Data Protection
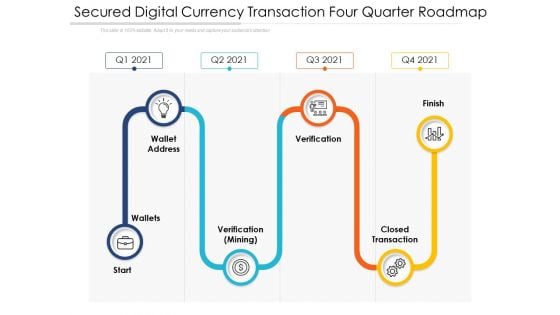
Secured Digital Currency Transaction Four Quarter Roadmap Slides
Presenting our innovatively structured secured digital currency transaction four quarter roadmap slides Template. Showcase your roadmap process in different formats like PDF, PNG, and JPG by clicking the download button below. This PPT design is available in both Standard Screen and Widescreen aspect ratios. It can also be easily personalized and presented with modified font size, font type, color, and shapes to measure your progress in a clear way.
Cyber Security Disaster Recuperation Quarterly Roadmap To Eradicate Intrusion Icons
Introducing our cyber security disaster recuperation quarterly roadmap to eradicate intrusion icons. This PPT presentation is Google Slides compatible, therefore, you can share it easily with the collaborators for measuring the progress. Also, the presentation is available in both standard screen and widescreen aspect ratios. So edit the template design by modifying the font size, font type, color, and shapes as per your requirements. As this PPT design is fully editable it can be presented in PDF, JPG and PNG formats.
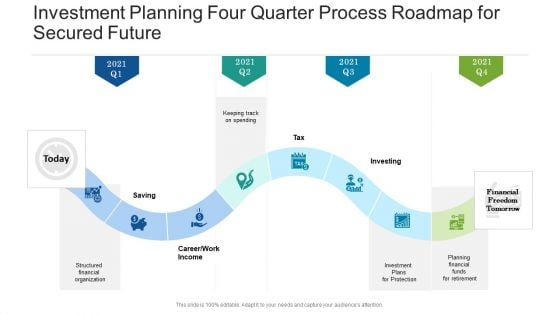
Investment Planning Four Quarter Process Roadmap For Secured Future Demonstration
Introducing our investment planning four quarter process roadmap for secured future demonstration. This PPT presentation is Google Slides compatible, therefore, you can share it easily with the collaborators for measuring the progress. Also, the presentation is available in both standard screen and widescreen aspect ratios. So edit the template design by modifying the font size, font type, color, and shapes as per your requirements. As this PPT design is fully editable it can be presented in PDF, JPG and PNG formats.
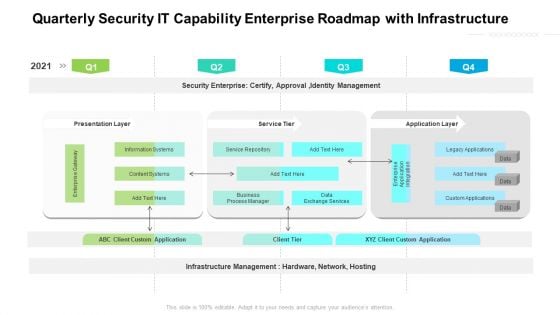
Quarterly Security IT Capability Enterprise Roadmap With Infrastructure Background
Presenting our jaw dropping quarterly security it capability enterprise roadmap with infrastructure background. You can alternate the color, font size, font type, and shapes of this PPT layout according to your strategic process. This PPT presentation is compatible with Google Slides and is available in both standard screen and widescreen aspect ratios. You can also download this well researched PowerPoint template design in different formats like PDF, JPG, and PNG. So utilize this visually appealing design by clicking the download button given below.
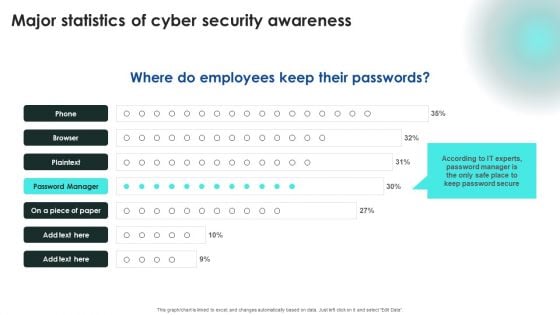
Implementing Cybersecurity Awareness Program To Prevent Attacks Major Statistics Of Cyber Security Awareness Structure PDF
Explore a selection of the finest Implementing Cybersecurity Awareness Program To Prevent Attacks Major Statistics Of Cyber Security Awareness Structure PDF here. With a plethora of professionally designed and pre made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Implementing Cybersecurity Awareness Program To Prevent Attacks Major Statistics Of Cyber Security Awareness Structure PDF to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks.

