Process Safety
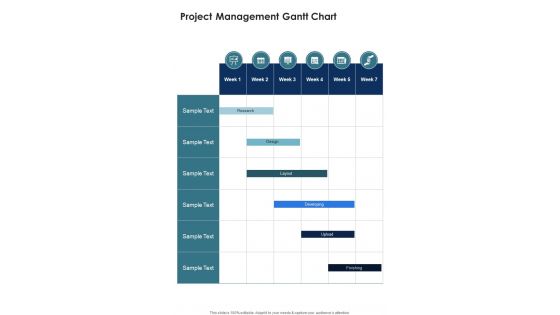
Project Management Gantt Chart Secure Network Construction Proposal One Pager Sample Example Document
Presenting you an exemplary Project Management Gantt Chart Secure Network Construction Proposal One Pager Sample Example Document. Our one-pager comprises all the must-have essentials of an inclusive document. You can edit it with ease, as its layout is completely editable. With such freedom, you can tweak its design and other elements to your requirements. Download this Project Management Gantt Chart Secure Network Construction Proposal One Pager Sample Example Document brilliant piece now.
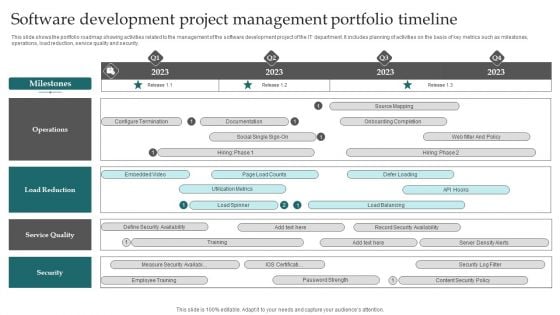
Software Development Project Management Portfolio Timeline Brochure PDF
This slide shows the portfolio roadmap showing activities related to the management of the software development project of the IT department. It includes planning of activities on the basis of key metrics such as milestones, operations, load reduction, service quality and security. Showcasing this set of slides titled Software Development Project Management Portfolio Timeline Brochure PDF. The topics addressed in these templates are Load Reduction, Service Quality, Security. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Impact Analysis For Effective Threat Management In Securing Workplace Professional PDF
This slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Impact Analysis For Effective Threat Management In Securing Workplace Professional PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.

Digital Project Management Strategies Deployment Of Cloud Project Management Model
This slide showcases deployment of cloud project management model. It provides information about public, private, hybrid, setup, data security, data control, privacy, scalability, integration, etc. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Digital Project Management Strategies Deployment Of Cloud Project Management Model. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Digital Project Management Strategies Deployment Of Cloud Project Management Model today and make your presentation stand out from the rest This slide showcases deployment of cloud project management model. It provides information about public, private, hybrid, setup, data security, data control, privacy, scalability, integration, etc.
Managing Cyber Security Incident Management Icon Ppt Infographics Design Templates PDF
Presenting Managing Cyber Security Incident Management Icon Ppt Infographics Design Templates PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Managing Cyber Security, Incident Management, Icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Threat Management At Workplace Impact Analysis For Effective Threat Management In Securing Structure PDF
This slide portrays information regarding how firm is successful in handling security threats and is able in reducing the occurrence of threats. Deliver an awe inspiring pitch with this creative threat management at workplace impact analysis for effective threat management in securing structure pdf bundle. Topics like security incidents, incidents damaging public image, actual access violations can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Email Security Encryption And Data Loss Prevention Proposal Ppt PowerPoint Presentation Complete Deck With Slides
Induce strategic thinking by presenting this complete deck. Enthrall your audience by deploying this thought-provoking PPT deck. It can be downloaded in both standard and widescreen aspect ratios, thus making it a complete package to use and deploy. Convey your thoughts and actions using the twenty eight slides presented in this complete deck. Additionally, feel free to alter its components like color, graphics, design, etc, to create a great first impression. Grab it now by clicking on the download button below.

