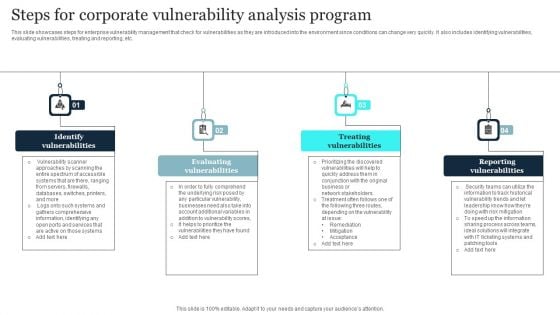
Steps For Corporate Vulnerability Analysis Program Background PDF
This slide showcases steps for enterprise vulnerability management that check for vulnerabilities as they are introduced into the environment since conditions can change very quickly. It also includes identifying vulnerabilities, evaluating vulnerabilities, treating and reporting, etc. Persuade your audience using this Steps For Corporate Vulnerability Analysis Program Background PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Treating Vulnerabilities, Reporting Vulnerabilities, Evaluating Vulnerabilities. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
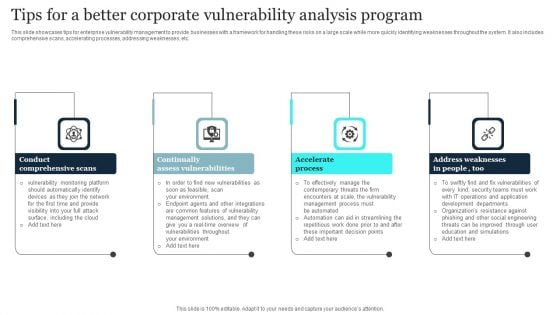
Tips For A Better Corporate Vulnerability Analysis Program Mockup PDF
This slide showcases tips for enterprise vulnerability management to provide businesses with a framework for handling these risks on a large scale while more quickly identifying weaknesses throughout the system. It also includes comprehensive scans, accelerating processes, addressing weaknesses, etc. Presenting Tips For A Better Corporate Vulnerability Analysis Program Mockup PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Continually Assess Vulnerabilities, Conduct Comprehensive Scan, Accelerate Process. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-
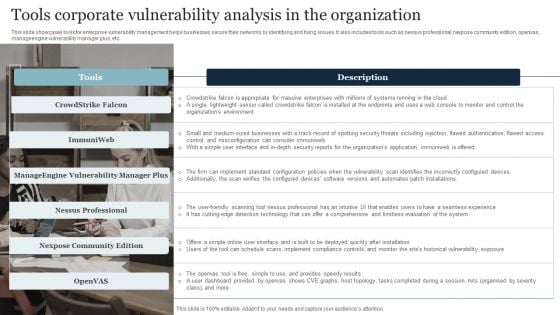
Tools Corporate Vulnerability Analysis In The Organization Guidelines PDF
This slide showcases tools for enterprise vulnerability management helps businesses secure their networks by identifying and fixing issues. It also includes tools such as nessus professional,nexpose community edition, openvas, manageengine vulnerability manager plus, etc. Persuade your audience using this Tools Corporate Vulnerability Analysis In The Organization Guidelines PDF. This PPT design covers one stages, thus making it a great tool to use. It also caters to a variety of topics including Organizations Environment, Limitless Evaluation, Implement. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
-
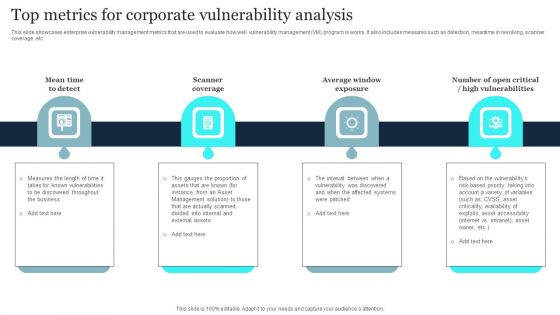
Top Metrics For Corporate Vulnerability Analysis Diagrams PDF
This slide showcases enterprise vulnerability management metrics that are used to evaluate how well vulnerability management VM program is works. It also includes measures such as detection, meantime in resolving, scanner coverage, etc. Presenting Top Metrics For Corporate Vulnerability Analysis Diagrams PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Scanner Coverage, Average Window Exposure, High Vulnerabilities. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
-

Cybersecurity Operations Cybersecops Vulnerabilities Tracking Dashboard For Secops Introduction PDF
This slide represents the vulnerabilities tracking dashboard for SecOps. The purpose of this slide is to demonstrate the tracking of vulnerabilities of an organizations assets, services with the most vulnerabilities, mean time to remediate, and the average age of vulnerabilities. This modern and well arranged Cybersecurity Operations Cybersecops Vulnerabilities Tracking Dashboard For Secops Introduction PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.
-

