Technology Risk
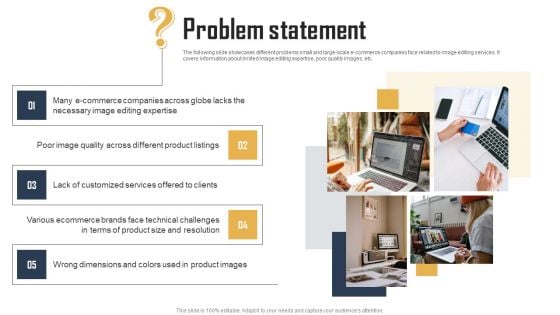
Ecommerce Photo Editing Services Fundraising Deck Problem Statement Diagrams PDF
The following slide showcases different problems small and large-scale e-commerce companies face related to image editing services. It covers information about limited image editing expertise, poor quality images, etc. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Ecommerce Photo Editing Services Fundraising Deck Problem Statement Diagrams PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable Ecommerce Photo Editing Services Fundraising Deck Problem Statement Diagrams PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.
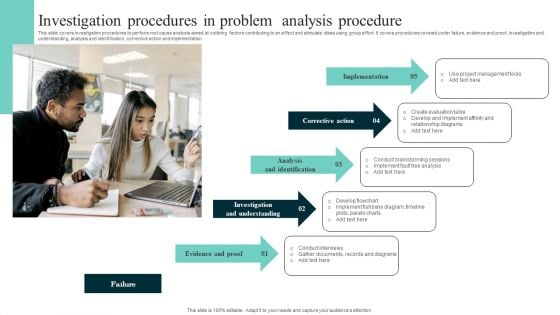
Investigation Procedures In Problem Analysis Procedure Template PDF
This slide covers investigation procedures to perform root cause analysis aimed at outlining factors contributing to an effect and stimulate ideas using group effort. It covers procedures covered under failure, evidence and proof, investigation and understanding, analysis and identification, corrective action and implementation. Persuade your audience using this Investigation Procedures In Problem Analysis Procedure Template PDF. This PPT design covers five stages, thus making it a great tool to use. It also caters to a variety of topics including Analysis And Identification, Corrective Action, Implementation. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Agile Crystal Method Problems Faced By The Company Slides PDF
This slide represents the problems faced by the company, including complex and repetitive tasks due to usage of traditional models, the productivity of team members is dwindling.Presenting Agile Crystal Method Problems Faced By The Company Slides PDF to provide visual cues and insights. Share and navigate important information on six stages that need your due attention. This template can be used to pitch topics like Computers Advanced, Environment During, Productivity Is Dwindling In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Real Time Assessment Of Security Threats Need For SIEM Software In Your Company Template PDF
This slide covers the need for the SIEM software which focuses on detecting incidents, compliance regulations, and incident management. Presenting real time assessment of security threats need for siem software in your company template pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like detecting incidents, compliance with regulations, efficient incident management. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
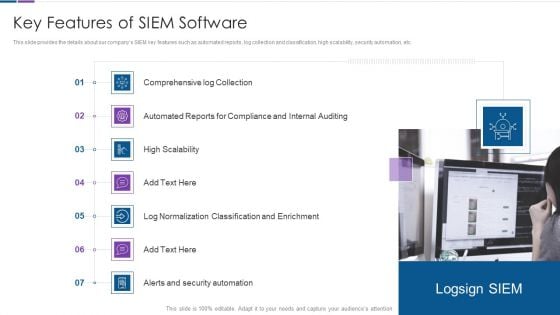
Real Time Assessment Of Security Threats Key Features Of SIEM Software Inspiration PDF
This slide provides the details about our companys SIEM key features such as automated reports, log collection and classification, high scalability, security automation, etc. Presenting real time assessment of security threats key features of siem software inspiration pdf to provide visual cues and insights. Share and navigate important information on seven stages that need your due attention. This template can be used to pitch topics like compliance and internal auditing, high scalability, classification and enrichment, security automation. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Cloud Information Security Cloud Security Threats Shared Vulnerabilities Ppt File Influencers PDF
This slide describes how organizations and providers share vulnerabilities of a system, so each party must take precautions to protect data. This is a Cloud Information Security Cloud Security Threats Shared Vulnerabilities Ppt File Influencers PDF template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Secure Cloud, Providers Already, Cloud Service. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Digital Agency Pitch Presentation Problems Faced By Customers Designs PDF