Advances In Healthcare Management System Why Do We Need Hospital Management System Introduction PDF
This slide illustrates the need for hospital management system such as cost effectiveness, reduction in errors, maintains security of information, improves patient care, etc. This is a Advances In Healthcare Management System Why Do We Need Hospital Management System Introduction PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Information Security, Reduction In Errors, Cost Effective. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
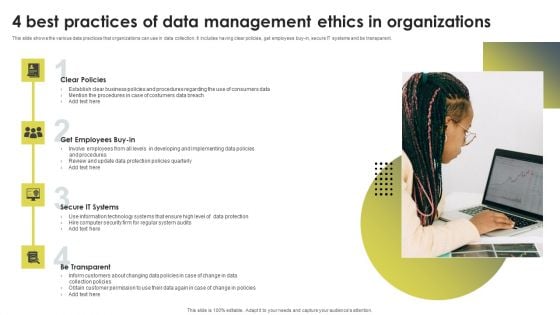
4 Best Practices Of Data Management Ethics In Organizations Ppt Infographics Grid PDF
This slide shows the various data practices that organizations can use in data collection. It includes having clear policies, get employees buy-in, secure IT systems and be transparent. Persuade your audience using this 4 Best Practices Of Data Management Ethics In Organizations Ppt Infographics Grid PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Clear Policies, Get Employees, Buy In, Secure IT Systems, Be Transparent. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
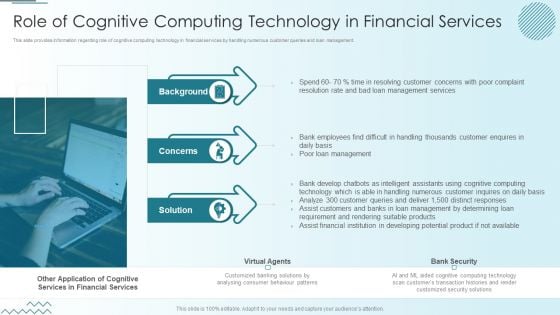
Computer Simulation Human Thinking Role Of Cognitive Computing Technology In Financial Services Diagrams PDF
This slide provides information regarding role of cognitive computing technology in financial services by handling numerous customer queries and loan management. Presenting Computer Simulation Human Thinking Role Of Cognitive Computing Technology In Financial Services Diagrams PDF to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like Background, Concerns, Solution, Virtual Agents, Bank Security. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
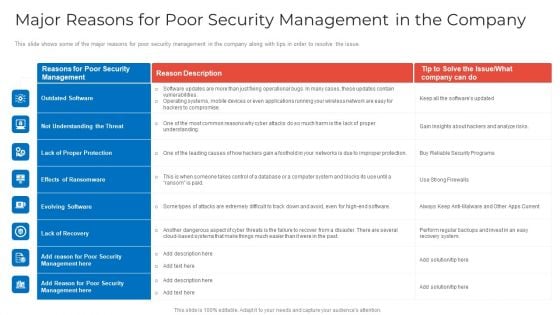
Major Reasons For Poor Security Management In The Company Topics PDF
This slide shows some of the major reasons for poor security management in the company along with tips in order to resolve the issue. Deliver an awe inspiring pitch with this creative major reasons for poor security management in the company topics pdf bundle. Topics like outdated software, lack of proper protection, effects of ransomware can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Analyzing Budget For Effective Mobile Device Management Mobile Device Security Management Sample PDF
Firm has prepared a budget for managing mobile device security by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Deliver an awe inspiring pitch with this creative Analyzing Budget For Effective Mobile Device Management Mobile Device Security Management Sample PDF bundle. Topics like Risk Management, Document Management, Information Management can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Deployment Of Cloud Project Management Model Digital Transformation In Project Management
This slide showcases deployment of cloud project management model. It provides information about public, private, hybrid, setup, data security, data control, privacy, scalability, integration, etc. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Deployment Of Cloud Project Management Model Digital Transformation In Project Management. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Deployment Of Cloud Project Management Model Digital Transformation In Project Management today and make your presentation stand out from the rest This slide showcases deployment of cloud project management model. It provides information about public, private, hybrid, setup, data security, data control, privacy, scalability, integration, etc.
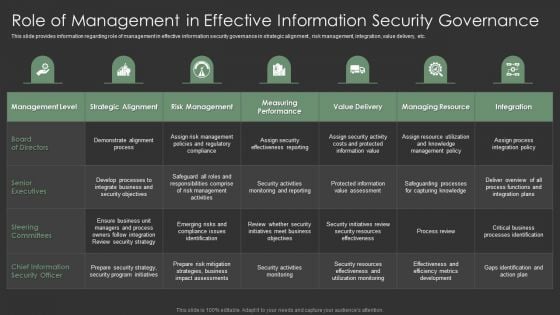
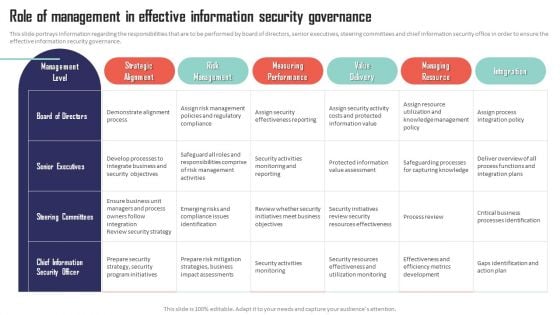
IT Spend Management Priorities By Cios Role Of Management In Effective Information Security Governance Graphics PDF
This slide provides information regarding role of management in effective information security governance in strategic alignment , risk management, integration, value delivery, etc. Deliver an awe inspiring pitch with this creative IT Spend Management Priorities By Cios Role Of Management In Effective Information Security Governance Graphics PDF bundle. Topics like Senior Executives, Strategic Alignment, Risk Management can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
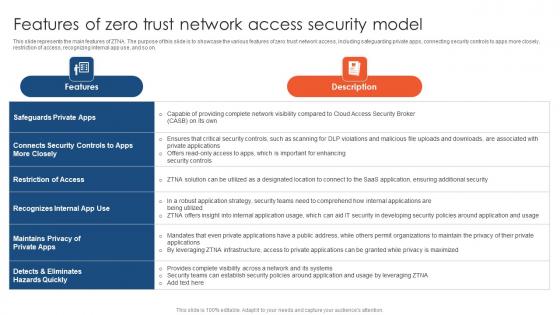
Zero Trust Network Access Features Of Zero Trust Network Access Security Model
This slide represents the main features of ZTNA. The purpose of this slide is to showcase the various features of zero trust network access, including safeguarding private apps, connecting security controls to apps more closely, restriction of access, recognizing internal app use, and so on. Slidegeeks has constructed Zero Trust Network Access Features Of Zero Trust Network Access Security Model after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates. This slide represents the main features of ZTNA. The purpose of this slide is to showcase the various features of zero trust network access, including safeguarding private apps, connecting security controls to apps more closely, restriction of access, recognizing internal app use, and so on.

