System Security

Key Statistics Of Customer Brand Loyalty Program Ppt PowerPoint Presentation File Background Image PDF
The purpose of this slide is to outline major statistics of customer loyalty program. The statistics is related to customer emotions such as interest, trust, optimism, admiration, acceptance, joy, security etc. Showcasing this set of slides titled key statistics of customer brand loyalty program ppt powerpoint presentation file background image pdf. The topics addressed in these templates are top ten emotions, customers for brand connection, top ten emotions by gender. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
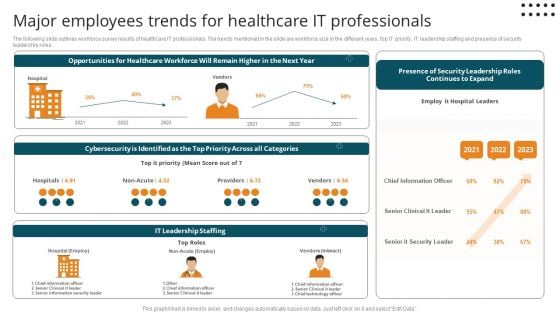
Major Employees Trends For Healthcare It Professionals Diagrams PDF
The following slide outlines workforce survey results of healthcare IT professionals. The trends mentioned in the slide are workforce size in the different years, top IT priority, IT leadership staffing and presence of security leadership roles.Pitch your topic with ease and precision using this Major Employees Trends For Healthcare It Professionals Diagrams PDF. This layout presents information on Cybersecurity Identified, Chief Information, Senior Clinical. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
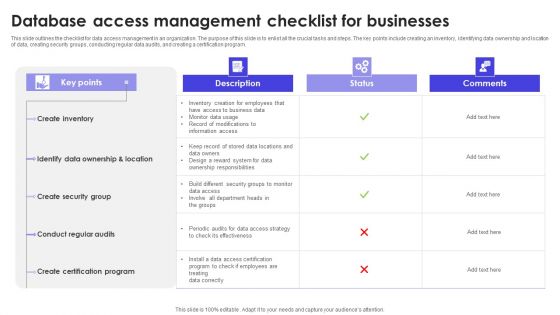
Database Access Management Checklist For Businesses Formats PDF
This slide outlines the checklist for data access management in an organization. The purpose of this slide is to enlist all the crucial tasks and steps. The key points include creating an inventory, identifying data ownership and location of data, creating security groups, conducting regular data audits, and creating a certification program. Showcasing this set of slides titled Database Access Management Checklist For Businesses Formats PDF. The topics addressed in these templates are Description, Status, Comments. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
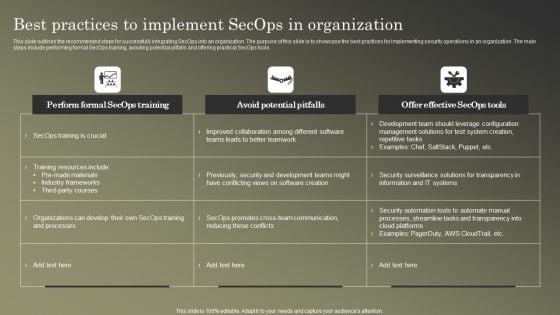
Cybersecurity Operations Cybersecops Best Practices To Implement Secops Information PDF
This slide outlines the recommended steps for successfully integrating SecOps into an organization. The purpose of this slide is to showcase the best practices for implementing security operations in an organization. The main steps include performing formal SecOps training, avoiding potential pitfalls and offering practical SecOps tools. Make sure to capture your audiences attention in your business displays with our gratis customizable Cybersecurity Operations Cybersecops Best Practices To Implement Secops Information PDF. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.

Implementation Of Digital Advancement Techniques Essential Personnel Required Pictures PDF
The following slide outlines key personnel required to develop digital transformation team for converting insurer traditional to technology based. Team consists of members which are technologists, security and compliance specialists, business technology liaisons, project managers, financial stakeholders, marketers, implementation leads and evangelists. There are so many reasons you need a Implementation Of Digital Advancement Techniques Essential Personnel Required Pictures PDF. The first reason is you cannot spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
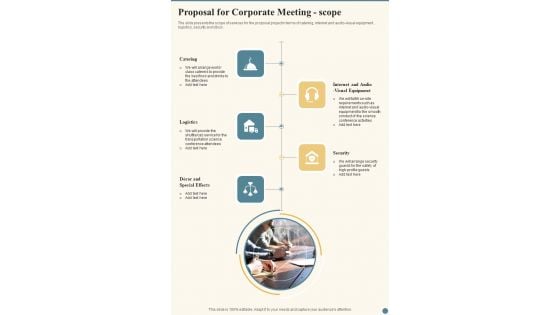
Proposal For Corporate Meeting Scope One Pager Sample Example Document
The slide presents the scope of services for the proposal project in terms of catering, internet and audio visual equipment , logistics, security and decor. Presenting you an exemplary Proposal For Corporate Meeting Scope One Pager Sample Example Document. Our one pager comprises all the must have essentials of an inclusive document. You can edit it with ease, as its layout is completely editable. With such freedom, you can tweak its design and other elements to your requirements. Download this Proposal For Corporate Meeting Scope One Pager Sample Example Document brilliant piece now.