This is a digital agency pitch presentation problems faced by customers designs pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like no social presence, not enough traffic, brand experience and engagement. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Problems In Implementing Digital Marketing Strategy Ppt Icon Topics PDF
This is a problems in implementing digital marketing strategy ppt icon topics pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like marketing, strategy, implementation, innovations. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Software Engineer Creating Cloud Computing Structure For Reducing Operational Threats Ppt PowerPoint Presentation File Skills PDF
Persuade your audience using this software engineer creating cloud computing structure for reducing operational threats ppt powerpoint presentation file skills pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including software engineer creating cloud computing structure for reducing operational threats. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
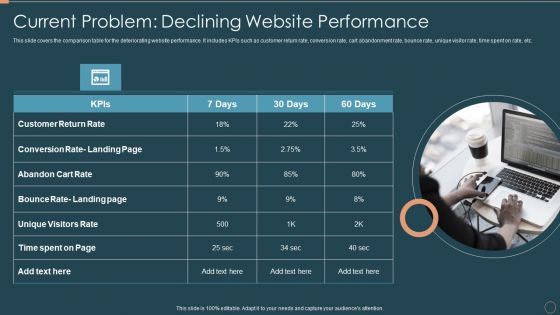
Remarketing Techniques Current Problem Declining Website Performance Microsoft PDF
This slide covers the comparison table for the deteriorating website performance. It includes KPIs such as customer return rate, conversion rate, cart abandonment rate, bounce rate, unique visitor rate, time spent on rate, etc. This is a Remarketing Techniques Current Problem Declining Website Performance Microsoft PDF template with various stages. Focus and dispense information on one stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Customer Return Rate, Conversion Rate, Abandon Cart Rate. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
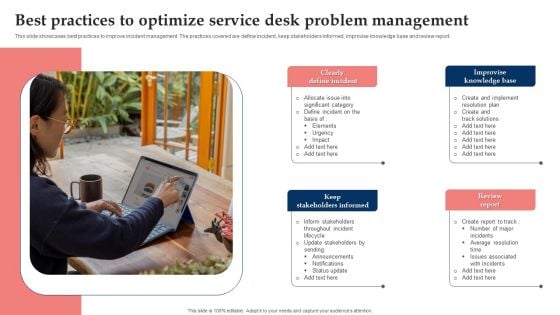
Best Practices To Optimize Service Desk Problem Management Topics PDF
This slide showcases best practices to improve incident management. The practices covered are define incident, keep stakeholders informed, improvise knowledge base and review report. Persuade your audience using this Best Practices To Optimize Service Desk Problem Management Topics PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Clearly Define Incident, Improvise Knowledge Base Review, Keep Stakeholders Informed. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
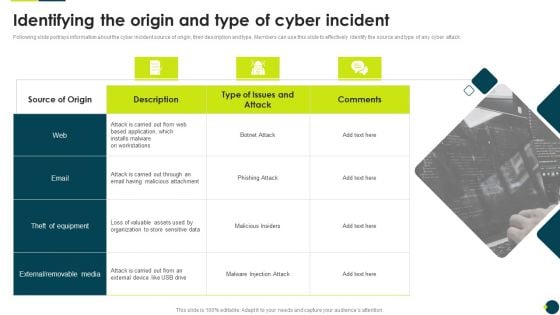
IT Threats Response Playbook Identifying The Origin And Type Of Cyber Incident Rules PDF
Following slide portrays information about the cyber incident source of origin, their description and type. Members can use this slide to effectively identify the source and type of any cyber attack.This is a IT Threats Response Playbook Identifying The Origin And Type Of Cyber Incident Rules PDF template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like External Removable, Malicious Attachment, Loss Valuable. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
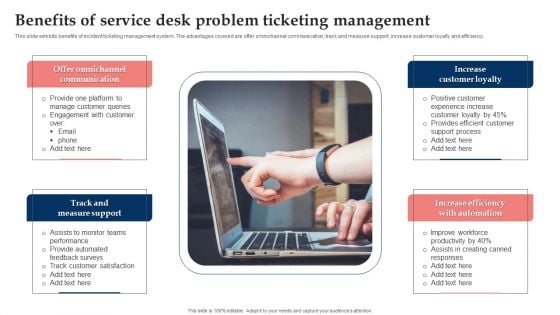
Benefits Of Service Desk Problem Ticketing Management Clipart PDF
This slide exhibits benefits of incident ticketing management system. The advantages covered are offer omnichannel communication, track and measure support, increase customer loyalty and efficiency. Presenting Benefits Of Service Desk Problem Ticketing Management Clipart PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Track And Measure Support, Increase Efficiency With Automation, Increase Customer Loyalty. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
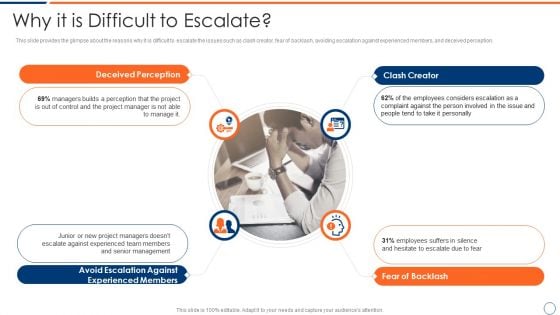
How To Intensify Project Threats Why It Is Difficult To Escalate Mockup PDF