Deployment Of Cloud Project Management Model Strategies For Success In Digital
This slide showcases deployment of cloud project management model. It provides information about public, private, hybrid, setup, data security, data control, privacy, scalability, integration, etc. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Deployment Of Cloud Project Management Model Strategies For Success In Digital. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Deployment Of Cloud Project Management Model Strategies For Success In Digital today and make your presentation stand out from the rest This slide showcases deployment of cloud project management model. It provides information about public, private, hybrid, setup, data security, data control, privacy, scalability, integration, etc.
Tracking Mobile Device Activities At Workplace Business Mobile Device Security Management Icons PDF
This slide covers information regarding the tracking mobile device activities at workplace with details about MDM managed mobile summary, MDM users, vulnerabilities and severity summary. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Tracking Mobile Device Activities At Workplace Business Mobile Device Security Management Icons PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.
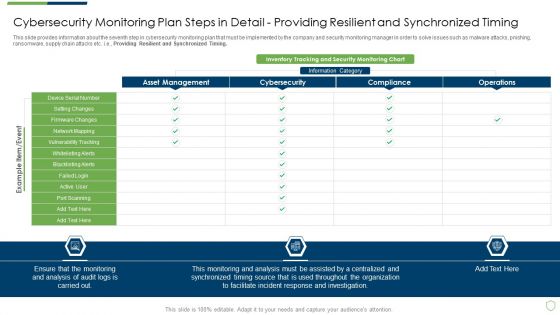
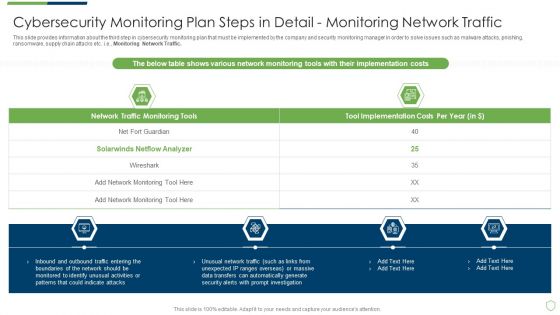
Modern Security Observation Plan To Eradicate Cybersecurity Risk And Data Breach Cybersecurity Monitoring Plan Steps In Detail Providing Sample PDF
This slide provides information about the second step in cybersecurity monitoring plan that must be implemented by the company and security monitoring manager in order to solve issues such as malware attacks, pnishing, ransomware, supply chain attacks etc. i.e., Monitoring All Systems. Deliver an awe inspiring pitch with this creative modern security observation plan to eradicate cybersecurity risk and data breach cybersecurity monitoring plan steps in detail providing sample pdf bundle. Topics like cybersecurity monitoring plan steps in detail monitoring all systems can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
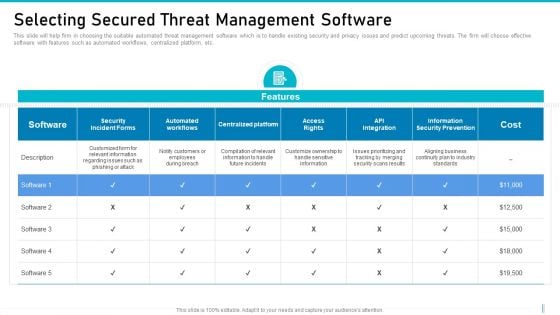
Risk Management For Organization Essential Assets Selecting Secured Threat Management Software Background PDF
This slide will help firm in choosing the suitable automated threat management software which is to handle existing security and privacy issues and predict upcoming threats. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Deliver an awe inspiring pitch with this creative risk management for organization essential assets selecting secured threat management software background pdf bundle. Topics like cost, information security prevention, api integration, access rights, centralized platform can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
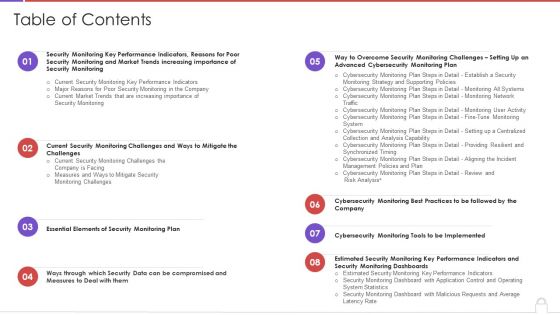
Table Of Contents Methods To Develop Advanced It Security Monitoring Plan Structure PDF
Deliver and pitch your topic in the best possible manner with this table of contents methods to develop advanced it security monitoring plan structure pdf. Use them to share invaluable insights on security monitoring, key performance indicators, security monitoring plan and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
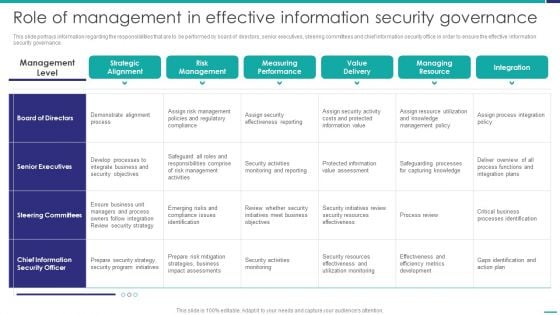
Role Of Management In Effective Governance Mobile Device Security Management Background PDF
This slide portrays information regarding the responsibilities that are to be performed by board of directors, senior executives, steering committees and chief information security office in order to ensure the effective information security governance. Deliver and pitch your topic in the best possible manner with this Role Of Management In Effective Governance Mobile Device Security Management Background PDF. Use them to share invaluable insights on Senior Executives, Steering Committees, Effectiveness Reporting and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
Mobile Device Management Role Of Management In Effective Information Security Microsoft PDF
This slide portrays information regarding the responsibilities that are to be performed by board of directors, senior executives, steering committees and chief information security office in order to ensure the effective information security governance. If your project calls for a presentation, then Slidegeeks is your go-to partner because we have professionally designed, easy-to-edit templates that are perfect for any presentation. After downloading, you can easily edit Mobile Device Management Role Of Management In Effective Information Security Microsoft PDF and make the changes accordingly. You can rearrange slides or fill them with different images. Check out all the handy templates
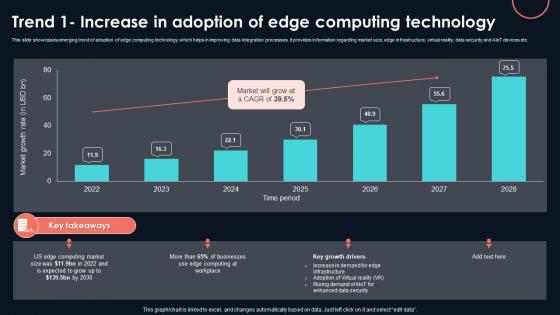
Trend 1 Increase In Adoption Of Edge Developing Strategic Insights Using Big Data Analytics SS V
This slide showcases emerging trend of adoption of edge computing technology which helps in improving data integration processes. It provides information regarding market size, edge infrastructure, virtual reality, data security and AIoT devices etc. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download Trend 1 Increase In Adoption Of Edge Developing Strategic Insights Using Big Data Analytics SS V to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the Trend 1 Increase In Adoption Of Edge Developing Strategic Insights Using Big Data Analytics SS V. This slide showcases emerging trend of adoption of edge computing technology which helps in improving data integration processes. It provides information regarding market size, edge infrastructure, virtual reality, data security and AIoT devices etc.
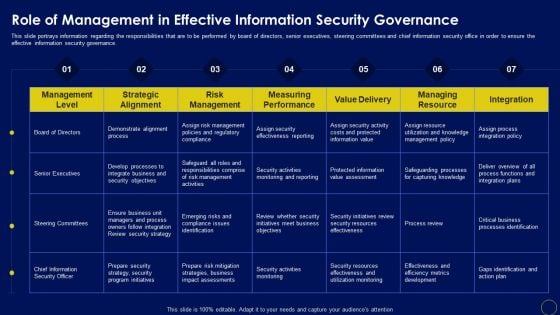
Role Of Management In Effective Business Mobile Device Security Management And Mitigation Slides PDF
This slide portrays information regarding the responsibilities that are to be performed by board of directors, senior executives, steering committees and chief information security office in order to ensure the effective information security governance. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Role Of Management In Effective Business Mobile Device Security Management And Mitigation Slides PDF can be your best option for delivering a presentation. Represent everything in detail using Role Of Management In Effective Business Mobile Device Security Management And Mitigation Slides PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.