Scope For Scientific Conference One Pager Sample Example Document
The slide presents the scope of services for the proposal project in terms of catering, internet and audio-visual equipment, logistics, security and decor. Presenting you an exemplary Scope For Scientific Conference One Pager Sample Example Document. Our one-pager comprises all the must-have essentials of an inclusive document. You can edit it with ease, as its layout is completely editable. With such freedom, you can tweak its design and other elements to your requirements. Download this Scope For Scientific Conference One Pager Sample Example Document brilliant piece now.
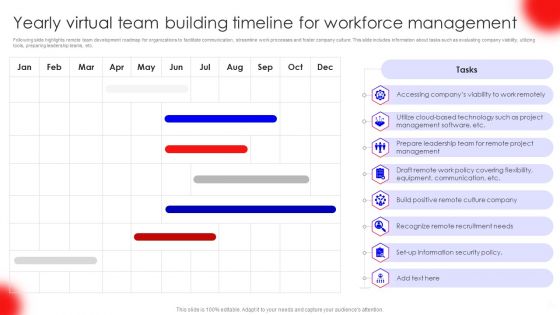
Yearly Virtual Team Building Timeline For Workforce Management Download PDF
Following slide highlights remote team development roadmap for organizations to facilitate communication, streamline work processes and foster company culture. This slide includes information about tasks such as evaluating company viability, utilizing tools, preparing leadership teams, etc. Showcasing this set of slides titled Yearly Virtual Team Building Timeline For Workforce Management Download PDF. The topics addressed in these templates are Communication, Security Policy, Management, Cloud Based Technology. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
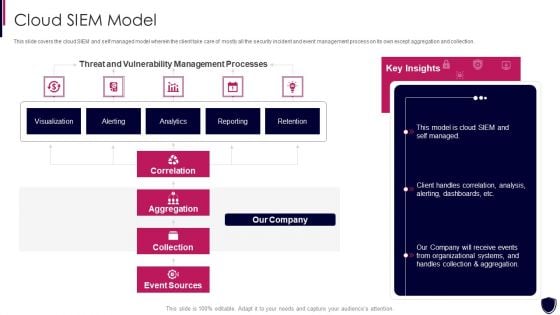
Enhancing Cyber Safety With Vulnerability Administration Cloud SIEM Model Clipart PDF
This slide covers the cloud SIEM and self managed model wherein the client take care of mostly all the security incident and event management process on its own except aggregation and collection. Deliver and pitch your topic in the best possible manner with this enhancing cyber safety with vulnerability administration cloud siem model clipart pdf. Use them to share invaluable insights on correlation, aggregation, collection, event sources, our company and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
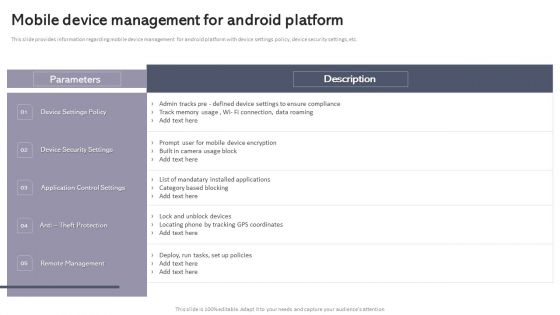
Workplace Portable Device Monitoring And Administration Mobile Device Management For Android Platform Slides PDF
This slide provides information regarding mobile device management for android platform with device settings policy, device security settings, etc. The Workplace Portable Device Monitoring And Administration Mobile Device Management For Android Platform Slides PDF is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression.

Income And Expenses Sheet Of Different Properties One Pager Documents
This page provides the income and expenses sheets of different properties of owner. It also provides financials such as gross income, total expenses, net income, security deposit etc. Presenting you a fantastic Income And Expenses Sheet Of Different Properties One Pager Documents. This piece is crafted on hours of research and professional design efforts to ensure you have the best resource. It is completely editable and its design allow you to rehash its elements to suit your needs. Get this Income And Expenses Sheet Of Different Properties One Pager Documents A4 One-pager now.

Next Step For Post Real Estate Cleaning Proposal One Pager Sample Example Document
The following slide displays the next step that the organization has to take once the security proposal has been signed, these steps can be teem meeting ,on-site visit etc. Presenting you an exemplary Next Step For Post Real Estate Cleaning Proposal One Pager Sample Example Document. Our one-pager comprises all the must-have essentials of an inclusive document. You can edit it with ease, as its layout is completely editable. With such freedom, you can tweak its design and other elements to your requirements. Download this Next Step For Post Real Estate Cleaning Proposal One Pager Sample Example Document brilliant piece now.

Proposal For Installing Radio Frequency Identification Next Step One Pager Sample Example Document
The following slide displays the next step that the organization has to take once the security proposal has been signed, these steps can be tem meeting ,on-site visit etc. Presenting you an exemplary Proposal For Installing Radio Frequency Identification Next Step One Pager Sample Example Document. Our one-pager comprises all the must-have essentials of an inclusive document. You can edit it with ease, as its layout is completely editable. With such freedom, you can tweak its design and other elements to your requirements. Download this Proposal For Installing Radio Frequency Identification Next Step One Pager Sample Example Document brilliant piece now.