Conducting Vulnerability Comprehensive Guide To Blockchain Digital Security Mockup Pdf
The following slide showcases blockchain cybersecurity vulnerability assessment framework to optimize resilience and transparency. It includes key elements such as identify, protect, respond, recover, etc. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Conducting Vulnerability Comprehensive Guide To Blockchain Digital Security Mockup Pdf for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
-
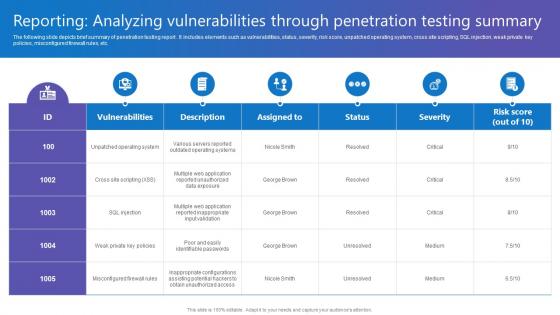
Reporting Analyzing Vulnerabilities Comprehensive Guide To Blockchain Digital Security Inspiration Pdf
The following slide depicts brief summary of penetration testing report . It includes elements such as vulnerabilities, status, severity, risk score, unpatched operating system, cross site scripting, SQL injection, weak private key policies, misconfigured firewall rules, etc. Do you know about Slidesgeeks Reporting Analyzing Vulnerabilities Comprehensive Guide To Blockchain Digital Security Inspiration Pdf These are perfect for delivering any kind od presentation. Using it, create PowerPoint presentations that communicate your ideas and engage audiences. Save time and effort by using our pre designed presentation templates that are perfect for a wide range of topic. Our vast selection of designs covers a range of styles, from creative to business, and are all highly customizable and easy to edit. Download as a PowerPoint template or use them as Google Slides themes.
-

Potential Technologies Deployed To Secure Vulnerable Monitoring Digital Assets Summary Pdf
This slide portrays information regarding potential technologies implemented to secure vulnerable systems. The systems include communication systems, bridge systems, access control system, core infrastructure system, etc. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Potential Technologies Deployed To Secure Vulnerable Monitoring Digital Assets Summary Pdf will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.
-
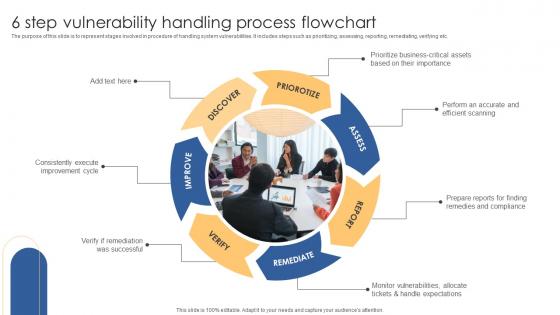
6 Step Vulnerability Handling Process Flowchart Download Pdf
The purpose of this slide is to represent stages involved in procedure of handling system vulnerabilities. It includes steps such as prioritizing, assessing, reporting, remediating, verifying etc. Showcasing this set of slides titled 6 Step Vulnerability Handling Process Flowchart Download Pdf. The topics addressed in these templates are Priorotize, Assess, Discover. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Database Vulnerability Handling Process Flowchart Icon Guidelines Pdf
Pitch your topic with ease and precision using this Database Vulnerability Handling Process Flowchart Icon Guidelines Pdf. This layout presents information on Database Vulnerability, Handling Process Flowchart Icon. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-