Business Mobile Device Security Management And Mitigation Ppt PowerPoint Presentation Complete Deck With Slides
If you are looking for Business Mobile Device Security Management And Mitigation Ppt PowerPoint Presentation Complete Deck With Slides to help improve your customer connect, this is the perfect option. Download this PowerPoint Template to make an effective observation on business strategies and policies. You can analyze techniques that prove beneficial or otherwise. You can easily monitor and compare other businesses on how they interact with customers and the industry benchmarks surrounding this with each of the sixty three slides of the complete deck a lesson the same. The 100 precent customizable feature of the presentation ensures that this has to be in your collection, at any cost. Download now.
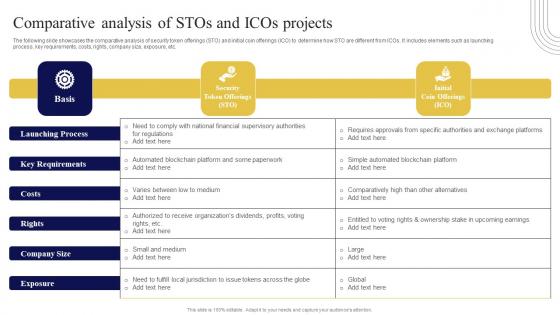
Comparative Analysis Of Stos And Icos Exploring Investment Opportunities Download Pdf
The following slide showcases the comparative analysis of security token offerings STO and initial coin offerings ICO to determine how STO are different from ICOs. It includes elements such as launching process, key requirements, costs, rights, company size, exposure, etc. Slidegeeks is here to make your presentations a breeze with Comparative Analysis Of Stos And Icos Exploring Investment Opportunities Download Pdf With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first The following slide showcases the comparative analysis of security token offerings STO and initial coin offerings ICO to determine how STO are different from ICOs. It includes elements such as launching process, key requirements, costs, rights, company size, exposure, etc.
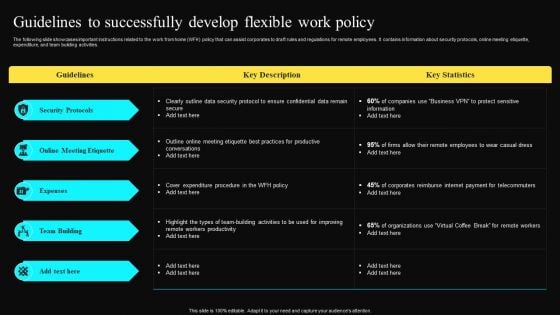
Guidelines To Successfully Develop Flexible Work Policy Professional PDF
The following slide showcases important instructions related to the work from home WFH policy that can assist corporates to draft rules and regulations for remote employees. It contains information about security protocols, online meeting etiquette, expenditure, and team building activities. Welcome to our selection of the Guidelines To Successfully Develop Flexible Work Policy Professional PDF. These are designed to help you showcase your creativity and bring your sphere to life. Planning and Innovation are essential for any business that is just starting out. This collection contains the designs that you need for your everyday presentations. All of our PowerPoints are 100 percent editable, so you can customize them to suit your needs. This multi-purpose template can be used in various situations. Grab these presentation templates today.
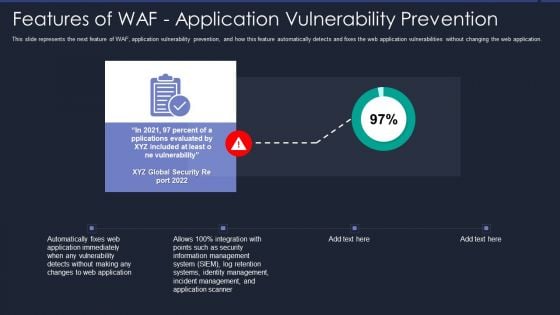
Web App Firewall Services IT Features Of WAF Application Vulnerability Prevention Information PDF
This slide represents the next feature of WAF, application vulnerability prevention, and how this feature automatically detects and fixes the web application vulnerabilities without changing the web application. Presenting web app firewall services it features of waf application vulnerability prevention information pdf to provide visual cues and insights. Share and navigate important information on one stages that need your due attention. This template can be used to pitch topics like management, security, application, information. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Investment Service Provider Capital Raising Elevator Details About Emerging Fintech Firm Topics PDF
This slide caters details about emerging fintech firm including details about vision statement, features of FinTech platform with rise in transactional value in FinTech addressing its growth potential. Deliver and pitch your topic in the best possible manner with this investment service provider capital raising elevator details about emerging fintech firm topics pdf. Use them to share invaluable insights on payment gateways, digital banking, asset management, secure and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
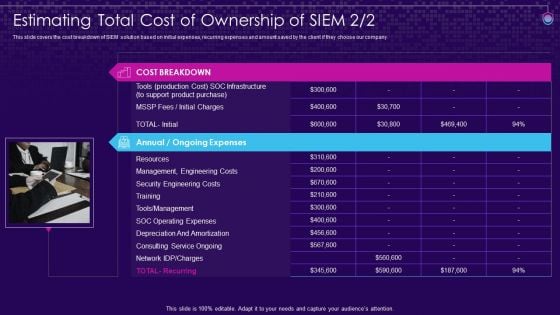
SIEM Services Estimating Total Cost Of Ownership Of SIEM Ppt Themes PDF
This slide covers the cost breakdown of SIEM solution based on initial expenses, recurring expenses and amount saved by the client if they choose our company. This is a siem services estimating total cost of ownership of siem ppt themes pdf template with various stages. Focus and dispense information on one stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like resources, management, engineering , security engineering costs, soc operating expenses. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