This slide provides the glimpse about the reasons why it is difficult to escalate the issues such as clash creator, fear of backlash, avoiding escalation against experienced members, and deceived perception. This is a how to intensify project threats why it is difficult to escalate mockup pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like clash creator, fear of backlash, avoiding escalation against experienced members, deceived perception. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
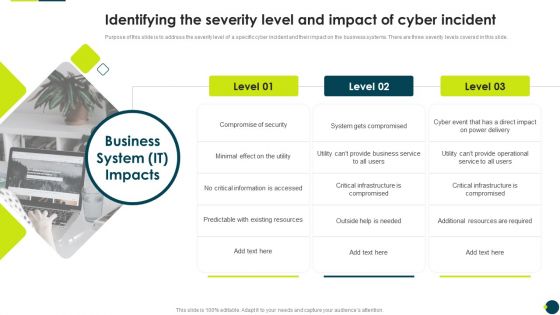
IT Threats Response Playbook Identifying The Severity Level And Impact Of Cyber Incident Portrait PDF
Purpose of this slide is to address the severity level of a specific cyber incident and their impact on the business systems. There are three severity levels covered in this slide.Presenting IT Threats Response Playbook Identifying The Severity Level And Impact Of Cyber Incident Portrait PDF to provide visual cues and insights. Share and navigate important information on one stage that need your due attention. This template can be used to pitch topics like Compromise Security, Information Accessed, Existing Resources. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Computer Protected With Security System From Online Threat Ppt PowerPoint Presentation File Example Topics PDF
Presenting computer protected with security system from online threat ppt powerpoint presentation file example topics pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including computer protected with security system from online threat. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Common Network Security Threats Vector Icon Ppt PowerPoint Presentation Ideas Elements PDF
Presenting common network security threats vector icon ppt powerpoint presentation ideas elements pdf to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including common network security threats vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Emerging Threats In Cyber Security Ppt PowerPoint Presentation Model Images PDF
Presenting emerging threats in cyber security ppt powerpoint presentation model images pdf to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including emerging threats in cyber security. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Threat Of Email Virus In Computer System Shape Ppt PowerPoint Presentation Inspiration Files PDF
Presenting threat of email virus in computer system shape ppt powerpoint presentation inspiration files pdf to dispense important information. This template comprises two stages. It also presents valuable insights into the topics including threat of email virus in computer system shape. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Network Threat Prevention And Security Vector Icon Ppt PowerPoint Presentation Outline Example Introduction PDF
Presenting network threat prevention and security vector icon ppt powerpoint presentation outline example introduction pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including network threat prevention and security vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Computer Virus Threat Vector Icon Ppt PowerPoint Presentation Professional Graphics Pictures PDF
Presenting computer virus threat vector icon ppt powerpoint presentation professional graphics pictures pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including computer virus threat vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Online Security Threat And Computer Virus Vector Icon Ppt PowerPoint Presentation Styles Vector PDF
Presenting online security threat and computer virus vector icon ppt powerpoint presentation styles vector pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including online security threat and computer virus vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Security Access To Protect Cyber Threat System Ppt PowerPoint Presentation Visual Aids Diagrams PDF