Impact On Organization After Implementing Information Technology Security Ppt Infographic Template Examples PDF
This slide depicts the hardware software update measure under the network security model. It also tells the current status of the devices that need to update in the organization. Deliver and pitch your topic in the best possible manner with this impact on organization after implementing information technology security ppt infographic template examples pdf. Use them to share invaluable insights on hardware and software update in company and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
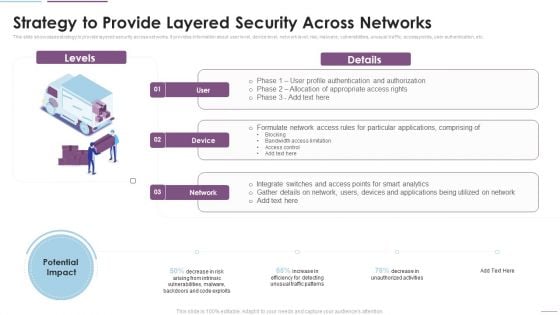
Supply Chain Management Strategy To Provide Layered Security Across Networks Brochure PDF
This slide showcases strategy to provide layered security across networks. It provides information about user level, device level, network level, risk, malware, vulnerabilities, unusual traffic, access points, user authentication, etc. Deliver and pitch your topic in the best possible manner with this Supply Chain Management Strategy To Provide Layered Security Across Networks Brochure PDF. Use them to share invaluable insights on Formulate Network, Access Rules, Particular Applications, Bandwidth Access Limitation and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
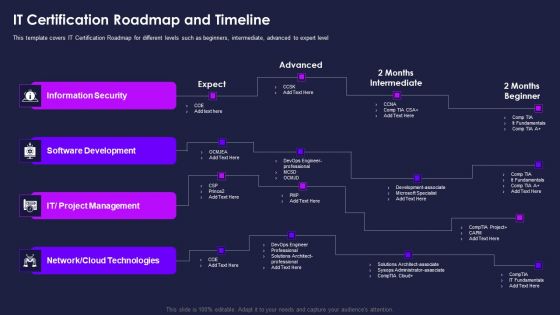
Certification Information Technology Professionals IT Certification Roadmap Elements PDF
This template covers IT Certification Roadmap for different levels such as beginners, intermediate, advanced to expert level Deliver an awe inspiring pitch with this creative certification information technology professionals it certification roadmap elements pdf bundle. Topics like information security, software development, project management, network cloud technologies can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
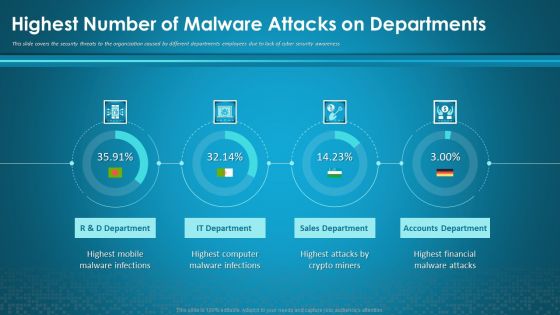
Organizational Network Security Awareness Staff Learning Highest Number Of Malware Attacks On Departments Information PDF
This slide covers the security threats to the organization caused by different departments employees due to lack of cyber security awareness. Deliver and pitch your topic in the best possible manner with this organizational network security awareness staff learning highest number of malware attacks on departments information pdf. Use them to share invaluable insights on sales department, accounts department, financial, computer, mobile and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
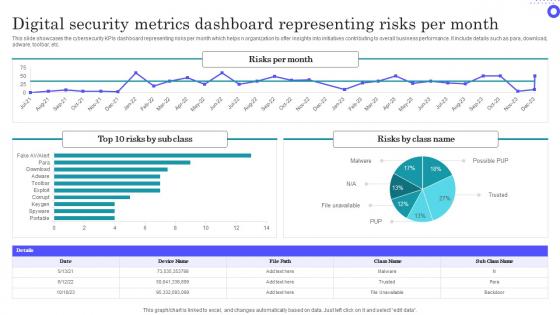
Digital Security Metrics Dashboard Representing Risks Per Month Themes Pdf
Showcasing this set of slides titled Digital Security Metrics Dashboard Representing Risks Per Month Themes Pdf The topics addressed in these templates are Digital Security, Metrics Dashboard, Representing Risks All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting. This slide showcases the cybersecurity KPIs dashboard representing risks per month which helps n organization to offer insights into initiatives contributing to overall business performance. It include details such as para, download, adware, toolbar, etc.
Security Incident Notification Email Template In Powerpoint And Google Slides Cpb
Introducing our well designed Security Incident Notification Email Template In Powerpoint And Google Slides Cpb. This PowerPoint design presents information on topics like Security Incident Notification Email Template. As it is predesigned it helps boost your confidence level. It also makes you a better presenter because of its high quality content and graphics. This PPT layout can be downloaded and used in different formats like PDF, PNG, and JPG. Not only this, it is available in both Standard Screen and Widescreen aspect ratios for your convenience. Therefore, click on the download button now to persuade and impress your audience. Our Security Incident Notification Email Template In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Cyber Security Risk Register Template In Powerpoint And Google Slides Cpb
Introducing our well designed Cyber Security Risk Register Template In Powerpoint And Google Slides Cpb. This PowerPoint design presents information on topics like Cyber Security Risk Register Template. As it is predesigned it helps boost your confidence level. It also makes you a better presenter because of its high quality content and graphics. This PPT layout can be downloaded and used in different formats like PDF, PNG, and JPG. Not only this, it is available in both Standard Screen and Widescreen aspect ratios for your convenience. Therefore, click on the download button now to persuade and impress your audience. Our Cyber Security Risk Register Template In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Laptop Deals Cyber Security Awareness In Powerpoint And Google Slides Cpb
Introducing our well-designed Laptop Deals Cyber Security Awareness In Powerpoint And Google Slides Cpb. This PowerPoint design presents information on topics like Laptop Deals Cyber Security Awareness. As it is predesigned it helps boost your confidence level. It also makes you a better presenter because of its high-quality content and graphics. This PPT layout can be downloaded and used in different formats like PDF, PNG, and JPG. Not only this, it is available in both Standard Screen and Widescreen aspect ratios for your convenience. Therefore, click on the download button now to persuade and impress your audience. Our Laptop Deals Cyber Security Awareness In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.
Google Pixel Enterprise Security System In Powerpoint And Google Slides Cpb
Introducing our well-designed Google Pixel Enterprise Security System In Powerpoint And Google Slides Cpb. This PowerPoint design presents information on topics like Google Pixel Enterprise Security System. As it is predesigned it helps boost your confidence level. It also makes you a better presenter because of its high-quality content and graphics. This PPT layout can be downloaded and used in different formats like PDF, PNG, and JPG. Not only this, it is available in both Standard Screen and Widescreen aspect ratios for your convenience. Therefore, click on the download button now to persuade and impress your audience. Our Google Pixel Enterprise Security System In Powerpoint And Google Slides Cpb are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Links Of Chain Security PowerPoint Templates And PowerPoint Themes 1012
Links Of Chain Security PowerPoint Templates And PowerPoint Themes 1012-Use this Template to elaborate the concept of security using this chain. Security in one's life is essential whether it Get on the boat with our Links Of Chain Security PowerPoint Templates And PowerPoint Themes 1012. Set sail for the port of success.