SIEM Software Challenges With Solutions SIEM Services Ppt Inspiration Ideas PDF
This slide covers the challenges and solutions of security information and event management software such as workforce limitations, weak responsiveness, dynamic data limitations, etc. Presenting siem software challenges with solutions siem services ppt inspiration ideas pdf to provide visual cues and insights. Share and navigate important information on two stages that need your due attention. This template can be used to pitch topics like workforce limitations, dynamic data limitations, responsiveness. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

IT Services And Consulting Company Profile Company Strategic Partnerships Mockup PDF
This slide focuses on leading partners associated with our company that is crucial to grow business venture which is established on the basis of trust, respect, similar values and shared goals.This is a IT Services And Consulting Company Profile Company Strategic Partnerships Mockup PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Tarsus Technology Group, Relationships Which Includes, Provides Security Management You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Cybersecurity Operations Cybersecops Key Outcomes Manage By Security Operations Demonstration PDF
This slide outlines the critical outcomes that are handled by the security operations team. The purpose of this slide is to demonstrate the various key outcomes, their activities, responsible person and remarks. The main outcomes include incident management, incident preparation and threat intelligence. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Cybersecurity Operations Cybersecops Key Outcomes Manage By Security Operations Demonstration PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable Cybersecurity Operations Cybersecops Key Outcomes Manage By Security Operations Demonstration PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.
Modern Security Observation Plan To Eradicate Cybersecurity Risk And Data Breach Cybersecurity Monitoring Plan Steps Elements PDF
This slide provides information about the ninth step in cybersecurity monitoring plan that must be implemented by the company and security monitoring manager in order to solve issues such as malware attacks, pnishing, ransomware, supply chain attacks etc. i.e. Review and Risk Analysis. Deliver and pitch your topic in the best possible manner with this modern security observation plan to eradicate cybersecurity risk and data breach cybersecurity monitoring plan steps elements pdf. Use them to share invaluable insights on cybersecurity monitoring plan steps in detail review and risk analysis and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Steps To Withdraw Funds From Digital Wallet In Depth Guide To Digital Wallets Fin SS V
The following slide highlights the various technologies used in digital wallets for payment processing. The different technologies are near field communication. Magnetic secure transmission, and QR codes. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Steps To Withdraw Funds From Digital Wallet In Depth Guide To Digital Wallets Fin SS V was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Steps To Withdraw Funds From Digital Wallet In Depth Guide To Digital Wallets Fin SS V The following slide highlights the various technologies used in digital wallets for payment processing. The different technologies are near field communication. Magnetic secure transmission, and QR codes.

Key Focus Areas In Digital Security And Access Management Ppt Visual Aids Model PDF
Showcasing this set of slides titled key focus areas in digital security and access management ppt visual aids model pdf. The topics addressed in these templates are digital security, cyber security, access management. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
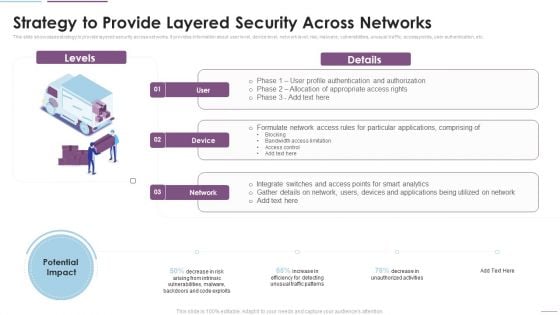
Supply Chain Management Strategy To Provide Layered Security Across Networks Brochure PDF
This slide showcases strategy to provide layered security across networks. It provides information about user level, device level, network level, risk, malware, vulnerabilities, unusual traffic, access points, user authentication, etc. Deliver and pitch your topic in the best possible manner with this Supply Chain Management Strategy To Provide Layered Security Across Networks Brochure PDF. Use them to share invaluable insights on Formulate Network, Access Rules, Particular Applications, Bandwidth Access Limitation and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
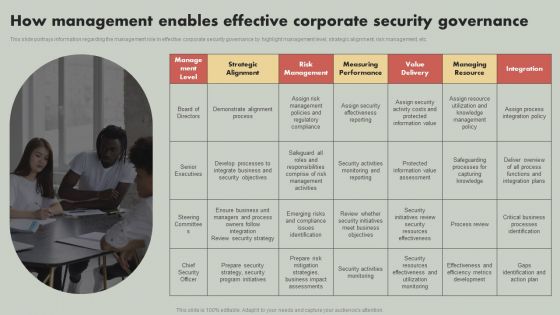
IT Reducing Costs And Management Tips How Management Enables Effective Corporate Security Governance Mockup PDF
This slide portrays information regarding the management role in effective corporate security governance by highlight management level, strategic alignment, risk management, etc. Get a simple yet stunning designed IT Reducing Costs And Management Tips How Management Enables Effective Corporate Security Governance Mockup PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy to edit IT Reducing Costs And Management Tips How Management Enables Effective Corporate Security Governance Mockup PDF can be your go to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.