IT Consultancy Services Company Profile Client Reviews And Testimonials Ideas PDF
This slides focuses on client testimonials post using our products and services which helps to build credibility and reliability to business and helps in decision making process. Presenting IT Consultancy Services Company Profile Client Reviews And Testimonials Ideas PDF to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like Excellent Data, Security Services, Software Services. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
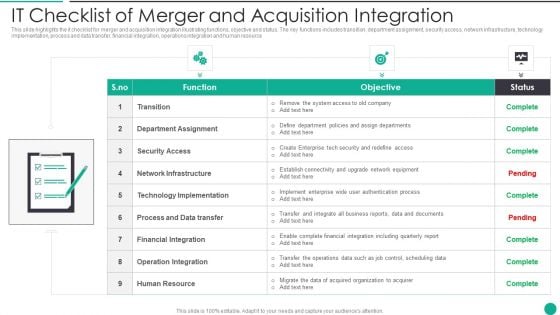
IT Checklist Of Merger And Acquisition Integration Designs PDF
This slide highlights the it checklist for merger and acquisition integration illustrating functions, objective and status. The key functions includes transition, department assignment, security access, network infrastructure, technology implementation, process and data transfer, financial integration, operations integration and human resource Presenting IT Checklist Of Merger And Acquisition Integration Designs PDF to dispense important information. This template comprises one stage. It also presents valuable insights into the topics including Department Assignment, Financial Integration, Operation Integration This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
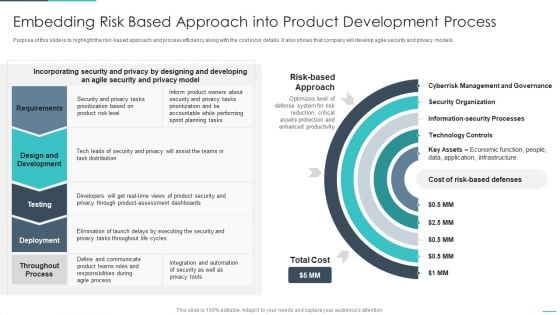
Handling Cyber Threats Digital Era Embedding Risk Based Approach Into Product Ppt Gallery Designs PDF
Purpose of this slide is to highlight the risk-based approach and process efficiency along with the cost incur details. It also shows that company will develop agile security and privacy models. Deliver an awe inspiring pitch with this creative handling cyber threats digital era embedding risk based approach into product ppt gallery designs pdf bundle. Topics like embedding risk based approach into product development process can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
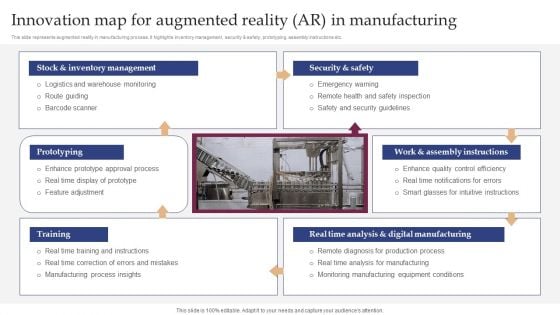
Innovation Map For Augmented Reality AR In Manufacturing Inspiration PDF
This slide represents augmented reality in manufacturing process. It highlights inventory management, security and safety, prototyping, assembly instructions etc. The best PPT templates are a great way to save time, energy, and resources. Slidegeeks have 100 peracent editable powerpoint slides making them incredibly versatile. With these quality presentation templates, you can create a captivating and memorable presentation by combining visually appealing slides and effectively communicating your message. Download Innovation Map For Augmented Reality AR In Manufacturing Inspiration PD from Slidegeeks and deliver a wonderful presentation.
Applications Of AI In Banking Industry Icons PDF
This slide signifies the smart manufacturing key threats and solutions to overcome. It covers information about challenges like safety in human robot collaboration, security issue and skill development with strategies implemented to overcome them Pitch your topic with ease and precision using this Applications Of AI In Banking Industry Icons PDF. This layout presents information on Experience, Banking, Process. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
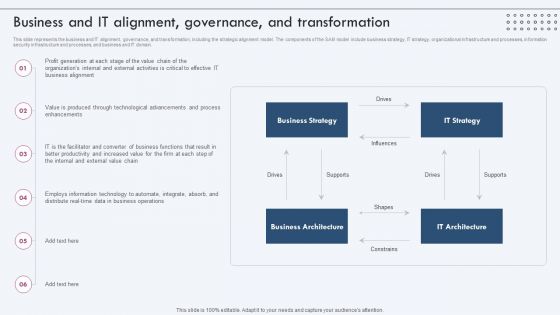
Business And IT Alignment Governance And Transformation Inspiration PDF
This slide represents the business and IT alignment, governance, and transformation, including the strategic alignment model. The components of the SAM model include business strategy, IT strategy, organizational infrastructure and processes, information security infrastructure and processes, and business and IT domain. Find a pre designed and impeccable Business And IT Alignment Governance And Transformation Inspiration PDF. The templates can ace your presentation without additional effort. You can download these easy to edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
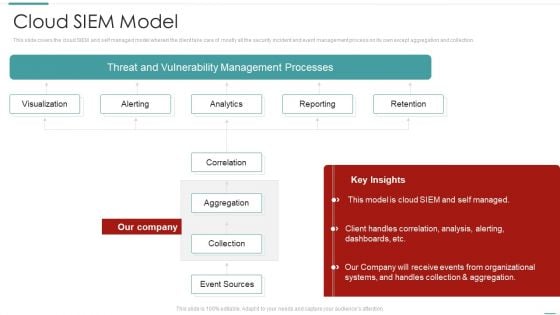
Risk Recognition Automation Cloud Siem Model Ppt Layouts Templates PDF
This slide covers the cloud SIEM and self managed model wherein the client take care of mostly all the security incident and event management process on its own except aggregation and collection. Deliver and pitch your topic in the best possible manner with this risk recognition automation cloud siem model ppt layouts templates pdf. Use them to share invaluable insights on visualization, alerting, analytics, reporting, retention and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
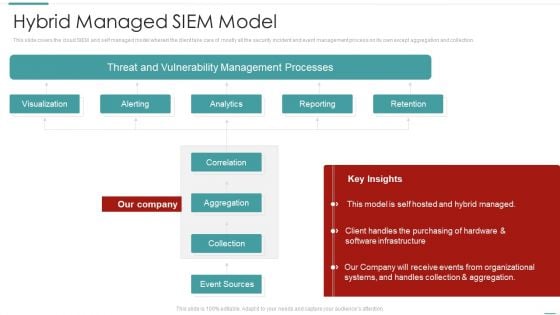
Risk Recognition Automation Hybrid Managed Siem Model Ppt Show Themes PDF
This slide covers the cloud SIEM and self managed model wherein the client take care of mostly all the security incident and event management process on its own except aggregation and collection. Deliver and pitch your topic in the best possible manner with this risk recognition automation hybrid managed siem model ppt show themes pdf. Use them to share invaluable insights on visualization, alerting, analytics, reporting, retention and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Convergence Strategy Information Launch Of Cyber IT OT Strategy Ppt Summary Portrait PDF
This slide covers IT or OT cyber security strategy and approaches such as raining of an internal employee in cybersecurity, from the OT side, to keep the near job relation to OT Teams etc. This is a Convergence Strategy Information Launch Of Cyber IT OT Strategy Ppt Summary Portrait PDF template with various stages. Focus and dispense information on nine stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Audit Demanded, Enable Collaboration, Industrialize Process. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
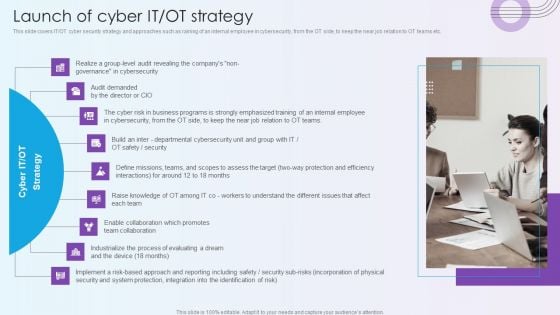
Digitalization Of Operative Enterprises Launch Of Cyber IT OT Strategy Themes PDF
This slide covers IT or OT cyber security strategy and approaches such as raining of an internal employee in cybersecurity, from the OT side, to keep the near job relation to OT teams etc. Presenting Digitalization Of Operative Enterprises Launch Of Cyber IT OT Strategy Themes PDF to provide visual cues and insights. Share and navigate important information on nine stages that need your due attention. This template can be used to pitch topics like Cybersecurity, Cyber Risk, Process Of Evaluating. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
Smart Venture Digitial Transformation Launch Of Cyber IT OT Strategy Ppt Icon Slides PDF
This slide covers IT or OT cyber security strategy and approaches such as raining of an internal employee in cybersecurity, from the OT side, to keep the near job relation to OT Teams etc. This is a Smart Venture Digitial Transformation Launch Of Cyber IT OT Strategy Ppt Icon Slides PDF template with various stages. Focus and dispense information on nine stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like OT Strategy, Cyber IT, Process Evaluating. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
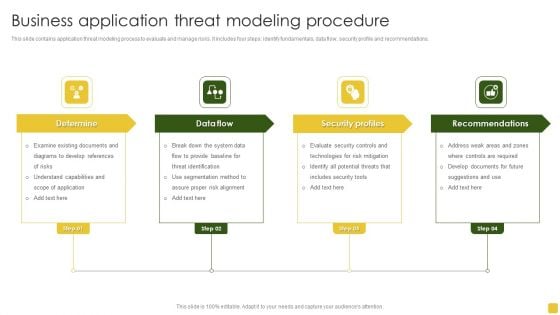
Business Application Threat Modeling Procedure Designs PDF
This slide contains application threat modeling process to evaluate and manage risks. It includes four steps identify fundamentals, data flow, security profile and recommendations. Persuade your audience using this Business Application Threat Modeling Procedure Designs PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Examine Existing, Understand Capabilities, Recommendations. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
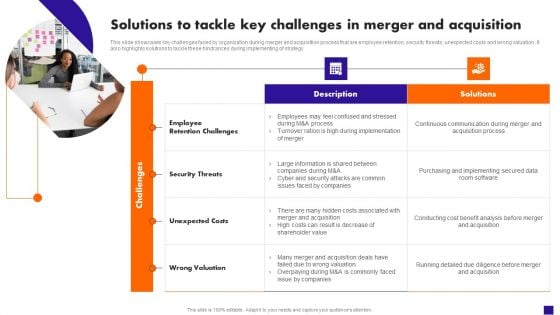
Solutions To Tackle Key Challenges In Merger And Acquisition Portrait PDF
This slide showcases key challenges faced by organization during merger and acquisition process that are employee retention, security threats, unexpected costs and wrong valuation. It also highlights solutions to tackle these hindrances during implementing of strategy. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Solutions To Tackle Key Challenges In Merger And Acquisition Portrait PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.
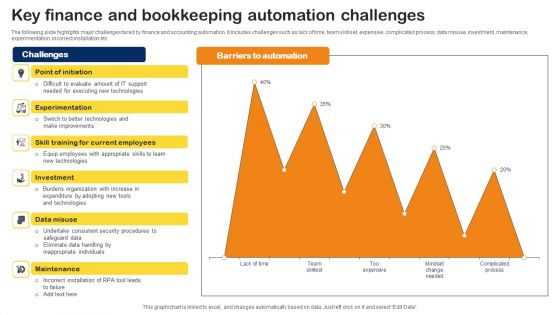
Key Finance And Bookkeeping Automation Challenges Professional PDF
The following slide highlights major challenges faced by finance and accounting automation. It includes challenges such as lack of time, team skillset, expensive, complicated process, data misuse, investment, maintenance, experimentation, incorrect installation etc. Showcasing this set of slides titled Key Finance And Bookkeeping Automation Challenges Professional PDF. The topics addressed in these templates are Burdens Organization, Investment, Consistent Security Procedures. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Cloud Readiness Evaluation Steps For IT Firms Ppt Outline Files Pdf
The slide showcases steps involved in process of determining whether to adopt cloud or third party into firms systems. It contains evaluation of cloud readiness assessment via steps such as identification of scope and business cases for application migration, evaluation of tangible intangible resources, assessment of infrastructure and security requirements, determination of timeline and budget. Pitch your topic with ease and precision using this Cloud Readiness Evaluation Steps For IT Firms Ppt Outline Files Pdf. This layout presents information on Determine Resources, Assign Employees Training, Determine Applications. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout. The slide showcases steps involved in process of determining whether to adopt cloud or third party into firms systems. It contains evaluation of cloud readiness assessment via steps such as identification of scope and business cases for application migration, evaluation of tangible intangible resources, assessment of infrastructure and security requirements, determination of timeline and budget.