Keyboard Symbol With Key Security PowerPoint Templates And PowerPoint Themes 0912
Keyboard Symbol With Key Security PowerPoint Templates And PowerPoint Themes 0912-Microsoft Powerpoint Templates and Background with computer keyboard with two security keys -Computer keyboard with two security keys, technology computer, internet, security, success Win trust with our Keyboard Symbol With Key Security PowerPoint Templates And PowerPoint Themes 0912. You will come out on top.

Secure Network Construction Proposal Table Of Contents One Pager Sample Example Document
Presenting you an exemplary Secure Network Construction Proposal Table Of Contents One Pager Sample Example Document. Our one-pager comprises all the must-have essentials of an inclusive document. You can edit it with ease, as its layout is completely editable. With such freedom, you can tweak its design and other elements to your requirements. Download this Secure Network Construction Proposal Table Of Contents One Pager Sample Example Document brilliant piece now.
Table Of Contents Secure Network Construction Proposal One Pager Sample Example Document
Presenting you an exemplary Table Of Contents Secure Network Construction Proposal One Pager Sample Example Document. Our one-pager comprises all the must-have essentials of an inclusive document. You can edit it with ease, as its layout is completely editable. With such freedom, you can tweak its design and other elements to your requirements. Download this Table Of Contents Secure Network Construction Proposal One Pager Sample Example Document brilliant piece now.
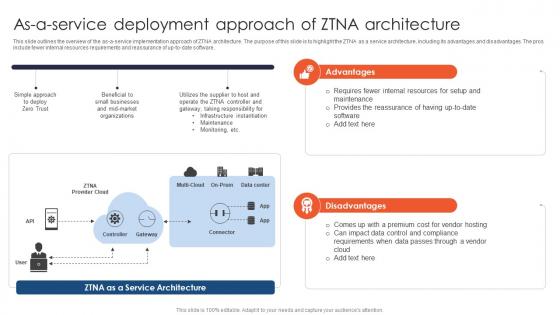
Zero Trust Network Access As A Service Deployment Approach Of ZTNA Architecture
This slide outlines the overview of the as-a-service implementation approach of ZTNA architecture. The purpose of this slide is to highlight the ZTNA as a service architecture, including its advantages and disadvantages. The pros include fewer internal resources requirements and reassurance of up-to-date software. If you are looking for a format to display your unique thoughts, then the professionally designed Zero Trust Network Access As A Service Deployment Approach Of ZTNA Architecture is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Zero Trust Network Access As A Service Deployment Approach Of ZTNA Architecture and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. This slide outlines the overview of the as-a-service implementation approach of ZTNA architecture. The purpose of this slide is to highlight the ZTNA as a service architecture, including its advantages and disadvantages. The pros include fewer internal resources requirements and reassurance of up-to-date software.
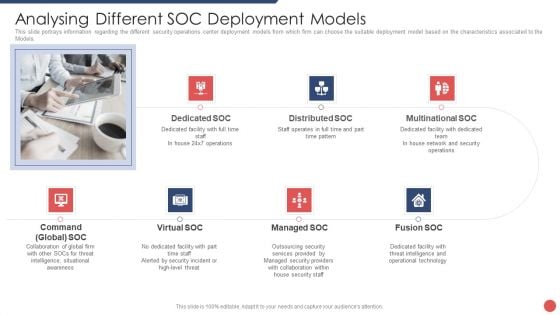
Security Functioning Centre Analysing Different SOC Deployment Models Template PDF
This slide portrays information regarding the different security operations center deployment models from which firm can choose the suitable deployment model based on the characteristics associated to the Models. This is a security functioning centre analysing different soc deployment models template pdf template with various stages. Focus and dispense information on seven stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like distributed, network, security operations, operational technology, threat intelligence. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Internal Stakeholder Engagement Security Emergency Response Communication Plan Introduction Pdf