Decision Making Process Flow For Vulnerability Management Portrait Pdf
The purpose of this slide is to represent decision making flow chart to handle vulnerabilities. It includes various steps such as identifying vulnerability, verifying vulnerability, determining possibility to remediate, applying remediation etc. Showcasing this set of slides titled Decision Making Process Flow For Vulnerability Management Portrait Pdf. The topics addressed in these templates are Identify Vulnerability, Verify Vulnerability, Apply Remediation. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
Information System Vulnerability Handling Process Flowchart Icon Designs Pdf
Pitch your topic with ease and precision using this Information System Vulnerability Handling Process Flowchart Icon Designs Pdf. This layout presents information on Information System Vulnerability, Handling Process Flowchart Icon. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
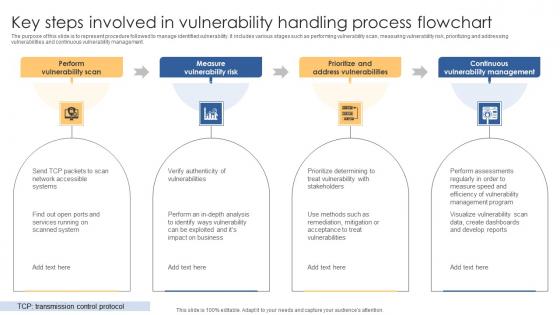
Key Steps Involved In Vulnerability Handling Process Flowchart Summary Pdf
The purpose of this slide is to represent procedure followed to manage identified vulnerability. It includes various stages such as performing vulnerability scan, measuring vulnerability risk, prioritizing and addressing vulnerabilities and continuous vulnerability management. Showcasing this set of slides titled Key Steps Involved In Vulnerability Handling Process Flowchart Summary Pdf. The topics addressed in these templates are Perform Vulnerability Scan, Measure Vulnerability Risk, Prioritize Address Vulnerabilities. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
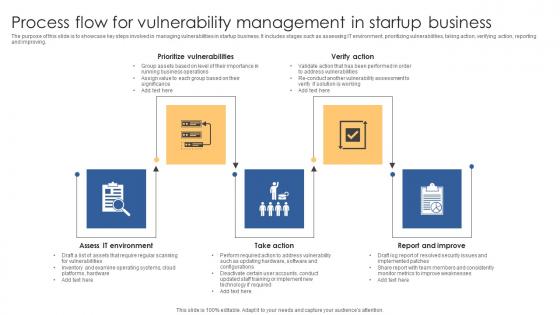
Process Flow For Vulnerability Management In Startup Business Background Pdf
The purpose of this slide is to showcase key steps involved in managing vulnerabilities in startup business. It includes stages such as assessing IT environment, prioritizing vulnerabilities, taking action, verifying action, reporting and improving. Pitch your topic with ease and precision using this Process Flow For Vulnerability Management In Startup Business Background Pdf. This layout presents information on Prioritize Vulnerabilities, Verify Action, Take Action. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
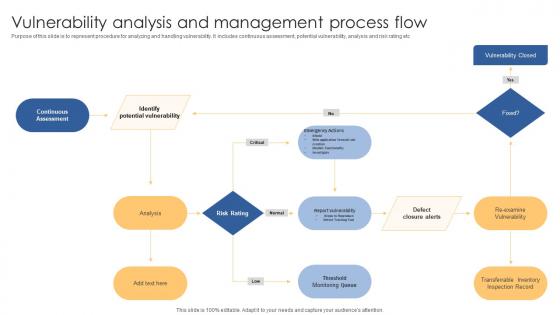
Vulnerability Analysis And Management Process Flow Introduction Pdf
Purpose of this slide is to represent procedure for analyzing and handling vulnerability. It includes continuous assessment, potential vulnerability, analysis and risk rating etc Showcasing this set of slides titled Vulnerability Analysis And Management Process Flow Introduction Pdf. The topics addressed in these templates are Identify Potential Vulnerability, Analysis, Defect Closure Alerts. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
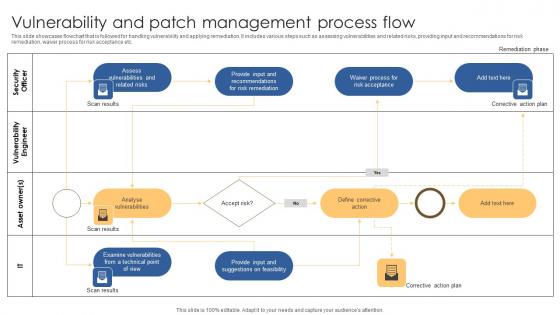
Vulnerability And Patch Management Process Flow Microsoft Pdf
This slide showcases flowchart that is followed for handling vulnerability and applying remediation. It includes various steps such as assessing vulnerabilities and related risks, providing input and recommendations for risk remediation, waiver process for risk acceptance etc. Pitch your topic with ease and precision using this Vulnerability And Patch Management Process Flow Microsoft Pdf. This layout presents information on Security Officer, Vulnerability Engineer, Asset Owner. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-

Vulnerability Handling Process Flowchart For It Organization Download Pdf
This slide represents procedure to handle and resolve vulnerability in an IT company. It includes various stages, such as identifying, evaluating, remediating, verifying, and reporting. Showcasing this set of slides titled Vulnerability Handling Process Flowchart For It Organization Download Pdf. The topics addressed in these templates are Identify, Evaluate, Remediate. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
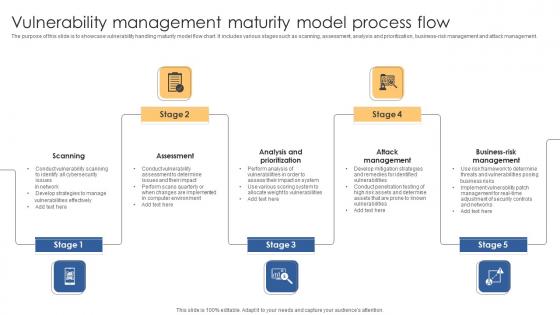
Vulnerability Management Maturity Model Process Flow Microsoft Pdf
The purpose of this slide is to showcase vulnerability handling maturity model flow chart. It includes various stages such as scanning, assessment, analysis and prioritization, business-risk management and attack management. Pitch your topic with ease and precision using this Vulnerability Management Maturity Model Process Flow Microsoft Pdf. This layout presents information on Scanning, Assessment, Analysis Prioritization. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-