Zero Trust Network Access Timeline To Implement Zero Trust Network Access Model
This slide showcases the timeline for implementing the ZTNA security model. This slide highlights the various steps organizations will take while deploying the ZTNA system, forming a dedicated team, choosing zero-trust implementation on-ramp, assessing the environment and so on. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Zero Trust Network Access Timeline To Implement Zero Trust Network Access Model was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Zero Trust Network Access Timeline To Implement Zero Trust Network Access Model This slide showcases the timeline for implementing the ZTNA security model. This slide highlights the various steps organizations will take while deploying the ZTNA system, forming a dedicated team, choosing zero-trust implementation on-ramp, assessing the environment and so on.

Zero Trust Model Timeline To Implement Zero Trust Network Access
This slide showcases the timeline for implementing the ZTNA security model. This slide highlights the various steps organizations will take while deploying the ZTNA system, forming a dedicated team, choosing zero-trust implementation on-ramp, assessing the environment and so on. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Zero Trust Model Timeline To Implement Zero Trust Network Access can be your best option for delivering a presentation. Represent everything in detail using Zero Trust Model Timeline To Implement Zero Trust Network Access and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results. This slide showcases the timeline for implementing the ZTNA security model. This slide highlights the various steps organizations will take while deploying the ZTNA system, forming a dedicated team, choosing zero-trust implementation on-ramp, assessing the environment and so on.
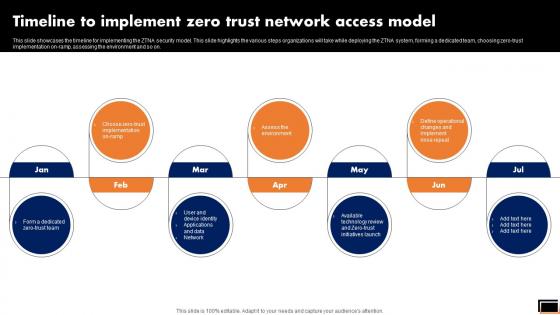
Timeline To Implement Zero Trust Network Access Model Software Defined Perimeter SDP
This slide showcases the timeline for implementing the ZTNA security model. This slide highlights the various steps organizations will take while deploying the ZTNA system, forming a dedicated team, choosing zero-trust implementation on-ramp, assessing the environment and so on. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Timeline To Implement Zero Trust Network Access Model Software Defined Perimeter SDP can be your best option for delivering a presentation. Represent everything in detail using Timeline To Implement Zero Trust Network Access Model Software Defined Perimeter SDP and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results. This slide showcases the timeline for implementing the ZTNA security model. This slide highlights the various steps organizations will take while deploying the ZTNA system, forming a dedicated team, choosing zero-trust implementation on-ramp, assessing the environment and so on.
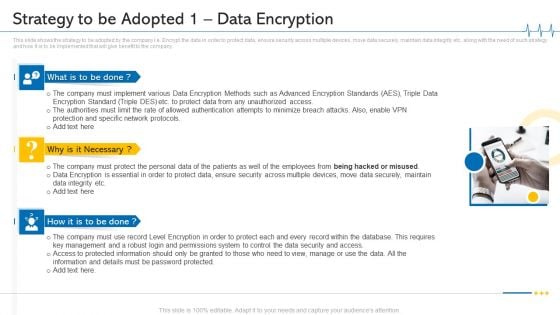
Minimize Cloud Risks Medical Care Business Case Competition Strategy To Be Adopted 1 Data Encryption Microsoft PDF
This slide shows the strategy to be adopted by the company i.e. Encrypt the data in order to protect data, ensure security across multiple devices, move data securely, maintain data integrity etc. along with the need of such strategy and how it is to be implemented that will give benefit to the company. Presenting minimize cloud risks medical care business case competition strategy to be adopted 1 data encryption microsoft pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like Protection And Specific Network Protocols, Protect Data, Permissions System, Key Management. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
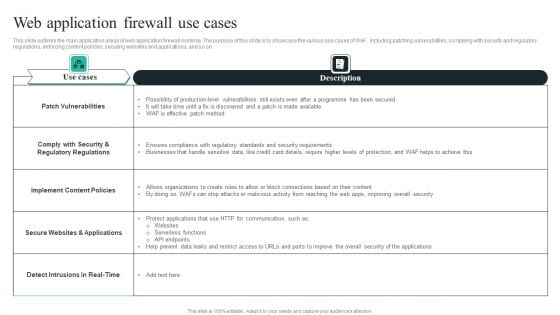
WAF Introduction Web Application Firewall Use Cases Topics PDF
This slide outlines the main application areas of web application firewall systems. The purpose of this slide is to showcase the various use cases of WAF, including patching vulnerabilities, complying with security and regulatory regulations, enforcing content policies, securing websites and applications, and so on. Presenting this PowerPoint presentation, titledWAF Introduction Web Application Firewall Use Cases Topics PDF, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting thisWAF Introduction Web Application Firewall Use Cases Topics PDF. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizableWAF Introduction Web Application Firewall Use Cases Topics PDF that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.