This slide showcase Internal stakeholder engagement security incident communication plan to manage crisis effectively. It includes elements such as when to engage, point of contact, channel and time interval Showcasing this set of slides titled Internal Stakeholder Engagement Security Emergency Response Communication Plan Introduction Pdf The topics addressed in these templates are Contact Authority, Time Interval, Director Of Security Operations All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting. This slide showcase Internal stakeholder engagement security incident communication plan to manage crisis effectively. It includes elements such as when to engage, point of contact, channel and time interval
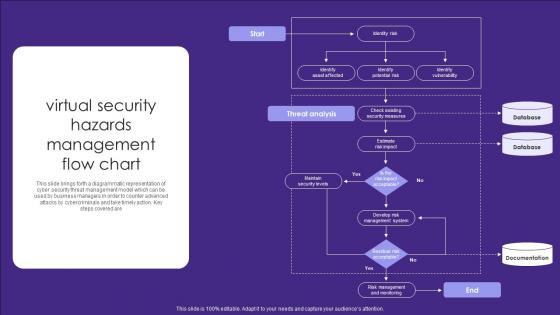
Virtual Security Hazards Management Flow Chart Infographics Pdf
This slide brings forth a diagrammatic representation of cyber security threat management model which can be used by business managers in order to counter advanced attacks by cybercriminals and take timely action. Key steps covered are Showcasing this set of slides titled Virtual Security Hazards Management Flow Chart Infographics Pdf. The topics addressed in these templates are Security Measures, Database, Documentation. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting. This slide brings forth a diagrammatic representation of cyber security threat management model which can be used by business managers in order to counter advanced attacks by cybercriminals and take timely action. Key steps covered are
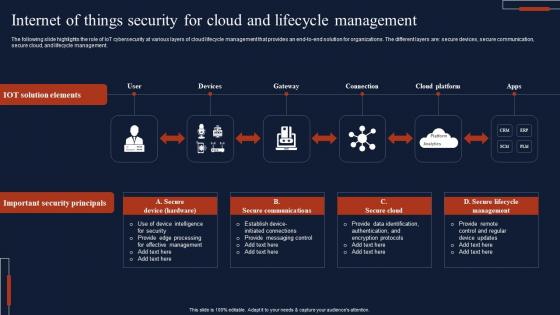
Internet Of Things Security For Cloud And Lifecycle Management Slides Pdf
The following slide highlights the role of IoT cybersecurity at various layers of cloud lifecycle management that provides an end-to-end solution for organizations. The different layers are secure devices, secure communication, secure cloud, and lifecycle management. Showcasing this set of slides titled Internet Of Things Security For Cloud And Lifecycle Management Slides Pdf The topics addressed in these templates are Important Security Principals, Secure Communications All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting. The following slide highlights the role of IoT cybersecurity at various layers of cloud lifecycle management that provides an end-to-end solution for organizations. The different layers are secure devices, secure communication, secure cloud, and lifecycle management.
Cloud Security KPI Dashboard With Key Statistics Ppt Icon Examples PDF
Pitch your topic with ease and precision using this Cloud Security KPI Dashboard With Key Statistics Ppt Icon Examples PDF. This layout presents information on Compliance Trend, Risk Status, Risk Severity. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
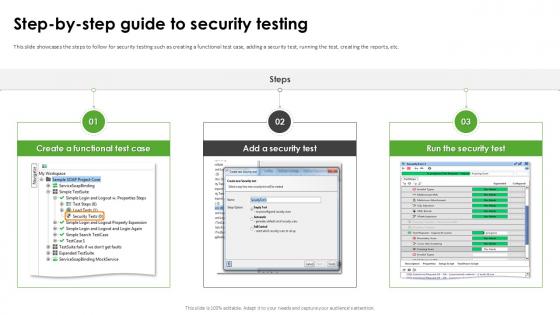
Step By Step Guide To Security Testing Harnessing The World Of Ethical Ppt Template
This slide showcases the steps to follow for security testing such as creating a functional test case, adding a security test, running the test, creating the reports, etc. Slidegeeks has constructed Step By Step Guide To Security Testing Harnessing The World Of Ethical Ppt Template after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates. This slide showcases the steps to follow for security testing such as creating a functional test case, adding a security test, running the test, creating the reports, etc.
Secured Childcare Market Strategic Assessment Icon Topics Pdf
Pitch your topic with ease and precision using this Secured Childcare Market Strategic Assessment Icon Topics Pdf This layout presents information on Secured Childcare, Market Strategic, Assessment Icon It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout. Our Secured Childcare Market Strategic Assessment Icon Topics Pdf are topically designed to provide an attractive backdrop to any subject. Use them to look like a presentation pro.