Presenting security access to protect cyber threat system ppt powerpoint presentation visual aids diagrams pdf to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including security access to protect cyber threat system. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Customer Getting Threat For The System Failure Ppt PowerPoint Presentation Gallery Layouts PDF
Presenting customer getting threat for the system failure ppt powerpoint presentation gallery layouts pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including customer getting threat for the system failure. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Security Settings To Prevent Online Threats Ppt PowerPoint Presentation Gallery Structure PDF
Presenting security settings to prevent online threats ppt powerpoint presentation gallery structure pdf to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including security settings to prevent online threats. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Icon Indicating Malware Detection In Business Threats Landscape Ppt Layouts Influencers PDF
Presenting Icon Indicating Malware Detection In Business Threats Landscape Ppt Layouts Influencers PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Icon Indicating, Malware Detection, Business Threats Landscape. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

IT Expert Assessing Cyber Threats On Laptop Ppt PowerPoint Presentation Gallery Brochure PDF
Presenting this set of slides with name it expert assessing cyber threats on laptop ppt powerpoint presentation gallery brochure pdf. This is a three stage process. The stages in this process are it expert assessing cyber threats on laptop. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
Threat Assessment For IT Network Security Ppt PowerPoint Presentation Gallery Example PDF
Presenting this set of slides with name threat assessment for it network security ppt powerpoint presentation gallery example pdf. This is a three stage process. The stages in this process are threat assessment for it network security. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Threat Scanning For IT Security Ppt PowerPoint Presentation Gallery Smartart PDF
Presenting this set of slides with name threat scanning for it security ppt powerpoint presentation gallery smartart pdf. This is a three stage process. The stages in this process are threat scanning for it security. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
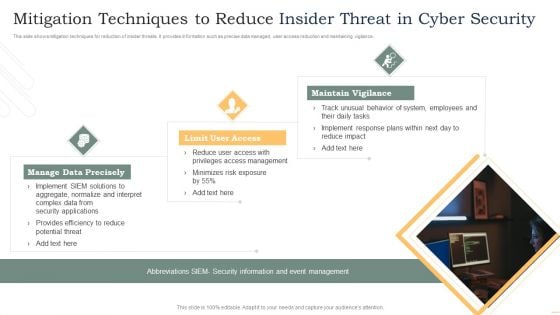
Mitigation Techniques To Reduce Insider Threat In Cyber Security Rules PDF
This slide shows mitigation techniques for reduction of insider threats. It provides information such as precise data managed, user access reduction and maintaining vigilance. Presenting Mitigation Techniques To Reduce Insider Threat In Cyber Security Rules PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Manage Data Precisely, Limit User Access, Maintain Vigilance. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Internet Security Ransomware Hacking And Data Loss Threat Ppt PowerPoint Presentation File Formats PDF
Persuade your audience using this internet security ransomware hacking and data loss threat ppt powerpoint presentation file formats pdf. This PPT design covers one stages, thus making it a great tool to use. It also caters to a variety of topics including internet security ransomware hacking and data loss threat. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Security Functioning Centre How Firm Handle Insider Threats Ppt Summary Background Image PDF
This slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc. This is a security functioning centre how firm handle insider threats ppt summary background image pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like employee training, develop threat hunting team, implement user behavioral analytics. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Cloud Security Assessment Cloud Security Threats End User Control Demonstration PDF