Global Strategic Objectives For Tackling Digital Terrorism Structure PDF
This slide shows global level objectives to protect and promote digital business activities with transparency. It include objectives such as developing global level cyber crime system, building resilient system etc. Presenting Global Strategic Objectives For Tackling Digital Terrorism Structure PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Develop Cyber Crime System, Global, Economic. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Computerized Framework For Cloud Management Topics PDF
This slide shows the automation architecture for cloud management which covers cloud portal, orchestration, tracking resources, automated provisioning, control panels, network management systems, etc. Pitch your topic with ease and precision using this computerized framework for cloud management topics pdf. This layout presents information on capacity and system management, configuration and asset management, network management systems. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
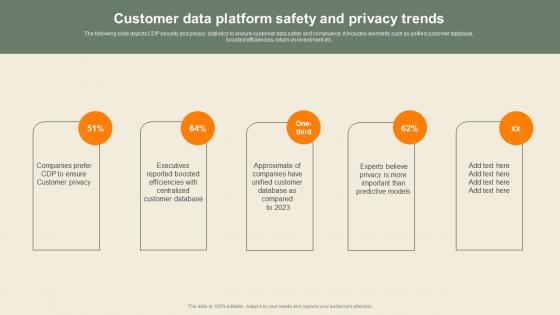
Customer Data Platform Safety And Privacy Usability Of CDP Software Tool Professional Pdf
The following slide depicts CDP security and privacy statistics to ensure customer data safety and compliance. It includes elements such as unified customer database, boosted efficiencies, return on investment etc. If you are looking for a format to display your unique thoughts, then the professionally designed Customer Data Platform Safety And Privacy Usability Of CDP Software Tool Professional Pdf is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Customer Data Platform Safety And Privacy Usability Of CDP Software Tool Professional Pdf and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. The following slide depicts CDP security and privacy statistics to ensure customer data safety and compliance. It includes elements such as unified customer database, boosted efficiencies, return on investment etc.
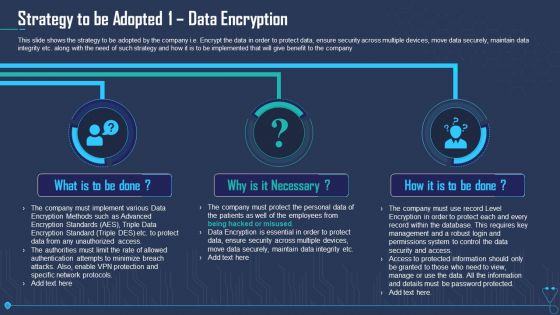
Strategy To Be Adopted 1 Data Encryption Ppt Outline PDF
This slide shows the strategy to be adopted by the company i.e. Encrypt the data in order to protect data, ensure security across multiple devices, move data securely, maintain data integrity etc. along with the need of such strategy and how it is to be implemented that will give benefit to the company. Presenting strategy to be adopted 1 data encryption ppt outline pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like strategy to be adopted 1 data encryption. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Wireless Banking To Improve Two Factor Authentication Process Flow For Enhanced Fin SS V
This slide shows flow chart which can be used to understand how two factor authentication security feature works. It includes steps such as enter username and password, verify biometrics or enter OTP, etc. Are you searching for a Wireless Banking To Improve Two Factor Authentication Process Flow For Enhanced Fin SS V that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Wireless Banking To Improve Two Factor Authentication Process Flow For Enhanced Fin SS V from Slidegeeks today. This slide shows flow chart which can be used to understand how two factor authentication security feature works. It includes steps such as enter username and password, verify biometrics or enter OTP, etc.
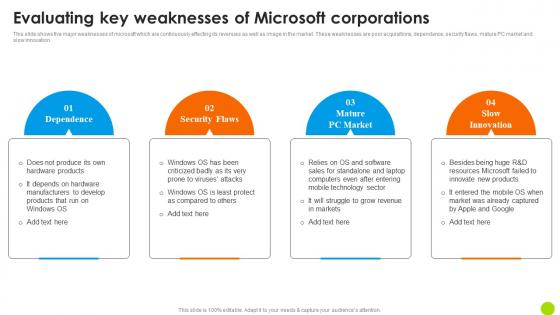
Evaluating Key Weaknesses Of Microsoft Corporations Microsoft Long Term Business Guidelines PDF
This slide shows five major weaknesses of microsoft which are continuously effecting its revenues as well as image in the market. These weaknesses are poor acquisitions, dependance, security flaws, mature PC market and slow innovation. If you are looking for a format to display your unique thoughts, then the professionally designed Evaluating Key Weaknesses Of Microsoft Corporations Microsoft Long Term Business Guidelines PDF is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Evaluating Key Weaknesses Of Microsoft Corporations Microsoft Long Term Business Guidelines PDF and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. This slide shows five major weaknesses of microsoft which are continuously effecting its revenues as well as image in the market. These weaknesses are poor acquisitions, dependance, security flaws, mature PC market and slow innovation.
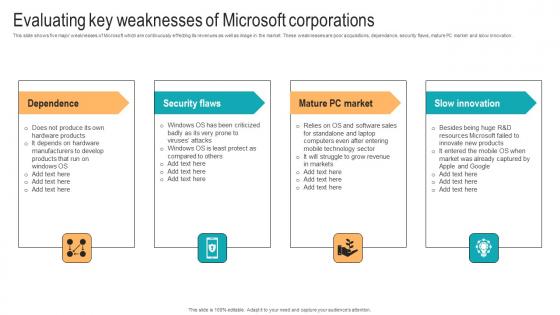
Evaluating Key Weaknesses Of Microsoft Strategic Advancements By Microsofts Microsoft Pdf
This slide shows five major weaknesses of Microsoft which are continuously effecting its revenues as well as image in the market. These weaknesses are poor acquisitions, dependance, security flaws, mature PC market and slow innovation. If you are looking for a format to display your unique thoughts, then the professionally designed Evaluating Key Weaknesses Of Microsoft Strategic Advancements By Microsofts Microsoft Pdf is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Evaluating Key Weaknesses Of Microsoft Strategic Advancements By Microsofts Microsoft Pdf and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. This slide shows five major weaknesses of Microsoft which are continuously effecting its revenues as well as image in the market. These weaknesses are poor acquisitions, dependance, security flaws, mature PC market and slow innovation.