Information And Technology Security Operations Financial Information PDF
Presenting information and technology security operations financial information pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like euro, dollar, pound. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
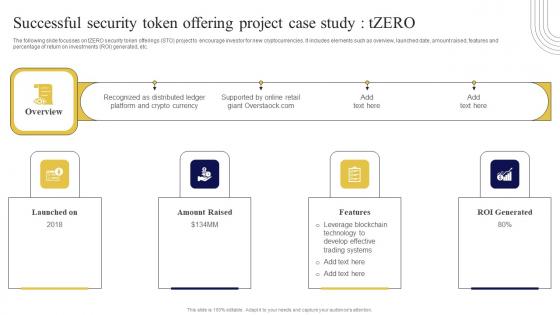
Successful Security Token Offering Exploring Investment Opportunities Background Pdf
The following slide focusses on tZERO security token offerings STO project to encourage investor for new cryptocurrencies. It includes elements such as overview, launched date, amount raised, features and percentage of return on investments ROI generated, etc. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download Successful Security Token Offering Exploring Investment Opportunities Background Pdf to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the Successful Security Token Offering Exploring Investment Opportunities Background Pdf. The following slide focusses on tZERO security token offerings STO project to encourage investor for new cryptocurrencies. It includes elements such as overview, launched date, amount raised, features and percentage of return on investments ROI generated, etc.
Private Knowledge Security PowerPoint Template 1110
3d illustration of a large brass key inserted into a human brain on a gray reflective surface Fresh concepts are ever evolving. Help the audience absorb them with our Private Knowledge Security PowerPoint Template 1110.

Key Security PowerPoint Backgrounds And Templates 1210
Microsoft PowerPoint Template and Background with Photo of a Vintage Key With Dramatic Lighting Our Key Security PowerPoint Backgrounds And Templates 1210 offer many amenities. They facilitate any excercise you undertake.
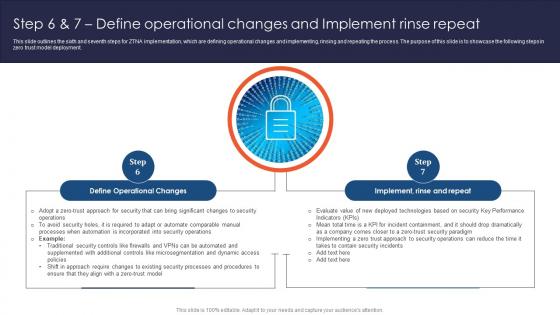
Zero Trust Network Access Step 6 And 7 Define Operational Changes And Implement Rinse Repeat
This slide outlines the sixth and seventh steps for ZTNA implementation, which are defining operational changes and implementing, rinsing and repeating the process. The purpose of this slide is to showcase the following steps in zero trust model deployment. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Zero Trust Network Access Step 6 And 7 Define Operational Changes And Implement Rinse Repeat and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable. This slide outlines the sixth and seventh steps for ZTNA implementation, which are defining operational changes and implementing, rinsing and repeating the process. The purpose of this slide is to showcase the following steps in zero trust model deployment.