Vulnerability Handling Process Flowchart Ppt PowerPoint Presentation Complete Deck With Slides
Improve your presentation delivery using this Vulnerability Handling Process Flowchart Ppt PowerPoint Presentation Complete Deck With Slides. Support your business vision and objectives using this well structured PPT deck. This template offers a great starting point for delivering beautifully designed presentations on the topic of your choice. Comprising twelve this professionally designed template is all you need to host discussion and meetings with collaborators. Each slide is self explanatory and equipped with high quality graphics that can be adjusted to your needs. Therefore, you will face no difficulty in portraying your desired content using this PPT slideshow. This PowerPoint slideshow contains every important element that you need for a great pitch. It is not only editable but also available for immediate download and utilization. The color, font size, background, shapes everything can be modified to create your unique presentation layout. Therefore, download it now.
-

Attack Vulnerability Management In Powerpoint And Google Slides Cpb
Introducing our well designed Attack Vulnerability Management In Powerpoint And Google Slides Cpb. This PowerPoint design presents information on topics like Attack Vulnerability Management. As it is predesigned it helps boost your confidence level. It also makes you a better presenter because of its high quality content and graphics. This PPT layout can be downloaded and used in different formats like PDF, PNG, and JPG. Not only this, it is available in both Standard Screen and Widescreen aspect ratios for your convenience. Therefore, click on the download button now to persuade and impress your audience.
-

Types Of Website Security Threats And Vulnerabilities Step By Step Guide Structure PDF
Following slide exhibits types of security threats that negatively affect website operational efficiency and goodwill. It include types such as malware, viruses, spam links, DDoS with examples, impact and mitigation tools. There are so many reasons you need a Types Of Website Security Threats And Vulnerabilities Step By Step Guide Structure PDF. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
-

Vulnerability Reporting Tool In Powerpoint And Google Slides Cpb
Presenting our innovatively-designed set of slides titled Vulnerability Reporting Tool In Powerpoint And Google Slides Cpb. This completely editable PowerPoint graphic exhibits Vulnerability Reporting Tool that will help you convey the message impactfully. It can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. Apart from this, you can download this well-structured PowerPoint template design in different formats like PDF, JPG, and PNG. So, click the download button now to gain full access to this PPT design.
-
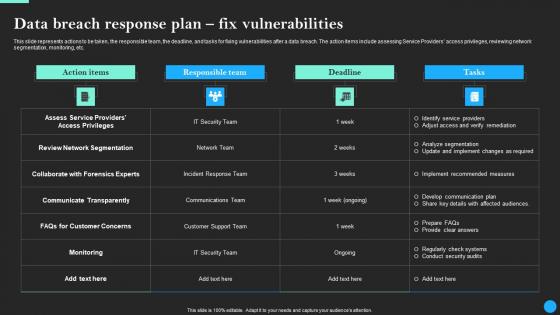
Data Breach Response Plan Fix Vulnerabilities Data Breach Prevention Information Pdf
This slide represents actions to be taken, the responsible team, the deadline, and tasks for fixing vulnerabilities after a data breach. The action items include assessing Service Providers access privileges, reviewing network segmentation, monitoring, etc. This modern and well-arranged Data Breach Response Plan Fix Vulnerabilities Data Breach Prevention Information Pdf provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint, no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.
-
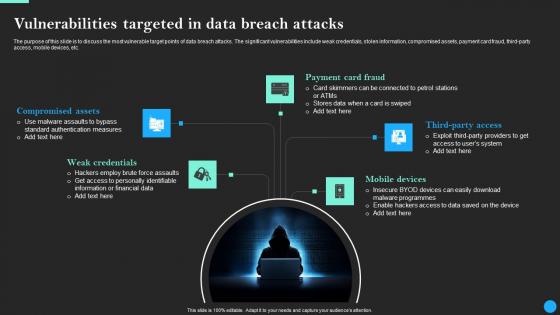
Vulnerabilities Targeted In Data Breach Attacks Data Breach Prevention Inspiration Pdf
Slidegeeks is here to make your presentations a breeze with Vulnerabilities Targeted In Data Breach Attacks Data Breach Prevention Inspiration Pdf With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first
-