Technologies Used To Protect Data In Confidential Computing Technologies Guidelines Pdf
This slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Present like a pro with Technologies Used To Protect Data In Confidential Computing Technologies Guidelines Pdf Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today. This slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on.
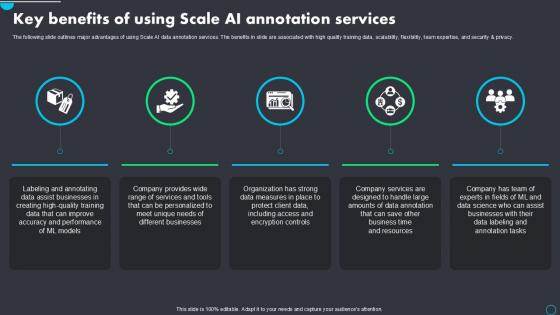
Key Benefits Of Using Implementing Scale AI PPT Presentation AI SS V
The following slide outlines major advantages of using Scale AI data annotation services. The benefits in slide are associated with high quality training data, scalability, flexibility, team expertise, and security and privacy. If you are looking for a format to display your unique thoughts, then the professionally designed Key Benefits Of Using Implementing Scale AI PPT Presentation AI SS V is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Key Benefits Of Using Implementing Scale AI PPT Presentation AI SS V and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. The following slide outlines major advantages of using Scale AI data annotation services. The benefits in slide are associated with high quality training data, scalability, flexibility, team expertise, and security and privacy.
Our Solution Value Based Investor Financing Pitch Deck Demonstration Pdf
The following slide outlines multiple solutions provided by our firm that can overcome problems faced by investors. The slide provides information about services rendered such as investment strategy, asset allocation, risk tolerance, asset and security selection, etc. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Our Solution Value Based Investor Financing Pitch Deck Demonstration Pdf to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation. The following slide outlines multiple solutions provided by our firm that can overcome problems faced by investors. The slide provides information about services rendered such as investment strategy, asset allocation, risk tolerance, asset and security selection, etc.

Major Challenges In Future Development Exploring Investment Opportunities Portrait Pdf
The following slide showcases the major issues in future development of security tokens to boost early stage adoption. It includes elements such as no uniformity, legal protection, regulations, manual processes, valuation, anti-money laundering, etc. Presenting this PowerPoint presentation, titled Major Challenges In Future Development Exploring Investment Opportunities Portrait Pdf, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Major Challenges In Future Development Exploring Investment Opportunities Portrait Pdf. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Major Challenges In Future Development Exploring Investment Opportunities Portrait Pdf that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs. The following slide showcases the major issues in future development of security tokens to boost early stage adoption. It includes elements such as no uniformity, legal protection, regulations, manual processes, valuation, anti-money laundering, etc.
Data Stewardship In Business Processes Uses Of Data Stewardship Program Icons Pdf
This slide represents the uses of a data stewardship program that includes resolving any data or data related challenges, decreasing risks by security measures, improving data documentation, developing and using quality measures, and so on. Explore a selection of the finest Data Stewardship In Business Processes Uses Of Data Stewardship Program Icons Pdf here. With a plethora of professionally designed and pre made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Data Stewardship In Business Processes Uses Of Data Stewardship Program Icons Pdf to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks. This slide represents the uses of a data stewardship program that includes resolving any data or data related challenges, decreasing risks by security measures, improving data documentation, developing and using quality measures, and so on.