Information Technology Security Policy In Business Organization Download PDF
This slide depicts the IT security policies that shape organizations preparedness and response to security incidents within the organization. Certain policies include acceptable, use policy, access control policy, security training policy, incident response policy, and remote access policy. Presenting Information Technology Security Policy In Business Organization Download PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Access Control Policy, Acceptable Use Policy, Remote Access Policy. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Network Structure Analysis Model For Security Management Ppt Styles Icons PDF
Showcasing this set of slides titled network structure analysis model for security management ppt styles icons pdf. The topics addressed in these templates are structure, management, analysis. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
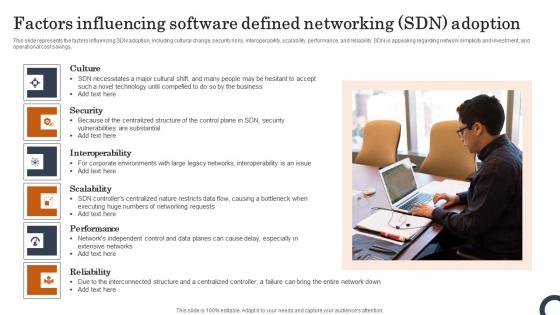
Factors Influencing Software Defined Networking SDN Adoption Evolution Of SDN Controllers Slides Pdf
This slide represents the factors influencing SDN adoption, including cultural change, security risks, interoperability, scalability, performance, and reliability. SDN is appealing regarding network simplicity and investment, and operational cost savings. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Factors Influencing Software Defined Networking SDN Adoption Evolution Of SDN Controllers Slides Pdf and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable. This slide represents the factors influencing SDN adoption, including cultural change, security risks, interoperability, scalability, performance, and reliability. SDN is appealing regarding network simplicity and investment, and operational cost savings.
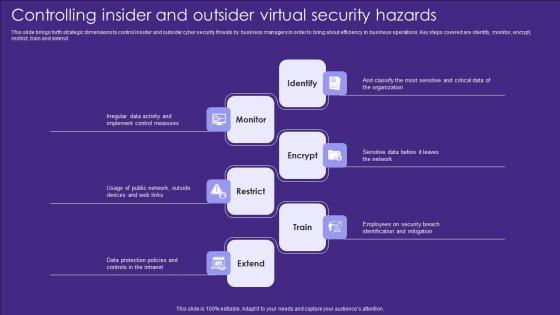
Controlling Insider And Outsider Virtual Security Hazards Designs Pdf
This slide brings forth strategic dimensions to control insider and outsider cyber security threats by business managers in order to bring about efficiency in business operations. Key steps covered are identify, monitor, encrypt, restrict, train and extend Showcasing this set of slides titled Controlling Insider And Outsider Virtual Security Hazards Designs Pdf. The topics addressed in these templates are Identify, Monitor, Encrypt. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting. This slide brings forth strategic dimensions to control insider and outsider cyber security threats by business managers in order to bring about efficiency in business operations. Key steps covered are identify, monitor, encrypt, restrict, train and extend

Settings Folder Security PowerPoint Templates And PowerPoint Backgrounds 0111
Microsoft PowerPoint Template and Background with settings folder icon for security Be absolutely professional with our Settings Folder Security PowerPoint Templates And PowerPoint Backgrounds 0111. Dont pass up this opportunity to shine.

Online Security PowerPoint Templates And PowerPoint Backgrounds 0211
Microsoft PowerPoint Template and Background with online security warning message browsing the web Export your ideas to different shores. Ship them out on our Online Security PowerPoint Templates And PowerPoint Backgrounds 0211.

Job Folder Security PowerPoint Templates And PowerPoint Backgrounds 0311
Microsoft PowerPoint Template and Background with a job folder for security Transfer knowledge with our Job Folder Security PowerPoint Templates And PowerPoint Backgrounds 0311. Download without worries with our money back guaranteee.

Microchip And Key Security PowerPoint Templates And PowerPoint Backgrounds 0411
Microsoft PowerPoint Template and Background with microchip and key security Color your presentation with success with our Microchip And Key Security PowerPoint Templates And PowerPoint Backgrounds 0411. You will come out on top.

Concept Of Internet Security PowerPoint Templates And PowerPoint Backgrounds 0511
Microsoft PowerPoint Template and Background with concept of internet security Drive to success with our Concept Of Internet Security PowerPoint Templates And PowerPoint Backgrounds 0511. You will come out on top.

Security Background PowerPoint Templates And PowerPoint Backgrounds 0911
Microsoft PowerPoint Template and Background with security online software as blue abstract art Carve out a name for yourself with our Security Background PowerPoint Templates And PowerPoint Backgrounds 0911. The audience will award you with accolades.

Microchip And Key Security PowerPoint Themes And PowerPoint Slides 0411
Microsoft PowerPoint Theme and Slide with microchip and key security Be an outperforming market competititor with our Microchip And Key Security PowerPoint Themes And PowerPoint Slides 0411. They will make you look good.

Security Background PowerPoint Themes And PowerPoint Slides 0911
Microsoft PowerPoint Theme and Slide with security online software as blue abstract art Exhibit global market dominance with our Security Background PowerPoint Themes And PowerPoint Slides 0911. They will make you look good.