Financing Catalogue For Security Underwriting Agreement Senior Management Biographies Information PDF
The slide provides the name and designation of senior management teams CEO, CFO, Department Head etc. of the company. It also covers brief information about their work experience, prior industry experience and education. This is a financing catalogue for security underwriting agreement senior management biographies information pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like senior management biographies and other details. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
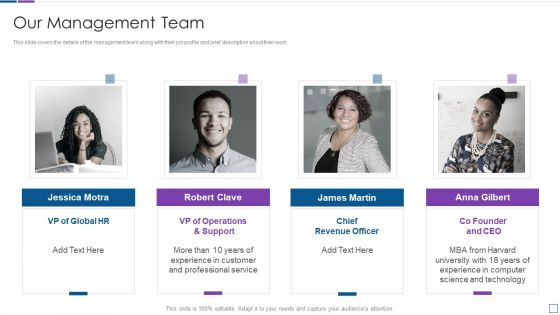
Real Time Assessment Of Security Threats Our Management Team Graphics PDF
This slide covers the details of the management team along with their job profile and brief description about their work. This is a real time assessment of security threats our management team graphics pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like our management team. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Key Hurdles For Security Management Reporting Ppt PowerPoint Presentation Styles Graphic Tips PDF
Showcasing this set of slides titled key hurdles for security management reporting ppt powerpoint presentation styles graphic tips pdf. The topics addressed in these templates are employee, job responsibilities, complicated reporting documentation. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Deploying Corporate Aligned IT Strategy How Management Enables Effective Corporate Security Governance Topics PDF
This slide portrays information regarding the management role in effective corporate security governance by highlight management level, strategic alignment, risk management, etc. The Deploying Corporate Aligned IT Strategy How Management Enables Effective Corporate Security Governance Topics PDF is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression.

Investment Banking Security Underwriting Pitchbook Senior Management Biographies And Other Details Microsoft PDF
The slide provides the name and designation of senior management teams CEO, CFO, department head etc. Of the company. It also covers brief information about their work experience, prior industry experience and education. This is a Investment Banking Security Underwriting Pitchbook Senior Management Biographies And Other Details Microsoft PDF template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Industry Experience, Designation, Education You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Determining Roles And Responsibilities For Risk Handling Business Mobile Device Security Management Graphics PDF
This slide provides information regarding the roles and responsibilities of management in handling mobile device security risks. Key people involved in risk handling are chief risk officer, chief information security officer, senior management and executives and line managers. Boost your pitch with our creative Determining Roles And Responsibilities For Risk Handling Business Mobile Device Security Management Graphics PDF. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
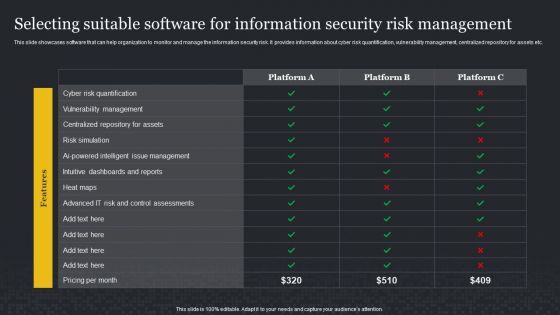
Selecting Suitable Software For Information Security Risk Management Cybersecurity Risk Assessment Infographics PDF
This slide showcases software that can help organization to monitor and manage the information security risk. It provides information about cyber risk quantification, vulnerability management, centralized repository for assets etc. If you are looking for a format to display your unique thoughts, then the professionally designed Selecting Suitable Software For Information Security Risk Management Cybersecurity Risk Assessment Infographics PDF is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Selecting Suitable Software For Information Security Risk Management Cybersecurity Risk Assessment Infographics PDF and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.
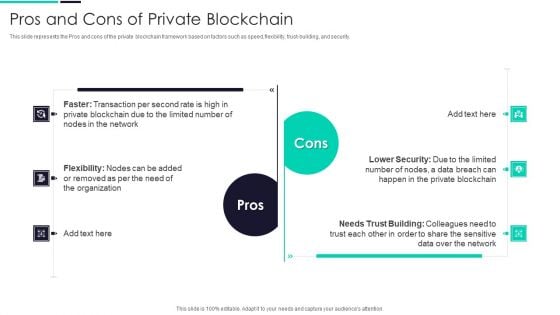
Blockchain And DLT Framework Pros And Cons Of Private Blockchain Portrait PDF
This slide represents the Pros and cons of the private blockchain framework based on factors such as speed, flexibility, trust-building, and security. Presenting Blockchain And DLT Framework Pros And Cons Of Private Blockchain Portrait PDF to provide visual cues and insights. Share and navigate important information on two stages that need your due attention. This template can be used to pitch topics like Lower Security, Needs Trust Building, Transaction Per Second. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
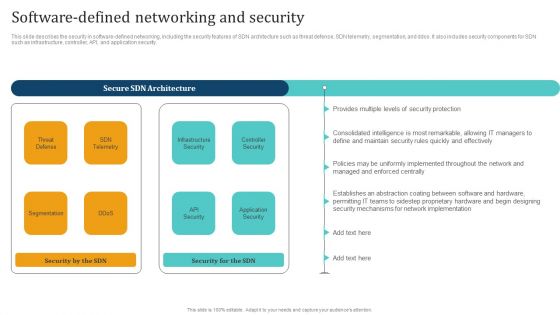
Empowering Network Agility Through SDN Software Defined Networking And Security Rules PDF
This slide describes the security in software defined networking, including the security features of SDN architecture such as threat defense, SDN telemetry, segmentation, and ddos. It also includes security components for SDN such as infrastructure, controller, API, and application security. Welcome to our selection of the Empowering Network Agility Through SDN Software Defined Networking And Security Rules PDF. These are designed to help you showcase your creativity and bring your sphere to life. Planning and Innovation are essential for any business that is just starting out. This collection contains the designs that you need for your everyday presentations. All of our PowerPoints are 100 percent editable, so you can customize them to suit your needs. This multi purpose template can be used in various situations. Grab these presentation templates today.
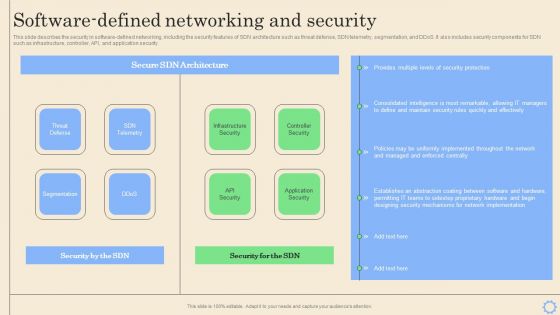
Software Defined Networking Development Strategies Software Defined Networking And Security Pictures PDF
This slide describes the security in software-defined networking, including the security features of SDN architecture such as threat defense, SDN telemetry, segmentation, and DDoS. It also includes security components for SDN such as infrastructure, controller, API, and application security. Want to ace your presentation in front of a live audience Our Software Defined Networking Development Strategies Software Defined Networking And Security Pictures PDF can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy to edit and downloadable. Use these for both personal and commercial use.