Iot Device Update Management Process Iot Device Management Background Pdf
This slide exhibits IoT device management and maintenance process in order to avoid security threats. It includes steps such as analyse IoT fleet, Create backup, Test updates, schedule plan, divide fleet into groups, execute updates, and collect feedback. This Iot Device Update Management Process Iot Device Management Background Pdf from Slidegeeks makes it easy to present information on your topic with precision. It provides customization options, so you can make changes to the colors, design, graphics, or any other component to create a unique layout. It is also available for immediate download, so you can begin using it right away. Slidegeeks has done good research to ensure that you have everything you need to make your presentation stand out. Make a name out there for a brilliant performance. This slide exhibits IoT device management and maintenance process in order to avoid security threats. It includes steps such as analyse IoT fleet, Create backup, Test updates, schedule plan, divide fleet into groups, execute updates, and collect feedback.
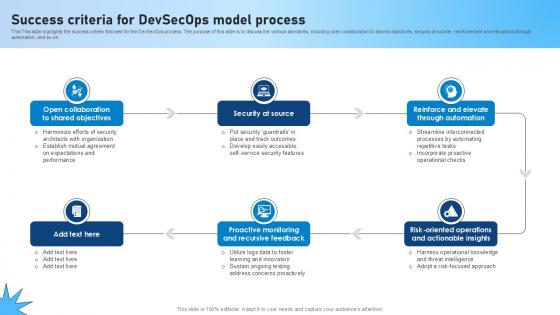
Success Criteria For Devsecops Model Process Role Of Devsecops Ppt Slide
This This slide highlights the success criteria followed for the DevSecOps process. The purpose of this slide is to discuss the various standards, including open collaboration to shared objectives, security at source, reinforcement and elevations through automation, and so on. Present like a pro with Success Criteria For Devsecops Model Process Role Of Devsecops Ppt Slide Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today. This This slide highlights the success criteria followed for the DevSecOps process. The purpose of this slide is to discuss the various standards, including open collaboration to shared objectives, security at source, reinforcement and elevations through automation, and so on.
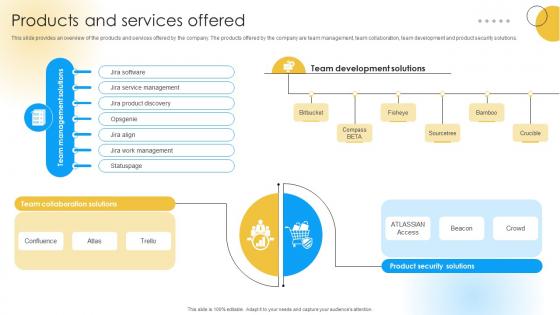
Products And Services Offered Software Development Company Funding Elevator Pitch Deck
This slide provides an overview of the products and services offered by the company. The products offered by the company are team management, team collaboration, team development and product security solutions. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Products And Services Offered Software Development Company Funding Elevator Pitch Deck was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Products And Services Offered Software Development Company Funding Elevator Pitch Deck. This slide provides an overview of the products and services offered by the company. The products offered by the company are team management, team collaboration, team development and product security solutions.
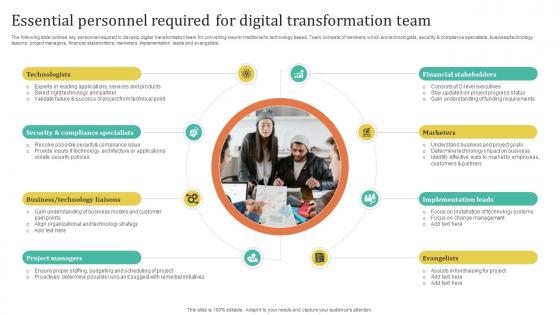
Improving Customer Satisfaction Essential Personnel Required For Digital Transformation
The following slide outlines key personnel required to develop digital transformation team for converting insurer traditional to technology based. Team consists of members which are technologists, security and compliance specialists, business technology liaisons, project managers, financial stakeholders, marketers, implementation leads and evangelists. This Improving Customer Satisfaction Essential Personnel Required For Digital Transformation is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Improving Customer Satisfaction Essential Personnel Required For Digital Transformation features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today The following slide outlines key personnel required to develop digital transformation team for converting insurer traditional to technology based. Team consists of members which are technologists, security and compliance specialists, business technology liaisons, project managers, financial stakeholders, marketers, implementation leads and evangelists.
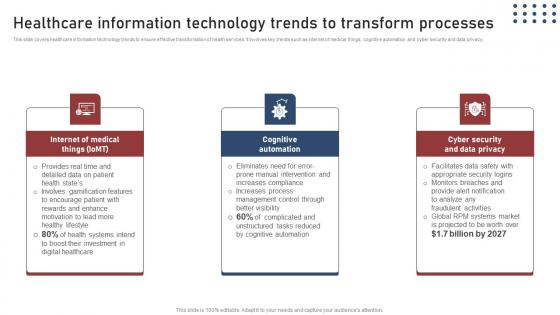
Healthcare Information Transforming Medical Workflows Via His Integration Designs Pdf
This slide covers healthcare information technology trends to ensure effective transformation of health services. It involves key trends such as internet of medical things, cognitive automation and cyber security and data privacy. If you are looking for a format to display your unique thoughts, then the professionally designed Healthcare Information Transforming Medical Workflows Via His Integration Designs Pdf is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Healthcare Information Transforming Medical Workflows Via His Integration Designs Pdf and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. This slide covers healthcare information technology trends to ensure effective transformation of health services. It involves key trends such as internet of medical things, cognitive automation and cyber security and data privacy.
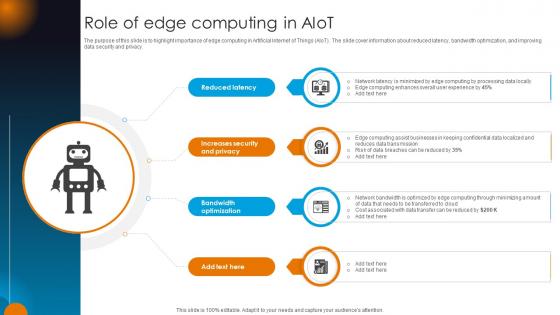
Integrating AI With IoT Role Of Edge Computing In AIoT IoT SS V
The purpose of this slide is to highlight importance of edge computing in Artificial Internet of Things AIoT. The slide cover information about reduced latency, bandwidth optimization, and improving data security and privacy. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Integrating AI With IoT Role Of Edge Computing In AIoT IoT SS V. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Integrating AI With IoT Role Of Edge Computing In AIoT IoT SS V today and make your presentation stand out from the rest The purpose of this slide is to highlight importance of edge computing in Artificial Internet of Things AIoT. The slide cover information about reduced latency, bandwidth optimization, and improving data security and privacy.
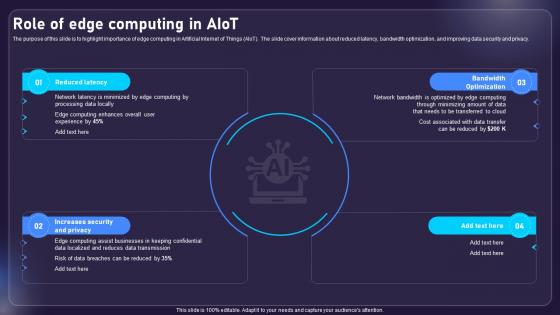
Role Of Edge Computing In AIOT Applications For Various Industries IoT SS V
The purpose of this slide is to highlight importance of edge computing in Artificial Internet of Things AIoT. The slide cover information about reduced latency, bandwidth optimization, and improving data security and privacy. Find highly impressive Role Of Edge Computing In AIOT Applications For Various Industries IoT SS V on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Role Of Edge Computing In AIOT Applications For Various Industries IoT SS V for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now The purpose of this slide is to highlight importance of edge computing in Artificial Internet of Things AIoT. The slide cover information about reduced latency, bandwidth optimization, and improving data security and privacy.

Terms And Clauses In Venture Capital Deal Investor Raising Venture Capital A Holistic Approach Fin SS V
This section discusses the provisions in venture capital deals that are designed to protect the interests and investments of venture capitalists, ensuring a level of security for their capital. The rights of investors include anti-dilution rights, preemptive rights, etc. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Terms And Clauses In Venture Capital Deal Investor Raising Venture Capital A Holistic Approach Fin SS V was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Terms And Clauses In Venture Capital Deal Investor Raising Venture Capital A Holistic Approach Fin SS V This section discusses the provisions in venture capital deals that are designed to protect the interests and investments of venture capitalists, ensuring a level of security for their capital. The rights of investors include anti-dilution rights, preemptive rights, etc.