This slide represents the end user threat in cloud security and how an organization needs to control user access and be aware of potential threats.This is a Cloud Security Assessment Cloud Security Threats End User Control Demonstration PDF template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Rival Organizations, Cybercriminals, Contact Information. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Determine Sequence Phases For Mitigating Cybersecurity Threats And Vulnerabilities Inspiration PDF
This slide provides details regarding sequence phases for threat attack by threat actor in terms of installation, command and control, actions and objectives, covering tracks. This is a determine sequence phases for mitigating cybersecurity threats and vulnerabilities inspiration pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like installation, command and control, actions and objectives, covering tracks. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
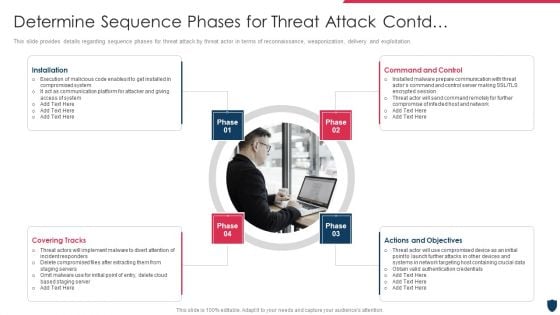
Cyber Safety Incident Management Determine Sequence Phases For Threat Attack Contd Control Inspiration PDF
This slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. This is a cyber safety incident management determine sequence phases for threat attack contd control inspiration pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like installation, covering tracks, actions and objectives, command and control. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Virus On Screen Online Crime Threat From Hacker Vector Icon Ppt PowerPoint Presentation Gallery Smartart PDF
Presenting virus on screen online crime threat from hacker vector icon ppt powerpoint presentation gallery smartart pdf to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including virus on screen online crime threat from hacker vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
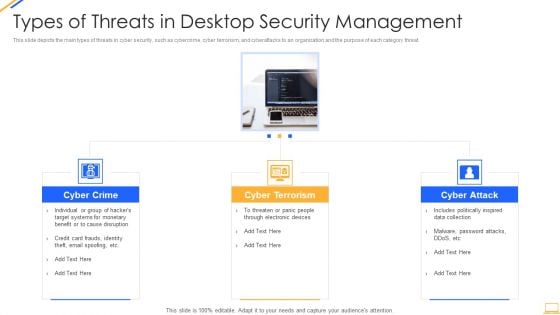
Desktop Security Management Types Of Threats In Desktop Security Management Themes PDF
This slide depicts the main types of threats in cyber security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Presenting desktop security management types of threats in desktop security management themes pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like target systems, devices. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
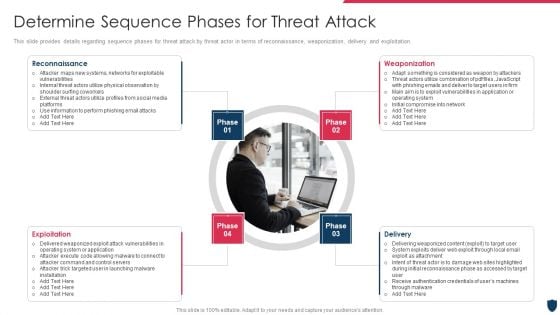
Cyber Safety Incident Management Determine Sequence Phases For Threat Attack Rules PDF
This slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Presenting cyber safety incident management determine sequence phases for threat attack rules pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like reconnaissance, weaponization, exploitation, delivery. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
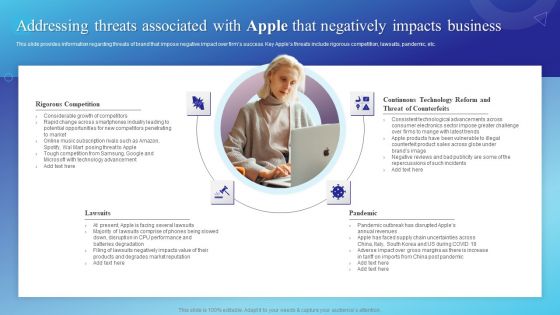
Addressing Threats Associated With Apple That Negatively Impacts Business Guidelines PDF
This slide provides information regarding threats of brand that impose negative impact over firms success. Key Apples threats include rigorous competition, lawsuits, pandemic, etc. Find a pre designed and impeccable Addressing Threats Associated With Apple That Negatively Impacts Business Guidelines PDF. The templates can ace your presentation without additional effort. You can download these easy to edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
Service Desk Problem Management Icon To Retain Customers Background PDF
Persuade your audience using this Service Desk Problem Management Framework To Reduce Team Stress Guidelines PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Service Desk Problem, Management Icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