Minimizing Customer Transaction Vulnerabilities Ppt Powerpoint Presentation Complete Deck With Slides
This Minimizing Customer Transaction Vulnerabilities Ppt Powerpoint Presentation Complete Deck With Slides is meant for audiences who need a new vision and mission to bring energy back to their enterprise. The eighteen slides in the complete deck complement the spirit of risk taking and investment that the adventure of business requires. There is also scope for ample customization,which is a hallmark of a good presentation. Improvise on the presentations or even while you make your point before you esteemed audience. There is no better way to win new clients in business than a passionate presentation we have the raw material,what is stopping you from giving your best. Download now and showcase your business potential to the world.
-
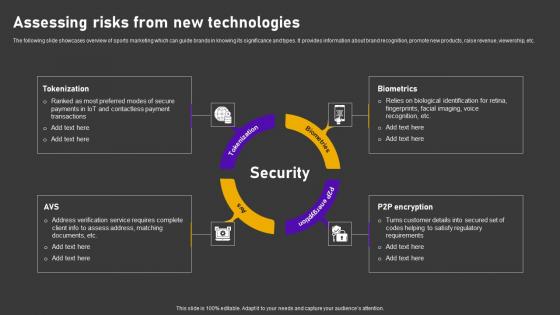
Assessing Risks From New Minimizing Customer Transaction Vulnerabilities Professional Pdf
The following slide showcases overview of sports marketing which can guide brands in knowing its significance and types. It provides information about brand recognition, promote new products, raise revenue, viewership, etc. The best PPT templates are a great way to save time, energy, and resources. Slidegeeks have 100 percent editable powerpoint slides making them incredibly versatile. With these quality presentation templates, you can create a captivating and memorable presentation by combining visually appealing slides and effectively communicating your message. Download Assessing Risks From New Minimizing Customer Transaction Vulnerabilities Professional Pdf from Slidegeeks and deliver a wonderful presentation.
-
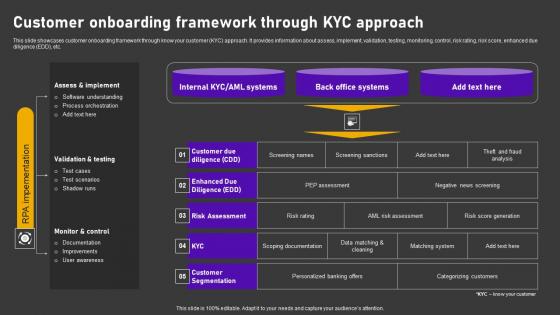
Customer Onboarding Framework Minimizing Customer Transaction Vulnerabilities Summary Pdf
This slide showcases customer onboarding framework through know your customer KYC approach. It provides information about assess, implement, validation, testing, monitoring, control, risk rating, risk score, enhanced due diligence EDD, etc. The Customer Onboarding Framework Minimizing Customer Transaction Vulnerabilities Summary Pdf is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression.
-
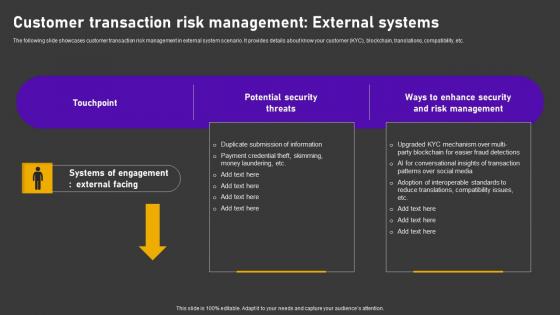
Customer Transaction Risk Management Minimizing Customer Transaction Vulnerabilities Clipart Pdf
The following slide showcases customer transaction risk management in external system scenario. It provides details about know your customer KYC, blockchain, translations, compatibility, etc. Are you searching for a Customer Transaction Risk Management Minimizing Customer Transaction Vulnerabilities Clipart Pdf that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Customer Transaction Risk Management Minimizing Customer Transaction Vulnerabilities Clipart Pdf from Slidegeeks today.
-
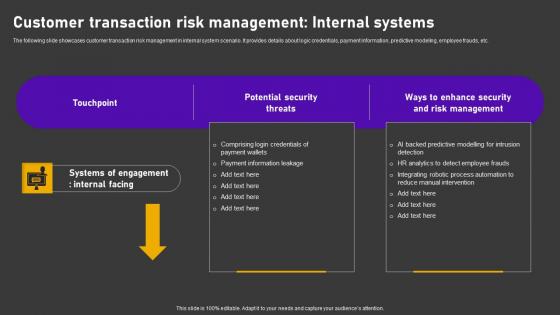
Customer Transaction Risk Minimizing Customer Transaction Vulnerabilities Designs Pdf
The following slide showcases customer transaction risk management in internal system scenario. It provides details about logic credentials, payment information, predictive modeling, employee frauds, etc. Retrieve professionally designed Customer Transaction Risk Minimizing Customer Transaction Vulnerabilities Designs Pdf to effectively convey your message and captivate your listeners. Save time by selecting pre made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.
-
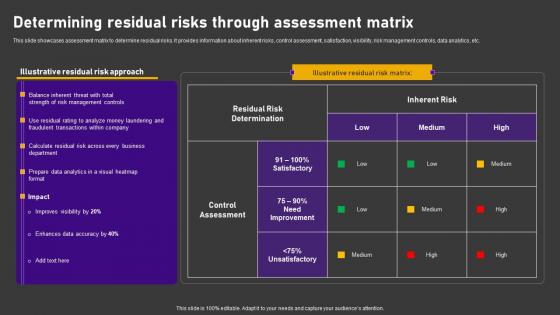
Determining Residual Risks Through Minimizing Customer Transaction Vulnerabilities Slides Pdf
This slide showcases assessment matrix to determine residual risks. It provides information about inherent risks, control assessment, satisfaction, visibility, risk management controls, data analytics, etc. Slidegeeks has constructed Determining Residual Risks Through Minimizing Customer Transaction Vulnerabilities Slides Pdf after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping off point to explore our content and will give new users an insight into our top notch PowerPoint Templates.
-