Our Management For Home Security Equipment Installation One Pager Sample Example Document
Purpose of the following slide is to show the team management of the organization as it displays the details of the team members such as name, designation image etc. Presenting you an exemplary Our Management For Home Security Equipment Installation One Pager Sample Example Document. Our one pager comprises all the must have essentials of an inclusive document. You can edit it with ease, as its layout is completely editable. With such freedom, you can tweak its design and other elements to your requirements. Download this Our Management For Home Security Equipment Installation One Pager Sample Example Document brilliant piece now.

Managing Cyber Security Incident Management KPI Dashboard To Measure Performance Download PDF
This slide covers cyber security incident management KPI dashboard to measure performance. It involves details such as average resolution time, new incidents, incident status, resolved vs unresolved incidents and created vs closed incidents. Showcasing this set of slides titled Managing Cyber Security Incident Management KPI Dashboard To Measure Performance Download PDF. The topics addressed in these templates are Average Resolution Time, Incident Status, New Incidents. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
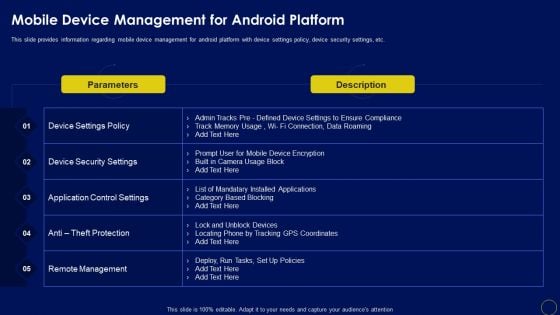
Mobile Device Management For Android Platform Business Mobile Device Security Management Graphics PDF
This slide provides information regarding mobile device management for android platform with device settings policy, device security settings, etc. Slidegeeks is here to make your presentations a breeze with Mobile Device Management For Android Platform Business Mobile Device Security Management Graphics PDF With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.
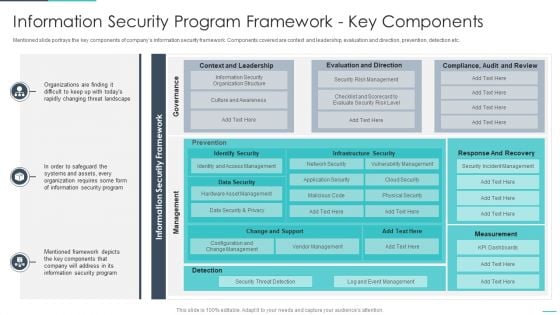
Handling Cyber Threats Digital Era Information Security Program Framework Ppt Model Summary PDF
Mentioned slide portrays the key components of companys information security framework. Components covered are context and leadership, evaluation and direction, prevention, detection etc. Deliver and pitch your topic in the best possible manner with this handling cyber threats digital era information security program framework ppt model summary pdf. Use them to share invaluable insights on information security program framework key components and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
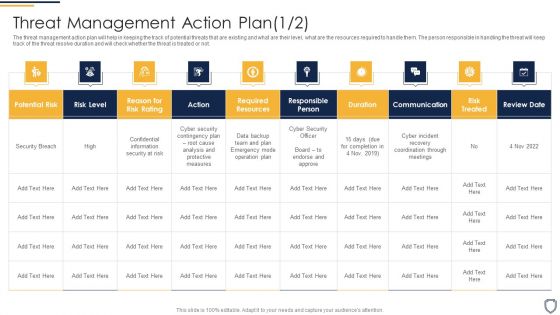
Corporate Security And Risk Management Threat Management Action Plan Risk Portrait PDF
The threat management action plan will help in keeping the track of various potential threats that are existing in the firm. The person responsible in handling the threats will keep track of the duration in which threat is resolved. Presenting corporate security and risk management threat management action plan risk portrait pdf to provide visual cues and insights. Share and navigate important information on two stages that need your due attention. This template can be used to pitch topics like threat identification, threat treatment . In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
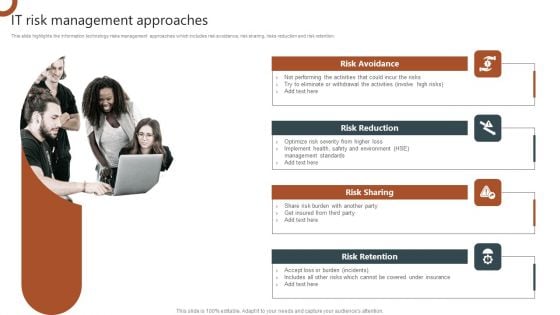
IT Risk Management Approaches Organizations Risk Management And IT Security Graphics PDF
This slide highlights the information technology risks management approaches which includes risk avoidance, risk sharing, risks reduction and risk retention. Want to ace your presentation in front of a live audience Our IT Risk Management Approaches Organizations Risk Management And IT Security Graphics PDF can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy to edit and downloadable. Use these for both personal and commercial use.
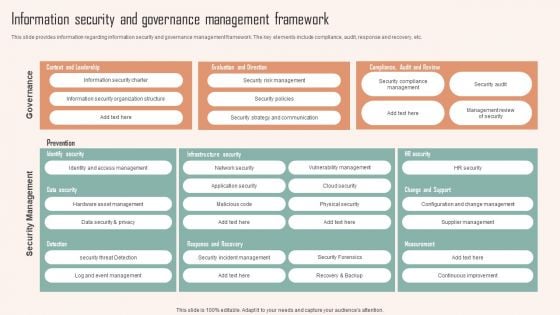
Information Security And Governance Management Framework Ppt PowerPoint Presentation Diagram Images PDF
This slide provides information regarding information security and governance management framework. The key elements include compliance, audit, response and recovery, etc. Make sure to capture your audiences attention in your business displays with our gratis customizable Information Security And Governance Management Framework Ppt PowerPoint Presentation Diagram Images PDF. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.