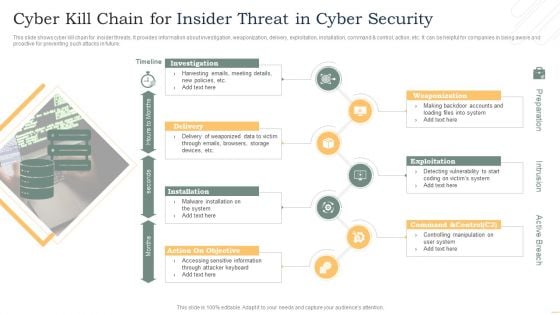
Cyber Kill Chain For Insider Threat In Cyber Security Slides PDF
This slide shows cyber kill chain for insider threats. It provides information about investigation, weaponization, delivery, exploitation, installation, command and control, action, etc. It can be helpful for companies in being aware and proactive for preventing such attacks in future. Presenting Cyber Kill Chain For Insider Threat In Cyber Security Slides PDF to dispense important information. This template comprises seven stages. It also presents valuable insights into the topics including Investigation, Delivery, Installation, Exploitation. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
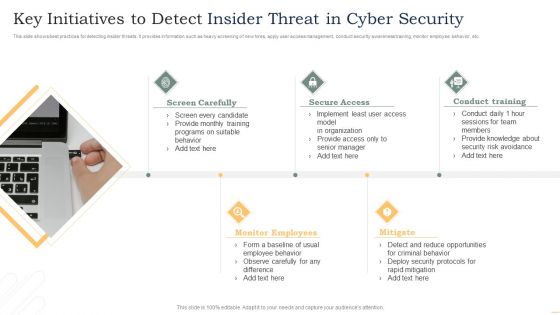
Key Initiatives To Detect Insider Threat In Cyber Security Designs PDF
This slide shows best practices for detecting insider threats. It provides information such as heavy screening of new hires, apply user access management, conduct security awareness training, monitor employee behavior, etc. Presenting Key Initiatives To Detect Insider Threat In Cyber Security Designs PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Screen Carefully, Secure Access, Conduct Training. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
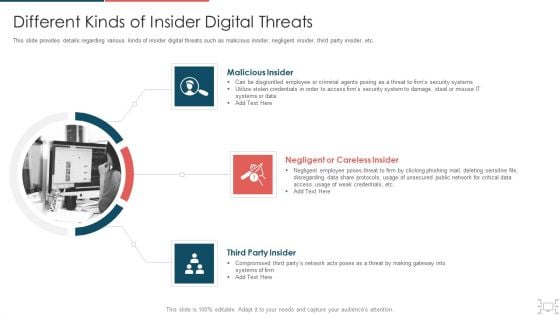
Cyber Security Administration In Organization Different Kinds Of Insider Digital Threats Microsoft PDF
This slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. This is a cyber security administration in organization different kinds of insider digital threats microsoft pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like disgruntled, employee, criminal, agents, damage, security. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Cyber Safety Incident Management Different Kinds Of Insider Digital Threats Download PDF
This slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. This is a cyber safety incident management different kinds of insider digital threats download pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like malicious insider, negligent or careless insider, third party insider. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Table Of Contents Overview On Mitigating Workplace IT Threats Slides PDF
Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Table Of Contents Overview On Mitigating Workplace IT Threats Slides PDF was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Table Of Contents Overview On Mitigating Workplace IT Threats Slides PDF.
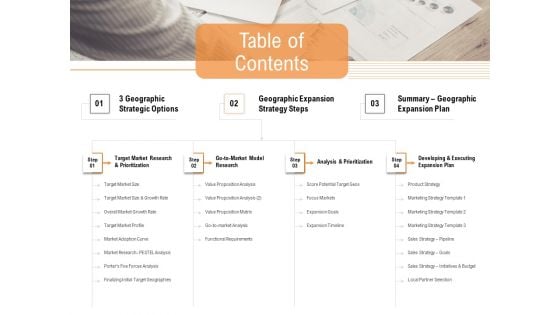
Opportunities And Threats For Penetrating In New Market Segments Table Of Contents Template PDF
Presenting opportunities and threats for penetrating in new market segments table of contents template pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like target market research and prioritization, go to market model research, analysis and prioritization, developing and executing expansion plan. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Solution Evaluation Criteria Assessment And Threat Impact Matrix Table Of Contents Sample PDF
Presenting solution evaluation criteria assessment and threat impact matrix table of contents sample pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like analysis, management, requirements, organizational. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Critical Measures For Ensuring How Firm Handle Various Insider Threats At Workplace Graphics PDF
This slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Critical Measures For Ensuring How Firm Handle Various Insider Threats At Workplace Graphics PDF was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Critical Measures For Ensuring How Firm Handle Various Insider Threats At Workplace Graphics PDF.