Cyber Strategies For KPMG For Client Data Protection Pictures PDF
This slide covers techniques to secure customers confidential data through several cyber security strategies. The purpose for this template is to provide an overview on important elements of top techniques deployed by the company . It includes strategies such as people, process, data and technology and regulatory. Boost your pitch with our creative Cyber Strategies For KPMG For Client Data Protection Pictures PDF. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.

IoT Device Management Fundamentals IoT Device Provisioning Overview With Best Practices IoT Ss V
This slide includes an IoT device provisioning overview with best practices to successfully enroll device on network. It includes best practices such as plan for data storage, automate device provisioning, and set suitable security measures. Whether you have daily or monthly meetings, a brilliant presentation is necessary. IoT Device Management Fundamentals IoT Device Provisioning Overview With Best Practices IoT SS V can be your best option for delivering a presentation. Represent everything in detail using IoT Device Management Fundamentals IoT Device Provisioning Overview With Best Practices IoT SS V and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results. This slide includes an IoT device provisioning overview with best practices to successfully enroll device on network. It includes best practices such as plan for data storage, automate device provisioning, and set suitable security measures.
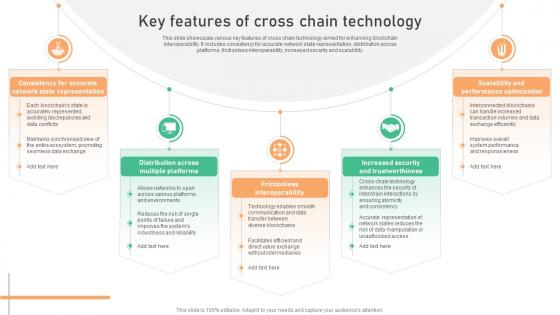
Seamless Integration The Power Key Features Of Cross Chain Technology BCT SS V
This slide showcases various key features of cross chain technology aimed for enhancing blockchain interoperability. It includes consistency for accurate network state representation, distribution across platforms, frictionless interoperability, increased security and scalability. Are you searching for a Seamless Integration The Power Key Features Of Cross Chain Technology BCT SS V that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Seamless Integration The Power Key Features Of Cross Chain Technology BCT SS V from Slidegeeks today. This slide showcases various key features of cross chain technology aimed for enhancing blockchain interoperability. It includes consistency for accurate network state representation, distribution across platforms, frictionless interoperability, increased security and scalability.
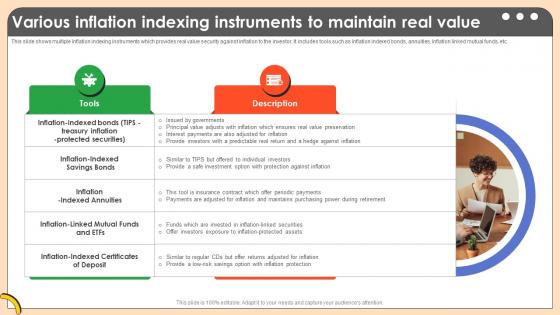
Various Inflation Indexing Instruments To Comprehensive Guide On Inflation Control CM SS V
This slide shows multiple inflation indexing instruments which provides real value security against inflation to the investor. It includes tools such as inflation indexed bonds, annuities, inflation linked mutual funds, etc. If you are looking for a format to display your unique thoughts, then the professionally designed Various Inflation Indexing Instruments To Comprehensive Guide On Inflation Control CM SS V is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Various Inflation Indexing Instruments To Comprehensive Guide On Inflation Control CM SS V and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. This slide shows multiple inflation indexing instruments which provides real value security against inflation to the investor. It includes tools such as inflation indexed bonds, annuities, inflation linked mutual funds, etc.

Unlocking Potential IoTs Application Emerging Trends And Future Applications Of IoT SS V
This slide presents the emerging trends and future applications of IoT. It incorporates edge computing in IoT, AI, and ML in IoT data analysis, IoT in smart cities, and Blockchain technology for security and privacy. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Unlocking Potential IoTs Application Emerging Trends And Future Applications Of IoT SS V was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Unlocking Potential IoTs Application Emerging Trends And Future Applications Of IoT SS V. This slide presents the emerging trends and future applications of IoT. It incorporates edge computing in IoT, AI, and ML in IoT data analysis, IoT in smart cities, and Blockchain technology for security and privacy.
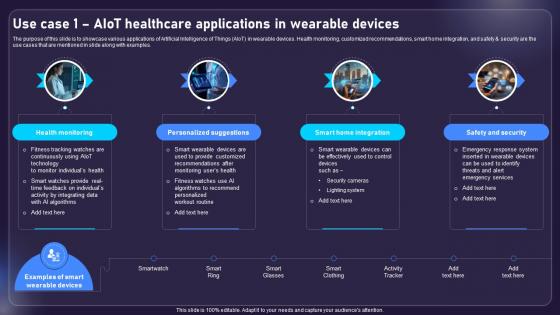
Use Case 1 AIOT Healthcare Applications In Wearable Devices AIOT Applications For Various Industries IoT SS V
The purpose of this slide is to showcase various applications of Artificial Intelligence of Things AIoT in wearable devices. Health monitoring, customized recommendations, smart home integration, and safety and security are the use cases that are mentioned in slide along with examples. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Use Case 1 AIOT Healthcare Applications In Wearable Devices AIOT Applications For Various Industries IoT SS V to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation. The purpose of this slide is to showcase various applications of Artificial Intelligence of Things AIoT in wearable devices. Health monitoring, customized recommendations, smart home integration, and safety and security are the use cases that are mentioned in slide along with examples.

Integrating AI With IoT Use Case 1 AIoT Healthcare Applications In Wearable Devices IoT SS V
The purpose of this slide is to showcase various applications of Artificial Intelligence of Things AIoT in wearable devices. Health monitoring, customized recommendations, smart home integration, and safety and security are the use cases that are mentioned in slide along with examples. Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Integrating AI With IoT Use Case 1 AIoT Healthcare Applications In Wearable Devices IoT SS V template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Integrating AI With IoT Use Case 1 AIoT Healthcare Applications In Wearable Devices IoT SS V that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers The purpose of this slide is to showcase various applications of Artificial Intelligence of Things AIoT in wearable devices. Health monitoring, customized recommendations, smart home integration, and safety and security are the use cases that are mentioned in slide along with examples.


 Continue with Email
Continue with Email

 Home
Home


