Digital Wallet Delivery Technology For Payment In Depth Guide To Digital Wallets Fin SS V
The following slide highlights the various technologies used in digital wallets for payment processing. The different technologies are near field communication. Magnetic secure transmission, and QR codes. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Digital Wallet Delivery Technology For Payment In Depth Guide To Digital Wallets Fin SS V can be your best option for delivering a presentation. Represent everything in detail using Digital Wallet Delivery Technology For Payment In Depth Guide To Digital Wallets Fin SS V and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results. The following slide highlights the various technologies used in digital wallets for payment processing. The different technologies are near field communication. Magnetic secure transmission, and QR codes.
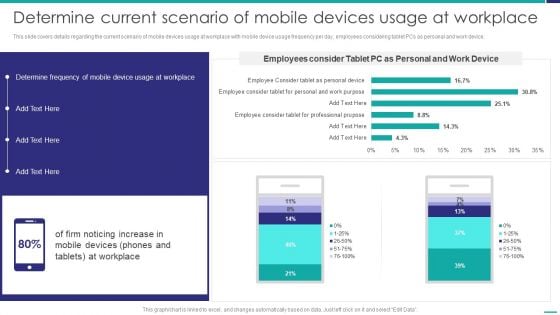
Determine Current Scenario Of Mobile Devices Usage At Workplace Mobile Device Security Management Template PDF
This slide covers details regarding the current scenario of mobile devices usage at workplace with mobile device usage frequency per day, employees considering tablet PCs as personal and work device. Deliver and pitch your topic in the best possible manner with this Determine Current Scenario Of Mobile Devices Usage At Workplace Mobile Device Security Management Template PDF. Use them to share invaluable insights on Determine Frequency, Mobile Device, Workplace and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Implementing Cyber Security Incident Management Ppt PowerPoint Presentation Complete Deck With Slides
This Implementing Cyber Security Incident Management Ppt PowerPoint Presentation Complete Deck With Slides is designed to help you retain your audiences attention. This content-ready PowerPoint Template enables you to take your audience on a journey and share information in a way that is easier to recall. It helps you highlight the crucial parts of your work so that the audience does not get saddled with information download. This seventy slide PPT Deck comes prepared with the graphs and charts you could need to showcase your information through visuals. You only need to enter your own data in them. Download this editable PowerPoint Theme and walk into that meeting with confidence.

Developing IT Security Strategy Matrix For Threat Solution And Risk Management Topics PDF
This slide showcases matrix that can help organization to formulate solutions for different types of information security attacks. It can help organization to mitigate the risks and safeguard information in case of any attack. Find highly impressive Developing IT Security Strategy Matrix For Threat Solution And Risk Management Topics PDF on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Developing IT Security Strategy Matrix For Threat Solution And Risk Management Topics PDF for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now.
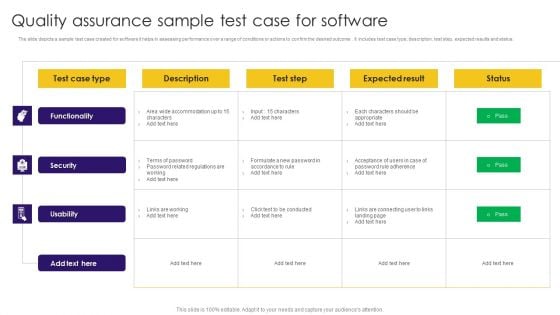
Quality Assurance Sample Test Case For Software Ppt Show Summary PDF
The slide depicts a sample test case created for software it helps in assessing performance over a range of conditions or actions to confirm the desired outcome. it includes test case type, description, test step, expected results and status. Pitch your topic with ease and precision using this Quality Assurance Sample Test Case For Software Ppt Show Summary PDF. This layout presents information on Functionality, Security, Usability, Test Case Type. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.


 Continue with Email
Continue with Email

 Home
Home


