Concept Of Internet Security PowerPoint Themes And PowerPoint Slides 0511
Microsoft PowerPoint Theme and Slide with concept of internet security Our Concept Of Internet Security PowerPoint Themes And PowerPoint Slides 0511 have a chrismatic effect. The audience will attest to your brilliance.
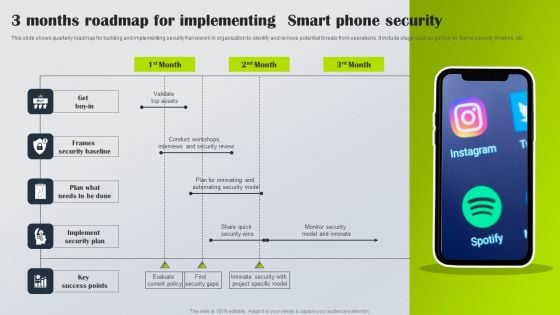
3 Months Roadmap For Implementing Smart Phone Security Information PDF
This slide shows quarterly roadmap for building and implementing security framework in organization to identify and remove potential threats from operations. It include stage such as get buy-in, frame security timeline, etc. Presenting 3 Months Roadmap For Implementing Smart Phone Security Information PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Get Buy In, Frames Security Baseline, Implement Security Plan. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Comparative Analysis Email Security Network Gateway Ppt Outline Graphics Template PDF
The following slide showcases comparison of email security gateways along with features rating and price. Main gateways included are mimecast, ironscales, avanan and trustifi. Showcasing this set of slides titled Comparative Analysis Email Security Network Gateway Ppt Outline Graphics Template PDF. The topics addressed in these templates are Gateway Device Establishment, Establish Strong, Identity For Gateway. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Quarterly Roadmap For Social Networking Marketing Plan Structure
Presenting our innovatively-structured quarterly roadmap for social networking marketing plan structure Template. Showcase your roadmap process in different formats like PDF, PNG, and JPG by clicking the download button below. This PPT design is available in both Standard Screen and Widescreen aspect ratios. It can also be easily personalized and presented with modified font size, font type, color, and shapes to measure your progress in a clear way.
Information Security Survey Example Ppt Templates
This is a information security survey example ppt templates. This is a five stage process. The stages in this process are information, secret, security, personal, business.

Stock Photo Monitor With Lock And Key Security PowerPoint Slide
This image slide displays monitor with key and key hole on the screen. This image slide may be used to express views on technology and security in your presentations. This image slide will help you express your views.

Zero Trust Model Zero Trust Network Access ZTNA Introduction
This slide represents the overview of zero trust network access, including its, benefits and principles. The purpose of this slide is to demonstrate the overview, principles and benefits of ZTNA. The primary benefits include seamless user experience, effortless scale, no need for legacy applications, etc. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download Zero Trust Model Zero Trust Network Access ZTNA Introduction to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the Zero Trust Model Zero Trust Network Access ZTNA Introduction. This slide represents the overview of zero trust network access, including its, benefits and principles. The purpose of this slide is to demonstrate the overview, principles and benefits of ZTNA. The primary benefits include seamless user experience, effortless scale, no need for legacy applications, etc.
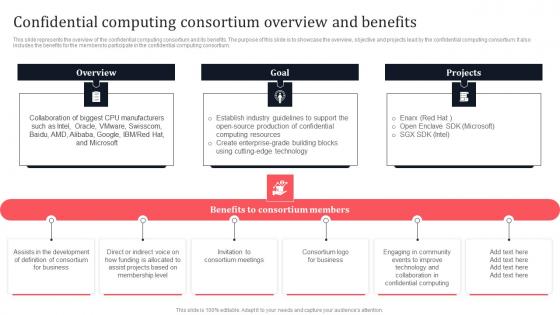
Confidential Computing Consortium Overview And Benefits Secure Multi Party Demonstration Pdf
This slide represents the overview of the confidential computing consortium and its benefits. The purpose of this slide is to showcase the overview, objective and projects lead by the confidential computing consortium. It also includes the benefits for the members to participate in the confidential computing consortium. If you are looking for a format to display your unique thoughts, then the professionally designed Confidential Computing Consortium Overview And Benefits Secure Multi Party Demonstration Pdf is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Confidential Computing Consortium Overview And Benefits Secure Multi Party Demonstration Pdf and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. This slide represents the overview of the confidential computing consortium and its benefits. The purpose of this slide is to showcase the overview, objective and projects lead by the confidential computing consortium. It also includes the benefits for the members to participate in the confidential computing consortium.
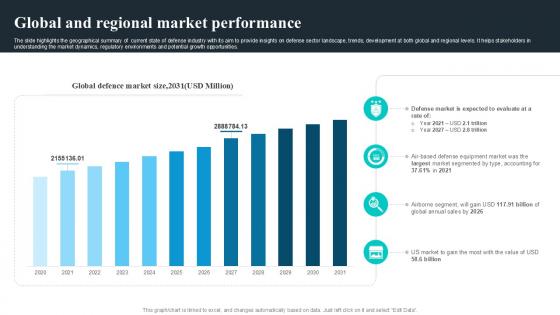
Global And Regional Market Performance Global Security Industry PPT Slide IR SS V
The slide highlights the geographical summary of current state of defense industry with its aim to provide insights on defense sector landscape, trends, development at both global and regional levels. It helps stakeholders in understanding the market dynamics, regulatory environments and potential growth opportunities. If you are looking for a format to display your unique thoughts, then the professionally designed Global And Regional Market Performance Global Security Industry PPT Slide IR SS V is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Global And Regional Market Performance Global Security Industry PPT Slide IR SS V and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable. The slide highlights the geographical summary of current state of defense industry with its aim to provide insights on defense sector landscape, trends, development at both global and regional levels. It helps stakeholders in understanding the market dynamics, regulatory environments and potential growth opportunities.
Open Lock Icon With Text Holders Ppt PowerPoint Presentation Ideas Templates PDF
Presenting this set of slides with name open lock icon with text holders ppt powerpoint presentation ideas templates pdf. This is a one stage process. The stage in this process is open lock icon with text holders. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
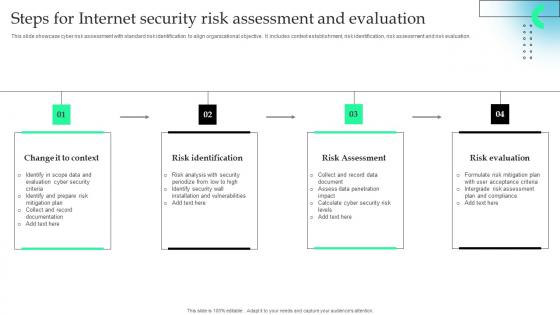
Steps For Internet Security Risk Assessment And Evaluation Microsoft Pdf
This slide showcase cyber risk assessment with standard risk identification to align organizational objective . It includes context establishment, risk identification, risk assessment and risk evaluation. Showcasing this set of slides titled Steps For Internet Security Risk Assessment And Evaluation Microsoft Pdf The topics addressed in these templates are Risk Identification, Risk Assessment, Risk Evaluation All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting. This slide showcase cyber risk assessment with standard risk identification to align organizational objective . It includes context establishment, risk identification, risk assessment and risk evaluation.