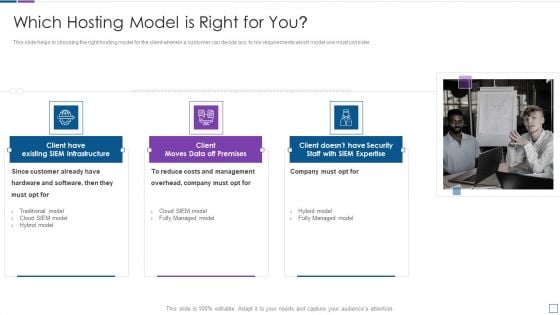
Real Time Assessment Of Security Threats Which Hosting Model Is Right For You Clipart PDF
This slide helps in choosing the right hosting model for the client wherein a customer can decide acc. to his requirements which model one must consider. This is a real time assessment of security threats which hosting model is right for you clipart pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like costs and management, company, hardware and software. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Cyber Security Administration In Organization Addressing Several Financial Scenarios And Signs Threat Template PDF
This slide provides information regarding the various financial scenarios that pose a threat to firm profitability and determine signs of financial distress. Presenting cyber security administration in organization addressing several financial scenarios and signs threat template pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like insolvency, scenario, bankruptcy, situation, fluctuations. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
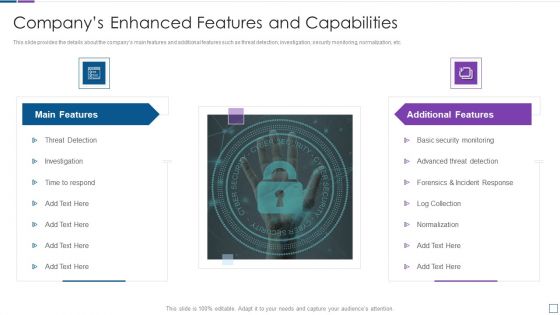
Real Time Assessment Of Security Threats Companys Enhanced Features And Capabilities Introduction PDF
This slide provides the details about the companys main features and additional features such as threat detection, investigation, security monitoring, normalization, etc. Presenting real time assessment of security threats companys enhanced features and capabilities introduction pdf to provide visual cues and insights. Share and navigate important information on two stages that need your due attention. This template can be used to pitch topics like main features, additional features. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Elastic NLB Problems Faced By The Organizations Elements PDF
This slide represents the problems faced by the organizations, such as performance of the websites, service availability, and high costs to maintain the performance and availability. The best PPT templates are a great way to save time, energy, and resources. Slidegeeks have 100 percent editable powerpoint slides making them incredibly versatile. With these quality presentation templates, you can create a captivating and memorable presentation by combining visually appealing slides and effectively communicating your message. Download Elastic NLB Problems Faced By The Organizations Elements PDF from Slidegeeks and deliver a wonderful presentation.