Identifying Inherent Risk Factors Minimizing Customer Transaction Vulnerabilities Portrait Pdf
This slide showcases identifying inherent risk factors and measures. It provides information about customer base, products, services, delivery channels, jurisdictions, qualitative factors, location, customer risk rating, transparency, fund transfer, etc. Presenting this PowerPoint presentation, titled Identifying Inherent Risk Factors Minimizing Customer Transaction Vulnerabilities Portrait Pdf, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Identifying Inherent Risk Factors Minimizing Customer Transaction Vulnerabilities Portrait Pdf. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Identifying Inherent Risk Factors Minimizing Customer Transaction Vulnerabilities Portrait Pdf that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.
-
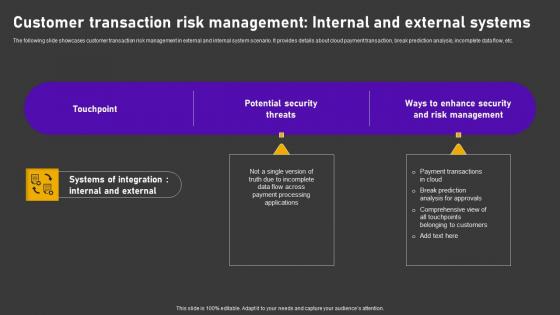
Minimizing Customer Transaction Vulnerabilities Customer Transaction Risk Management Clipart Pdf
The following slide showcases customer transaction risk management in external and internal system scenario. It provides details about cloud payment transaction, break prediction analysis, incomplete data flow, etc. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye catching visual experience. Download Minimizing Customer Transaction Vulnerabilities Customer Transaction Risk Management Clipart Pdf to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high quality content for you. Later on, you can personalize the content by editing the Minimizing Customer Transaction Vulnerabilities Customer Transaction Risk Management Clipart Pdf.
-
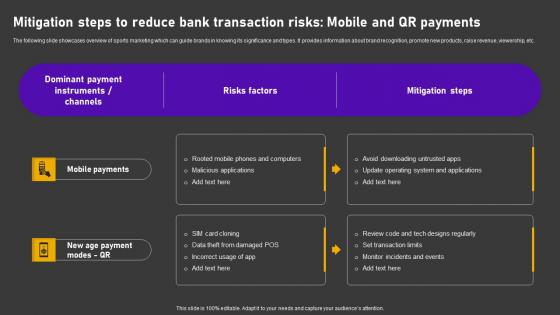
Minimizing Customer Transaction Vulnerabilities Mitigation Steps To Reduce Bank Download Pdf
The following slide showcases overview of sports marketing which can guide brands in knowing its significance and types. It provides information about brand recognition, promote new products, raise revenue, viewership, etc. Do you know about Slidesgeeks Minimizing Customer Transaction Vulnerabilities Mitigation Steps To Reduce Bank Download Pdf These are perfect for delivering any kind od presentation. Using it, create PowerPoint presentations that communicate your ideas and engage audiences. Save time and effort by using our pre designed presentation templates that are perfect for a wide range of topic. Our vast selection of designs covers a range of styles, from creative to business, and are all highly customizable and easy to edit. Download as a PowerPoint template or use them as Google Slides themes.
-