Malware Cyber Security Breach Training Program In Organization Designs Pdf
Following slides shows the various campaign plan organize in organization regarding cyber awareness to reduce the threat. It includes various campaign Pitch your topic with ease and precision using this Malware Cyber Security Breach Training Program In Organization Designs Pdf This layout presents information on Malware Cyber Security Breach, Training Program In Organization It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout. Following slides shows the various campaign plan organize in organization regarding cyber awareness to reduce the threat. It includes various campaign
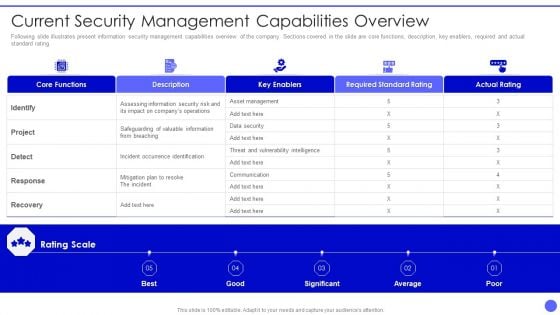
Info Safety And ISO 27001 Current Security Management Capabilities Overview Ideas PDF
Following slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating. Deliver an awe inspiring pitch with this creative Info Safety And ISO 27001 Current Security Management Capabilities Overview Ideas PDF bundle. Topics like Core Functions, Rating Scale, Key Enablers, Required Standard Rating, Actual Rating can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Chain Security PowerPoint Templates And PowerPoint Themes 1012
Chain Security PowerPoint Templates And PowerPoint Themes 1012-This PowerPoint template consists of an image of many linked chains connected to one circular green chain. This image represents the concept of security or steps of business strategies. This template also emphasize strong group between family, business etc. Present your views using our innovative slides and be assured of leaving a lasting impression. -Chain Security PowerPoint Templates And PowerPoint Themes 1012-This PowerPoint template can be used for presentations relating to-Chains of design, communication, security, business, teamwork, industrial Set a good example with our Chain Security PowerPoint Templates And PowerPoint Themes 1012. Be the benchmark for others to follow.

Information Architecture Security Architecture Ppt Slides
This is an information architecture security architecture ppt slides. This is a four stage process. The stages in this process are business, marketing, security.

SIEM Services Ppt PowerPoint Presentation Complete Deck With Slides
This complete deck covers various topics and highlights important concepts. It has PPT slides which cater to your business needs. This complete deck presentation emphasizes siem services ppt powerpoint presentation complete deck with slides and has templates with professional background images and relevant content. This deck consists of total of sixty five slides. Our designers have created customizable templates, keeping your convenience in mind. You can edit the colour, text and font size with ease. Not just this, you can also add or delete the content if needed. Get access to this fully editable complete presentation by clicking the download button below.

Overview And Workflow Process Comprehensive Guide To Blockchain Digital Security Template Pdf
The following slide showcases the brief introduction of eclipse attack to have understanding of malicious node among peer to peer network P2P. It includes elements such as how does and eclipse attack works, reconnecting with malicious node, exposure to information, etc. The best PPT templates are a great way to save time, energy, and resources. Slidegeeks have 100 percent editable powerpoint slides making them incredibly versatile. With these quality presentation templates, you can create a captivating and memorable presentation by combining visually appealing slides and effectively communicating your message. Download Overview And Workflow Process Comprehensive Guide To Blockchain Digital Security Template Pdf from Slidegeeks and deliver a wonderful presentation. The following slide showcases the brief introduction of eclipse attack to have understanding of malicious node among peer to peer network P2P. It includes elements such as how does and eclipse attack works, reconnecting with malicious node, exposure to information, etc.


 Continue with Email
Continue with Email

 Home
Home


