Solution Evaluation Criteria Assessment And Threat Impact Matrix Description Of Babok Areas Business Icons PDF
This slide shows the description of a BABOK Business Analysis Body of Knowledge area i.e. business analysis planning and monitoring whose main purpose is to develop estimates of business analysis tasks, determine the business analyses deliverables, identify stakeholders, determine business analysis process etc. along with elements and techniques at each stage. Presenting solution evaluation criteria assessment and threat impact matrix description of babok areas business icons pdf to provide visual cues and insights. Share and navigate important information on six stages that need your due attention. This template can be used to pitch topics like plan business, conduct stakeholder analysis, business analysis, communication, requirements management. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Handling Cyber Threats Digital Era Security Lifecycle Ppt Summary Brochure PDF
This is a handling cyber threats digital era security lifecycle ppt summary brochure pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like security lifecycle. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
How To Intensify Project Threats Issue And Escalation Process Flow Chart Icons PDF
This slide provides the glimpse about the issue and escalation process flowchart which covers various steps involved in this process. Presenting how to intensify project threats issue and escalation process flow chart icons pdf to provide visual cues and insights. Share and navigate important information on seven stages that need your due attention. This template can be used to pitch topics like analysis, validation and prioritization, tracking and reporting, escalation, resolution and closure. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
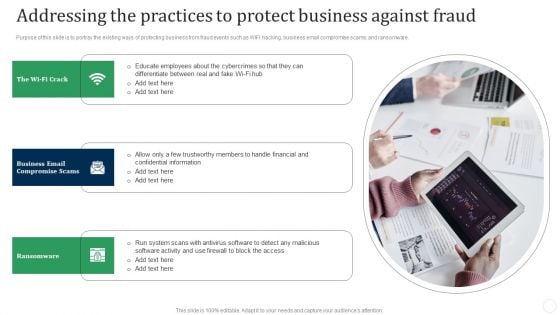
Addressing The Practices To Protect Business Against Fraud Fraud Threat Administration Guide Sample PDF
Purpose of this slide is to portray the existing ways of protecting business from fraud events such as WIFI hacking, business email compromise scams, and ransomware.This is a Addressing The Practices To Protect Business Against Fraud Fraud Threat Administration Guide Sample PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Compromise Scams, Ransomware, Confidential Information. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Handling Cyber Threats Digital Era Categorization Worksheet For Assets Ppt Icon Outline PDF
This slide illustrates asset categorization worksheet covering information about security system such as system name, its version, system location and other general information. Presenting handling cyber threats digital era categorization worksheet for assets ppt icon outline pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like server computer, system location, system accessibility. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

How To Intensify Project Threats Issues Faced By Project Manager Elements PDF
This slide provides the glimpse about the issues faced by project manager such as late shipments from suppliers, equipment malfunctions, sickness, random acts of nature, etc. This is a how to intensify project threats issues faced by project manager elements pdf template with various stages. Focus and dispense information on eight stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like priority changes, sickness, random acts of nature, equipment malfunctions, resignations. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
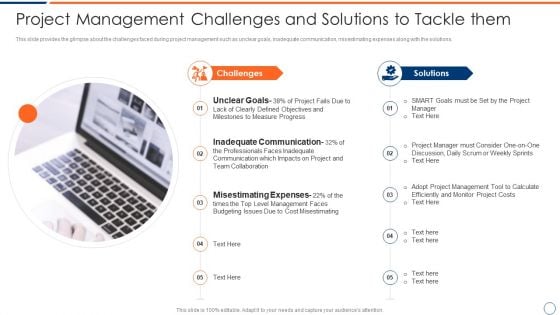
How To Intensify Project Threats Project Management Challenges And Solutions Guidelines PDF
This slide provides the glimpse about the challenges faced during project management such as unclear goals, inadequate communication, misestimating expenses along with the solutions. This is a how to intensify project threats project management challenges and solutions guidelines pdf template with various stages. Focus and dispense information on two stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like challenges, solutions. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
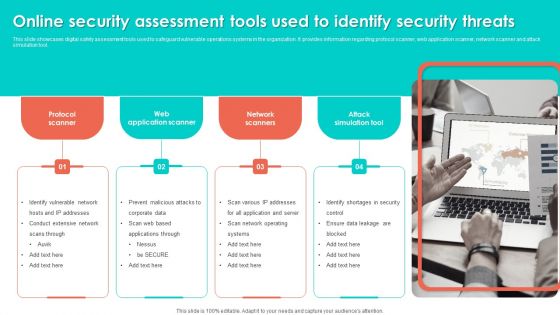
Online Security Assessment Tools Used To Identify Security Threats Slides PDF
This slide showcases digital safety assessment tools used to safeguard vulnerable operations systems in the organization. It provides information regarding protocol scanner, web application scanner, network scanner and attack simulation tool. Persuade your audience using this Online Security Assessment Tools Used To Identify Security Threats Slides PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Network Scanners, Attack Simulation Tool, Web Application Scanner. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.


 Continue with Email
Continue with Email

 Home
Home


