Mitigating Transaction Risks Minimizing Customer Transaction Vulnerabilities Infographics Pdf
This slide illustrates mitigating transaction risks through policies and procedures. It provides information about due diligence, transaction monitoring, screening, customer identification, data analysis, investigation, review, etc. Find a pre designed and impeccable Mitigating Transaction Risks Minimizing Customer Transaction Vulnerabilities Infographics Pdf. The templates can ace your presentation without additional effort. You can download these easy to edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
-
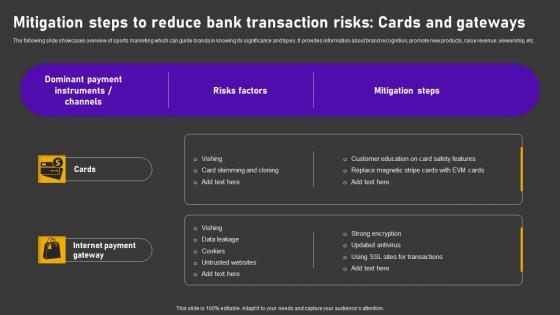
Mitigation Steps Reduce Bank Minimizing Customer Transaction Vulnerabilities Microsoft Pdf
The following slide showcases overview of sports marketing which can guide brands in knowing its significance and types. It provides information about brand recognition, promote new products, raise revenue, viewership, etc. Boost your pitch with our creative Mitigation Steps Reduce Bank Minimizing Customer Transaction Vulnerabilities Microsoft Pdf. Deliver an awe inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
-
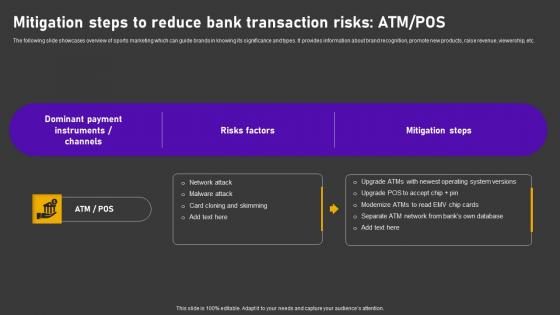
Mitigation Steps To Reduce Bank Minimizing Customer Transaction Vulnerabilities Inspiration Pdf
The following slide showcases overview of sports marketing which can guide brands in knowing its significance and types. It provides information about brand recognition, promote new products, raise revenue, viewership, etc. Create an editable Mitigation Steps To Reduce Bank Minimizing Customer Transaction Vulnerabilities Inspiration Pdf that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre designed presentation templates help save time. Mitigation Steps To Reduce Bank Minimizing Customer Transaction Vulnerabilities Inspiration Pdf is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
-

Omnichannel Payment Solution Minimizing Customer Transaction Vulnerabilities Professional Pdf
The following slide showcases omni channel payment solution to mitigate risks. It provides details about unwavering controls, configurable workflows, virtual cards, managed services, industry standards, etc. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Omnichannel Payment Solution Minimizing Customer Transaction Vulnerabilities Professional Pdf for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
-
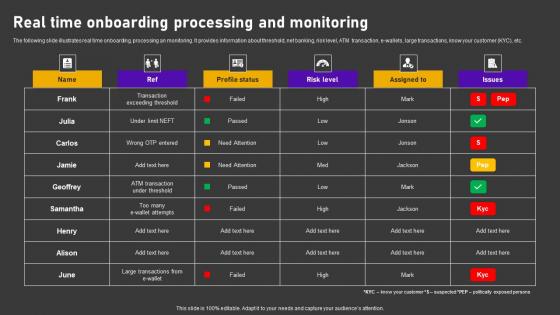
Real Time Onboarding Processing Minimizing Customer Transaction Vulnerabilities Inspiration Pdf
The following slide illustrates real time onboarding, processing an monitoring. It provides information about threshold, net banking, risk level, ATM transaction, e wallets, large transactions, know your customer KYC, etc. Want to ace your presentation in front of a live audience Our Real Time Onboarding Processing Minimizing Customer Transaction Vulnerabilities Inspiration Pdf can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy to edit and downloadable. Use these for both personal and commercial use.
-
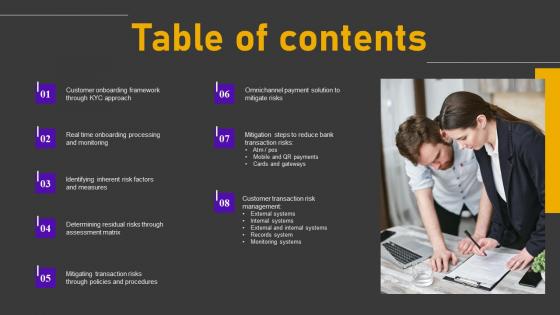
Table Of Contents Minimizing Customer Transaction Vulnerabilities Mockup Pdf
There are so many reasons you need a Table Of Contents Minimizing Customer Transaction Vulnerabilities Mockup Pdf. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
-
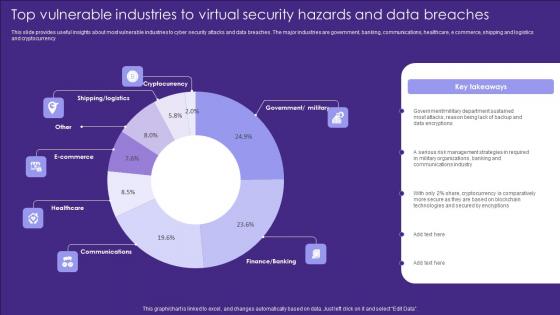
Top Vulnerable Industries To Virtual Security Hazards And Data Breaches Introduction Pdf
This slide provides useful insights about most vulnerable industries to cyber security attacks and data breaches. The major industries are government, banking, communications, healthcare, e commerce, shipping and logistics and cryptocurrency Pitch your topic with ease and precision using this Top Vulnerable Industries To Virtual Security Hazards And Data Breaches Introduction Pdf. This layout presents information on Cryptocurrency, Ecommerce, Healthcare. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
-
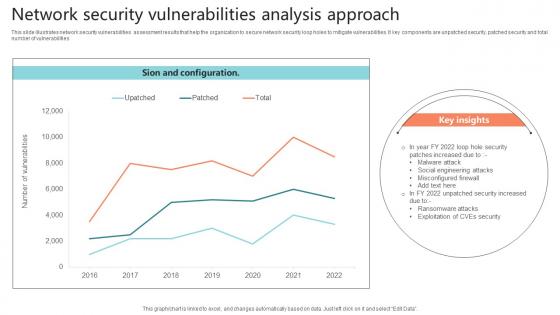
Network Security Vulnerabilities Analysis Approach Sample Pdf
This slide illustrates network security vulnerabilities assessment results that help the organization to secure network security loop holes to mitigate vulnerabilities. It key components are unpatched security, patched security and total number of vulnerabilities.Showcasing this set of slides titled Network Security Vulnerabilities Analysis Approach Sample Pdf The topics addressed in these templates are Misconfigured Firewall, Malware Attack, Social Engineering Attacks All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-

Steps To Perform Vulnerability Analysis For Network Security Pictures Pdf
This slide showcase vulnerability assessment process that help organization to identify security vulnerabilities in network system and prioritize them to plan mitigation action plan. It includes steps such as identifying, scanning, identify type of scan, configure scan etc.Showcasing this set of slides titled Steps To Perform Vulnerability Analysis For Network Security Pictures Pdf The topics addressed in these templates are Evaluate Possible Risk, Interpret Scan Results, Create Mitigation Plan All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-

Food Adulteration Prevention Strategy Development To Remove Vulnerability Designs Pdf
This slide provide information about procedure to formulate food fraud mitigation plan to remove vulnerability. It includes elements such as pre-screening, vulnerability assessment, impact assessment, overall risk assessment etc. Showcasing this set of slides titled Food Adulteration Prevention Strategy Development To Remove Vulnerability Designs Pdf. The topics addressed in these templates are Vulnerability Assessment, Risk Assessment, Control Plan. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-

Food Adulteration Vulnerability Assessment With Prevention Strategy Formats Pdf
This slide illustrate food fraud vulnerability assessment mitigation plan to remove frauds occurring in food industry. It includes elements such as mitigation plan, potential vulnerability, mention trade mark etc. Showcasing this set of slides titled Food Adulteration Vulnerability Assessment With Prevention Strategy Formats Pdf. The topics addressed in these templates are Strategy, Food, Vulnerability. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-
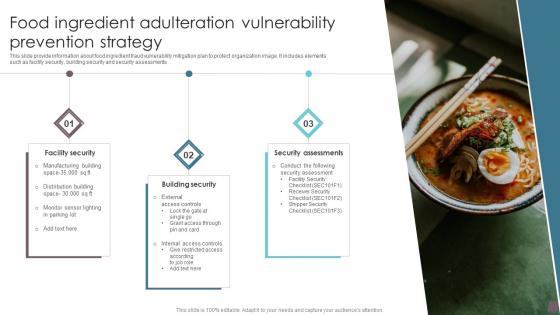
Food Ingredient Adulteration Vulnerability Prevention Strategy Information Pdf
This slide provide information about food ingredient fraud vulnerability mitigation plan to protect organization image. It includes elements such as facility security, building security and security assessments Showcasing this set of slides titled Food Ingredient Adulteration Vulnerability Prevention Strategy Information Pdf. The topics addressed in these templates are Security Assessments, Building Security, Facility Security. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
-

Nessus Vulnerability Report In Powerpoint And Google Slides Cpb
Introducing our well designed Nessus Vulnerability Report In Powerpoint And Google Slides Cpb. This PowerPoint design presents information on topics like Nessus Vulnerability Report. As it is predesigned it helps boost your confidence level. It also makes you a better presenter because of its high quality content and graphics. This PPT layout can be downloaded and used in different formats like PDF, PNG, and JPG. Not only this, it is available in both Standard Screen and Widescreen aspect ratios for your convenience. Therefore, click on the download button now to persuade and impress your audience.



